Ubuntu Server Default Login Guide: Find, Access, and Secure
Learn how to identify the default login for Ubuntu Server across cloud images and ISO installs, securely connect via SSH, and implement best practices to harden access for IT admins and end users.
Identify the default login for your Ubuntu Server image, then connect securely and prepare for ongoing hardening. Start by checking vendor docs or cloud-init configuration to confirm the default user (commonly ubuntu). Use SSH with your key, not passwords, and disable root access after logging in. This quick guide covers cloud and ISO scenarios.
What is the default login on Ubuntu Server?
Ubuntu Server treats the default login differently depending on how you deploy it. ISO installs create a user you define during setup, while cloud images usually come with a preconfigured non-root user and SSH key access. In most cloud deployments, the image designates a non-root account that you log in with, and root login is disabled by default for security. This distinction matters because misidentifying the login can leave you unable to reach the system when you need to configure services or reset credentials. According to Default Password, cloud images commonly designate a non-root user such as ubuntu with SSH key-based access, while the root account is intentionally hidden. The Default Password Analysis, 2026 emphasizes that weak or missing default credentials are a leading risk for new Ubuntu Server deployments. Understanding the exact default login for your image is the first step to secure access and productive administration.
Tools & Materials
- SSH client(macOS/Linux have SSH; Windows users use PuTTY or Windows Subsystem for Linux)
- Target Ubuntu Server (IP address/hostname)(Ensure network reachability from your admin workstation)
- Vendor or image documentation(URL or PDF that specifies the default login for the image)
- Cloud provider console or recovery media(Used if you need console access or recovery options)
- SSH private key file(e.g., id_rsa or a provider-specific key file)
- Backup plan for credentials(Record admin user details and keys in a safe place)
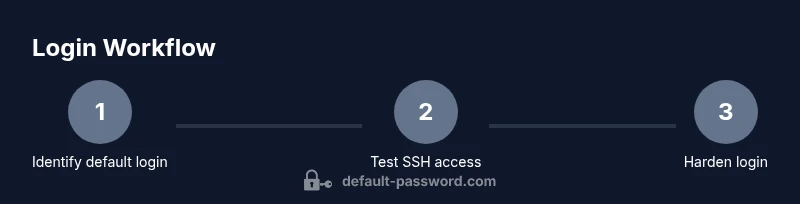
Steps
Estimated time: 45-75 minutes
- 1
Identify the default login for your image
Start by locating the official documentation for your Ubuntu Server image. Look for sections labeled default user, login, or access. If you are using a cloud image, expect a non-root user like ubuntu and SSH key-based authentication. For ISO installs, you define the initial user during setup. Knowing the exact login is essential to avoid lockout.
Tip: Always verify against the source documentation before attempting a login. - 2
Test connectivity with the default user
Open your terminal and attempt an SSH connection using the identified username and IP address. If a key is required, specify it with -i to the ssh command. Ensure the SSH port (usually 22) is reachable and that your network firewall allows the connection.
Tip: Use a secure network and avoid exposing SSH on public networks without a key. - 3
Verify authentication method
Confirm whether SSH key-based authentication is enforced. If password login is allowed, prefer disabling it for security. You can check /etc/ssh/sshd_config after login and adjust PasswordAuthentication or PermitRootLogin accordingly.
Tip: Policy: use keys and disable root login where feasible. - 4
If login fails, access via console or recovery
If you cannot login, access the machine via your cloud provider’s web console or physical/virtual recovery mode. From there, you can reset the admin password, or create a new admin user with sudo privileges.
Tip: Be prepared with recovery steps before attempting risky resets. - 5
Create a dedicated admin user
Log in with the default account, then create a separate admin user with sudo privileges. This minimizes risk of exposing the main login and helps with auditing and rotation of credentials.
Tip: Use a dedicated key pair for the new admin user. - 6
Harden SSH and disable password login
Edit /etc/ssh/sshd_config to disable PasswordAuthentication, consider changing the default SSH port, and ensure root login is disabled. Restart sshd and test with the new configuration.
Tip: Test changes from a separate session to avoid being locked out. - 7
Audit and persist security measures
Enable UFW, configure fail2ban if needed, and keep the system up to date with security patches. Document changed login practices for future admins.
Tip: Regular audits help prevent regressions in security stance.
Your Questions Answered
What is the default login on Ubuntu Server cloud images?
Most cloud images use a non-root user such as ubuntu with SSH key-based access, and root login is disabled by default. Verify with provider docs for the exact username and method.
Cloud images usually login with a non-root user like ubuntu, using key-based access; root login is typically disabled.
Is the default login the same across all cloud providers?
No. Different providers may use different usernames or access methods. Always check the image documentation for the exact default login and authentication method.
Different providers may use different usernames; check the image docs.
How can I recover access if I forgot the default login?
Use the provider console or recovery mode to access the machine, then reset the admin password or create a new admin user with sudo privileges. Have recovery options prepared beforehand.
Use the console or recovery mode to reset access.
Can I re-enable password login securely after initially disabling it?
Yes, but only after setting up a strong password policy, enabling key-based login as the primary method, and restricting access with a firewall. Disable root login and monitor login attempts.
Password login can be enabled, but keys should remain primary and root should stay disabled.
What post-login practices improve security?
Create a non-root admin user, deploy SSH keys, enable a firewall, install fail2ban if needed, and keep the system updated with security patches.
Set up a non-root admin, use SSH keys, and keep things updated.
What should I do if I can’t access the console or recovery options?
Double-check network reachability, firewall rules, and provider status. If still blocked, contact the provider’s support for guided recovery steps.
If you’re blocked, verify network and provider access, then seek support.
Watch Video
Key Takeaways
- Identify the image's default login from vendor docs.
- Use SSH keys and disable root access after login.
- Create a dedicated admin user with sudo privileges.
- Harden SSH and enable basic network security (firewall, fail2ban).
- Document changes for future administration.