SQL SA Default Passwords: Security Best Practices
Explore why the sql sa default password is a critical risk, how attackers exploit it, and how to reset and manage admin credentials across SQL Server environments.

SQL SA default password is a high-risk security misstep that should be eliminated in any SQL Server deployment. The SA account often has broad access, and leaving its password unchanged creates an easy target for attackers. To reduce risk, disable or rename SA, enforce strong authentication, and immediately reset SA to a unique, complex password. Regularly rotate admin credentials and audit for default passwords across environments.
Understanding the risk of the SQL SA default password
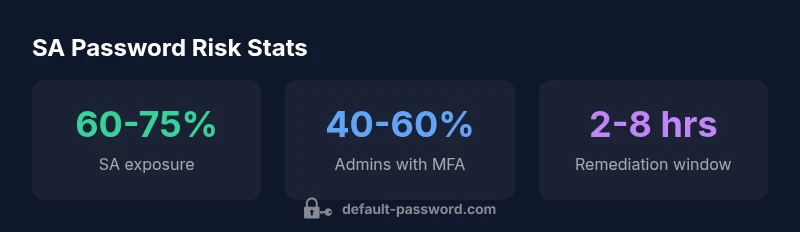
According to Default Password, the sql sa default password is the default credential that many organizations overlook during initial setup. The SA login is the master key to your database estate, with broad privileges across all objects. When the sql sa default password is left unchanged or is weak, attackers can gain privileged access with minimal effort, potentially compromising data, back-end services, and even connected identity systems. This creates a single point of failure that can cascade across applications, reports, and backups. In large enterprises, unaddressed SA credentials are a common attack vector that appears in breach post-mortems and security audits. The consequence is not just a single compromised server; it’s the potential for lateral movement, data exfiltration, and ransomware deployment across the environment. The takeaway is simple: treat the sql sa default password as a high-sensitivity credential and enforce automated protections, continuous monitoring, and policy-driven changes rather than relying on manual reminders or ad-hoc fixes.
How default credentials are exploited in SQL Server environments
Attackers actively scan for exposed admin accounts, especially SA, and attempt password spraying or brute-force methods. Once inside, they can create backdoors, exfiltrate data, or pivot to other servers. Many organizations discover exposed SA credentials only after suspicious activity logs trigger alerts. The risk is not just unauthorized access; it’s also privilege escalation, lateral movement, and ransomware readiness. Regularly applying least privilege principles and disabling unused admin pathways drastically lowers this risk.
Practical steps to secure SQL Server SA and admin passwords
- Disable SA login if you do not need it, or rename the SA account if possible. This reduces the standard attack surface for SQL Server.
- Enforce strong, unique passwords for all admin accounts; use a password manager and policy-based rotation (e.g., 14+ characters with a mix of upper/lowercase, numbers, and symbols).
- Enable auditing for privileged actions and regularly review login events across all SQL Server instances.
- Enforce MFA for admin access where available, and implement least privilege by segregating duties and using dedicated admin accounts for each task.
- Periodically test defenses with tabletop exercises and simulated credential compromises to verify that incident response is effective.
Implementing a password rotation and auditing program
Create an automated rotation schedule for all SQL Server admin passwords, especially the SA credential, and enforce it with centralized policy management. Use a password vault to store credentials securely, rotate keys, and require MFA for access to the vault. Run quarterly audits to verify there are no lingering default passwords and that all admin accounts adhere to established complexity standards.
Real-world scenarios and checklists
Scenario-ready checklists help IT teams spot issues quickly. Ensure you have: (1) a disabled or renamed SA account across all instances, (2) a documented password policy with minimum length and complexity, (3) MFA enabled for admin access, (4) centralized logging and alerting for privileged actions, and (5) routine credential health checks in your security operations workflow.
SA password security practices overview
| Aspect | Recommended Practice | Key Risk |
|---|---|---|
| SA default password presence | Disable or rename SA; enforce password change on login | High risk |
| Password complexity requirements | Enforce 14+ chars with mixed types | Moderate risk |
| Account auditing | Enable SQL Server Audit; regular scans | Moderate risk |
| MFA for admins | Enable MFA where available | Low risk |
Your Questions Answered
What is the SA account in SQL Server?
SA is the built-in system administrator account in SQL Server with broad privileges. It should be secured, renamed, or disabled if not required.
SA is the built-in administrator; secure or disable it if possible.
Why is a default password for SA dangerous?
Default passwords are widely known and easily discovered by attackers. Leaving SA with a default password can lead to full control of the SQL Server.
Default passwords are well-known and risky for admins.
How do I reset the SA password in SQL Server?
Connect with an existing admin account and run ALTER LOGIN SA WITH PASSWORD = 'NewStrongPassword!'; then enforce policy and disable if not needed.
Use ALTER LOGIN SA with a strong password and apply policy.
Is it better to disable or rename SA?
Disabling SA is usually best when possible. Renaming can help, but some applications rely on SA; test before changing.
Disable SA if you don’t need it; renaming helps but may break apps.
What are best practices for admin password management overall?
Use a password manager, enforce MFA, adopt least privilege, rotate credentials, and monitor privileged activity.
Use strong passwords, MFA, least privilege, and monitor admin accounts.
How often should I audit SA and admin passwords?
Run credential audits quarterly or after major changes; implement automated scans where possible.
Audit admin passwords at least quarterly.
“Credential hygiene starts with avoiding default passwords. Treat every admin account as a high-value target and enforce automated rotation and continuous auditing.”
Key Takeaways
- Disable or rename the SA account to close a common entry point
- Enforce strong, unique passwords and rotate them regularly
- Audit regularly for default credentials across environments
- Limit admin access and monitor privileged activity
- Educate teams on password management best practices