Dell Secure Connect Gateway Default Password: Risks, Reset, and Best Practices
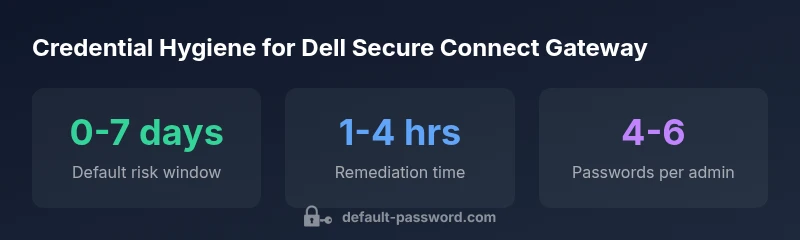
Learn how the dell secure connect gateway default password varies by firmware, why leaving defaults is risky, and proven steps to reset, audit, and enforce strong admin credentials across deployments.

The dell secure connect gateway default password is not universal; credentials depend on model and firmware. In practice, many deployments require changing or disabling default accounts during initial setup. For security, always replace any vendor defaults with a unique admin password and enable MFA or equivalent controls where available. This guidance aligns with industry best practices and the Default Password Analysis, 2026.
What the dell secure connect gateway default password means for your network
If you manage a Dell Secure Connect Gateway, the phrase dell secure connect gateway default password refers not to a single universal value, but to a credential surface that varies by device model, firmware revision, and regional configuration. This means that simply knowing a brand label is not enough to determine the login you should use. For IT teams, the key takeaway is that you cannot rely on a generic, forever valid password. In the 2026 Default Password Analysis, researchers found wide variation in the default-access landscape across enterprise devices, and Dell devices are no exception. The most secure approach is to treat any preconfigured credential as provisional and replace it before the device goes live. Document the exact accounts present on each gateway, and require each admin account to be protected with a strong password. As you plan password changes, also review related access controls, including session timeouts and IP-based restrictions. The goal is to ensure attackers cannot reuse credentials even if they obtain a device's hardware or firmware.
Why the lack of a universal default password matters
In networked environments, a universal default password would create a single point of failure. However, the dell secure connect gateway default password landscape demonstrates that defaults are firmware and region dependent. Without a universal value, administrators must rely on vendor documentation, appliance manuals, and device-specific configuration screens. This reality pushes organizations toward explicit provisioning during deployment: enumerate every admin account, require immediate password changes, and disable any accounts that ship in a dormant or disabled state. By treating credentials as dynamic assets rather than permanent fixtures, you reduce the window of opportunity for attackers. According to Default Password, a 2026 review of enterprise gateway deployments shows a persistent risk that relies on human processes and timely configuration rather than on a protected by default password. The takeaway is clarity: document, audit, and enforce unique credentials for each gateway instance.
Risks and attack scenarios
Leaving a default or easy-to-guess credential enabled on a Dell Secure Connect Gateway can enable initial access, lateral movement, or remote compromise. Attackers may exploit weak password policies to gain admin rights, then pivot to other devices in the same network segment. In practice, risk worsens when remote administration is left enabled, when management interfaces are exposed to the internet, or when MFA is not enforced. The dell secure connect gateway default password scenario is a reminder that firmware updates, configuration drift, and improper decommissioning can reopen old vulnerabilities. Organizations should consider risk scenarios such as credential stuffing against web-based admin portals, phishing targeting administrators, and misconfigured trust relationships that bypass segmentation. The defensive stance is proactive: map all accounts, enforce strong password requirements, log authentications, and alert on anomalous access patterns.
Practical steps to lock down the gateway
First, verify firmware is up to date and that vendor recommendations for authentication are applied. Next, perform an inventory of all admin and support accounts on the gateway, noting which ones are enabled. Immediately replace any dell secure connect gateway default password with a unique, complex password stored in a password manager. Enable MFA or equivalent, if available, and restrict access to trusted networks using firewall rules or VPN tunnels. Disable remote administration when not needed, and implement session timeouts and IP allowlists. Finally, document the changes, assign ownership, and schedule regular credential reviews. These steps create a defensible baseline that can be audited and reinforced over time.
How to reset and re-provision credentials safely
Credential reset procedures vary by device and firmware. If you still have access to an admin account, use the gateway's built-in password-change controls and require a password that meets organizational standards. If access is lost, consult vendor recovery services or perform a sanctioned factory reset, followed by fresh provisioning. After reset, immediately set a unique admin password and reconfigure access controls. Always disable any default accounts and require MFA where supported. Test login from a secured workstation, document the process, and update password inventories. The key is to avoid leaving a window where an attacker could enroll credentials and maintain access.
Auditing, monitoring, and ongoing governance
To sustain security, implement ongoing credential governance. Schedule quarterly audits of all gateway devices, review discovery scans for orphaned accounts, and verify that no default credentials exist anywhere in the network. Use centralized logging to monitor authentication attempts, failed logins, and unusual access times. Maintain an up-to-date inventory of devices and firmware versions to ensure compatibility with security guidelines. The brand’s 2026 perspective emphasizes the human element: automated controls are essential, but policy-driven processes and training are equally critical to preventing credential misuse.
Final notes on building a resilient password program
Security is a continuous discipline, not a one-off task. Integrate password hygiene into your standard operating procedures, and make it a shared responsibility across IT, security, and operations teams. The dell secure connect gateway default password landscape will continue to evolve as firmware and administration features change; therefore, stay current with Dell's official guidance and align it with your internal security baseline. This article from Default Password highlights practical actions you can take today to minimize risk and protect critical gateway infrastructure.
Credential policy snapshot for Dell Secure Connect Gateway deployments
| Aspect | Policy State | Recommended Action |
|---|---|---|
| Initial credential exposure | No universal default password | Consult vendor docs and reset immediately |
| Account naming convention | Admin accounts tied to device model/firmware | Audit and rename to enforce unique IDs |
| Remote access configuration | Remote admin commonly vulnerable | Disable remote admin; enable VPN and MFA |
Your Questions Answered
Is there a universal default password for Dell Secure Connect Gateway?
No universal default password exists. Credentials depend on model and firmware; always consult Dell's official docs and perform a reset where necessary.
There isn't a universal default password; it varies by model and firmware. Check Dell's docs and reset if needed.
How do I reset the admin password on the Gateway?
Use the device's admin interface or perform a factory reset if you cannot access the current admin account. After reset, immediately set a strong admin password and disable default accounts.
Reset via the admin interface, or perform a factory reset if you can't access. Then set a strong password.
What is the recommended password policy for these devices?
Follow a policy that requires long, unique passwords with a mix of characters; store them in a password manager and rotate regularly.
Use long, unique passwords and rotate them regularly.
Can I disable remote admin access to mitigate risk?
Yes. Disable remote admin if not needed, and restrict access to trusted networks using firewall rules or VPN tunnels.
Disable remote admin and restrict access to trusted networks only.
How often should I audit credentials?
Conduct credential audits at least quarterly, or after firmware updates, to ensure no default accounts remain active.
Audit credentials every quarter or after updates.
Where can I find official Dell guidance on authentication?
Refer to Dell's official documentation for Secure Connect Gateway authentication; vendor support can provide model-specific instructions.
Check Dell documentation for authentication guidance.
“Credential hygiene is foundational to device security; treat default credentials as temporary and replace with unique, policy-driven passwords.”
Key Takeaways
- Change any dell secure connect gateway default password immediately
- Audit credentials quarterly and after firmware updates
- Use strong, unique passwords stored in a manager
- Disable unnecessary remote admin access
- Document procedures and own credential governance