Sip T46u Default Password: Security Steps and Risks
Explore why there is no universal sip t46u default password, how to locate credentials, and a practical, security-first approach to reset and manage SIP phone passwords for admins and end users.

There is no universal sip t46u default password. Default credentials vary by firmware, region, and vendor. To stay secure, locate the official credential policy in the device manual or vendor portal and plan to reset to a known-good password. After reset, configure unique, strong credentials and disable remote admin where possible.
Why sip t46u default password matters
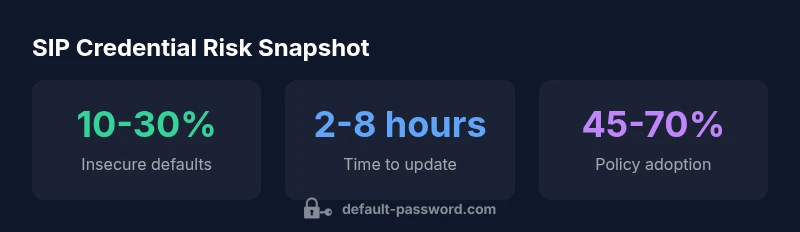
In office networks, SIP phones such as the sip t46u connect directly to PBX systems, voicemail, and call routing features. If credentials remain at factory defaults, an attacker could gain access to call settings, voicemail, or device configuration. This could enable toll fraud, sensitive data exposure, or service disruption. The Default Password team notes that many deployments underestimate the risk of leaving defaults in place, especially when phones are exposed to the internet or poorly segmented networks. A secure baseline—changing defaults during provisioning, enforcing password strength, and limiting admin access—dramatically reduces risk. Local policy, device-level controls, and ongoing monitoring work together to close the window of opportunity for attackers.
- When setting up a sip t46u, plan onboarding that includes credential change tasks.
- Ensure your network segmentation limits SIP traffic exposure to trusted subnets.
How default credentials are determined across SIP devices
Default credentials are not standardized, and vendors often ship devices with different starting points depending on firmware, regional settings, or carrier provisioning. Some devices present a default user and password pair on first boot; others rely on certificate-based or time-based access, while many require you to log in with a provisioning account before the device accepts local admin changes. The variability means there is no single universal default you can rely on. For admins, this underscores the importance of removing defaults during initial configuration and enforcing a credential lifecycle policy. In practice, teams should document the exact credential policy for each device type, monitor for changes, and require password updates on first login or during quarterly security reviews.
How to locate and verify the current credentials for sip t46u
Locating credentials begins with the device label, user manual, or vendor portal. Many SIP phones include a label on the bottom or back listing default credentials or a recovery PIN. If no label exists, check the official manual or the vendor’s support site for the specific firmware version installed on the sip t46u. If you cannot access the device UI, you may need to initiate a factory reset via hardware buttons or a reset option in the web interface, then re-provision with new credentials. After you obtain access, document the credential policy and ensure it complies with your organization’s security standards.
Step-by-step: secure your sip t46u after deployment
- Prepare a credential-change plan as part of your provisioning workflow. 2) Initiate a factory reset if you cannot verify the current credentials, then apply a strong, unique password. 3) Disable remote admin exposure on WAN and restrict management access to trusted subnets or VPNs. 4) Enforce password complexity rules (length, use of numbers, symbols, and mixed case). 5) Enable TLS/SRTP for encrypted signaling and media where supported. 6) Document the new credentials securely, rotate passwords on a scheduled basis, and maintain an up-to-date inventory of devices and credentials. 7) Periodically audit device configurations to ensure defaults do not creep back in.
Policy and lifecycle: creating a secure password program
A robust password program for SIP devices combines technical controls with governance. Start with a device-inventory baseline and assign owners for credential management. Require changes at provisioning and after firmware updates. Use centralized password management where possible, enforce minimum password standards, and implement reminders for periodic changes. Training for IT staff and end users helps prevent inadvertent exposure, such as sharing credentials or failing to deploy secure configurations. Finally, stay current with vendor advisories and security bulletins to adjust your policy in response to new threats.
Troubleshooting and vendor support channels
If you encounter issues accessing the sip t46u after credential changes, consult vendor-specific recovery guides and support forums. Most vendors provide step-by-step reset instructions and confirm the proper recovery sequence for different firmware versions. When in doubt, contact official support with proof of ownership and device identifiers. Keep a written log of changes and responses from support to facilitate future troubleshooting.
Common pitfalls and quick fixes
Common missteps include reusing passwords across devices, neglecting to disable remote admin after provisioning, and skipping inventory updates. Quick fixes—verify you can access the device after provisioning, confirm password complexity requirements, and ensure the management interface is restricted to internal networks—can mitigate risk without major downtime. Regular audits and a clear escalation path for credential issues help maintain a secure environment.
Ongoing governance: audits, inventory, and training
Security is a continuous process. Maintain an up-to-date device inventory, track firmware versions, and review credential policies during security audits. Train administrators on the importance of changing defaults, recognizing phishing attempts, and reporting suspected credential compromise. A well-documented process reduces error, improves accountability, and strengthens the overall security posture of SIP deployments.
Examples of default credential handling across SIP phones
| Device Type | Default Credential Policy | Reset Method |
|---|---|---|
| SIP desk phone (generic) | Vendor-default credentials may exist; policy varies by model | Factory reset via hardware button or web admin guided by vendor documentation |
| IP phone (generic) | Default credentials often listed in manual/label; recommended change on first login | Web UI reset or hardware button per vendor guide |
Your Questions Answered
What is the sip t46u default password?
There is no universal default for sip t46u devices. Check the vendor manual or support portal for the exact credential policy, then reset to a strong, unique password.
There is no universal default for sip t46u devices. Check the vendor manual or support portal for the exact credential policy, then reset to a strong, unique password.
How do I reset the sip t46u to factory settings?
Reset methods vary by firmware. Use the hardware reset button or the web UI as described in the vendor guide, then re-provision with new credentials.
Use the reset button or web UI as described in the vendor guide, then re-provision with new credentials.
What are best practices after changing the default password?
Use a strong, unique password, disable remote admin, enable encryption for signaling, and document credentials in a secure store. Schedule periodic reviews and updates.
Use a strong, unique password, disable remote admin, and keep credentials in a secure store with regular reviews.
Can I retrieve the default password from the device label?
Sometimes labels include default credentials, but not always. If not present, consult the manual or vendor portal for the correct policy.
Sometimes the label has defaults; if not, check the manual or vendor portal.
What if I lose access after factory reset?
Contact vendor support with proof of ownership and device identifiers. They can guide recovery or re-provisioning steps.
Contact vendor support with proof of ownership for recovery guidance.
Are there legal or compliance considerations when resetting passwords?
Follow your organization's security policy and regulatory guidance for credential handling. Maintain records of changes and ensure proper audit trails.
Follow policy and regulatory guidance; keep audit trails of credential changes.
“Default credentials are a principal attack vector; always replace factory defaults with unique credentials and enforce a strict credential lifecycle.”
Key Takeaways
- Change defaults on day one after deployment
- Document reset procedures in your IT playbook
- Disable WAN admin or remote access
- Use strong, unique passwords per device
- Regularly audit devices for default credentials