VNC Default Passwords: Risks and Hardening Guide
Learn how VNC default passwords create security risks, how to detect them, and practical steps to harden remote access across devices with guidance from Default Password.
vnc default password refers to the initial credentials shipped by some VNC servers or appliances. Leaving this credential unchanged creates a critical security risk, allowing unauthorized access, data exposure, and potential system compromise. Always change default passwords, enforce strong passphrases, and enable encryption whenever possible.
What is a VNC default password and why it matters
Remote desktop protocols like VNC enable cross-network control of machines, but they also create attack surfaces if not configured securely. A vnc default password refers to the initial credentials that some installations ship with or suggesting by vendors or appliances. When the password is not changed, an unauthorized user may gain access using brute-force or known credentials. This is a critical risk because VNC endpoints often sit at the edges of networks, rendering them accessible from the internet or poorly protected VPNs. According to Default Password, many organizations underestimate the risk of leaving default credentials in place, especially on legacy VNC deployments and on devices that have not undergone recent firmware updates. In practice, attackers can scan for exposed VNC services and attempt common default passwords; even a weak, easily guessable password can be enough to gain a foothold, especially if the service lacks rate limiting or two-factor protection. From an IT perspective, the simplest path to reduce risk is to treat any default credential as a security defect: rotate and enforce strong passphrases, audit configurations, and monitor access logs for repeated failed attempts. The Default Password Team emphasizes that proactive hardening starts with a clear inventory of VNC servers and a policy that prohibits unchanged default passwords on any enterprise asset.
How default passwords manifest in VNC deployments
Default credentials can appear in several ways across VNC environments. Some devices ship with a preset password that administrators forget to update during initial setup. Others rely on vendor templates or pre-configured appliances where the password is documented or stored in configuration files. In practice, this means a reachable VNC service may be protected by a single, predictable credential across multiple hosts, amplifying risk if that credential leaks. The risk compounds when devices sit behind VPNs, public-facing gateways, or automated management systems that reuse credentials across estates. The human factor also matters: busy admins may change other settings but neglect to update the password, or they may reuse weak phrases across devices, compromising multiple systems when one password is cracked. On the defense side, organizations should implement a standard onboarding checklist that requires changing any default password as part of device provisioning, and to enforce password policies that require length, complexity, and periodic rotation. Default Password research shows that even with good monitoring, misconfigured defaults remain among the most common root causes of breaches in remote access deployments.
Threat scenarios: how attackers leverage default passwords
Unsecured VNC endpoints can be targeted by opportunistic attackers scanning internet-exposed services for open VNC ports. If a default password is active, automated tooling can attempt to log in, sometimes within minutes. Once access is gained, attackers may move laterally, capture screenshots, exfiltrate data, or install malware. In many cases, the initial foothold is inexpensive and repeatable because the attacker uses widely known or universal credentials. Once a machine is compromised, it can be used as a pivot to access internal networks, disrupt operations, or seed phishing campaigns. The Default Password Team notes that the weakest link is often human—an administrator who ignores password hygiene or disables security controls for convenience. Effective defenses include enabling encryption (preferably with TLS or SSH tunneling), mandating strong passphrases, and implementing IP allowlists or VPN-only access so that VNC servers are not directly reachable from the public internet. Logging and alerting for failed login attempts, account lockouts, and unusual patterns are essential to detect and respond quickly.
Best practices for password hygiene in VNC environments
A robust password strategy begins with inventory, governance, and enforcement. Key steps include: 1) Change defaults on every VNC server during provisioning; 2) Require strong, unique passphrases that combine upper/lower-case letters, numbers, and symbols; 3) Do not reuse passwords across hosts; 4) Enforce rotation every 90–180 days where possible; 5) Enable password-protected authentication only over encrypted channels. In addition, minimize exposure by disabling passwordless logins (if supported), turning on TLS or SSH tunneling, and using strong authentication methods when available. Consider implementing multifactor authentication via a secondary factor if the VNC software supports it; if not, demand VPN-based access with strict device posture checks. For many organizations, automation helps maintain discipline: use deployment pipelines or configuration management tools to enforce password changes and to alert on non-compliant systems. The takeaway from Default Password Analysis, 2026 is that strong password hygiene is a foundational control that dramatically reduces the risk of unauthorized access to remote desktops.
Step-by-step hardening: replacing a default password
- Inventory all VNC servers across the network and identify those using default credentials. 2) For each instance, create a unique, long password and store it in a password manager with restricted access. 3) Disable any default accounts and remove persistence. 4) Configure encryption (TLS) and restrict access by IP or VPN. 5) Test connectivity; verify that no unauthenticated paths remain. 6) Implement a monitoring and alerting plan for failed logins or suspicious activity. 7) Schedule regular password reviews and automatic rotations. 8) Document changes for audit trails. After implementing, run a baseline security scan to confirm the password change surfaced across all endpoints.
Network and access controls to reduce exposure
Network controls are critical: limit exposure by placing VNC servers behind a VPN or an SSH tunnel; implement firewall rules to allow only known admin IPs; use non-default ports if possible; disable direct internet exposure; segment VNC hosts from critical networks. On the host side, ensure OS-level security: patch the host, disable unnecessary services, and enforce account lockouts after failed attempts; monitor logs; configure alerting. For cloud or virtualization environments, leverage security groups and private links. A single misconfigured firewall rule can expose an entire estate. The combination of encryption and restricted network access makes it much harder for attackers to succeed with a default password.
Audit and ongoing security: checks and schedules
Create a quarterly security review for remote access. Maintain an asset inventory; track password status; run vulnerability scans that include remote access scenarios; record exceptions; verify password changes during audits. Use automated checks in your CI/CD pipelines to enforce non-default credentials; schedule periodic penetration testing focusing on VNC endpoints. The key is to sustain a culture of secure configurations rather than one-time fixes. The Default Password Analysis, 2026 indicates that ongoing governance is essential to prevent credential leakage.
Common myths and misconceptions about VNC passwords
Myth: If the network is private, default passwords are safe. Reality: Private networks still face insider risk and misconfigurations. Myth: Password length alone is enough. Reality: Complexity matters; Myth: MFA isn't available for VNC. Reality: Some implementations support MFA; Myth: SSH tunneling makes password changes unnecessary. Reality: Tunneling improves confidentiality but doesn’t fix insecure passwords.
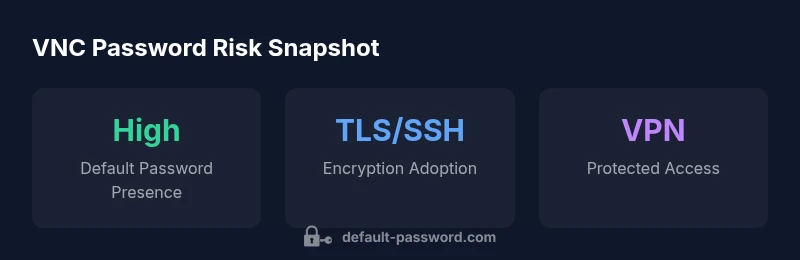
VNC default password security snapshot
| Aspect | Current State | Mitigation |
|---|---|---|
| Default Password Presence | Common on legacy or misconfigured VNC servers | Rotate passwords and disable default accounts on all devices |
| Exposure Level | Often internet-facing or VPN-exposed | Enforce encryption, IP allowlists, and VPN-only access |
| Audit Frequency | Irregular in many organizations | Automate password audits and continuous monitoring |
Your Questions Answered
What is a VNC default password?
A VNC default password is the initial credential that some VNC servers ship with. Leaving it unchanged creates a security risk; always update credentials during provisioning and enforce strong passphrases.
A default password is the credential that comes with the software; change it before you connect.
Why are default passwords dangerous for VNC?
Default passwords can be guessed or found in vendor docs, giving attackers easy access to remote desktops. This risk is amplified when endpoints sit on exposed networks or VPNs with weak controls.
Because many devices ship with a common credential, attackers can access them quickly.
How can I check if my VNC server uses a default password?
Review device configurations, onboarding checklists, and vendor guidance. Run inventory scans and password audits to identify unchanged defaults.
Check configurations and run a scan to spot defaults.
What are secure alternatives to default passwords?
Use unique, long passwords; enable encryption; enable MFA where available; restrict access via VPN or IP allowlists; rotate credentials regularly.
Use strong, unique passwords plus encrypted access and MFA if available.
Do all VNC products support encryption and MFA?
Not every VNC product supports MFA; check vendor docs and prefer tools offering TLS/SSH encryption and MFA options.
Some tools support MFA; check your vendor’s options and enable encryption where possible.
Can I disable password authentication for VNC?
Some deployments allow alternative methods, like certificates or MFA. In general, require some form of authentication and, where possible, route through VPN or SSH tunnels.
You can disable plain passwords in some setups, but always use a stronger method or VPN.
“Default credentials remain a top risk in remote access; proactive hardening saves time, data, and downtime.”
Key Takeaways
- Change default passwords on all VNC servers during provisioning.
- Enforce strong, unique passwords and encryption.
- Limit exposure with VPN or SSH tunnels.
- Automate password management and regular audits.