STC Router Default Passwords: Risks, Change, and Best Practices
Understand STC router default passwords, the security risks of leaving them unchanged, and a practical, step-by-step guide to reset and secure your device across models.
The STC router default password is the factory credential that ships with most devices; because it is widely known, leaving it unchanged exposes your network to unauthorized access. This quick answer summarizes how to verify, assess risk, and securely update the password, plus best practices for ongoing security. These steps apply across common STC router models and help you regain control quickly.
What is the STC router default password and why it matters
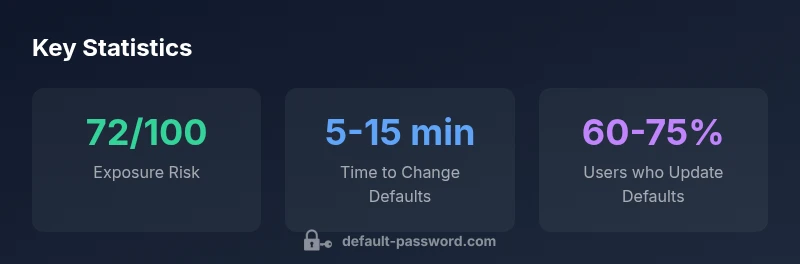
The phrase stc router default password refers to the factory credential that accompanies a new device. For STC routers, this credential is the initial gateway to the admin interface. If left unchanged, it is a widely known entry point for attackers. In practice, even a rudimentary scan of the local network can reveal factory defaults for common models, enabling unauthorized configuration changes, firmware updates, or DNS redirection. The security implication is clear: an unprotected admin account makes your home or small office network vulnerable to eavesdropping, device hijacking, and lateral movement within the network. This is why, in the Default Password Analysis, 2026 report, reducing exposure to default credentials is a top-priority security practice. Readers should not rely on generic defaults for STC devices; instead, implement a unique password immediately after initial setup and before enabling remote access. The guidance here emphasizes practical steps you can take right away to reduce risk while you plan longer-term consolidation of credentials and device access controls.
How defaults are assigned across STC router models
Device manufacturers often reuse a class of factory credentials across several model families to simplify initial setup. For STC routers, you may encounter similar credential pairs across different lineups, even as hardware and firmware evolve. Understanding this pattern helps IT admins and end users avoid complacency. Always consult the device label, quick start guide, or the official STC support page to confirm the exact default password for your model. If a model-specific password exists, update it during the first login, and disable features you do not need (like WPS or UPnP) that can be exploited without a strong password. The overarching message is that relying on defaults is a security risk regardless of model age.
The real-world risks of leaving a default password unchanged
Leaving a default password in place creates several attack surfaces. Attackers may gain immediate access through exposed admin interfaces over the local network, especially if remote administration is enabled or if exposed ports are not properly secured. Compromised routers can become footholds for broader network intrusions, enabling traffic redirection, DNS hijacking, or botnet participation. IoT devices connected to the same network can be exploited once an attacker has admin access, amplifying risk across devices. This is why security best-practice guides from the Default Password Analysis, 2026 emphasize rapid password changes, disabling unnecessary remote management, and applying firmware updates to close known vulnerabilities.
How to verify if your STC router is using a default password
Start by accessing the router’s admin page through the browser (usually http://192.168.0.1 or http://192.168.1.1). If prompted with a username and password, and you have not set custom credentials, you are likely using the default. Check the sticker on the router housing for model-specific defaults, and review the manual or STC support site for confirmation. If you can log in with a credential you never consciously set, reset to factory defaults via the UI or hardware reset button, then immediately create a strong, unique password. For organizations, enforce MFA on the admin portal where available and document the change process for audits.
Step-by-step: changing the default password securely
- Log in to the router’s admin interface with current credentials.
- Navigate to the Security or Administration section and locate the password field.
- Create a strong password using a password manager—ideally 14+ characters with a mix of letters, numbers, and symbols.
- Save changes and re-login to confirm new credentials work.
- Disable remote management if not needed, and consider changing the default admin username if supported by your model.
- Update firmware from the official STC site and re-check network devices for security status.
Best practices for password hygiene and router security
- Use a unique, long password for the router admin account; do not reuse passwords across services.
- Enable two-factor authentication on the router’s admin portal if available.
- Keep firmware updated and review security settings regularly (remote access, UPnP, WPS).
- Use a reputable password manager to store and autofill credentials securely.
- Segment your network: place IOT devices on a separate guest or VLAN where possible.
Troubleshooting and recovery: locked out admin access
If you lose access after changing credentials or suspect a configuration error, try a hardware reset to factory defaults (consult the manual for the correct procedure), then reconfigure from scratch with a unique password. If the reset is insufficient, contact STC support for model-specific recovery steps. Maintain a written record of admin credentials in a secure vault or password manager to avoid future lockouts.
Representative STC router default-password patterns and security guidance
| Model Type | Default Password Pattern | Security Notes |
|---|---|---|
| STC Router A | admin / password | Change immediately; avoid common defaults |
| STC Router B | admin / admin | Set unique password; disable unused services |
| STC Router C | user / password | Strong password required; enable firmware updates |
Your Questions Answered
What is the best practice after buying a new STC router?
Change the default password during initial setup and disable remote management if it is not required. Enable firmware updates and consider segmenting the network for IoT devices. Regularly back up configuration changes.
Change the default password during setup and disable remote access unless you need it. Keep firmware current and segment IoT devices for better security.
Is it safe to use remote management after changing the password?
Remote management can be convenient but increases exposure if misconfigured. If you enable it, restrict access to trusted IPs, require strong authentication, and monitor logs. Otherwise, keep it disabled.
Remote management should be disabled unless you need it; if enabled, restrict access and use strong authentication.
How often should I change default credentials?
Change passwords whenever there is a known vulnerability, after a device is decommissioned, or when you suspect credential exposure. For home networks, annual reviews plus after major device changes are common practice.
Review and change credentials after major updates or suspected exposure, at least annually.
What if I forgot the new password?
Use the router’s hard reset to restore factory settings, then reconfigure with a new password stored in a password manager. If you’re managing a business network, contact IT for a secure reset procedure.
If you forget it, reset the router and set a new password right away.
Can firmware updates affect login credentials or settings?
Firmware updates may reset some settings or improve security features. After updating, re-verify credentials and re-enable any security features you had previously configured.
Yes—check credentials after updates and re-enable security features as needed.
Are there regulatory considerations for default passwords?
Most regulations target consumer privacy and network security; following best practices for password hygiene and device hardening aligns with industry expectations and reduces risk of non-compliance incidents.
Following best practices helps with regulatory expectations and keeps your network safer.
“"Default credentials are a leading, preventable risk in home and small office networks. Changing the password and hardening the admin interface drastically reduces the attack surface."”
Key Takeaways
- Change the default password immediately after setup
- Disable remote management unless necessary
- Use a strong, unique password stored in a password manager
- Regularly update router firmware and review security settings