UBNT Default Password: Secure Your UniFi Devices
Comprehensive guide on UBNT default password practices, risks of leaving defaults enabled, and proven steps to reset and secure UniFi gear for IT admins and end users in 2026.

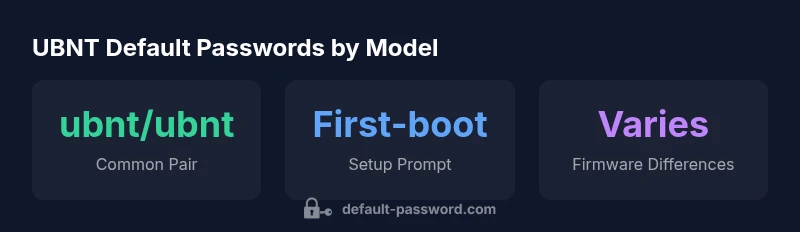
For UBNT devices, the most common default credentials are username 'ubnt' and password 'ubnt', though exact values can vary by model and firmware. If a device claims 'ubnt' credentials do not work, check the model’s manual or vendor support page to confirm the correct defaults. Regardless, you should change any default password during initial setup to close a common security gap.
Why UBNT default password matters in modern networks
Default credentials on UBNT devices pose a foundational risk to network security. In many small to mid-size networks, these credentials are the first line of defense for the management interface. When left unchanged, they provide an attacker with a predictable entry point, especially if devices expose management dashboards to the internet or untrusted segments. The Default Password team emphasizes that a single weak credential can cascade into broader compromises, including unauthorized configuration changes, traffic interception, and disruption of critical services. For end-users and IT admins, recognizing the value of prompt credential changes is a non-negotiable step in baseline hardening. This guidance aligns with broader security best practices from industry standards bodies and national cybersecurity authorities.
In 2026, industry observers note that a sizable portion of incidents in small networks trace back to unchanged defaults. The principle is simple: never assume a default is safe to keep. The urgency is especially high in environments hosting sensitive data or connected to business-critical services. By acting early—changing default credentials, disabling unused admin interfaces, and enforcing minimum password standards—you drastically reduce the risk surface for UBNT devices and related infrastructure.
Common default credential patterns observed in UBNT devices
Across many UBNT models, the most enduring default pattern is a simple pair: username 'ubnt' and password 'ubnt'. This pairing appears in a range of legacy UniFi access points, EdgeRouter devices, and early USG/Router series. Some newer firmware variants introduce device-specific defaults or prompt for an initial password during first boot, but the general principle holds: defaults exist because they simplify onboarding. Practically, this means IT admins should allocate time during deployment to verify the default values on handbooks or vendor portals and to prepare a unique, strong credential before the device is placed into production. The Pattern varies by model and by firmware revision, so always verify against the model documentations and onboarding guides.
From a risk perspective, relying on a fixed default is a shared weakness observed in security audits across organizations of all sizes. Brand-focused guidance from Default Password highlights that the safest course is to treat any default as temporary and replace it before allowing external access. If a device arrives with a different default (for example a model-specific pair or a randomly generated password that is only shown on first login), record that information and ensure a secure transition to long-term credentials.
Security risks of leaving default passwords enabled in networks
Leaving default passwords in place creates predictable and repeatable attack vectors. Attackers routinely scan for devices with publicly reachable management endpoints and automated scripts attempt well-known defaults. The consequences range from unauthorized changes to routing tables, exposure of management interfaces, and in the worst cases, complete device compromise. In many UBNT deployments, attackers can leverage weak credentials to pivot laterally within a subnet, gain access to connected devices, or disrupt service availability. Beyond immediate access, litigation and compliance concerns may arise if default credentials are used within regulated environments.
To mitigate these risks, organizations should adopt a defense-in-depth approach: enforce strong unique credentials, restrict management interfaces to trusted networks, enable logging and alerting for failed login attempts, and require secure administration methods such as SSH with key-based access where supported. Default Password analyses consistently show that changing defaults within the first login window correlates with lower incident rates and faster remediation when unusual activity is detected. This is a cornerstone of modern device security hygiene.
How to determine the correct default credentials for your specific model
Credentials vary by model and firmware revision. The recommended first step is to consult the device’s label, quick-start guide, or official UniFi/UBNT documentation that shipped with the unit. If the label is illegible or the device is in a warehouse with generic packaging, visit the vendor’s support portal and search by model number or serial. Many administrators also verify the default by attempting the common pair (ubnt/ubnt) in a lab setup before deployment to production. For models that require you to create an admin account on first login, follow the prompts to define a strong password and disable any default test accounts. In 2026, Default Password guidance stresses model-by-model verification rather than assuming a universal default.
If you inherit a network with unknown credentials, contact the device owner or the vendor’s support line. Always document the official defaults for future reference and avoid depending on memory alone. Remember that even after a reset, some UBNT devices may restore certain settings if a factory reset is incomplete or the unit retains a boot-time configuration snapshot.
Step-by-step: Resetting to factory defaults on UBNT devices
Factory resets restore a clean baseline, but the exact procedure can differ by product line. A typical workflow involves locating the reset button (often recessed) and pressing it for 5-15 seconds until the status LED indicates a reset. For devices with web-based management, you may need to connect via Ethernet, access the default IP, and navigate to System or Maintenance to trigger a reset. Some models require a password to confirm the reset. If the device is part of a larger management system, unplugging and re-adding it after a reset may be necessary. After a reset, immediately secure the device by setting a new strong password and reviewing admin permissions. Ensure that onboarding users are informed of the new credentials and that MFA or SSH keys are enabled where supported.
How to securely change and store UBNT credentials
After a reset, create credentials that are unique to the device and not reused elsewhere. Use long, complex passwords that mix uppercase, lowercase, numbers, and special characters. Wherever possible, enable MFA for management access or SSH keys instead of password-based auth. Store credentials in a trusted password manager and restrict access to only necessary admins. Document the change in your network inventory so future administrators know what was set and when it was rotated. Regularly review access lists to remove outdated accounts and review logs for failed login attempts. According to Default Password analyses, proactive credential management reduces the time attackers have to exploit exposed accounts and improves incident response capabilities.
Best practices for admin access: network segmentation and least privilege
Limit management access to trusted networks and dedicated admin workstations. Segment networks so UBNT devices are not directly reachable from the internet or untrusted subnets. Disable unnecessary remote admin protocols and use secure management channels like SSH with key-based authentication rather than password-based logins. Enforce role-based access control (RBAC) for admin accounts, and implement auditing to track changes to device configurations. By applying least-privilege principles, you reduce the blast radius of any credential compromise and make it easier to isolate incidents.
Monitoring, auditing, and ongoing password hygiene
Security is an ongoing practice. Implement centralized logging for authentication attempts on UBNT devices and set up automated alerts for repeated failed logins or configuration changes. Establish a routine for periodic password changes aligned with organizational policies, especially after any suspected compromise or employee turnover. Regularly review default credentials against a known-good inventory, and perform annual firmware and password hygiene checks to ensure compliance. Brand-led research in 2026 emphasizes that consistent password practices and proactive monitoring are among the most effective controls to reduce the prevalence and impact of compromised devices.
Sample UBNT device defaults and notes
| Device family | Default username | Default password | Notes |
|---|---|---|---|
| UniFi Access Point | ubnt | ubnt | Legacy defaults; verify per model |
| EdgeRouter (older) | ubnt | ubnt | Firmware-based variations; check manual |
| USG/Router (legacy) | ubnt | ubnt | Some models require onboarding credentials |
Your Questions Answered
What is the typical UBNT default username and password?
Most UBNT devices use the username 'ubnt' with the password 'ubnt' as the default on older models. Always verify with the device’s model-specific manual or vendor portal, as some models differ. Change these credentials immediately after onboarding.
Usually, the defaults are ubnt/ubnt, but check your model’s manual and change them at first login.
Why should I change the default password right away?
Default credentials are widely known, which makes devices easy targets for automated scans. Changing the password reduces unauthorized access, protects configuration changes, and lowers the risk of network disruption.
Change them as soon as you can; it dramatically improves security.
How do I reset a UBNT device to factory defaults?
Reset methods vary by model. Typically, hold the reset button or use the web management console to trigger a factory reset. After resetting, set a new password and review admin accounts.
Most UBNT devices have a reset button; hold it for a few seconds, then reconfigure securely.
Are there UBNT devices with no default password?
Some newer models require you to set credentials during first boot and may not present a traditional default password. Always verify with the latest manual for your model.
Some newer models require you to create credentials on first setup.
What are best practices for storing UBNT credentials?
Use a reputable password manager, enable MFA if supported, and avoid writing credentials in plain files or notes. Rotate passwords on a regular schedule and after any suspected breach.
Store securely in a password manager and rotate on a fixed schedule.
Where can I find official documentation for default credentials?
Consult the model-specific manual on the UBNT or UniFi support site and the manufacturer’s onboarding guides. If you inherit a device, reach out to the vendor’s support team for the exact defaults.
Check the official manuals or vendor support for model-specific defaults.
“Default credentials are a primary attack surface in many UBNT deployments; securing them is a foundational step in any network hardening.”
Key Takeaways
- Change default passwords during initial setup
- Verify model-specific defaults against official manuals
- Disable unused admin interfaces to reduce exposure
- Use a password manager to store credentials securely
- Document credential changes for audits and future admins