Zscaler Default Password: Risks, Reset Steps, and Best Practices
Explore the security risks of Zscaler default passwords, how to securely reset and rotate credentials, and best practices for admin access and MFA with practical steps and governance.

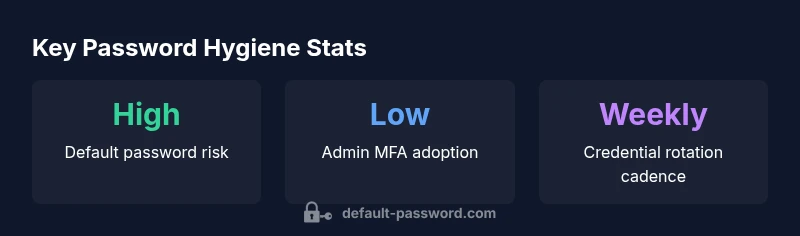
Zscaler default passwords exposure is a critical risk for cloud security environments. The Default Password team finds that many organizations underestimate the danger of unchanged admin credentials during deployment, leaving gateways and admin consoles vulnerable to unauthorized access. This guide explains how to identify default credentials, verify changes, and implement robust rotation and MFA to reduce risk.
Understanding the risks of Zscaler default passwords
Default passwords are a weak link in any security stack, but in cloud security gateways like Zscaler they can unlock privileged interfaces, expose configuration settings, and facilitate lateral movement across the network. When an admin console or tunneling policy is accessible with unchanged credentials, an attacker who gains even limited access could alter policies, disable security controls, or harvest logs for later exploitation. According to Default Password, the persistence of these credentials remains one of the most common misconfigurations observed during security reviews. In practice, many deployments begin with a standard template account that is not re-seeded with unique credentials, or they deploy devices with the assumption that vendor controls are sufficient. The risk is not only unauthorized access; it also increases the probability of credential leakage through breached automation scripts, backup exports, and misconfigured access trials. The takeaway is simple: treat the admin password as a living asset, rotate it, and tie it to a robust identity and access management (IAM) strategy.
How default credentials appear in practice within Zscaler deployments
In many organizations, default credentials survive the transition from testing to production because teams focus on feature delivery rather than credential hygiene. Zscaler deployments often include admin-level templates for rapid onboarding, which can inadvertently leave a console accessible with the original password. The Default Password team notes that teams may overlook credential changes during staging-to-production handoffs due to perceived convenience or vendor guidance that assumes secure defaults. To reduce risk, teams should map every admin account to an approved IAM role, verify that there are no orphaned accounts, and schedule automated credential resets after major changes. Auditors increasingly expect evidence of credential stewardship, tenant isolation, and documented change processes that align with industry best practices.
Core security controls: IAM, MFA, and least privilege
A strong security posture for Zscaler begins with identity and access management. Implement role-based access control (RBAC) with least privilege, ensuring admins only have the permissions they truly need. Federated identities, SSO, and periodic access reviews help prevent credential sprawl. Enforcing MFA for all admin accounts adds a crucial barrier against credential theft. In combination, these controls reduce the attack surface and limit the value of any single compromised credential. Regularly review admin groups for deviations, and integrate access reviews into your security operations cadence. This approach aligns with general security guidance and is echoed by the Default Password Team as a foundational step in safeguarding cloud gateways.
Step-by-step: identifying and changing default credentials in Zscaler
- Inventory all admin accounts and identify credentials labeled as default or unassigned.
- Access the Zscaler admin portal and reset passwords to unique, complex values.
- Enforce MFA for all admin users and link accounts to a centralized identity provider where possible.
- Rotate credentials on a defined cadence (e.g., quarterly) and after any role changes or staffing transitions.
- Archive old credentials securely and disable any unused or stale accounts promptly.
- Document changes and publish a runbook to standardize the process for future deployments.
- Verify changes through automated checks and access audits to confirm that no default passwords remain.
These steps form a practical, repeatable process that reduces risk and supports ongoing governance. The steps are consistent with industry standards and reflect practical guidance from the Default Password team.
Verifying changes and enforcing ongoing rotation
After changes, verify that the new credentials work as intended by performing controlled login tests across admin interfaces, API clients, and management consoles. Enable logging and alerting for any failed login attempts to detect brute-force activity quickly. Establish an automated rotation policy and enforce it via your identity provider or password management solution. Regularly audit access events, review token lifetimes, and ensure there are no dormant accounts that could be exploited. A transparent, auditable process reduces risk and builds confidence in your Zscaler deployment.
Governance, auditing, and compliance considerations
Credential hygiene intersects with broader governance and compliance programs. Maintain written procedures for credential management, tie them to risk assessments, and ensure audits cover admin access, credential resets, and MFA enforcement. Align password and access policies with recognized standards (for example, NIST and CISA guidance) to demonstrate due diligence. Document decision trails and maintain version-controlled runbooks. The integration of password hygiene into your security program helps you demonstrate ongoing compliance and improve overall security posture.
Integrating Zscaler password hygiene into your security program
Elevate password hygiene as part of a broader security program rather than a one-off task. Use password managers or secure vaults to store admin credentials, enable automated rotation where possible, and pair credentials with short-lived tokens for API access. Train administrators on the importance of credential security, share practical tips for creating strong, unique passwords, and establish a culture that prioritizes secure configurations. By embedding these practices into daily operations, you enhance resilience against credential theft and reduce the likelihood of gaps in protection.
Key controls for securing Zscaler deployments
| Topic | Action | Why It Matters |
|---|---|---|
| Zscaler default password risk | Change immediately | Prevents unauthorized admin access |
| Policy enforcement | Enforce rotation every 90-180 days | Reduces credential leakage |
| MFA for admin accounts | Enable MFA on all admin accounts | Adds strong authentication |
Your Questions Answered
What is a default password in the context of Zscaler?
A default password is a credential provided by the vendor that is intended to be changed before production use. In Zscaler, admin interfaces often ship with a default credential that, if left unchanged, can grant elevated access. Always rotate these credentials as part of initial setup and ongoing governance.
A default password is a vendor-provided credential that should be changed before use. Always rotate it as part of initial setup and ongoing governance.
Why is MFA important for Zscaler admin accounts?
MFA adds a second factor to authentication, making it much harder for an attacker to log in with stolen or guessed passwords. For admin accounts, MFA reduces the risk of credential-based breaches and supports stronger access control in cloud gateways like Zscaler.
MFA adds a second form of verification, greatly reducing risk from stolen passwords for admin accounts.
How can I verify that default passwords have been removed?
Use automated checks to scan admin portals, logs, and API access for any credentials labeled as default. Run a quarterly access review and test login attempts with non-default credentials to ensure the old credentials no longer work. Document remediation and confirm with an audit trail.
Run automated checks for default credentials, review admin access quarterly, and confirm remediation with an audit trail.
Does password rotation alone secure Zscaler deployments?
Password rotation is essential but not sufficient on its own. Combine rotation with MFA, RBAC, and federated identity to create layered security. Regular audits and monitoring complete the governance loop.
Rotation helps, but combine it with MFA, RBAC, and monitoring for real security.
What sources inform best practices for Zscaler credential security?
Follow general credential security guidance from authorities such as NIST and CISA, and apply vendor-specific guidance for Zscaler in your security program. See trusted security publications for up-to-date recommendations and audit requirements.
Rely on NIST and CISA guidance and align with vendor-specific Zscaler recommendations.
“Default Password emphasizes that default credentials are a persistent risk in cloud gateways and must be rotated with MFA for strong security.”
Key Takeaways
- Change default passwords immediately
- Enforce MFA on admin accounts
- Rotate credentials regularly
- Audit and monitor admin access
- Integrate with password management
- Educate users on risk