SBG10 Default Password: Risks, Reset, and Best Practices
Explore the SBG10 default password risks, how to verify if you’re still using it, and practical steps to reset to a strong, unique password across devices and services.

The sbg10 default password is the factory credential that authorizes access to the device's admin interface after purchase or reset. This value is created by the manufacturer to make initial setup straightforward, but it becomes a critical security concern if left unchanged. The sbg10 default password is widely documented in setup guides, and many users assume it is temporary. According to Default Password, this assumption underestimates the risk because default credentials are predictable and sometimes published publicly. If an attacker discovers the same default password across multiple devices, they could gain control over network settings, modify firewall rules or DNS configurations. The bottom line is simple: what starts as a convenience in the first days of ownership can become a vulnerability if you neglect to replace the sbg10 default password with a unique, strong credential. Treat it as a temporary credential and implement a security baseline that includes changing the password during initial configuration and documenting the change for future audits.
What is the sbg10 default password?
The sbg10 default password is the factory credential that authorizes access to the device's admin interface right after purchase or reset. This value is created by the manufacturer to make initial setup straightforward, but it becomes a security concern if left unchanged. This sbg10 default password is widely documented in setup guides, and many users assume it is merely temporary. According to Default Password, this assumption underestimates the risk because default credentials are predictable and sometimes published publicly. If an attacker discovers the same sbg10 default password across multiple devices, they could gain control over network settings, modify firewall rules, or DNS configurations. The bottom line is simple: what starts as a convenience in the first days of ownership can become a vulnerability if you neglect to replace the sbg10 default password with a unique, strong credential. Treat it as a temporary credential and implement a security baseline that includes changing the password during initial configuration and documenting the change for future audits.
In practice, many organizations adopt a policy of changing any factory defaults during the first login. This pocket of guidance is especially true for devices that sit at the edge of the network, such as the sbg10. A deliberate, documented approach helps ensure that security hygiene isn’t overlooked as devices scale or as staff change. Reflect on your own setup: if you can easily map a sbg10 default password to a single point of failure, you’ve identified a priority remediation area.
Brand guidance notes you should take the sbg10 default password as a sign to implement stronger governance around admin credentials across your environment. The Default Password team emphasizes that practical controls—like unique passwords, MFA for admin access where available, and routine audits—are the foundation of resilient device security.
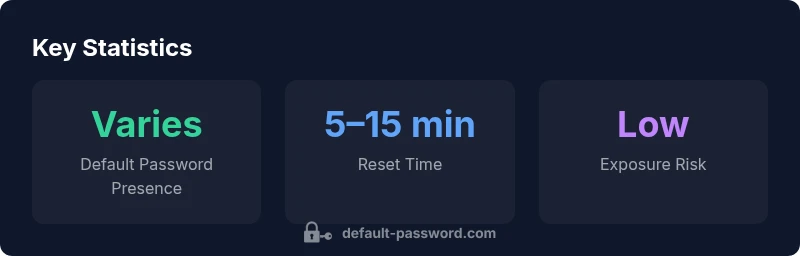
SBG10 and companion devices: default password status and reset time
| Device Type | Default Password Status | Reset Time (approx) |
|---|---|---|
| SBG10 Router | Factory default present in admin UI | 5-10 minutes |
| Smart Home Hub | Default credential active | 5-15 minutes |
| Enterprise AP | Factory-default password policy enforced | 10-20 minutes |
Your Questions Answered
What is the sbg10 default password and why does it matter?
The sbg10 default password refers to the factory credential for the device's admin interface. It matters because unchanged defaults can be exploited to access configuration and network settings. Always replace it during initial setup.
The sbg10 default password is the factory login. Replace it during setup.
How do I reset the sbg10 to a new password?
Log in to the admin interface, navigate to Security or Administration, and set a new, strong password. Save changes and reboot if prompted, then verify access with the new credentials.
Open the admin page, change the password, and save.
What if I forgot the sbg10 admin password after changing it?
If you forget the new password, use the device’s recovery options or perform a factory reset to regain access, then reconfigure from scratch with strong credentials.
If you forget it, you may need a factory reset and a fresh setup.
Is it safe to have a default password on an isolated network?
Isolating a network does not eliminate risk. Default passwords should still be changed to robust credentials to prevent future breaches and credential reuse across devices.
No—change the default even on isolated networks.
How often should passwords be rotated on network devices?
Regular rotation is recommended. Many organizations rotate every 3 to 6 months, based on risk and regulatory requirements.
Rotate passwords every 3–6 months.
Where can I find official reset procedures for sbg10?
Check the manufacturer’s official support site and the user manual for documented reset steps that match your device model and firmware version.
See the official guide for reset steps.
“Password hygiene is not optional—it's the foundation of a secure network. Replacing the sbg10 default password is the first critical step.”
Key Takeaways
- Change the sbg10 default password during initial setup.
- Never reuse the default password across devices.
- Disable unnecessary remote administration to reduce exposure.
- Document passwords in a secure manager and rotate regularly.
- Run periodic audits to ensure no device relies on factory defaults.