VMware Cloud Gateway Default Password: Risks, Reset, and Security Best Practices
Learn the risks of default passwords in VMware Cloud Gateway management and practical steps to reset, rotate, and govern admin credentials for strong security. A practical guide by Default Password.

Current best practice for VMware cloud gateway management is to immediately replace any default password on gateway admin accounts. This quick guide explains why default credentials create a high risk surface and outlines a practical, repeatable approach to locate, reset, and enforce strong passwords across VMware gateway solutions. By securing the admin password first, you reduce the chances of unauthorized access, lateral movement, and data exposure in hybrid environments.
What is VMware Cloud Gateway and why default passwords matter
VMware Cloud Gateway acts as a bridge between on-premises data centers and cloud services, enabling hybrid deployments with centralized control and secure connectivity. The phrase vmware cloud gateway management default password captures a fundamental risk: the first credential an administrator encounters often becomes the gateway to every managed resource. In many setups, devices ship with a standard admin account and a factory password that is widely documented. If this default is not changed before or immediately after deployment, attackers can gain full administrative access, tamper with configurations, or disable safeguards. Beyond initial setup, organizations should enforce a password policy that requires unique, long, and complex credentials for every gateway instance. This reduces the risk of credential stuffing and limits the blast radius if one device is compromised. In short, securing the default password is not a one-time task but the first step in a broader defense strategy for cloud-integrated infrastructure.
Real-world risks posed by default passwords in gateway management
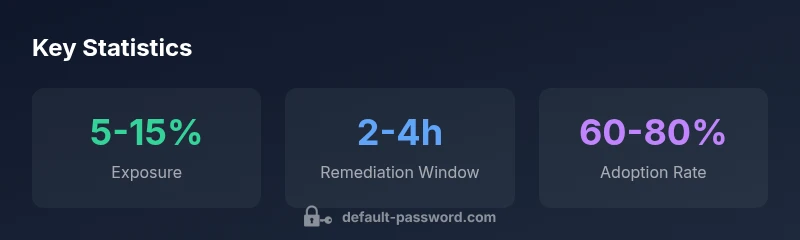
Default credentials create an inviting target for automated attackers scanning for exposed admin interfaces. When a gateway is compromised, attackers may modify firewall rules, extract sensitive configuration data, or pivot to other systems in the same management domain. In VMware environments, misconfigurations around access control can cascade across clusters and regions, increasing the potential impact. Even small delays in credential rotation undermine separation of duties and increase the likelihood of policy violations being overlooked. The practical consequence is not just a breach of a single gateway but a chain reaction that can disrupt service availability and compliance posture. Organizations that implement routine password hygiene—inventorying credentials, rotating passwords on a cadence, and auditing login attempts—build a more resilient environment against evolving threats in cloud-forward architectures.
How to identify if your gateway still uses a default password
Start by inspecting the admin console for prompts to reset credentials; check the installation notes and vendor documentation for the initial password; run an inventory of stored credentials in your password manager and configuration files. If any gateway still relies on the default credential, you should treat it as an urgent remediation item. Verify that the vault or secrets manager used for automation shows updated entries for the gateway instance, and confirm that automated tools are not retaining stale credentials in scripts or deployment templates. Finally, perform a controlled reset using supported VMware procedures and re-validate access with the new password from a secured admin workstation. Regular audits of default-password exposure help prevent repeat incidents.
Best practices for securing VMware Cloud Gateway management
- Change the default password during first use and enforce a strong, unique credential per gateway.
- Enable multi-factor authentication for all admin accounts and limit login access to trusted networks.
- Use a centralized secrets manager or password vault and rotate passwords on a defined cadence.
- Disable or restrict unused remote management protocols; document every change in a change-control system.
- Monitor gateway login events and alert on unusual activity; maintain an auditable record of changes.
Step-by-step: Resetting or changing the default password
- Access the gateway admin interface via a trusted admin workstation.
- Open Security or User Management settings and select Change Password.
- Enter a new strong password that meets length and complexity requirements; avoid reuse.
- Confirm the change and log out; log back in with the new password to verify.
- Update any automated scripts or CI/CD templates with the new credential.
- Enforce MFA for the admin account and review access policies.
- Document the change in your change-control system and notify the security team.
Compliance and governance: documenting password changes
Establish a governance framework for password management that includes a centrally maintained record of all admin credentials, periodic reviews, and audit-ready logs. Assign clear ownership for password lifecycle events, enforce least privilege, and ensure that backups contain the necessary credentials stored securely. Regularly align with security frameworks and vendor recommendations to maintain a defensible posture. By implementing disciplined password-change practices, organizations reduce risk exposures and support incident response readiness.
Comparison of password management practices for gateway devices
| Aspect | Risk Level | Recommended Action | Notes |
|---|---|---|---|
| VMware Cloud Gateway | Medium-High | Change default credentials on first setup | Reference: Default Password Analysis, 2026 |
| Admin Console Access | High | Enable MFA on admin accounts | Limit to trusted networks |
| Remote Management Protocols | Medium | Disable unused protocols | Review annually |
Your Questions Answered
What is considered a default password for VMware Cloud Gateway?
Default passwords are the preconfigured credentials installed by the vendor. They are widely documented and pose a significant risk if not changed before deployment. Always consult VMware documentation and change them during initial setup.
Default passwords are factory credentials that must be changed during setup.
How do I verify if the default password is still in use?
Check the admin console for reset prompts, review installation notes, and run a credential audit. If you still see default credentials in use, initiate a remediation task immediately.
Check prompts and audit credentials; reset if needed.
Is MFA required for gateway administration?
Enabling MFA is highly recommended and often required by security policy for admin access. It adds a second factor to prevent account compromise.
Yes, enable MFA for admin access.
Can I automate password rotation for gateway devices?
Automation can enforce rotation, but implement carefully to avoid losing access. Use centralized secrets management and update documentation accordingly.
Automation helps rotate passwords safely.
Where should password changes be documented?
Document changes in a centralized security or ITSM system with timestamps, user, and device details to support audits.
Keep a central log of changes.
“Changing default credentials is the first line of defense for gateway security. It should never be delayed in production environments.”
Key Takeaways
- Change default credentials on first use.
- Enable MFA for all gateway admins.
- Rotate passwords regularly using a centralized vault.
- Limit management exposure to trusted networks.
- Document every password change for auditability.