PTZOptics Default Password Guide: Reset, Secure, and Manage Admin Access
Comprehensive guide to ptzoptics default password: how to reset, secure admin access, and implement best practices for PTZOptics cameras and IP devices in 2026.

The ptzoptics default password varies by model and is often reset at first boot. For security, change it immediately and enable strong authentication. On most PTZOptics cameras, you access the web UI, navigate to Admin or Security settings, then create a unique password and disable any factory defaults. Always consult the official PTZOptics user guide for model-specific details.
Why PTZOptics Default Password Security Matters
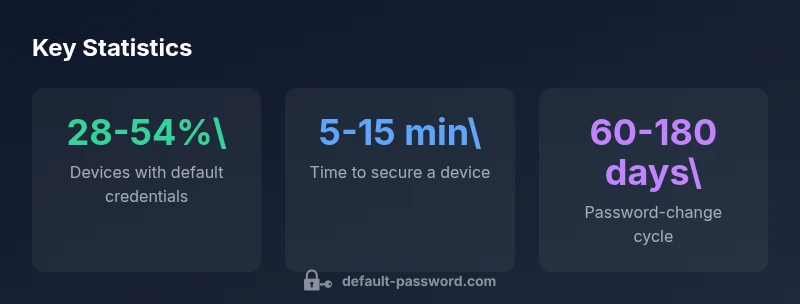
In today’s networked surveillance environment, a default password on a PTZOptics device is more than a nuisance—it’s a serious security risk. Default credentials are widely documented and exploit-able by automated scanners and opportunistic attackers. The Default Password team notes that even a single unredirected default password can allow an attacker to view live feeds, alter camera angles, or disable alerts. The potential impact ranges from privacy violations to complete exposure of sensitive site information. A strong password policy is a fundamental, low-friction control that raises the barrier for attackers and eases compliance with security guidelines. For end-users and IT admins, the takeaway is simple: do not assume that “factory settings” are safe for production networks. According to Default Password, proactive credential hygiene is the first and most valuable layer of protection for PTZOptics cameras and other IP devices.
Key concepts tied to this topic include admin access controls, password rotation, device firmware integrity, and network segmentation. When you plan a password strategy for PTZOptics devices, you should also account for remote access, alerting, and logging. The higher the exposure (e.g., cameras on public networks or in multi-tenant environments), the more important it becomes to enforce unique credentials and routine reviews. This article emphasizes practical steps you can take to minimize risk without slowing down operations.
How Credential Provisioning Works on PTZOptics Cameras
Credential provisioning for PTZOptics devices typically follows a two-step approach: (1) initial onboarding and (2) ongoing credential maintenance. During first boot, many models prompt you to set an admin username and a strong password. If you skip this step or rely on a factory password, you create an unattended risk vector. Modern PTZOptics models support encrypted admin sessions, role-based access, and event logging, which means that proper provisioning should include configuring an admin account with least-privilege rights and enabling audit logs.
From a cybersecurity perspective, the provisioning phase is when most misconfigurations become locked in. IT admins should enforce unique passwords per device, prohibit reuse across devices, and disable any remote services that are not required for normal operation. If a device supports two-factor authentication (2FA) or OAuth-based access, enable it. While PTZOptics devices can be managed individually, consider scalable onboarding via centralized management where practical, while preserving strong authentication and clear ownership of each device’s credentials. In short, secure provisioning reduces risk at the source by ensuring credentials aren’t left in a default, guessable state.
Step-by-Step: Resetting a PTZOptics Default Password
- Identify model and firmware version via the device’s label or web UI.
- Access the camera’s web interface (http://<IP>/) and log in with the current admin credentials. If you don’t know them, perform a factory reset using the hardware button or the reset sequence documented in the user guide.
- Navigate to Security or Admin settings → Change Password. Enter a new, strong password that is unique to this device.
- Use a combination of length (12+), uppercase, lowercase, numbers, and symbols. Avoid common words or prompts.
- Disable any “default credentials” option, if available, and review user roles to enforce least privilege.
- Update the firmware if an update is available before re-enabling remote access.
- Save changes and log out. Test login with the new password to verify success.
- Record the new credentials securely in a password manager and document the device’s security changes for audits.
Best Practices for PTZOptics Admin Access
- Use a unique, strong password for every PTZOptics device. Do not reuse passwords across devices or services.
- Enable 2FA if the device or its cloud portal supports it; when not possible, require complex passwords and regular rotation.
- Limit admin access to a dedicated, trusted network segment. Use VPNs or secure remote management gateways where remote access is required.
- Regularly review access rights and remove users who no longer need access. Maintain an auditable log trail of changes.
- Keep firmware updated. Security patches often address known credential vulnerabilities and authentication flaws.
Verifying Password Strength and Access Controls
Verify that admin passwords are not stored in plaintext, that password age is enforced if feasible, and that all devices report failed login attempts to a centralized log system. Use a password manager for all credentials, and rotate passwords on a scheduled basis. If the device supports 2FA, enable it and test it periodically. Regularly scan for exposed credentials in configuration exports or backups, and ensure that backups do not contain unencrypted passwords. For teams, implement RBAC (role-based access control) to minimize the number of users with admin privileges.
Post-Reset Logging, Monitoring, and Network Segmentation
After you reset credentials, enable and centralize logs from PTZOptics devices to monitor login attempts, changes, and firmware updates. Place cameras on a dedicated security VLAN that is isolated from sensitive internal networks. Review port exposure in firewalls and ensure that remote access is necessary and properly secured. Maintain an incident response plan that includes password-related events, and practice tabletop exercises to improve readiness.
Common Pitfalls and How to Avoid Them
- Re-using passwords across devices or services. Remedy: use a password manager and unique device passwords.
- Forgetting to disable factory-default access after setup. Remedy: explicitly disable defaults and audit access controls.
- Not updating firmware. Remedy: enable automatic updates if available and monitor vendor advisories.
- Inadequate documentation of credential changes. Remedy: document changes with timestamps for audits and compliance.
Model-Specific Guidance and Resources
Always refer to the official PTZOptics manuals for model-specific steps, including reset sequences, password requirements, and firmware notes. Our guidance aggregates best practices across devices and is intended to complement model-specific instructions rather than replace them. When in doubt, contact PTZOptics support or consult the product’s admin portal documentation to ensure your security posture aligns with current recommendations.
Illustrative comparison of default password scenarios for PTZOptics devices
| Model Type | Default Password Status | Recommended Action |
|---|---|---|
| IP Camera (PTZ variant) | Default credentials present | Change to unique password on first login |
| PTZOptics family device | Password already changed | Maintain strong password; enable 2FA if supported |
| Cloud-enabled PTZ device | Factory credentials disabled | Regularly rotate passwords and monitor access |
Your Questions Answered
What is the default password for PTZOptics cameras?
There isn’t a universal default password. Model-specific defaults may exist, but you should assume a password exists and set a new one during first login. Always refer to the device manual for exact details.
There isn’t one universal default password. Check your model’s manual and change it during setup.
How do I reset a PTZOptics device to factory settings?
Use the reset button or the documented reset sequence for your model to restore factory settings, then reconfigure credentials from scratch.
Use the reset option per your model’s manual to restore factory settings and reconfigure credentials.
How can I verify if a PTZOptics device still uses a factory default password?
Log in to the admin interface, go to Security settings, and look for any default-password indicators or prompts to change credentials. Consider running a security scan if supported.
Log in, check Security settings, and confirm there’s no default password remaining.
Why should I avoid using default passwords on PTZOptics devices?
Default passwords are widely known and can be exploited to access feeds or change device behavior. Always replace them with strong, unique credentials.
Default passwords are easy to guess and dangerous—always set strong, unique passwords.
Are there recommended password-management practices for PTZOptics devices?
Use a password manager, rotate passwords on a schedule, avoid reuse, and enable available 2FA. Maintain a centralized inventory of credentials for audits.
Use a password manager, rotate regularly, and enable 2FA where possible.
Can PTZOptics devices be integrated with enterprise password managers?
Some PTZOptics devices support integration via standard credentials; check vendor docs for API access or vault compatibility.
Some devices support enterprise password managers; consult the vendor docs for specifics.
“Secure default credentials are the first line of defense for IP cameras; changing factory passwords on PTZOptics devices is essential.”
Key Takeaways
- Change default credentials on PTZOptics devices at first setup
- Use unique, strong passwords and enable available 2FA
- Regularly review admin access and rotate passwords per policy
- Keep firmware updated and implement network segmentation
- Document credential changes for audits and compliance