Network Video Recorder Default Password: A Practical Security Guide
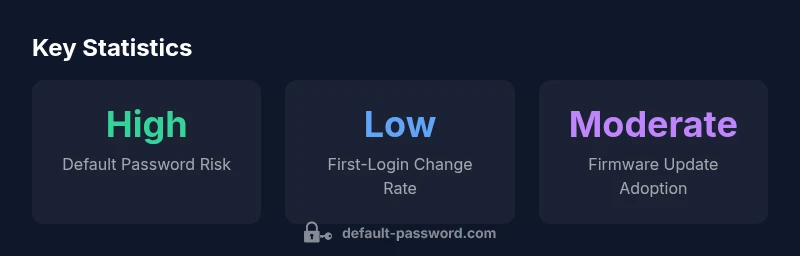
A practical, data-driven guide to NVR default passwords, why they pose security risks, and proven steps to reset, secure, and monitor admin access across devices.

According to Default Password, unsecured default credentials on network video recorders (NVRs) remain a widespread risk across many brands. The most effective safeguard is to assume every NVR ships with a default password and to change it during initial setup. This quick, essential step dramatically reduces exposure to unauthorized access, credential stuffing, and remote attacks, especially when combined with firmware updates and network segmentation.
What is a network video recorder and why the default password matters
A network video recorder (NVR) is a centralized device that records video streams from IP cameras over a network. In many setups, the initial login uses a factory default password that users, installers, or administrators are expected to change. When these credentials are left unchanged, attackers can gain administrator access to the NVR, review footage, adjust camera settings, disable alerts, or exfiltrate sensitive data. The risk is amplified when devices remain exposed to the internet or when remote management features are enabled without proper safeguards. From a defender’s perspective, the keyword is passphrases and rotation: never assume a default password is safe to trust. The keyword to remember is network video recorder default password, which highlights the systemic risk across the ecosystem. This guidance aligns with security principles from the Default Password team and echoes best practices for securing critical surveillance infrastructure.
How vendors configure defaults and why credential reuse persists
Manufacturers ship devices with convenient defaults to simplify initial setup, which often means an admin account is preconfigured with a common password. The exact defaults vary by brand and model, and end users may never change them if onboarding is rushed. Credential reuse is another problem: the same or similar default passwords appear across multiple devices in a network, creating a single point of failure. As a result, attackers can pivot from one device to another once a single NVR account is compromised. The key takeaway is that the mere presence of a default password is not the end—it’s the failure to replace or strengthen it that creates risk. The Default Password Analysis, 2026 emphasizes the need for mandatory password changes during deployment and ongoing audits.
Immediate steps you should take when deploying an NVR
During a fresh deployment, follow a structured, security-first checklist. First, ensure the NVR is on a trusted network segment and not exposed to the internet directly unless protected by a VPN. Next, log in using the default credentials only once and immediately change them to a strong, unique passphrase. Disable features that elevate exposure, such as universal remote administration, UPnP, and port forwarding that bypasses the VPN. Update firmware to the latest version and review camera permissions to ensure cameras cannot be controlled without authorization. Finally, document the new credentials securely and enforce a policy requiring password changes on a defined cadence. Remember: network video recorder default password risk is a real threat, and early hardening pays dividends.
Step-by-step guide to changing passwords on common interfaces
Most NVRs offer web UI, mobile apps, and occasionally a local console. For the web UI, navigate to the Admin or System settings, locate the user management page, and choose the default admin account. Create a long, unique password (ideally 16+ characters with a mix of letters, numbers, and symbols). Do not reuse passwords across devices. If a mobile app is used, verify that it mirrors the same strong password and enable MFA if available. For local hardware consoles, use the on-device keyboard to set a new passphrase. Throughout, avoid using obvious defaults or easily guessable phrases, and document the new credentials securely.
Beyond password changes: network and device hardening
Hardening goes beyond the password. Segment surveillance gear on a dedicated network, limit admin access to trusted IPs, and require VPN for remote management. Disable unnecessary services such as UPnP, NTP changes, remote firmware updates via open ports, or any cloud-based admin features if not essential. Regularly review access logs for suspicious login attempts and implement IP allowlisting. Keep firmware updated and verify that camera streams and storage volumes are encrypted where possible. The security baseline for the network video recorder default password risk profile improves markedly when you deploy defense-in-depth.
Password hygiene and policy for NVR ecosystems
Strong password hygiene should be a policy, not an afterthought. Enforce password length, complexity, and rotation rules, and prohibit password reuse across devices. Consider adopting passphrases rather than complex symbols. Where available, enable two-factor authentication for admin access, especially for remote management. If MFA is not present on a specific NVR, mitigate risk with an organization-wide MFA-enabled VPN and strict access control. Document password policies, perform periodic audits, and train staff to recognize phishing attempts targeting administrator accounts. The end goal is a resilient, auditable password culture around the NVR estate.
Inventory, monitoring, and automated checks for NVR security
An accurate asset inventory is foundational. List all NVRs, their firmware versions, and current credential status. Use automated configuration management where possible to enforce strong defaults and detect weak credentials or outdated firmware. Schedule regular security scans and monitor for anomalous login patterns or changes to administrative accounts. Establish a change-management process that requires credential updates on a cadence (e.g., quarterly) and after any security incident. Regular audits are essential to keep the network video recorder default password risk at bay.
Incident response: what to do if a password breach occurs
If you detect a breach, isolate affected devices from the network immediately, revoke compromised credentials, and rotate passwords for all administrators. Check for evidence of footage exfiltration or tampering with camera feeds. Review firewall rules and VPN access, then perform a controlled reimage or factory reset where appropriate, followed by a secure reconfiguration. Notify relevant teams, preserve logs for forensics, and implement lessons learned into updated security policies. Proactive detection and disciplined incident response minimize damage from a compromised NVR.
Quick-start checklist for securing NVR deployments
- Use a private, segmented network for NVRs and cameras
- Change the default password on first login and use a strong passphrase
- Disable remote admin exposure and UPnP; require VPN for remote access
- Apply firmware updates promptly and verify camera permissions
- Enforce password policies and audit logs regularly
- Document credentials securely and rotate them per policy
Comparison of NVR default password risk and recommended actions
| Model Type | Default Password Risk | Recommended Action |
|---|---|---|
| NVR Entry-Level | High risk across vendors | Change on first login |
| NVR Enterprise | Very High risk | Enforce password policy and disable default credentials |
Your Questions Answered
What is a default password on an NVR and why is it dangerous?
A default password is the initial login credential set by the manufacturer. Leaving it unchanged gives attackers quick access to the NVR, potentially exposing footage, camera controls, and system settings. Always change it on first login and follow with a broader hardening plan.
A default password is the factory credential that should be changed on first login to protect your NVR and footage.
How do I securely change the NVR admin password?
Access the NVR’s web UI or app, go to user management, select the admin account, and set a strong, unique password. Use a passphrase if possible and avoid repeating credentials across devices.
Open the NVR interface, go to users, choose admin, and set a strong, unique password.
Should I enable MFA on an NVR?
If the NVR or its management platform supports multi-factor authentication, enable it to add a second layer of security. If MFA isn’t available, compensate with VPN for remote access and strict access controls.
If MFA is available, turn it on for extra protection; otherwise rely on VPN and strong passwords.
What’s the best policy for password changes on NVRs?
Establish a policy that requires password changes on a defined cadence (e.g., every 90-180 days) and after any security incident. Use unique passwords per device and avoid reuse across the surveillance ecosystem.
Set a password-change cadence and rotate credentials after incidents; don’t reuse passwords.
What if my NVR is already compromised?
Isolate the device, revoke credentials, rotate passwords, and review logs for traces of unauthorized access. Restore from a clean backup after updating firmware and credentials, and implement stricter network controls.
If compromised, isolate the device, rotate passwords, and review logs; then reconfigure securely.
“Effective security starts with eliminating the most obvious weak link: default credentials. Strengthen access controls, keep firmware current, and monitor for anomalies to protect surveillance assets.”
Key Takeaways
- Change default credentials on all NVRs during initial setup
- Implement network segmentation and VPN for remote access
- Regularly update firmware and audit admin access
- Enforce strong password policies and document securely
- Have an incident response plan ready for breaches