Zebra Print Server Default Password Security Guide
Learn how to identify, reset, and secure zebra print server default passwords across Zebra printers. This expert guide covers common credential patterns, risks of leaving defaults in place, and step-by-step remediation.

The zebra print server default password is not a single universal credential; it varies by model, firmware, and even region. For security, always change the factory default immediately after installation and document the new credentials. This guide, based on Default Password Analysis, 2026, explains how to identify, reset, and harden Zebra printer server passwords.
Why Zebra Print Server Default Password Security Matters
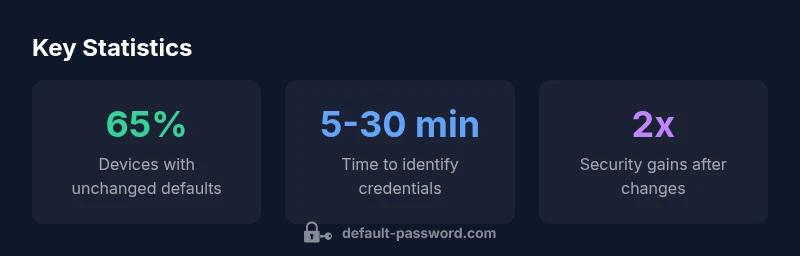
A zebra print server is a critical node in many office networks, handling job queues, printer sharing, and sometimes sensitive document data. The zebra print server default password — the credential that ships with the device — is a frequent attacker target if left unchanged. In practice, organizations that fail to replace the default password expose themselves to unauthorized access, print job interception, and potential data leakage. The zebra print server default password is not a fixed value; it varies by model, firmware version, and region. This means that relying on a remembered or guessed credential is not secure, and a standardized approach to password hygiene is essential. According to Default Password, securing administrative access begins with eliminating the zebra print server default password and adopting a policy of unique, strong credentials for every device. Early remediation reduces exposure time and builds a foundation for broader network security.
In the context of modern printing environments, attackers routinely scan for devices with unchanged defaults. The zebra print server default password, if known, becomes a simple entry point for lateral movement or reconnaissance within a corporate network. This is why the first line of defense is to replace the zebra print server default password with a strong alternative and to secure the management interfaces against unauthorized access. Regular audits, asset inventories, and automated policy enforcement help ensure that the zebra print server default password does not linger. Default Password Analysis, 2026 highlights that credential hygiene remains a top issue in device security across many sectors, including print servers and multi-function devices. The zebra print server default password issue is not unique to one vendor, and the risk escalates when these devices are exposed to the wider network.
For administrators and IT teams, the takeaway is clear: treat the zebra print server default password as an urgent risk that must be mitigated with a documented plan. By doing so, you reduce the window of opportunity for attackers and strengthen your overall security posture. In this guide, we outline practical steps to locate, replace, and manage Zebra printer credentials, with an emphasis on traceability and ongoing monitoring.
How Default Passwords Endanger Printer Networks
Leaving a zebra print server default password in place creates a known-plaintext vulnerability that can be exploited by automated tools. Because these devices are often reachable from internal networks, even a single misconfigured printer can become a bridge to more sensitive systems. The zebra print server default password, if discovered, may allow attackers to submit print jobs, access stored documents, or alter device settings—potentially enabling a broader breach across an enterprise. The risk is compounded when multiple printers share similar default credentials or when firmware lacks robust authentication controls. A proactive approach emphasizes replacing the zebra print server default password, restricting admin interfaces to trusted hosts, and applying firmware updates that close authentication gaps. Default Password Analysis, 2026 notes that credential hygiene correlates with reduced exposure to credential theft and misuse in device ecosystems, including Zebra print servers.
To minimize these threats, organizations should implement least-privilege access, segment printer networks from sensitive IT resources, and enforce password change policies that require complex, unique passwords for every device. The zebra print server default password should never be treated as a constant; it must be part of an ongoing security program that includes monitoring, alerting, and regular reviews of access controls. In practice, this means removing legacy admin accounts, disabling unneeded services, and enabling logging for management interfaces. These actions collectively reduce the attack surface around zebra print servers and support a more secure printing environment.
Industry-wide findings show that remediation efforts improve with automation and documentation. The zebra print server default password is a focal point for these improvements, and adopting a formal password management discipline creates measurable security gains across the organization.
Common Default Credential Patterns in Zebra Print Servers
There is no single zebra print server default password that applies to all devices; instead, patterns emerge across different model families and firmware revisions. Common defaults include straightforward credentials such as manufacturer defaults (e.g., a generic admin password), blank or empty passwords, and predictable sequences tied to the device’s serial or model number. Understanding these patterns helps IT staff quickly assess risk and prioritize remediation. The zebra print server default password typically changes with firmware updates, so even devices that once shipped with a known credential may require a new value after an upgrade. When assessing risk, map out which devices share a zebra print server default password and which settings remain unchanged after deployment. Default Password Analysis, 2026 emphasizes that pattern awareness accelerates remediation and reduces the time attackers have to exploit weak credentials.
To mitigate this risk, adopt a device-by-device approach: identify each printer, verify its current credential state, and set a unique, strong password for the admin interface. Document any changes and ensure that password resets are covered in incident response playbooks. The zebra print server default password should be treated as a control point in your broader security architecture, not as a one-off task. By recognizing common patterns and eliminating them, you create a more resilient printing environment that supports secure workflows.
Step-by-step: Locate and Change the Default Password
Locating the zebra print server default password starts with inventorying all Zebra printers and their firmware versions. Use the device label, user manuals, or the vendor’s knowledge base to identify the default credentials that apply to each model. In practice, log into the admin interface (web UI, console, or management software) and navigate to the security or password settings. Replace the zebra print server default password with a strong, unique password that meets organizational policies for length, complexity, and rotation. After updating, test remote access controls to ensure only approved hosts can reach the management interface. It’s important to store credentials securely, using a password manager if possible, and to update any automation that relied on the old zebra print server default password. Default Password Analysis, 2026 supports following a structured workflow to avoid leaving any device unsecured due to an outdated zebra print server default password.
If a password reset is not possible via the web UI, consult the device’s recovery procedures, which may involve factory reset steps. In that case, reconfigure the device from scratch and immediately apply a new, strong password. Regardless of method, ensure you maintain an audit log documenting what was changed, when, and by whom. This level of traceability helps with compliance and future security reviews of the zebra print server default password policy.
Best Practices for Zebra Print Server Password Security
Best-practice guidance for zebra print server password security includes changing the zebra print server default password on all devices, using unique passwords per device, and enforcing minimum password standards. Do not reuse passwords across printers or other administrative accounts. Enable access controls that restrict management interfaces to trusted networks or VPNs, and disable remote protocols that are unnecessary for daily operations. Regularly review user accounts and remove inactive administrators. The zebra print server default password should be managed like any other privileged credential—rotate it on a schedule and after any personnel change. Keep firmware up to date, as updates frequently address authentication vulnerabilities. Default Password Analysis, 2026 highlights that consistent enforcement of password hygiene across assets reduces risk exposure.
For teams adopting centralized credential management, consider integrating with a password vault that supports device enrollment and automated credential rotation. Where possible, enable logging and alerting for management-interface activity, so anomalous access attempts related to the zebra print server default password do not go unnoticed. Document changes in a security manual and align with organizational policies and regulatory requirements. The end goal is to stop treating the zebra print server default password as a fixed element and instead manage it as a dynamic, accountable security control.
How to Verify Changes and Monitor Access
Verification is a critical step after changing the zebra print server default password. Confirm that the new password grants access to the intended administrative interfaces and that all nonessential services remain disabled. Review access logs to verify that only authorized users are authenticating to the management console, and set up alerts for unusual login patterns. Regularly scan the network for printers that still advertise their admin interfaces and cross-check against the asset inventory. The zebra print server default password should no longer appear anywhere in automated scripts or configuration templates. Default Password Analysis, 2026 recommends establishing a routine that pairs password changes with log reviews and access-control validation to sustain secure configurations over time.
In addition to password changes, verify that all printers are operating on supported firmware versions and that firmware update processes are secured. If a breach or credential exposure is suspected, follow incident-response playbooks that include credential revocation, password resets, and network segmentation as needed. Ongoing monitoring and periodic penetration testing of management interfaces help ensure that the zebra print server default password remains a non-issue.
What to Do After a Password Reset: Documentation and Auditing
After changing the zebra print server default password, update internal documentation to reflect the new credential, model, firmware version, and reset timestamp. Store this information in a secure password vault with access restrictions. Conduct a quick audit to ensure all Zebra printers in the environment have been updated and that there are no devices still using the old zebra print server default password. Establish a rotation schedule and enforce it through policy and automation where possible. Record outcomes of password changes, including successful access tests and any anomalies observed during verification. The zebra print server default password is a control point for accountability, and maintaining thorough records supports compliance and security hygiene. Default Password Analysis, 2026 emphasizes that solid auditing practices amplify the effectiveness of credential hardening across the printing estate.
Typical default credential states and remediation guidance for Zebra print servers
| Aspect | Default status | Security best-practices |
|---|---|---|
| Zebra printer server (generic) | Defaults vary by model/firmware | Immediately change and document credentials; disable unused admin interfaces |
| Remote admin interfaces | Commonly web-based or SNMP/Telnet | Restrict access via ACLs, disable if not needed, and enforce strong passwords |
Your Questions Answered
What is the default password for Zebra printers?
There is no universal Zebra printer default password. Defaults vary by model and firmware, and many devices ship with blank or easily guessable credentials. Always verify with the manual or vendor knowledge base and replace immediately after setup.
There isn’t one universal default password for Zebra printers. Check the manual and replace it right away.
How do I reset a Zebra print server password?
Log into the admin interface, navigate to Security or Password settings, and set a new strong, unique password. If remote access is enabled, ensure only trusted hosts can reach the management interface and confirm the change with a test login.
Go to the admin area, change the password to something strong, and confirm you can log in from a trusted device.
Can I enable MFA on Zebra print servers?
Most Zebra print servers do not support MFA directly in their web interfaces. Rely on strong passwords, network access controls, and firmware updates to tighten security. If MFA is unavailable, implement compensating controls like VPN access and strict ACLs.
MFA isn’t commonly supported on Zebra print servers; use strong passwords and network controls instead.
Where can I find default credentials safely?
Check the device label, the user manual, or the vendor knowledge base. Some models store credentials in secure areas of the web UI; always replace them after initial setup.
Look in the label on the device or the vendor manual, then replace the credentials after setup.
What are best practices after changing defaults?
Rotate credentials on a schedule, store them in a password manager, audit access logs, and restrict management interfaces to trusted networks. Document every change and review periodically for gaps.
Rotate passwords on a schedule, keep them in a vault, and audit access regularly.
Are there known vulnerabilities related to Zebra default passwords?
Vendor advisories exist for various models; keep firmware up to date and monitor security advisories. Apply patches promptly and re-check credentials after updates.
Keep firmware updated and monitor vendor advisories for credential-related issues.
“Default credentials are an easy foothold for attackers; secure Zebra print servers by treating defaults as urgent risks and enforcing credential hygiene across your fleet.”
Key Takeaways
- Change the zebra print server default password immediately.
- Document credential changes for audits and compliance.
- Restrict admin interfaces to trusted networks only.
- Use unique, strong passwords per device and rotate them regularly.