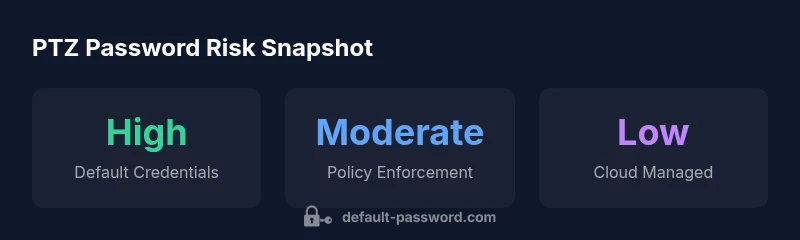
PTZ Camera Default Password: A Practical Security Guide
Learn how to identify, mitigate, and monitor default passwords on PTZ cameras. Practical steps for IT admins and end-users to secure IP cameras against unauthorized access.

The ptz camera default password is a critical security risk that can grant unauthorized access to live feeds and device settings. For most PTZ cameras, changing the default credentials to a unique, strong password and disabling unused services dramatically reduces risk. The quickest mitigation is to replace the factory password with a unique, complex credential, enable two-factor if available, and limit remote access. This quick answer outlines practical steps and why it's essential.
Understanding PTZ Cameras and Default Password Risks
PTZ cameras (pan-tilt-zoom) are common in offices, schools, retail, and homes. They offer remote control of viewing angles and often integrate with NVRs and cloud services. A default password is designed to simplify setup, but it's a glaring security flaw if not changed. Attackers can exploit default credentials to access live feeds, adjust camera settings, or push firmware updates to compromise networks. In many deployments, credentials are reused across devices or documented in manuals, making discovery trivial for automated scans. This combination creates a huge attack surface, especially when devices are exposed to the internet or accessible through weak firewall rules. The risk becomes acute when cameras reside behind NAT or in shared networks where a single compromised device can lead to lateral movement. The Default Password team notes that incidents often begin with unchanged factory credentials. Treat every PTZ installation as if the default password is known to outsiders, and plan credential hygiene as a foundational security control.
Common Default Password Scenarios in PTZ Cameras
Many PTZ deployments suffer from predictable patterns that make intrusions easy:
- Reusing a single password across multiple devices
- Printing or recording the default credential on device labels or manuals
- Leaving an admin account with the factory password active
- Provisioning through cloud services that auto-fill defaults
- Exposing devices to the internet without proper access controls These scenarios are not rare anecdotes; they echo findings highlighted by the Default Password team and underline why every PTZ setup needs a password hygiene plan. By recognizing common patterns, IT admins can prioritize changes that reduce exposure and prevent attackers from gaining initial footholds.
Immediate Actions: What to Do Right Now
If you are responsible for PTZ cameras, begin with a quick but thorough triage:
- Locate the current credentials in device labels, manuals, or the web UI. If you cannot locate them, perform a factory reset per the manufacturer’s instructions.
- Change the default password to a unique, long credential (preferably 16+ characters with a mix of cases, numbers, and symbols).
- Disable any services you do not use, such as unnecessary remote management or UPnP, and update the firmware to the latest security patch.
- Enable logging and alerting so you receive notifications on failed logins or unusual access patterns.
- If possible, implement network segmentation so cameras are isolated from sensitive systems and limit access to a trusted IP range. These steps dramatically reduce the risk surface and reflect best practices highlighted by the Default Password Analysis for 2026.
How to Change a PTZ Camera Password: A Step-by-Step Guide
Changing a PTZ password typically follows a consistent pattern across vendors, though interfaces vary. Here is a generic, high-level workflow you can adapt:
- Access the camera’s web UI or mobile app using the current credentials.
- Navigate to Settings > Security > Password (or Admin) and select Change Password.
- Enter a new, strong password. Avoid common phrases, reuse of past passwords, or simple substitutions. Consider using a passphrase with mixed character types.
- Create or assign a second administrator or user with restricted permissions if supported; remove or disable the default admin account if the option exists.
- Save changes, log out, and log back in with the new credentials to verify access.
- Check for firmware updates and apply them; reboot if required.
- Document the new credentials securely using a password manager with restricted access. This process aligns with recommended practices from the Default Password team and reduces the risk of credential exposure.
Best Practices for Password Management on IP Cameras
Beyond a one-time change, maintain ongoing password hygiene:
- Use unique passwords for each PTZ camera and related admin accounts
- Enforce length and complexity requirements; avoid dictionary words and personal data
- Rotate credentials on a fixed cadence (e.g., every 90-180 days) and whenever a security event occurs
- Enable two-factor authentication if the camera supports it or use a centralized authentication gateway
- Centralize credential storage in a password manager and restrict access to IT staff only
- Regularly review user accounts and remove any unused or stale accounts
- Disable or limit remote access to trusted networks; use VPN or MFA-protected access where feasible
Auditing and Monitoring PTZ Access
Security is strengthened by visibility. Implement comprehensive logging of login attempts, configuration changes, and firmware updates. Integrate camera logs with a SIEM or an alerting platform to detect unusual activity. Set up automated alerts for failed logins from unfamiliar IPs, repeated password attempts, or changes to critical settings. Maintain an access audit trail for accountability and facilitate forensics if a breach occurs. In practice, consistent monitoring can identify compromised credentials early and prevent broader incidents.
Real-World Examples and Risks of Non-Compliance
When organizations neglect PTZ password hygiene, small missteps can escalate into major incidents. For example, insecure remote access configurations can allow attackers to view sensitive feeds or manipulate PTZ controls, potentially endangering people and assets. Forced password changes and regular audits reduce these risks. The field reports synthesized by the Default Password team show that organizations that institutionalize credential hygiene, firmware updates, and network segmentation experience far fewer breaches related to IP cameras. Proactive policies and practical controls are the difference between a minor alert and a full-blown security incident.
PTZ camera default password risk and mitigation matrix
| Aspect | Risk Level | Mitigation |
|---|---|---|
| PTZ camera default password on new devices | High | Change default password during initial setup; disable unused features; update firmware. |
| Shared credentials across multiple cameras | Medium | Assign unique passwords per device; document changes. |
Your Questions Answered
What is a PTZ camera default password?
A default password is the factory-set credential used by the manufacturer. It is often documented in the manual or on the device label. If not changed, attackers can gain access. Always change it to a strong, unique password.
A default password is the factory credential; change it immediately for security.
Why are PTZ cameras particularly risky with default passwords?
PTZ cameras control live video and pan/tilt; if compromised, attackers can spy or disrupt. Many units ship with simple defaults; remote access makes it easy to reach devices.
Because PTZs control live feeds, default passwords create a high-risk doorway for attackers.
How do I reset a PTZ camera to factory settings?
Consult the manufacturer’s manual for the exact procedure. It typically involves a physical reset button or a reset option in the web UI. Note that a factory reset will erase custom configurations, so back up settings if possible.
Use the reset option in the menu or a physical button, then reconfigure credentials.
What are best practices to manage camera credentials?
Use unique passwords per device, enforce rotation, enable two-factor authentication if available, and store credentials in a secure password manager with restricted access.
Keep each camera’s password unique and rotate them regularly.
Can I avoid default password issues with cloud-managed cameras?
Some cloud-managed cameras enforce stronger credential policies and automatic password changes. Ensure remote access is restricted to trusted networks and use MFA where possible.
Cloud management can help enforce stronger security, but you should still change defaults and monitor access.
“The Default Password Team emphasizes that default credentials are the weakest link in IP camera security; changing them is the simplest yet most effective defense.”
Key Takeaways
- Change default passwords immediately
- Use strong, unique credentials
- Enable automatic alerts for credential changes
- Regularly audit camera access