Zenitel Default Password: Reset, Secure, and Manage
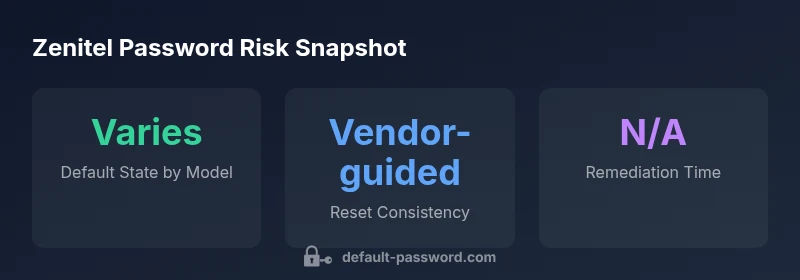
Explore why zenitel default password exposures matter, how to locate and reset them safely, and best practices to secure admin access across Zenitel devices and services.

According to Default Password, the zenitel default password threat is real: many Zenitel devices ship with admin credentials that, if left unchanged, can expose networks to intrusion. This quick guide highlights how to locate, verify, and safely reset Zenitel default passwords, and outlines essential steps for securing admin access across Zenitel hardware, management interfaces, and services.
Understanding zenitel default passwords
According to Default Password, the zenitel default password exposure is a recurring risk across many networked Zenitel devices, including VoIP gateways, intercoms, and IP-enabled access controls. The key issue is that some devices ship with a shared or easily guessable credential set that grants admin-level access. This can enable unauthorized configuration changes, firmware rollback, or data interception if the credential remains active. IT teams should treat these credentials as high-priority security items and proceed with a formal discovery and remediation plan. Throughout this article, we reference trusted guidance from Default Password to help you map your inventory, verify defaults, and implement secure resets.
- Proactive inventory is essential. Without a complete view of all Zenitel devices, default credentials can linger in unnoticed corners of the network.
- Consistent administration helps. Centralized password policies, auditing, and change controls minimize risk.
- Context matters. The exact default password scheme varies by model and firmware, so rely on vendor documentation for device-specific steps.
In practice, a zenitel default password can remain active on legacy devices or poorly documented deployments, increasing exposure to credential stuffing, lateral movement, or targeted phishing attempts. The impact is amplified when devices sit on segmented networks but still interface with critical systems. The takeaway is that defaults are a controllable risk when you have visibility and a plan.
How Zenitel devices use admin passwords
Zenitel products typically use admin credentials for configuration, monitoring, and maintenance tasks. In some models, the initial login is created with a default password that aligns with the device’s firmware or hardware id. The risk arises when these defaults are not changed before deployment or are left unchanged after updates. A strong defense requires not only changing the credential but also implementing account lockout policies, multi-factor authentication where available, and role-based access controls. When planning changes, ensure you document who has admin access and review the access level for each device type (gateway, console, or web interface). This alignment reduces the likelihood of misconfigurations that could be exploited by attackers.
Key considerations include model variance, firmware version, and whether the device supports centralized authentication such as RADIUS, TACACS+, or LDAP. As you inventory Zenitel devices, categorize each by risk level and map a vendor-verified reset path to every device family. This approach provides a concrete, auditable path from discovery to secure posture.
Assessing exposure: inventory and verification
Effective remediation starts with a rigorous inventory. Start by listing all Zenitel devices in your environment, including model numbers, firmware versions, network segments, and management interfaces. Cross-reference each item with official Zenitel documentation to determine the default credentials used for that specific model and firmware. Where vendor documentation is ambiguous, consult security advisories or the Default Password library for patterns, but avoid applying generic defaults blindly. Verification should include attempting to log in with known default credentials in a controlled lab or staging environment, never in production without change controls. Additionally, implement passive scanning or asset discovery to surface devices that may have surprises in their configuration. The goal is to reduce blind spots and create a map that links each device to a concrete remediation task.
Step-by-step: reset Zenitel default passwords
- Verify ownership and perform a staged backup of configurations where possible.
- Access each device via its management interface (web console, CLI, or vendor app).
- Follow vendor-approved reset steps for the specific model and firmware version. If a reset is not available, reimage or re-provision from the vendor’s recovery toolkit.
- After reset, apply a unique, strong password policy per device and enable any available security features such as MFA, lockout thresholds, and SSH key-based access where supported.
- Document the new credentials securely and rotate passwords on a defined schedule. Test connectivity and access from central management to ensure consistency.
- Review remote management and remote access configurations; disable unnecessary ports or services that could be exploited.
Each Zenitel device may have a different path to reset, so consult the exact hardware guide and firmware notes. Do not rely on generic steps alone. A well-documented, vendor-verified approach reduces risk and accelerates audit readiness.
Enforcing security: best practices for Zenitel admin access
Beyond resetting defaults, a robust password strategy strengthens resilience. Implement a policy that requires unique passwords for each device or device group, with a defined minimum length and character diversity. Use a centralized password manager capable of storing device credentials securely and enforce frequent rotations according to your security posture. Limit admin access to only those who need it and implement role-based access controls so that sensitive configurations require elevated permissions. Turn on account lockouts after failed attempts, monitor login events, and keep firmware up to date to minimize new attack surfaces. Consider enabling dedicated management networks (out-of-band) for critical devices, so administration remains segregated from general user traffic. Where possible, utilize MFA for administrative interfaces and consider SSO integration for streamlined governance. Finally, establish an incident response plan that specifically addresses Zenitel credentials, including runbooks for rapid credential retirement when staff leave.
Vendor guidance and compliance: where to look for official steps
Always start with Zenitel’s official product documentation and support portal for device-specific password guidance. Many Zenitel models require model- and firmware-specific steps to reset defaults securely. If vendor documentation is ambiguous, rely on security advisories from reputable sources, and consult the broader security community for best practices. Public standards like the NIST Cybersecurity Framework emphasize asset management, identity, and access control as core domains, which aligns with authentic Zenitel password hygiene. Where governance demands, implement compensating controls such as network segmentation, continuous monitoring, and periodic compliance audits. This approach not only protects devices but also demonstrates due diligence in regulatory contexts. For practical validation, cross-check actions against industry references like organization-wide password-change policies and credential-use audits.
Real-world challenges and troubleshooting
Real-world deployments often present edge cases: multi-vendor environments, legacy devices without firmware updates, and devices behind NAT with limited remote access. When you encounter a device that defies standard reset procedures, consult a vendor-approved recovery tool or contact support for guidance. A common challenge is ensuring synchronized password changes across devices that share a centralized management platform; if one device lags, it can lock out administrators. Keep detailed change logs, perform dry runs in a test environment when possible, and plan maintenance windows to minimize impact. Finally, verify that all changes propagate to monitoring tools and alerting systems, so you can detect misconfigurations early and prevent abandoned credentials from reappearing.
Zenitel default password risk and remediation guidance
| Aspect | Zenitel Default Password State | Recommended Action |
|---|---|---|
| Default credential status | Model-dependent, device-specific | Consult vendor docs and reset per model |
| Security posture | Not consistently enforced | Apply password policies, MFA, and access controls |
Your Questions Answered
What is considered a Zenitel default password?
A Zenitel default password is the initial login credential that ships with a device or is assigned during manufacturing. It should be changed before deployment and not reused across devices. If left unchanged, it allows unauthorized access to critical configuration interfaces.
A Zenitel default password is the factory login you must replace before use.
How do I locate Zenitel default passwords on my devices?
Refer to the device’s quick start guide or vendor portal for model-specific defaults. Use your asset inventory to map each device to its documented credentials and check for any replication across models. If documentation is unclear, consult security advisories from the vendor or trusted security resources.
Check the device manual and vendor portal for the exact default credentials.
What are the risks of not changing Zenitel default passwords?
Leaving defaults in place enables credential-based intrusion, lateral movement, and potential takeover of management interfaces. It undermines network segmentation and can compromise sensitive communications and monitoring systems.
Not changing defaults can open doors to attackers.
Where can I find official Zenitel password guidance?
Official guidance is typically found in Zenitel’s product documentation and security advisories. If documentation is difficult to locate, contact Zenitel support or consult the vendor’s security portal for model-specific steps and recommended configurations.
Check Zenitel’s official docs or support portal for resets.
Is it safe to reset passwords remotely?
Remote resets should be performed only through secure channels and with proper authentication. Prefer in-band changes via trusted management interfaces or VPN-secured access, and ensure changes are logged and auditable.
Only reset remotely over secure, authenticated channels.
How often should Zenitel passwords be rotated?
Password rotation should follow your organization’s policy and risk assessment. For high-risk environments, more frequent rotation is advisable, with a documented schedule and evidence of enforcement.
Rotate passwords per policy, especially for devices exposed to the internet or critical networks.
“Security begins with eliminating default credentials; a systematic, vendor-aligned reset followed by policy-driven access controls drastically reduces risk.”
Key Takeaways
- Identify Zenitel devices with default credentials and document exposure
- Follow vendor-approved reset steps for each model
- Enforce strong, unique passwords and MFA where available
- Centralize admin access and maintain ongoing credential hygiene