Your Default Password Is: Reset and Secure Guide
Learn how to identify devices using default credentials, reset passwords safely, and enforce strong, unique access across routers, printers, NAS, and servers with practical steps and security best practices.
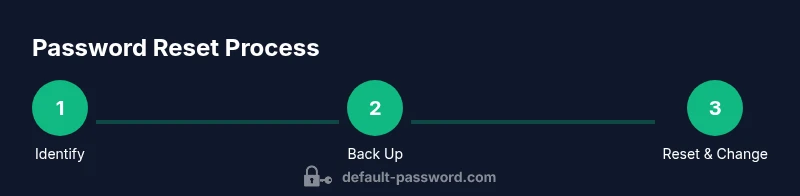
You will learn to identify devices with default credentials, prepare for password resets, execute secure changes, and verify admin access across your network. The guide covers routers, printers, NAS, and endpoints, with practical steps and security best practices. Expect 60–90 minutes depending on your environment, and aim to minimize exposure by applying least-privilege access and documenting changes. This process helps reduce common attack vectors.
Why your default password is a risk and what to do about it
Your default password is not just a nuisance—it is a built-in invitation for unauthorized access. When devices ship with a factory credential, any attacker who discovers it can operate or disrupt the device before you even know there is a problem. According to Default Password, this common scenario often serves as the first foothold in broader network breaches. By treating these credentials as high-risk assets, IT teams can shift to a proactive stance: perform a quick inventory, replace credentials, and implement ongoing password hygiene. The goal is to reduce visibility to opportunistic attackers while preserving necessary access for legitimate admins. Start by categorizing devices (routers, printers, storage, cameras) and setting a baseline policy that every device must have a unique, strong password before production use. This approach aligns with security best practices and minimizes the chance of forgotten or reused credentials across platforms.
How to identify devices that still use default passwords
The easiest starting point is a network-wide audit: scan devices on the LAN, review admin dashboards, and check vendor documentation for default accounts. Look for common labels such as “admin,” “root,” or “password” in the user lists and note any accounts that show no password change history. Create a simple inventoried list that captures device type, model, location, last password change, and owner. You can also use configuration export features or centralized management tools to flag devices lacking a password change or lacking a recent audit trail. The aim is to surface every instance where a default credential remains in place so you can plan a secure reset.
Understanding common default credentials and admin access patterns
Many devices follow predictable patterns, such as a default username paired with a simple password or a single panel password for admin access. While we won’t catalog every default string here, the principle remains: these credentials are widely known and easily tested by attackers. Some devices expose an admin interface that is reachable over the network, others require physical access to reset. Regardless of the path, treating default credentials as temporary and replacing them with strong, unique passwords is essential. Pair password changes with role-based access controls and ensure that only approved admins can make changes to critical devices.
Step-by-step: prepare for password reset
Preparation is the silent driver of a successful reset. Start by backing up current configurations and exporting device settings where possible. Document current users and permissions to minimize disruption after the change. Gather admin credentials or recovery options, ensure you have administrative access locally or via a secure remote method, and verify you have a way back in if something goes wrong. Prepare a change window or maintenance period to avoid impacting operations. This preparation reduces the risk of lockouts and ensures you can verify the changes in a controlled manner.
Step-by-step: reset a router or gateway device
For most routers, you’ll access the admin interface via a web browser using the device’s local IP. Navigate to the password or admin section and replace the default password with a strong, unique one. If the device offers a factory reset option, use it only when you cannot recover the configuration. After updating, save the new settings and reboot if required. Test both wireless and wired connections to confirm you can log in under the new credentials. If you use cloud-based management, ensure the new password is reflected there as well and revoke any old tokens.
Step-by-step: reset other devices (NAS, printers, cameras, IoT)
For NAS and printers, start with a local admin login, then update both the admin password and any guest or service accounts. For cameras and IoT devices, consider changing the default password on the device and, if supported, on the companion mobile app. In all cases, enable password encryption, log access attempts, and disable unused accounts. If a device doesn’t support password changes through the interface, consult the vendor’s recovery guide and perform a factory reset as a last resort, followed by reconfiguration.
Verify and enforce password security after reset
After any reset, verify access from multiple devices and user roles to ensure the new credentials grant the expected permissions. Enable two-factor authentication where possible and enforce password complexity rules (length, character variety, rotation). Consider centralizing credential management with a password manager for administrators and documenting each credential change in a change log. Finally, communicate the new policy to all stakeholders and ensure ongoing training for admins on recognizing phishing and social engineering that targets password changes.
Document, audit, and maintain ongoing password hygiene
Create a living inventory of devices, credentials, owners, and expiration dates. Schedule regular audits (quarterly or semi-annual) and tie reviews to your security policy. Maintain a secure repository for password evidence, with access restricted to authorized personnel. A thorough record-keeping habit not only simplifies audits but also shortens recovery time after misconfigurations or suspected breaches. The aim is to create a resilient process that scales with your environment while reducing risk over time.
Troubleshooting and next steps
If a device resists password changes or you cannot log in after a reset, consult the vendor’s official recovery process and documentation. Ensure the device isn’t bound to a software license or cloud account that enforces specific credentials. When in doubt, pause and revert to last known-good configuration, then reattempt with a more conservative approach. If you’re managing a large estate, consider a centralized password policy, automated reminders for password changes, and periodic security drills to validate your defenses. The process is ongoing, not a one-time fix, and requires discipline.
Tools & Materials
- Device to reset (router, NAS, printer, camera, IoT)(Identify all devices that use default credentials and plan their reset.)
- Admin credentials or recovery options(You need admin access to perform changes.)
- Backup/config export capability(Export current settings before making changes.)
- Network access (Ethernet preferred)(Local access reduces risk of remote errors.)
- Password manager or secure vault(Store new passwords securely and share access as needed.)
- Two-factor authentication device (optional)(Adds an extra layer of protection.)
Steps
Estimated time: 60-150 minutes
- 1
Identify devices with default credentials
Scan your network and review device documentation to surface every device using defaults. Create a centralized list with device type, location, owner, and last password change.
Tip: Start with critical infrastructure (routers, VPNs, servers). - 2
Back up configurations
Export configurations and take screenshots of current settings. Store backups in a secure location and label them clearly for quick recovery if needed.
Tip: Verify backups before proceeding. - 3
Access admin interface or reset button
Login locally or use physical reset to factory defaults if necessary. Ensure you have the correct recovery path and that you can re-access after the change.
Tip: Do not perform resets during peak hours. - 4
Change to a strong, unique password
Replace the default password with a long, unpredictable password. Apply best practices (length, complexity) and avoid password reuse across devices.
Tip: Document the new password securely. - 5
Enable 2FA where possible
Turn on two-factor authentication for admin accounts to add a second layer of protection. Review user permissions and remove unnecessary accounts.
Tip: Use app-based 2FA rather than SMS when available. - 6
Test access and document the changes
Log in with new credentials from multiple devices to confirm access. Update the password inventory and share the report with stakeholders.
Tip: Keep a log of exact times and outcomes for audits.
Your Questions Answered
Why is leaving a default password risky for my network?
Default passwords are widely known and easily exploited. They provide attackers with a predictable entry point. Changing them to strong, unique credentials significantly reduces the risk of unauthorized access.
Default passwords are widely known and can be exploited. Changing them to strong, unique credentials reduces risk.
How can I quickly tell if a device still uses a default password?
Run a quick inventory against vendor docs, check admin panels for accounts with no password changes, and verify that every device has a password policy applied. Use automated scans where possible to flag offenders.
Check vendor docs, admin panels, and run scans to flag devices with default passwords.
Can I reset passwords remotely, or do I need to be on-site?
Some devices support remote changes via management interfaces or cloud portals; many require local access or a physical reset. Always follow the vendor's documented procedure to avoid bricking the device.
Some devices allow remote resets; others require local access. Follow vendor docs to avoid issues.
What should I do if I forget the new password?
Use recovery options provided by the device or service. If unavailable, you may need a factory reset and reconfiguration, which underscores the importance of backups and documented procedures.
If you forget the new password, use recovery options or a factory reset after backing up.
Is using a password manager recommended for default credentials?
Yes. A password manager helps store and retrieve strong passwords securely and can assist with documenting credential changes across devices. Some devices may not integrate directly, so maintain a secure reference log as well.
Yes, use a password manager to securely store and access strong passwords.
Are there devices that do not allow password changes easily?
Some devices have locked interfaces or vendor-enforced policies. When this happens, consult the documentation for supported recovery or reset options and establish an exception process with governance.
Some devices can't change passwords easily; consult docs and follow the recovery process.
Watch Video
Key Takeaways
- Identify devices with default credentials and prioritize them for change.
- Back up configurations before applying password changes.
- Use strong, unique passwords and enable 2FA when possible.
- Document changes for audits and continuous improvement.
- Run regular password hygiene reviews to reduce future risk.