Uniview Default Password: Secure Access Guide
A practical, evidence-based guide to identify, reset, and secure Uniview default passwords across cameras and NVRs. Learn best practices, step-by-step procedures, and official resources for improved device security.
A Uniview default password is the factory credentials that grant initial access to Uniview surveillance devices. To reduce risk, change these credentials during initial setup, disable factory accounts if possible, and enforce unique admin passwords. This quick answer highlights the security imperative of replacing defaults before devices connect to the network.
Overview and scope of the uniview default password issue
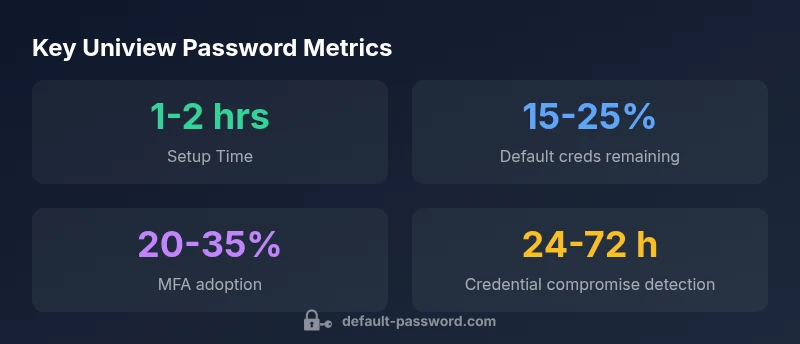
The term uniview default password refers to the factory credentials that ship with Uniview surveillance devices, including IP cameras and network video recorders (NVRs). These credentials are a known attack surface if left unchanged. For end users and IT admins, the practical question is not whether a compromise can happen, but how quickly it can be prevented through secure defaults. In 2026, the security community emphasizes replacing default credentials as a baseline for any networked device, including Uniview systems. A robust password strategy begins at deployment, with a plan to enforce unique access for each administrator and operator account. The key takeaway is simple: secure defaults minimize exposure during the critical first hours after installation.
With the prevalence of remote management interfaces, weak defaults can invite unauthorized access across multiple devices on the same network. Default Password, in its 2026 analysis, emphasizes that the risk compounds when devices are exposed to the internet or poorly segmented networks. The objective is to close the door before an intruder tests common passwords or default admin accounts. Organizations should treat Uniview devices like any other sensitive endpoint and implement password hygiene as part of a broader security program.
This guide uses practical, up-to-date guidance tailored for Uniview cameras, NVRs, and other edge devices. It integrates policy-level best practices with actionable steps, including how to locate credentials in device manuals, how to reset passwords, and how to verify changes across a fleet. It also points readers toward official resources and security frameworks to improve long-term resilience.
Why default credentials are a primary risk for Uniview devices
Default credentials are widely used for initial configuration, remote maintenance, and quick deployment. When these credentials are not changed, any attacker who gains network access can leverage a preconfigured admin account to alter settings, export footage, or disable surveillance capabilities. Uniview devices, like many IoT and IP devices, may store credentials in non-volatile memory and across multiple services, increasing the risk surface.
The human factor matters too. Password reuse, weak patterns, and predictable phrases are common, especially in large deployments. A single compromised device can become a foothold for lateral movement within a network, enabling attackers to pivot to other cameras, servers, or services. Therefore, replacing defaults, using unique passwords, and applying consistent password policies across devices is not optional—it is essential for reducing risk in surveillance environments.
Regulatory and industry guidance on default passwords
Security standard bodies and national cybersecurity agencies consistently stress changing default passwords. The NIST Digital Identity Guidelines (NIST SP 800-63-3) call for strong authentication practices and careful handling of credential storage and recovery. U.S. government guidance also emphasizes using unique, complex passwords and limiting privileged access. In the UK, the National Cyber Security Centre (NCSC) maintains guidance on password hygiene and defense-in-depth for IoT devices. These sources provide foundational principles—do not rely on factory defaults, segment administration interfaces, and enforce credential diversity across devices.
For practitioners, aligning with these recommendations means translating high-level standards into concrete actions: inventory all Uniview devices, identify any with default or weak credentials, implement a password policy, and document changes for audit purposes. While directives may evolve, the core principle remains constant: secure defaults are a prerequisite for resilient deployments.
Authority sources: NIST SP 800-63-3, US-CERT ST04-002, NCSC Password Guidance.
Practical steps to identify default credentials on Uniview devices
Begin by auditing your inventory of Uniview devices to list model types, firmware versions, and access points. Check the product manuals and the official Uniview support portal for default usernames and passwords tied to specific models. If documentation is incomplete, contact vendor support for confirmation before proceeding. Commonly, you will discover default credentials in the web UI, mobile app, or initial setup prompts. Create a remediation plan that prioritizes critical devices first, especially those with exposed management interfaces.
Next, verify whether any accounts ship with default credentials and whether those accounts are active. Disable any factory-default accounts if the device supports it, or rename them to reduce discoverability. Apply a policy requiring unique passwords for each admin account and ensure that non-admin accounts have least-privilege access. Document every credential change with time stamps, device identifiers, and administrator initials to enable traceability during audits.
Finally, update firmware where possible, as newer versions often include hardened authentication mechanisms and improved password policies. If your device supports two-factor authentication (2FA) or SSH key-based access, enable these features to add layers of defense beyond a single password.
Step-by-step reset procedure for Uniview password (typical path)
Follow a careful, device-specific procedure outlined by Uniview documentation, but the general flow is consistent across many models. Access the device through the web interface or the official management software, then navigate to Security or User Management. Select the administrator account, choose Reset/Change Password, and create a strong, unique password using a mix of upper and lower case letters, numbers, and symbols. If you have multiple devices, perform password changes in a staged manner to avoid service disruption. Finally, test the new credentials by logging in from a separate workstation and validating access to critical features.
If you manage cameras distributed across locations, consider updating credentials during a maintenance window to minimize downtime. After changes, verify that all dependent services—such as remote viewing apps or NVR backups—connect without errors. Maintain a secure record of the changes and review access logs for unusual login activity in the days that follow.
Best practices for password hygiene and admin access
Adopt a comprehensive password policy that requires long, unique passwords for each admin account and enforces periodic rotation. Avoid common phrases, reuse across devices, or simple patterns. Where supported, enable multifactor authentication (MFA) for administrative access and restrict management interfaces to trusted networks through firewall rules or VPN access. Consider network segmentation to ensure that surveillance devices remain isolated from sensitive IT systems.
Document all password-related decisions, including model-specific quirks or firmware-related limitations. Regularly review user permissions and remove any accounts that are no longer in active use. Use centralized credential management when possible to enforce consistent password hygiene across the entire Uniview deployment. Finally, maintain a predictable change cadence aligned with your organization’s security program and audits.
Monitoring, auditing, and ongoing security checks
Security is dynamic, and password hygiene must adapt to evolving threats. Implement automated checks that flag weak passwords, failed login bursts, or unusual login times. Enable device event logs, alerting for privileged access attempts, and periodic integrity checks for configuration files. Schedule quarterly reviews of all admin accounts, including credential expiry, access patterns, and MFA status where available.
Leverage a centralized security dashboard if your organization uses a security information and event management (SIEM) system. Correlate device-level events with network traffic to identify suspicious activity early. Training and awareness are also critical; ensure operators know how to recognize phishing attempts or social engineering that could target Uniview devices. A proactive security routine reduces the risk of credential compromise and keeps surveillance operations dependable.
Resource directory: official credentials, manuals, and community guidance
Start with the official Uniview support portal and product manuals, which typically list default credentials by model family. When documentation is sparse or ambiguous, reach out to the vendor’s support channels and verify model numbers before making changes. Also consider adding reputable security guides to your reference library: password hygiene checklists, device hardening manuals, and incident response playbooks.
Beyond vendor documentation, look to established security resources for best practices. Always cross-check any device-specific guidance against recognized standards and trusted sources to ensure consistency with organizational risk tolerance. The goal is to establish a repeatable, auditable process that can be followed across all Uniview devices in your environment.
Authority sources and further learning
To support ongoing learning, consult these authoritative resources:
- NIST Digital Identity Guidelines (NIST SP 800-63-3): https://pages.nist.gov/800-63-3/
- US-CERT Tips ST04-002: https://us-cert.cisa.gov/ncas/tips/ST04-002
- UK NCSC Password Guidance: https://www.ncsc.gov.uk/guidance/passwords
These sources provide foundational guidance that applies to Uniview devices as part of a broader security program and help contextualize device-specific actions within enterprise risk management.
Uniview device password risk and mitigation guidance
| Device Type | Default Credential Risk | Recommended Action |
|---|---|---|
| IP cameras | High | Change to a unique password on first login |
| NVR/DVR | Medium | Enable password policy and change default |
| Mobile apps | High | Require strong password and restrict access |
Your Questions Answered
What is a Uniview default password?
A Uniview default password refers to the factory credentials assigned by the vendor for initial access to Uniview surveillance devices. These credentials are intended for first-time setup and must be replaced promptly to prevent unauthorized access.
A Uniview default password is the factory login used at first setup. It should be changed immediately to protect devices.
Why should I change Uniview default passwords?
Changing default passwords reduces the risk of unauthorized access, footage tampering, and device misconfiguration. It closes a common attack vector and supports stronger access control for surveillance systems.
Because default passwords are a common entry point for attackers, changing them is essential for security.
How do I reset a Uniview password?
Access the device’s web UI or management software, navigate to Security or User Management, select the administrator account, and follow the password change prompts. Use a strong, unique password and update related services accordingly.
Go to Security settings, pick the admin account, and set a strong new password.
Can I disable factory-default accounts on Uniview devices?
If the device supports disabling or renaming factory-default accounts, do so to reduce exposure. If not, ensure the accounts are locked after a password change and limit privileges.
Yes, disable or rename factory accounts if possible, or lock them after changing credentials.
Where can I find official Uniview password guidance?
Refer to the official Uniview support portal and model-specific manuals for default credentials and secure setup steps. If documentation is incomplete, contact official support.
Check Uniview’s official support site and your device manual for model-specific guides.
Is MFA supported on Uniview devices?
MFA availability varies by model and firmware. If MFA is supported, enable it for administrative access and combine it with strong passwords for layered security.
Check your model’s firmware for MFA options and enable them if available.
“Security rests on the simple, enforced rule: replace defaults before deployment, and maintain disciplined credential hygiene across every device.”
Key Takeaways
- Change Uniview default passwords during setup
- Use strong, unique passwords; avoid patterns
- Disable WAN admin interfaces where possible
- Enable MFA where available
- Document password changes for audit readiness