uap ac lr default password: security guide
Comprehensive guide on the uap ac lr default password, how to reset, and best practices for securing UniFi AP LR devices. Learn how to replace the default credentials, lock down management interfaces, and maintain secure configurations.
On most UniFi APs, the uap ac lr default password is ubnt for both the username and password, but you should change it immediately after setup to prevent unauthorized access. If SSH is enabled, use key-based authentication instead of password login, and always disable remote admin when not needed. This simple step dramatically reduces exposure to attackers seeking admin access.
Understanding the uap ac lr default password and its implications
The phrase uap ac lr default password refers to the initial login credentials that were shipped with UniFi AP LR devices. Leaving these credentials unchanged can give unauthorized users a foothold into the management interface, the controller, or the device itself. In practice, many networks begin provisioning with a basic username/password pair to simplify setup, but this approach creates a window of risk during onboarding. From a security perspective, the most critical takeaway is that any credential left in its factory state should be replaced before production use. As part of a layered defense, changing a default password is a foundational step that supports better access control and reduces attack surface across the wireless deployment.
For context, administrators should treat the uap ac lr default password as a temporary credential, intended only for initial access, and plan a secure password strategy that integrates with the broader network policy. It is also wise to review the UniFi Controller’s onboarding process to ensure that password management aligns with your organization’s security standards. This approach helps preserve the integrity of your wireless network while maintaining administrative usability for IT teams.
How default credentials are configured on UniFi AP LR devices
UniFi AP LR devices typically ship with a default login configuration that enables quick, local administration during initial setup. The standard pairing involves a default username and password that allows a technician to sign in to the web GUI or SSH console before enrolling the device in the UniFi Controller. The exact defaults can vary slightly by firmware and regional builds, so always cross-check the official UniFi documentation for the specific hardware revision you are deploying. In general, the moment you complete the initial provisioning, you should replace the default credentials with a unique, strong set of access keys and consider disabling password-based SSH if you can rely on certificate-based or key-based authentication.
Customizing credentials is particularly important when devices are deployed in edge locations or where physical security cannot be guaranteed. With UniFi devices, a careful password strategy should include regular rotations and the use of complex combinations that resist common attacks, such as credential stuffing or brute-force attempts.
Security risks of leaving a default password in place
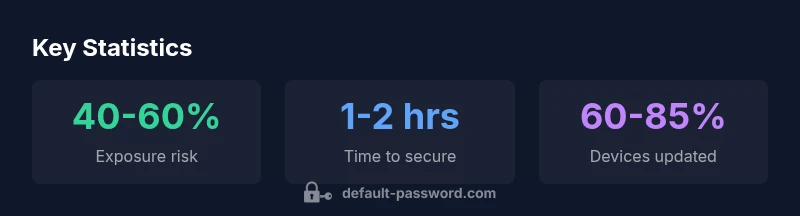
Default passwords create an immediate risk vector for unauthorized access. Attackers often search for devices with unchanged credentials and attempt automated login attempts to gain control over the device or the network. In an environment with a managed UniFi Controller, compromised APs can become footholds for broader attacks, including traffic interception and configuration tampering. The risk grows when devices remain on default credentials across multiple sites or are accessible from untrusted networks.
To mitigate these risks, it is essential to implement a defense-in-depth approach: enforce credential changes during onboarding, restrict management interfaces to trusted networks, monitor login attempts via the controller, and apply firmware updates that address known vulnerabilities related to authentication and access control.
Step-by-step: resetting to factory defaults and securing the AP LR
If you need to reset a UAP-AC-LR to factory settings, locate the physical reset button on the device and hold it for about 10 seconds until the LED indicates a reset. After the device reboots, follow the UniFi Controller onboarding process to re-configure the AP LR. Immediately change any default credentials to strong, unique passwords and enable secure access methods, such as SSH keys or certificate-based authentication, wherever supported. Be sure to disable remote management if it is not required and apply the latest firmware to minimize exposure to known issues related to default credentials.
During re-setup, verify that the device is reachable only through authorized networks and that your password policy mandates complexity, rotation, and storage in a password manager. Document the credentials securely and limit access to the IT team to reduce the chance of credential leakage.
Best practices for password management on UniFi devices
Effective password management for UniFi devices starts with replacing any default credentials during initial deployment. Adopt a policy that requires unique, long, and complex passwords for every device. Disable password-based access methods wherever possible in favor of SSH keys or certificate-based authentication. Limit access to the UniFi Controller and management interfaces to trusted networks and VPNs. Regular firmware updates also reduce the risk of exploitation through authentication weaknesses. Finally, consider enabling multi-factor authentication for accounts with administrator privileges and maintaining an auditable log of changes to credentials and configurations.
Advanced considerations: SSH, GUI access, and cloud management
SSH access should be tightly controlled. If SSH is enabled, prefer key-based authentication and disable password logins to reduce brute-force risk. Restrict SSH access to management networks or dedicated admin subnets, and enforce time-based access controls where feasible. For GUI access, ensure that strong passwords are used, and consider enabling two-factor authentication if supported by the UniFi Controller or device firmware. If you rely on cloud management, ensure that cloud access is secured with robust authentication methods, and limit exposure through firewall rules and IP allowlists. Regularly review controller permissions and revoke access for users who no longer require it.
Default password and recommended security actions for UniFi AP LR
| Component | Default Credential | Security Guidance |
|---|---|---|
| UAP-AC-LR Admin Web GUI | ubnt/ubnt | Change immediately; set a unique password and enable 2FA if supported by the UI |
| SSH Access | ubnt/ubnt | Disable unless needed; use SSH keys and disable password login when possible |
| Firmware Update Route | N/A | After updates, re-check credentials and reset if necessary |
Your Questions Answered
What is the default username and password for uap ac lr?
Most UniFi access points use a default username and password of ubnt/ubnt for initial login, though this can vary by firmware. Always confirm with the official UniFi documentation and reset if you suspect the device is still using defaults.
The typical default is ubnt/ubnt, but always check the official docs for your exact firmware version.
How do I reset a UAP-AC-LR to factory settings?
Press and hold the reset button on the device for about 10 seconds until the LED indicates reset. After reboot, reconfigure via the UniFi Controller and immediately replace any default credentials with strong, unique ones.
Hold the reset button for about ten seconds, then set a new password during reconfiguration.
Is it safe to disable remote admin on UniFi APs?
Disabling remote admin reduces exposure to attackers. Turn it off when not needed, and restrict access to trusted networks. Re-enable only when necessary and monitor access through your controller.
Yes—disable remote admin unless you need it, and limit who can reach the device.
What are best practices for SSH access on UniFi devices?
If SSH is enabled, use key-based authentication and disable password login. Restrict SSH to management networks and consider disabling SSH entirely if it’s not required.
Use SSH keys and disable passwords when you can.
Where can I find official defaults documentation for UAP-AC-LR?
Consult the official UniFi documentation and release notes for device-specific defaults; general guidance is to replace defaults before deployment and maintain access controls.
Check the official UniFi help center for device-specific default credentials.
“Security hinges on changing default passwords and strengthening access controls across network devices.”
Key Takeaways
- Change the default password immediately after setup
- Use strong, unique credentials for every device
- Disable unnecessary remote admin and SSH access
- Prefer key-based authentication over passwords for SSH
- Keep firmware up to date and monitor admin access