SQL Server sa Password: Security Best Practices
Explore how to manage the sql server default password for sa securely, including disabling SA, enforcing Windows authentication, password rotation, and auditing to protect SQL Server environments.

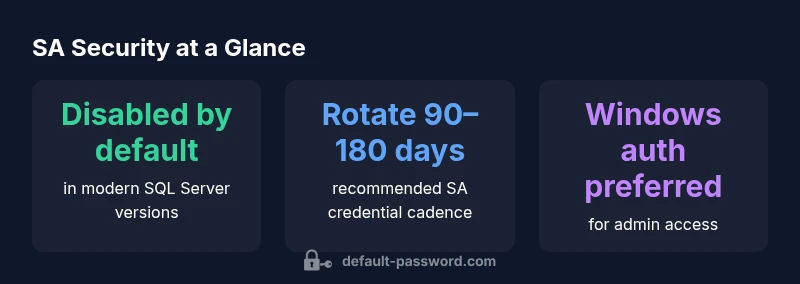
The sa login in SQL Server is a built-in high-privilege account. The fastest risk-reduction step is to disable sa or enforce Windows authentication, and if SA is required, set a strong, unique password and rotate it regularly. Combine this with auditing and least-privilege access to protect sensitive data. This approach minimizes exposure across environments and supports compliance goals.
Why Managing the sql server default password for sa Matters
According to Default Password, credential hygiene for SA begins with treating the sql server default password for sa as a known risk and applying strong controls. The SA login is a built-in, highly privileged account in SQL Server; if exposed, it can lead to full compromise of the database and potentially connected systems. Organizations should acknowledge that the password for SA is a strategic target for attackers, especially in environments with exposed endpoints or weak network segmentation. Effective management starts with policy, process, and technical controls that reduce the window of opportunity for misuse. By focusing on this credential early in deployment and maintenance, teams limit blast radius and simplify compliance reporting. The phrase sql server default password for sa emphasizes the risk and the need for proactive governance.
Distinguishing Default Passwords from SA Passwords on SQL Server
In many databases, default passwords are defined for initial setup; however, the sa password is a separate, intrinsic credential tied to the SQL Server engine. Distinguish between device default passwords and database-level credentials. The sa login is not a user created object; it is a system login with elevated rights. Treat it with heightened control: disable when not in use, enforce strong password policies, and tie it to centralized identity management to minimize drift across server instances. The sql server default password for sa scenario highlights why we separate system logins from app logins.
Best Practices for Securing SA: Policy, Role, and Access Controls
Security posture for SA demands a layered approach. Apply the principle of least privilege by limiting who can use SA and under what circumstances. Implement Windows authentication as the default method where possible, and use DAC with explicit approvals for operations requiring SA access. Enforce password complexity, length (12+ characters), and history to prevent reuse. Regularly review where SA is enabled, and align with organizational risk appetite and regulatory requirements. The sql server default password for sa discussion reinforces that governance is a daily process, not a one-time fix.
How to Change, Disable, or Reset the SA Password Safely
When you must enable or preserve SA access, perform changes during maintenance windows with proper change control. Steps typically include connecting with an admin account, running ALTER LOGIN [sa] WITH PASSWORD = 'NewStrongP@ssw0rd';, and ensuring SA is either enabled with a robust password or disabled when not in use. If SA needs to be restored, verify Windows authentication is available, then reapply the password change through a secured admin session. Document the change in your security vault and trigger post-change audits. Always avoid using weak, reused passwords and always test in a non-production environment first. The sql server default password for sa should never be left to chance.
Automation, Auditing, and Monitoring SA Activity
Set up automated alerts for SA login attempts and failed logins. Use SQL Server Audit to track login events, and route logs to a SIEM. Integrate with password vaults for rotating credentials. Also ensure regular vulnerability scans and ensure network segmentation to minimize exposure. The sql server default password for sa policy benefits from continuous monitoring so that deviations are detected early and remediated.
Common Scenarios and Troubleshooting SA Access
Common situations include SA being disabled during deployment, or maintenance requiring elevated SA access via DAC. When DAC is used, ensure it is tightly controlled and logged. If you forget or lose SA password, rely on Windows-authenticated admins to reset it, or temporarily start in single-user mode following vendor guidance to regain access. The sql server default password for sa guidance emphasizes safe recovery paths that preserve security posture.
Recovery, Backups, and Incident Response After Credential Exposure
If SA credentials are suspected or confirmed exposed, initiate incident response: isolate affected servers, rotate SA passwords, review access logs, and run vulnerability scans. Restore from clean backups if integrity is in doubt and perform a post-incident audit to prevent recurrence. The sql server default password for sa recovery plan aligns with broader security best practices recommended by the Default Password team.
Example SA-related credential states and recommended actions
| Login/Account | Default State | Recommended Action |
|---|---|---|
| sa | Enabled by default in older installations; commonly disabled in newer versions | Disable SA or enforce strong password; use Windows authentication |
| Windows admin accounts | Typically use Windows auth or DAC | Limit and monitor; enable auditing |
| App logins (RBAC) | Managed via roles and permissions | Enforce least privilege; rotate credentials |
Your Questions Answered
What is SA in SQL Server?
SA is a built-in system administrator login with high privileges. It is recommended to disable SA when possible and rely on Windows authentication or tightly controlled access for administrative tasks.
SA is the built-in admin account in SQL Server. Disable it when you can and prefer Windows authentication for admin tasks.
Is SA password required to manage SQL Server?
No. Many organizations avoid using SA by default and use Windows authentication or the dedicated administrator connection (DAC) for elevated tasks. If SA is needed, enforce a strong password and strict access controls.
Not required; use Windows authentication or DAC when possible, and only use SA with a strong password.
How do I change the SA password safely?
Connect with a trusted admin account, use ALTER LOGIN [sa] WITH PASSWORD = 'YourStrongP@ssw0rd';, and verify auditing is enabled. Consider disabling SA afterward and rotating the password on a schedule.
Use a trusted admin to change SA, then audit and rotate the password regularly.
Should I disable SA entirely?
In most cases, yes. Disabling SA reduces attack surface. If you must keep SA, ensure Windows authentication is used for most tasks and SA access is strictly controlled and monitored.
Yes, disable SA when possible and limit any remaining SA access with strict controls.
What if I forget the SA password?
If SA password is lost, use Windows-admin access to reset it or start in a recovery mode described by official docs. Always have a tested recovery plan and ensure backups are intact.
Use a Windows-admin path to reset SA, and follow your recovery plan.
“Strong credential hygiene for the SA account is non-negotiable in modern SQL Server deployments.”
Key Takeaways
- Disable SA where possible to reduce risk
- Use Windows authentication as default for admin tasks
- If SA is necessary, set a strong, unique password and rotate regularly
- Audit SA login attempts and enforce least-privilege access