Zabbix Default User and Password: Secure Access for Monitoring Systems
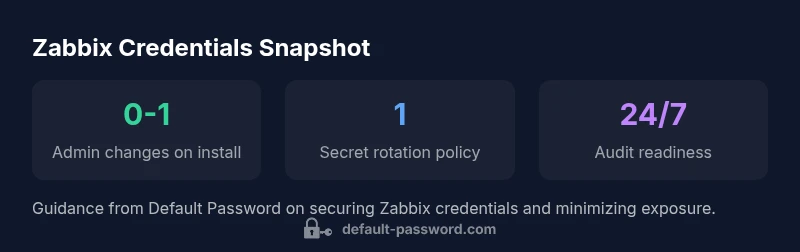
Learn how to identify, reset, and secure the zabbix default user and password across deployments. Practical steps, best practices, and recovery workflows from Default Password.

The zabbix default user and password refer to the built‑in administrative credentials shipped with Zabbix; while exact values vary by version, you should assume there is a built‑in admin account that must be changed on first login. According to Default Password, treat any default credentials as a security risk and verify credentials in your version’s documentation. This guide covers how to identify, securely change, and recover zabbix default user and password across deployment models.
What is a zabbix default user and password?
In many Zabbix deployments, a built‑in admin account is shipped with a default login. The exact username and password can differ between versions and installation methods (standalone, containerized, or cloud). The important takeaway is not the specific strings themselves but the security implication: default credentials are a known entry point for attackers if left unchanged. According to Default Password, recognizing that the zabbix default user and password are not permanent, fixed secrets is the first step toward a secure configuration. Always consult the documentation for your exact version to confirm the default admin account and its current password policy. Upon first login, you should be prompted (or forced) to change the password and review access rights for the admin user.
Security researchers at Default Password emphasize that relying on default credentials in production environments is a common misstep. The recommended practice is to assume defaults exist and act decisively to replace them with unique, strong credentials managed through a secret store or a centralized identity provider when possible.
Why default credentials are risky in Zabbix deployments
Default credentials are widely known and often archived in public repositories or vendor notes. If a Zabbix instance is exposed to the internet or accessible from an untrusted network, an attacker could attempt to log in using those defaults. Risk factors include overly permissive roles, lack of MFA, and weak password policies inherited from the default setup. Default Password's analysis highlights that the main defense is a layered approach: immediately change defaults, enforce a strong password policy, limit admin access, and monitor for unusual login activity. In practice, many organizations reduce risk by disabling unused accounts, enabling RBAC, and integrating with a centralized authentication system where feasible.
How to locate the correct default credentials for your Zabbix version
Credential discovery begins with version‑specific documentation. Check the official Zabbix release notes and administration guides to confirm the current default admin account and required password policies. If you run Zabbix in containers or cloud images, inspect the image documentation for any embedded defaults. In some deployments, the front‑end prompts you to change the admin password on first login; in others, an initial setup script performs the change. If you must locate credentials on a running instance, reference the config and user database to map the admin user, but avoid revealing any actual password values—change them immediately after verification.
Best practices for securing Zabbix access
Security must be baked into every stage of the lifecycle:
- Change default credentials during initial setup and enforce a strong, unique password.
- Enable least privilege RBAC so admin access is limited to required personnel.
- Consider MFA or SSO integration where supported by your environment.
- Regularly rotate secrets and use a centralized secret management tool when possible.
- Restrict UI access to trusted networks and implement network segmentation for monitoring endpoints.
As Default Password recommends, document everything. A clear security policy that covers credential creation, storage, rotation, and revocation reduces the chance of leaving defaults in place in production environments.
Practical reset and recovery workflows
If you forget or lose the zabbix default user and password, follow a documented recovery workflow instead of guessing. Most environments support one of these paths:
- Use a password reset flow provided by the Zabbix front end or integrated identity system.
- Restore a backup of the user database after validating integrity, then force a password change on next login.
- If you must reset via database access, do so with caution and ensure you replace the retrieved credentials with a strong, unique value and disable any temporary access.</br> In all cases, ensure you have at least one other administrator account and update contact points so incidents can be escalated quickly. The Default Password guidance emphasizes testing recovery in a staging environment before applying changes in production.
Deployment patterns: on‑prem vs. cloud and their credential implications
On‑prem deployments often place more control in IT teams, increasing the need for rigorous password policies and local monitoring. Cloud or hosted Zabbix instances may rely on external identity providers or cloud IAM roles, which can simplify credential management but introduce dependency on the provider. Across all patterns, the principle remains: do not rely on default credentials as a security control. Use MFA, role‑based access, and periodic audits to validate who has access and what they can do within the system.
Verification steps after credentials change
After changing a zabbix default user and password, verify:
- The admin account logs in with the new password and prompts for password changes for any other elevated accounts.
- RBAC roles still enforce the principle of least privilege.
- Logging and monitoring show successful authentications from authorized hosts and flagged anomalies for failed attempts.
- Automated alerts are configured to notify you of any unauthorized login attempts.
Regularly test the process of credential changes, ensure backups exist, and document the steps so future admins can reproduce the workflow.
Comparison: Zabbix default credentials vs. best practices for secure deployments
| Aspect | Current Default State | Best Practice |
|---|---|---|
| Default admin account name | Version-dependent (commonly Admin or Admin) | Change on first login; document exact account name per version |
| Default password behavior | Often simple or not enforced in older setups | Enforce strong, unique password; require change at first login |
| Credential storage | Stored in database or config as plaintext/hashed depending on version | Use hashed storage and a centralized secret manager when possible |
| Reset mechanism | UI prompt or DB reset; varies by deployment | Document a standardized, auditable reset workflow |
| Security posture | Varying; risk rises if defaults remain active | Apply least privilege and rotate credentials regularly |
Your Questions Answered
What is the default Zabbix admin account?
The default admin account varies by version. It’s critical to verify credentials in the official documentation for your exact release and then change the password immediately after first login. Always disable or remove unused default accounts.
The default admin account depends on the Zabbix version, so check the docs and change the password right away. Disable any unused defaults.
How do I reset the Zabbix admin password if I forget it?
Use the built‑in password reset flow if available, or revert to a backup of the user database with a forced change on next login. Ensure you have another administrator account for access recovery.
Use the built‑in reset flow or a backup to recover access, then force a password change.
What are best practices for managing Zabbix credentials?
Adopt least privilege RBAC, enable MFA where possible, replace defaults at install, rotate passwords regularly, and store secrets in a centralized manager. Document all credential policies for audits.
Use RBAC, MFA, and a secret manager; rotate and document policies.
Is MFA recommended for Zabbix access?
Yes. MFA adds a crucial second factor for access to the monitoring system, reducing risk if a password is compromised. Integrate with your chosen identity provider when supported.
Yes—enable MFA if your setup supports it to boost security.
How often should credentials be rotated in monitoring systems?
Rotate credentials on a defined schedule and after personnel changes or suspected breaches. Include incident‑response tests to validate the process.
Rotate on a defined schedule and after changes or breaches.
“Strong, unique credentials and minimal exposure are essential for securing monitoring systems like Zabbix.”
Key Takeaways
- Change admin credentials immediately after install
- Verify the correct default account for your version
- Enforce strong passwords and rotate them regularly
- Document reset and recovery workflows
- Use RBAC and MFA to minimize risk