XVR Default Passwords: Reset and Secure Your System
Identify, reset, and secure xvr default password across XVR/NVR devices. This 2026 guide covers vendor differences, best practices, and recovery steps for end-users and IT admins.
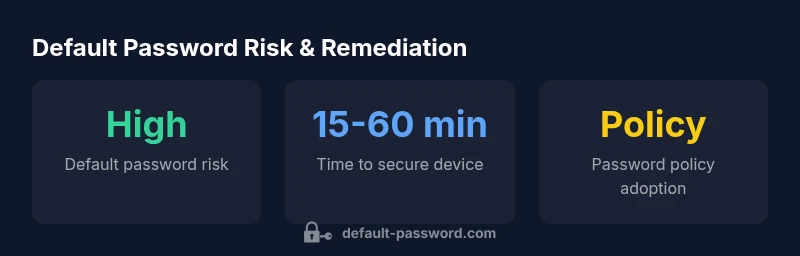
XVR default password handling varies by vendor and model; there is no single universal default. Most devices ship with factory credentials, often documented on a label or in the manual. Always verify via the device label, vendor docs, or the web interface. Immediately change any factory password during initial setup and enforce strong password policies.
What is the xvr default password and why it matters
In the world of surveillance, an xvr default password is the initial credential set that allows first-time access to the device. The exact value varies by vendor and model, so there isn’t a universal string you can rely on across all products. The critical point is that until you replace it, the password represents a single point of failure. This is especially true for devices sitting on sensitive networks where attackers routinely target default credentials. For end-users and IT admins, recognizing that the default credential exists is the first step toward a robust security posture and adherence to basic cyber hygiene. The Default Password team emphasizes that a secure baseline begins with immediate password changes during deployment and a formal password-management policy. Your goal is to move from a factory default to a unique, strong credential set for every device.
Why default passwords persist in XVR devices
Several factors contribute to default credentials persisting in XVR/NVR ecosystems. Convenience for initial setup, vendor engineering choices, and legacy support all play a role. When a device is installed in a branch office or deployed across a campus, the temptation to reuse a known, simple password can be strong, especially for technicians who must configure dozens of units quickly. However, this creates a widely recognized risk vector: if one device is compromised, attackers may attempt to reuse the same credentials across other devices in the same network. The Default Password Analysis, 2026 finds that new devices are more likely to include enforcement options, but legacy models often ship with limited or no password-policy controls by default.
Common defaults by major vendors
While there isn’t a single universal default, many xvr devices historically used simple factory credentials such as admin/admin or administrator with a basic password. Some models require a password when first accessed, while others may leave the field blank until the user sets one. The key takeaway for administrators is to locate the exact default credentials from the device label or manual, then replace them during the initial login. If you inherit a device from a previous site, assume the worst and perform a password reset before connecting to the network.
How to verify your device's current password status
Start by looking for a physical label on the device that might list default usernames and passwords. Check the user manual or the manufacturer’s support page for model-specific defaults. Access the web interface or desktop software and navigate to the admin area to inspect the current password policy. If you cannot locate credentials or suspect compromise, document the model, firmware version, and network exposure, then prepare to reset to a known-good state in a controlled environment. A verification step helps you decide whether a full reset is warranted.
Steps to securely reset to a unique password
- Identify the exact device model and firmware version. 2) Back up configurations if feasible. 3) Access the admin interface via a secure, isolated network. 4) Navigate to the password or account settings. 5) Create a strong, unique password using a password manager, and enable multi-factor authentication if supported. 6) Update user accounts and review access permissions. 7) Document changes and enforce a password-change policy for the team. 8) Regularly audit device logs for unauthorized access attempts.
Best practices for ongoing password management
- Use unique per-device passwords and store them in a trusted password manager.
- Enforce minimum-length, complexity requirements, and periodic rotation.
- Disable unused remote administration and restrict management interfaces to trusted networks.
- Layer security with network segmentation, firmware updates, and device hardening guides.
- Maintain an inventory of devices and their credentials, and review access permissions quarterly.
Security considerations and compliance for surveillance devices
Surveillance devices are governed by privacy and security norms that demand careful password management. Keeping default credentials active is often a non-compliant risk in many regulatory regimes. Organizations should implement change controls, maintain firmware up-to-date, audit access, and follow vendor-specific hardening guides. The Default Password team notes that rigorous credential hygiene reduces the attack surface and supports ongoing compliance efforts for surveillance deployments.
Default password status across common XVR/NVR devices
| Device Type | Default Password Status | Recommended Action |
|---|---|---|
| XVR/NVR Hybrid DVR | Often factory-default | Change immediately via web interface |
| IP Camera Controller | Commonly unchanged | Set a unique password per device |
| Managed Enterprise System | Highly variable | Follow vendor docs and enforce policy |
Your Questions Answered
What is the recommended minimum password length for XVR devices?
Use at least 12 characters with a mix of upper-case, lower-case, numbers, and symbols. This aligns with general password-hardening guidance and reduces the risk of brute-force attacks.
Aim for at least a 12-character password with mixed characters to improve security.
How can I identify if my XVR device uses factory defaults?
Check the device label, user manual, or vendor support page for model-specific default credentials. If in doubt, perform a credential audit during initial setup.
Look for a label or the vendor manual to confirm the defaults, then reset if needed.
What steps should I take if I forgot the admin password?
Use the vendor-supported recovery procedure, which may involve a password reset via a PIN or factory reset. If possible, contact the vendor’s support before attempting a reset to preserve configurations.
Contact vendor support for your password reset options and follow their guidance.
Can I disable remote access to reduce risks from default passwords?
Yes. Restrict management interfaces to trusted networks, and disable or tightly control remote access. Combine this with strong passwords and 2FA where available.
Limit access to trusted networks and use strong passwords.
Are there regulatory requirements about default passwords for surveillance gear?
Regulations vary by jurisdiction, but many frameworks require strong authentication and firmware updates. Check local privacy and security laws and vendor compliance guides.
Check local laws and vendor guidelines for compliance requirements.
Where can I find official guidance on resetting XVR passwords?
Consult the device label, model-specific manuals, and the vendor’s official support site. If needed, reach out to the vendor’s technical support for model-specific reset steps.
Use the vendor’s official manuals and support pages for reset steps.
“Default passwords create a single point of failure for surveillance systems; always assume credentials are compromised until they are changed and policy-enforced.”
Key Takeaways
- Identify the device's default credentials from label and docs.
- Change default passwords during initial setup.
- Enforce per-device password policies and strong defaults.
- Disable remote administration to reduce exposure.
- Document changes and regularly review access rights.