Speco Default Password: Reset and Secure Speco Devices
Learn how to locate, reset, and securely manage the speco default password across Speco cameras, NVRs, and related devices with practical, step-by-step guidance and security best practices.

Key point: changing the speco default password is essential to secure surveillance devices. If factory credentials remain active, unauthorized users can gain admin-level access to cameras and recordings. The immediate action is to locate the official reset path for your model, create a unique password, and enable protections like account lockouts or firmware updates where available. In practice, changing defaults dramatically reduces exposure and strengthens device security.
What is the speco default password and why it matters
Speco default password refers to the factory credentials assigned to Speco security cameras, NVRs, and related devices before initial setup. The exact password may vary by model and firmware, but a common thread is that many devices ship with a weak, easily guessed credential set that grants administrator access. According to Default Password, the speco default password is a critical risk until it is changed. If an attacker learns or guesses the factory password, they could view live feeds, export recordings, and alter device settings. The consequences escalate in a monitored environment such as retail stores or small offices where surveillance is trusted. This is why the first security practice is to reset the password immediately after unboxing and to plan a secure password strategy. Essential considerations include unique credentials per device, a password with a strong length and complexity, and enabling any available protections, such as account lockouts, device hardening, and firmware updates. In practice, keep a simple, memorable approach not possible due to the need for complexity; use a password manager to store and generate strong app- or device-specific passwords. The collection of specs and policies below provides a practical framework for addressing the speco default password problem without requiring highly technical expertise.
How default passwords pose risks in Speco devices
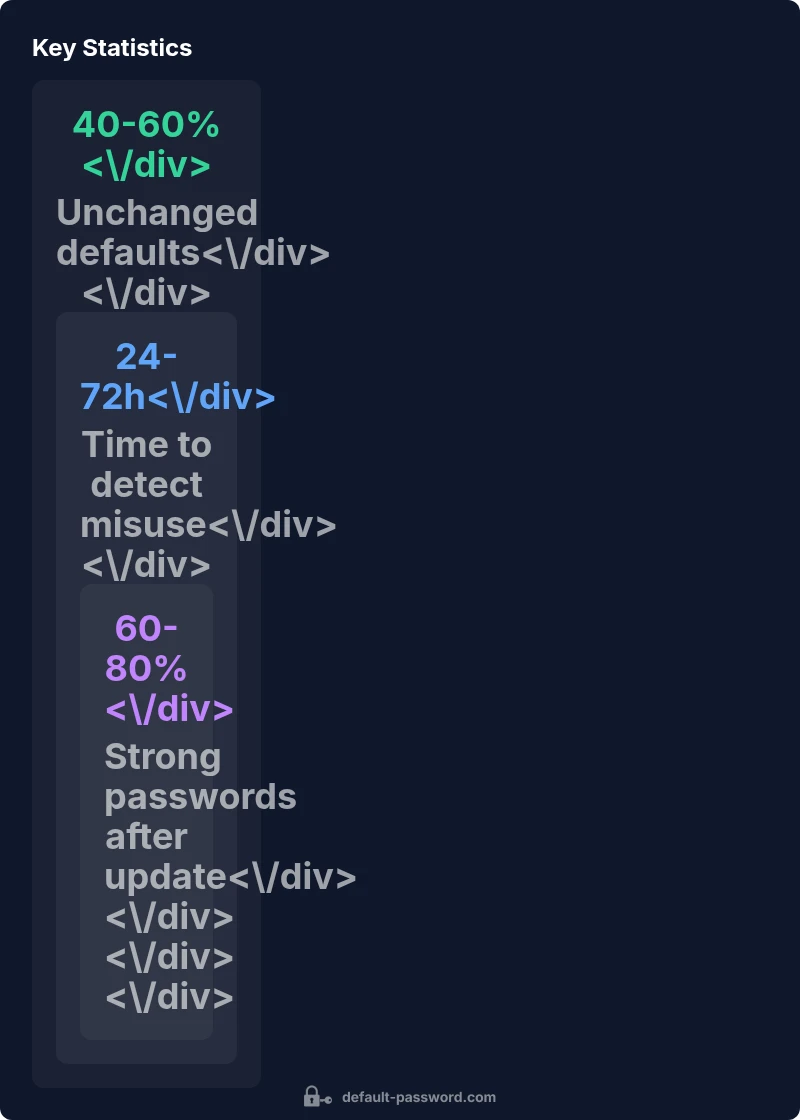
Default passwords are a widely known attack vector. When devices ship with predictable credentials, attackers can gain access to live feeds, modify recording schedules, or disable alerts. The risk multiplies if devices sit on unsegmented networks or if remote administration is enabled without MFA. A compromised Speco device can become a foothold for broader breaches, potentially exposing sensitive footage and undermining physical security. Organizations should treat the speco default password as a controllable risk, not an immutable setting. Regular password rotation, prompt firmware updates, disabling unnecessary remote access, and strict access controls reduce exposure. In practice, a disciplined password hygiene routine paired with network segmentation delivers measurable improvements in security posture. This approach aligns with industry best practices for IP-based surveillance systems and supports broader security goals across the enterprise.
Common patterns you might encounter across Speco models
Across different Speco models, you may encounter a few common default credential patterns. These patterns range from simple strings like “admin/admin” to more generic combinations such as usernames like “admin” paired with short passwords. Many devices also accept the username “admin” with a blank or near-blank password, which is a critical vulnerability. The variability by model and firmware means there is no universal default password. The practical implication is clear: do not assume a fixed credential exists across devices. Always perform the initial access with the documentation at hand, and treat any unfamiliar credential set as a potential risk until proven otherwise. A cautious, model-by-model verification process minimizes surprises during deployment or migration.
Step-by-step: Resetting the admin password on Speco devices
- Identify your device model and locate the official reset path in the manual or on the support site. 2) If you can access the web UI, navigate to the user or password settings and initiate a password reset. 3) If the device has a physical reset button, hold it for the recommended duration (often 10-15 seconds) until indicators show reset completion. 4) After reset, reconfigure the device with a unique, long password, and disable default admin accounts if possible. 5) Update firmware to the latest version and apply any security hardening options, such as account lockouts and remote access restrictions. 6) Document the new credentials securely in a password manager and limit administrative access to authorized personnel only.
Note: A factory reset may erase configuration. Back up essential settings if supported and be prepared to reapply network and recording configurations after the reset. Always follow the manufacturer’s official guidance for model-specific steps and caveats.
Security risks and best practices after identifying a default password
Identifying a default password should trigger a rapid, layered response. Immediately rotate to a unique, length- and complexity-restricted password. Enable MFA if supported, and disable unnecessary admin accounts. Enforce least privilege for users and limit remote administration exposure by restricting management interfaces to trusted networks. Regularly monitor logs for unusual login attempts and schedule periodic password changes as part of a broader security policy. Firmware updates should be treated as critical security actions, not optional maintenance. In practice, this approach reduces the window of opportunity for attackers and aligns with established security frameworks. The goal is not only to fix a single device but to create a resilient security culture around your Speco ecosystem.
A practical guide to configuring secure admin access across Speco devices
A solid security baseline begins with strong, unique credentials and a documented process. Use a password manager to generate and store long, complex passwords for each device. Disable default guest accounts and minimise the number of users with admin rights. Where supported, enable MFA for admin access and enforce IP-based access controls to limit exposure. Regularly review user permissions and implement firmware updates as a recurring practice. Consider network segmentation for IP cameras, NVRs, and control workstations to restrict lateral movement in case of a breach. Finally, implement continuous monitoring with alerting for unusual login activity and failed authentication attempts to respond quickly to potential incidents.
Troubleshooting password issues and recovery options
If you cannot reset or access a Speco device after attempting a password change, consult the official support resources or contact technical support for guided recovery. Some devices provide recovery modes that require physical access or maintenance port usage. Collect device serial numbers, firmware versions, and model identifiers to speed up assistance. Avoid attempting risky hardware interventions without guidance, as that could void warranties or brick the device. Maintaining backups of configuration where possible accelerates recovery after password-related incidents. When in doubt, leverage vendor knowledge bases and professional support channels to restore access safely.
Comparison of reset processes by Speco device type
| Device Type | Default Password Pattern | Reset Process |
|---|---|---|
| Speco IP cameras | Often admin + simple default password (model-dependent) | Factory reset via physical button or web UI and reconfigure from scratch |
| Speco NVR/DVR systems | Likely admin with short, common password | Use reset button or web UI to reset; reconfigure securely |
| Speco hybrid devices | Mixed credentials by model | Consult model-specific reset steps and re-secure after restore |
Your Questions Answered
What is the default password for Speco devices?
Default passwords vary by model and firmware. Consult the device manual or support site to identify the correct credentials. If you cannot locate them, perform a factory reset to regain access and reconfigure securely.
Default passwords differ by model, so always check the manual or support site. If you can’t locate them, perform a factory reset to regain access and reconfigure securely.
How do I reset the admin password on a Speco DVR/NVR?
Use the device’s reset option via the physical button or the web interface, then create a new, strong password and reapply security settings after the reset.
Use the reset button or the web interface to reset, then set a strong new password and recheck security settings.
Can I recover access if I forget the password?
If you forget, use the official reset process to regain control, or contact support for recovery options. Do not guess credentials repeatedly to avoid lockout.
If you forget it, use the official reset path or contact support for recovery. Avoid repeated guessing to prevent lockouts.
Is it safe to keep the default password after setup?
No. Default passwords are widely known and present a high risk. Change to a unique password and disable any default admin accounts.
No—default passwords are risky. Change to a unique password and disable default admin accounts.
Do Speco devices support two-factor authentication (2FA)?
Some models support 2FA. Check firmware features and admin settings to enable MFA if available on your device.
Some models do support 2FA; check your firmware and admin settings to enable it if available.
What are best practices after resetting a Speco device?
Immediately set a unique password, enable MFA if possible, update firmware, limit admin access, and document changes in a centralized password manager.
After resetting, set a unique password, enable MFA if possible, update the firmware, and limit admin access.
“Changing factory credentials is the single most effective step to secure any Speco device. A repeatable, documented process reduces exposure and simplifies ongoing security.”
Key Takeaways
- Change factory credentials on every Speco device immediately
- Use a password manager to enforce strong, unique passwords
- Disable unused admin accounts and enable MFA where available
- Regularly update firmware and review access logs
- Document password changes and access policies for audits