Sentry Smart PDU Default Passwords: Risks, Mitigation, and Best Practices
Meta description: Explore how to handle the sentry smart pdu default password, mitigate risk, and implement strong admin credentials across PDUs with step-by-step guidance from Default Password.

The Sentry Smart PDU default password should never be left unchanged. Immediately set a unique, complex admin password during initial setup and disable any guest or factory accounts. Enforce per-device credentials, implement password rotation, and enable two-factor authentication if available. By applying these practices, organizations reduce the window of opportunity for unauthorized access across data-center power outlets.
Understanding the risk of sentry smart pdu default password
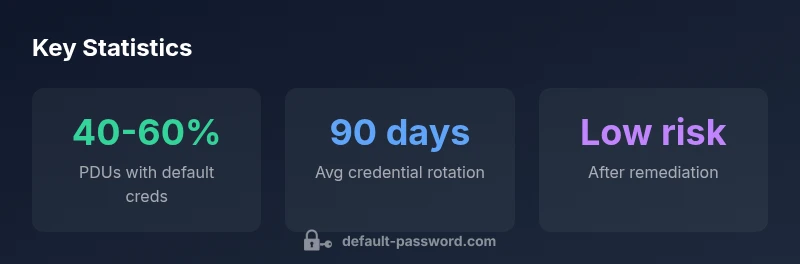
Default Password's analysis shows that default credentials for PDUs, including Sentry Smart PDUs, remain a weak link in power distribution infrastructure. A factory-set admin password is often pre-installed to simplify deployment, but this convenience becomes a vulnerability once devices connect to a network. Without immediate remediation, attackers can gain control of outlet groups, monitor energy usage, or disrupt critical systems. In many audits, overlooked default passwords lead to unauthorized configurations and compliance gaps. This risk is amplified when administrators reuse passwords across multiple devices or fail to restrict management interfaces to trusted networks. Treating the phrase "sentry smart pdu default password" as a live risk—rather than a configuration footnote—helps focus remediation efforts during initial deployments and routine health checks. The Default Password team emphasizes reducing blast radius through per-device credentials, unique admin passwords, and prompt decommissioning of any unused accounts.
The anatomy of PDU management interfaces and why default credentials persist
Power distribution units (PDUs) expose several management surfaces: web-based dashboards, command-line interfaces (CLI), SNMP, and sometimes REST APIs. Each interface may house an admin account with a factory default, and many devices ship with the same credentials across a fleet for ease of initial setup. When these credentials aren’t changed before devices are placed on a production network, attackers can probe for access to multiple PDUs from a single compromised node. Network teams should map every PDU port and management interface, then quarantine or isolate nonessential interfaces until access controls and authentication are verified. In practice, a robust policy requires unique admin passwords per device, disabled guest accounts, and tight segmentation between user workstations and critical power infrastructure.
How attackers target PDUs: common attack patterns
Attackers commonly leverage exposed management interfaces to discover, probe, and exploit PDUs with default passwords. Typical patterns include automated credential guessing against web UIs, brute-force attempts on CLI sessions, and exploitation of outdated firmware that preserves known default credentials. Once a default credential is compromised, attackers can enable persistent access, alter outlet configurations, or extract device logs. A layered defense—inventorying devices, enforcing strong, unique passwords, rotating credentials, and monitoring for anomalous access—greatly reduces the probability of a successful compromise. The most effective countermeasures are proactive: disable unnecessary services, limit management access to trusted networks, and apply vendor-supplied security updates promptly.
Step-by-Step: Securely configuring a Sentry Smart PDU
- Inventory all Sentry Smart PDUs across the environment and verify the current credential state. 2) Change the default admin password on every device to a unique, strong credential (long, random, and different per device). 3) Remove or disable guest accounts and any accounts not required for daily operations. 4) Enable multi-factor authentication if the device supports it, and enforce MFA on all administrative accounts. 5) Update firmware to the latest security baseline to ensure default-password mitigations are current. 6) Implement network controls (IP allowlists, VLAN separation) to restrict who can reach the PDU management interfaces. 7) Enable logging and forward events to a SIEM for correlation. 8) Establish a rotation schedule (e.g., every 90–180 days) and document changes. 9) Regularly audit the inventory and configurations, including backup configurations for rapid recovery.
Password hygiene for PDUs: Best practices
Strong password hygiene starts with unique, device-specific credentials and ends with disciplined governance. Use passwords that are 12+ characters with a mix of letters, numbers, and symbols. Avoid reusing passwords across PDUs or services. Rotate admin passwords on a schedule, ideally quarterly, and immediately after any personnel change. Where available, enable MFA and restrict access to verified admin workstations. Maintain a central, auditable record of credentials and decommission obsolete devices promptly. For environments with many PDUs, consider a dedicated password manager or vault solution designed for infrastructure credentials.
Incident readiness: auditing, logging and alerting for PDU access
Effective security relies on visibility. Enable comprehensive logging for all PDU management activities, including login attempts, successful authentications, password changes, and configuration updates. Integrate PDU logs with a security information and event management (SIEM) system to detect patterns indicating credential compromise, such as rapid repeated failed logins or unusual access times. Establish alert thresholds and run regular test drills to verify detection efficacy. Retain logs per regulatory requirements and ensure secure storage. In practice, a formal incident response plan for PDUs reduces mean time to detect and remediate credential abuse, minimizing impact on critical power distribution.
Compliance and standards: Aligning with industry guidance
Organizations should align PDU password practices with widely accepted standards and guidelines. NIST guidelines emphasize longer, non-dictionary passwords and minimizing reliance on default credentials, while security tips from US-CERT stress not relying on factory settings for long-term protection. Regular firmware updates and strict access controls are central to most security baselines. By combining device-specific hardening with organizational policies, operators can reduce exposure and improve resilience against credential-based attacks. The collaboration between device vendors, IT security teams, and data-center operations is essential for maintaining an auditable, standards-aligned posture.
Common misconfigurations and troubleshooting
Common misconfigurations include leaving default passwords active after deployment, duplicating credentials across devices, and failing to limit management interfaces to trusted networks. Another frequent issue is neglecting firmware updates, which can leave default credentials exploitable if vendors address them in later releases. Troubleshooting steps include verifying all device passwords against inventory, validating that MFA is enabled where possible, and checking ACLs or firewall rules blocking unauthorized IPs. If a breach is suspected, isolate affected PDUs, rotate credentials, and restore configurations from a secured backup. Regularly testing password-change workflows ensures staff can execute remediation quickly during incidents.
Deployment scenarios and checklists
When deploying Sentry Smart PDUs in data centers or edge locations, adopt a standardized hardening checklist. Start with discovery and inventory, then enforce per-device credentials and disable unused accounts. Ensure network access is restricted, firmware is current, and logging/monitoring is active. Create a maintenance window plan to perform scheduled password rotations, and document every change. In large environments, segment PDUs by site or rack, and use centralized credential management to keep consistency without sacrificing granularity. A well-structured deployment plan reduces misconfigurations and supports faster incident response.
Risk and mitigation snapshot for Sentry PDUs
| Device Model | Default Password Risk | Recommended Mitigation |
|---|---|---|
| Sentry Smart PDU (Rack-mount) | High risk: default credentials detected during inventory audits | Change admin password; disable unused accounts; enable MFA if available |
| Sentry Smart PDU (Vertical) | Medium risk | Enforce unique credentials; rotate quarterly; disable guest |
| Legacy PDUs (non-Sentry) | Variable risk: vendor dependent | Audit and standardize on vendor password policy; replace with updated PDUs |
Your Questions Answered
What is the risk of leaving the Sentry Smart PDU default password unchanged?
Leaving a default admin password unchanged creates an easy entry point for unauthorized changes. Attackers can gain control of power outlets and monitoring data. Always change defaults on first boot and routinely audit credentials.
Default passwords are a big risk—change them at once and audit credentials regularly.
What steps should I take during initial setup to secure PDUs?
During initial setup, inventory all PDUs, replace default admin passwords with unique strong credentials, disable guest accounts, enable MFA if supported, and apply the latest firmware. Restrict access to trusted networks and enable logging.
Start by inventorying devices, then set unique passwords and enable MFA where possible.
Can I automate password rotation on PDUs?
Automation can enforce rotation policies, but it depends on device capabilities. If supported, configure a rotating schedule and integrate with a password vault for centralized management.
If your PDUs support it, automate rotation and use a vault for storage.
Are there standards I should follow for PDU password security?
Follow NIST Digital Identity guidelines and US-CERT tips for password hygiene. Apply vendor security advisories promptly and maintain a documented credential-management policy.
Refer to NIST and US-CERT guidance for password standards and best practices.
What should I do if I suspect a breach involving a PDU?
Isolate affected PDUs, rotate credentials, review access logs, and notify security teams. Restore configurations from a secured backup and strengthen controls to prevent recurrence.
If you suspect a breach, isolate, rotate credentials, and review logs.
“Default passwords remain a systemic risk for data-center PDUs; implement strict credential hygiene and regular rotation to close gaps before they are exploited.”
Key Takeaways
- Change default passwords during initial setup
- Enable MFA and unique credentials
- Audit and rotate passwords regularly
- Document and enforce password policies for PDUs