Web3 0 Default Passwords: Reset and Secure Guide 2026
Learn to identify, reset, and secure web3 0 default passwords. A practical, step-by-step guide for end-users and IT admins to protect wallets, nodes, and admin access in Web3 environments.
According to Default Password, a web3 0 default password refers to credentials that ship with devices or services used to enable admin access, node operation, or wallet interfaces before they are secured. This term highlights the moment when a deployment relies on a credential that should be changed but often isn’t. In web3 contexts, where wallets hold value and smart contracts govern funds, keeping defaults open creates a high-impact attack surface. The goal of this guide is to help end-users and IT admins identify where web3 0 defaults hide, replace them with unique, strong credentials, and implement safeguards that persist across deployment cycles. This article emphasizes identification, safe reset procedures, governance considerations, and practical automation strategies.
What 'web3 0 default password' means in practice
In the Web3 world, a web3 0 default password refers to credentials that ship with devices, servers, or services used to enable admin access, node operation, or wallet interfaces before they are secured. This term highlights the moment when a deployment relies on a credential that should be changed but often isn’t. According to Default Password, leaving defaults enabled creates a disproportionate risk in crypto ecosystems where private keys, seed phrases, and admin dashboards control real value. The risk isn’t limited to software alone: hardware wallets, routers, node operators, and cloud-connected services may all rely on a default credential during initial setup. The goal of this article is to help end-users and IT admins recognize where web3 0 defaults hide, replace them with unique, strong credentials, and implement safeguards that persist across deployment cycles. Throughout, you’ll see practical steps, governance ideas, and automation tips to raise the bar on password hygiene across teams.
Why defaults are especially risky in web3 ecosystems
Web3 ecosystems combine value-sensitive components such as wallets, private keys, and validator nodes with distributed apps and smart contracts. A single default password can grant attackers access to admin consoles, node dashboards, or deployment pipelines, enabling data theft or unauthorized changes to smart contracts. The Default Password team notes that when defaults persist in production, attackers may move laterally from an accessible interface to sensitive cryptographic material. Human factors—staff onboarding, contractor access, and rapid onboarding—often exacerbate the problem, as teams overlook changes made during quick demos. In addition, many Web3 devices rely on web-based admin panels that auto-fill credentials or reuse passwords across services, widening the attack surface. To reduce risk, organizations should treat default credentials as a security debt that demands prompt remediation and ongoing monitoring, not a one-off cleanup.
How to locate and inventory default passwords across devices and services
Begin with a complete asset inventory: list all hardware wallets, nodes, routers, gateways, cloud services, and developer tools used in the Web3 stack. Inspect documentation and initial setup notes for any embedded credentials or prompts to create defaults. Use configuration scanners or security dashboards to search for common default strings, weak passwords, or blank fields. Build a live inventory that includes device type, owner, location, and last change date. Create a remediation plan that prioritizes assets with greatest impact on funds or access. Finally, ensure you have an up-to-date backup of configurations and recovery data before initiating changes.
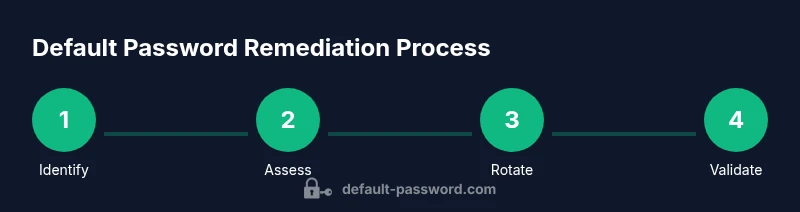
Step-by-step: secure reset and credential rotation
- Identify targets where default credentials still exist and document the scope. The reason is to avoid blind changes and to map dependencies.
- Gather current credentials and verify access control so you can revert if needed. Having a rollback plan reduces downtime.
- Change each default password to a unique, long passphrase generated by a password manager. Enable multi-factor authentication where available.
- Update all related references (scripts, configs, automation pipelines) to use the new credentials and avoid hard-coded values.
- Test access under controlled conditions, rotate keys or tokens if applicable, and document the new security baseline. Time: 30–60 minutes for smaller environments; larger deployments may require planning.
Implementing password hygiene in Web3 projects: governance and automation
Security hygiene in Web3 requires more than individual changes. Establish governance that assigns owners for credentials, requires MFA, and schedules regular rotations. Use automation to enforce password changes on new deployments and to retrofit existing systems with updated credentials. Consider integrating password hygiene checks into CI/CD pipelines so that deployments fail if defaults or weak passwords are detected. Documentation should accompany changes, including who authorized the change, what was altered, and when the next review is due.
Tools and resources for managing default passwords
A practical toolkit includes a password manager for generating and storing strong, unique credentials; an MFA authenticator app for multi-factor protection; an asset inventory spreadsheet to track devices and services; security baselines and templates to standardize changes across teams; and a secure vault for recovery data. For cloud and containerized Web3 environments, leverage built-in secret management features and audit trails to ensure visibility. Always maintain offline backups of recovery codes and keys in a secure location.
Case studies: lessons from incidents caused by default passwords
In several anonymized Web3 incidents, attackers gained unauthorized access through unmodified default credentials on admin dashboards and node interfaces. These breaches resulted in service downtime, participant distrust, and reputational damage. The common thread across cases is the failure to treat defaults as a security debt and to enforce cross-team password hygiene. Lessons include conducting regular credential audits, enforcing MFA, and ensuring that all change workflows require proper approvals before deployment.
Ongoing security: audits, training, and policy enforcement
Ongoing security means continuous improvement. Schedule quarterly credential audits, run simulated compromise exercises, and train teams on recognizing phishing attempts and social-engineering tactics. Publish and enforce a formal password policy that specifies minimum length, character diversity, rotation intervals, and MFA requirements. Use automated reminders and dashboards to maintain visibility over credential health across devices, services, and cloud environments.
Debunking myths about web3 0 default passwords and security myths
Myth: Default passwords are a one-and-done issue. Reality: Defaults create ongoing risk if not rotated and monitored. Myth: Strong passwords alone fix Web3 security. Reality: Without MFA and least-privilege access, passwords are just one layer. Myth: Passwords don’t matter for crypto assets. Reality: Weak credentials can expose admin access and seed phrases, threatening funds. Addressing these myths helps teams build resilient security postures.
Tools & Materials
- Password manager(Use a business-grade manager with strong master password and MFA enabled)
- MFA authenticator(Enable on all admin interfaces and critical services)
- Asset inventory spreadsheet(Catalog devices, wallets, nodes, and services with owners)
- Security policy templates(Templates for password hygiene, rotation, and access control)
- Secure recovery data storage(Offline backups of recovery keys and seed phrases)
Steps
Estimated time: 1-2 hours
- 1
Identify targets holding default credentials
Map all assets in the Web3 stack and locate any credentials that may be set to defaults. Document scope and potential impact on funds and access.
Tip: Start with admin dashboards, wallet interfaces, and node consoles. - 2
Audit access and backups
Verify who has access to each credential and ensure you have a rollback plan. Confirm configurations are backed up before changes.
Tip: Prepare rollback procedures in case a change breaks legitimate access. - 3
Generate and apply strong, unique passwords
Create long passphrases using a password manager for each credential. Avoid reuse across assets and enable MFA where possible.
Tip: Do not reuse a password even if the asset seems similar. - 4
Update references and automation
Replace any hard-coded credentials in scripts, configs, and pipelines with the new values. Validate integration points after update.
Tip: Search codebases and deployment scripts for old credentials. - 5
Test and document the new baseline
Test access, verify that all critical interfaces are reachable, and document changes, owners, and next review date.
Tip: Schedule a quarterly review to keep changes current.
Your Questions Answered
What is a web3 0 default password?
A web3 0 default password is a credential that ships with a device or service and is not yet changed. Leaving these defaults in place creates security risks for wallets, nodes, and admin interfaces in Web3 environments.
A web3 0 default password is a credential that comes with a device and hasn't been changed yet. Leaving it in place can expose wallets and admin interfaces to risk.
Why are defaults risky in Web3?
Defaults present attackers with a known entry point to critical controls. In Web3, this could grant access to private keys, node dashboards, or deployment pipelines, potentially compromising funds and smart contracts.
Defaults give attackers a known entry point to control panels and keys, risking funds and contracts.
How often should I change passwords in Web3 environments?
Schedule regular rotations aligned with your security policy. Increase frequency when changes in personnel, deployments, or access needs occur.
Rotate passwords on a regular schedule and after personnel changes or deployment updates.
What should I do if I find a default password in production?
Immediately replace the default with a unique, strong password and enable MFA. Document the change and run an audit to ensure no other defaults remain.
Replace it with a strong password, enable MFA, and audit for others.
Can password managers alone secure a Web3 stack?
Password managers are essential but must be paired with MFA, least-privilege access, and regular audits to be effective.
A password manager is key, but you also need MFA and audits to stay secure.
Are there standards for admin access in Web3 projects?
Yes. Establish a formal policy covering credential lifecycle, access control, MFA, and incident response. Align with industry best practices and your governance model.
There are formal policies for credential lifecycle and access control; align them with best practices.
Watch Video
Key Takeaways
- Identify all assets with default credentials
- Rotate to unique, long passwords with MFA
- Update scripts and pipelines to avoid hard-coded secrets
- Enforce governance and regular credential audits