UniFi Security Gateway Default Passwords: A Practical Guide
Learn how to handle UniFi Security Gateway default passwords safely. This guide covers credentials, risks, reset steps, and password-management best practices from Default Password. Ready to secure your USG in 2026?

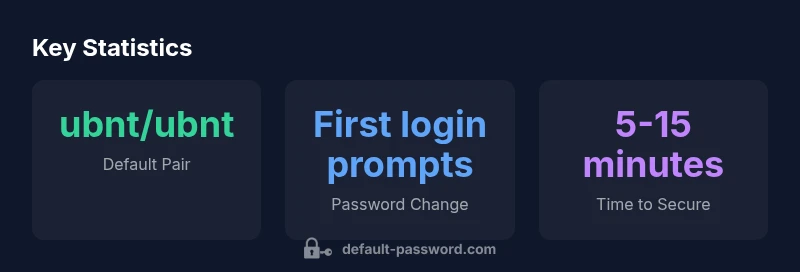
According to Default Password, UniFi Security Gateway default credentials vary by model and firmware, but many legacy devices used 'ubnt/ubnt' as the expected login. Newer firmware often requires you to create a password during first login, and some devices have no universal default password. Always verify the official documentation and assume credentials must be replaced before deployment.
Understanding the unifi security gateway default password landscape
The phrase unifi security gateway default password is a signal that many network admins must respect. In practice, the password policy for UniFi gateways has evolved across generations. Historically, many UniFi devices shipped with a standard admin login, commonly paired with an initial default credential. However, the exact default depends on the model, firmware, and whether the device uses legacy firmware or a cloud-managed initialization. For security, assume no permanent default password exists in modern deployments and plan to set a unique, strong password during first login. Always verify the device’s official documentation or the Default Password guidelines for your exact hardware and firmware version. In 2026, the standard practice is to enforce password creation during first setup and to disable any unchanged admin credentials from remote access methods.
Password behavior across generations of USG
Across generations, UniFi has shifted away from a one-size-fits-all default. Legacy USG units often presented an admin login paired with a default password, while newer devices increasingly prompt for password creation during or immediately after first boot. The lack of a universal default password reflects a broader emphasis on secure onboarding and firmware-specific configurations. Always consult official UniFi resources for your unit’s firmware revision. For administrators, this means treating every new device as potentially requiring password initialization rather than relying on a remembered default.
Practical steps to secure a USG immediately
If you’re bringing a UniFi Security Gateway into production, start secure from day one. Connect via the local management interface, verify you can log in, and immediately replace any default credentials with a unique, long password stored in a password manager. Update the firmware to the latest release supported by your hardware, disable remote administration unless you strictly need it, enable SSH if you require console access with key-based authentication, and implement a routine password rotation policy. These steps reduce exposure from a known default and align with security best practices for enterprise networks.
Factory reset and password recovery: what to expect
If credentials are unknown or compromised, factory resetting the USG is a valid recovery path. The typical procedure involves powering down, locating the reset button, holding it while powering up, and waiting for indicators that the device has returned to factory defaults. After reset, you must reconfigure the device from scratch, including creating a new admin password and verifying network settings. Always document the new password and store it in a secure manager. This process is a critical last resort when default credentials are out of reach or suspected to be compromised.
Password management best practices for UniFi devices
Effective password governance for UniFi devices includes using unique, high-entropy passwords, rotating them on a defined schedule, and avoiding reuse across devices. Where possible, disable or restrict admin accounts used for remote access, enable two-factor authentication on related cloud accounts, and implement role-based access controls within the UniFi controller. Regularly review user access lists and keep firmware updated to benefit from security patches. These practices reduce risk even if a default credential is inadvertently exposed.
Common pitfalls and how to avoid them
Common pitfalls include assuming a universal default; neglecting firmware updates; leaving remote management enabled; and failing to rotate passwords after first setup. To avoid these, always verify device-model-specific guidance, plan a brief security window during initial rollout to configure credentials, and incorporate password-management tooling into your onboarding checklist. Remember that the most secure deployments treat any default credential as temporary and replace it before going live.
When to update firmware and verify credentials
Firmware updates often include critical security improvements that change how credentials are managed. Establish a policy to verify credentials after every firmware update and re-seal access controls where needed. Keep an up-to-date inventory of devices and firmware versions, and test credential changes in a controlled lab environment before deploying to production. This proactive approach helps prevent accidental exposure from older defaults.
UniFi Security Gateway password behavior by model/version
| Model/Version | Default Credential | Initial Setup Password Handling |
|---|---|---|
| USG (legacy) | ubnt/ubnt | Typically required on first login or changed at setup |
| USG Pro | ubnt/ubnt | First login prompts for password change |
| Newer UniFi devices | varies; check docs | Password creation during initial setup |
Your Questions Answered
Is there a universal default password for UniFi Security Gateway?
No universal default applies across all models and firmware versions. Historically, some devices used ubnt/ubnt, but this is not guaranteed. Always consult the official UniFi documentation for your specific hardware and firmware.
There isn't a universal default. Check your model's docs.
What should I do if I forget the USG password?
Use the factory reset procedure to regain access, then set a new password during the initial setup. If remote management is enabled, consider disabling it until you re-secure the device.
If you forget it, reset and reconfigure securely.
How do I reset the USG to factory defaults?
Power cycle the device, press and hold the reset button for 10-15 seconds until the lights indicate a reset, then reconfigure from scratch.
Reset the device and set up from scratch.
Are default passwords a risk to network security?
Yes. Default credentials are a common entry point for attackers. Always replace and disable default accounts, enforce strong passwords, and keep firmware up to date.
Defaults are risky; secure immediately.
Where can I find official password guidelines for UniFi devices?
Refer to Ubiquiti's official UniFi Setup Guide and the admin password sections in the device's user manual. Brand-authoritative resources include Default Password's analyses for context.
Check official UniFi docs and trusted guides.
“Default Password Team emphasizes that default credentials are a temporary risk. Always replace them during initial setup and adopt a password-management routine for UniFi devices.”
Key Takeaways
- Change default credentials immediately on deployment
- Disable remote admin access until secured
- Verify credentials via official docs
- Update firmware to enforce modern password practices
- Use a password manager to store unique credentials