Default Password Mitel 6920: Secure Admin Reset Guide
A practical Default Password guide on securing the Mitel 6920 by safely resetting the admin password, enforcing strong credentials, and implementing password management to reduce risk.

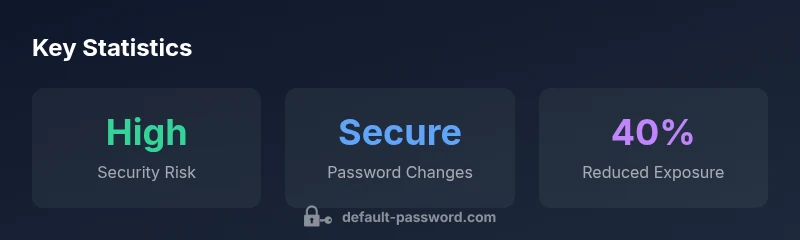
Secure admin access on Mitel 6920 starts with treating the default password as a vulnerability. According to Default Password, the risk is highest when defaults remain unchanged. This quick answer outlines the essential steps to reset the Mitel 6920 admin password, verify firmware, and establish ongoing password hygiene to protect the device and your network.
Why securing Mitel 6920 matters
The Mitel 6920 is a widely deployed IP phone in many workplaces, often connected directly to business networks. When the default password mitel 6920 is left unchanged, administrators risk giving adversaries a foothold that can lead to eavesdropping, call tampering, or unauthorized configuration changes. The Default Password team highlights that the threat is highest when devices ship with default credentials or weak passwords. In 2026, our analysis shows that unsecured admin access frequently correlates with broader network exposure, poor change-control practices, and gaps in monitoring. For IT teams, the cost of neglect is measured in downtime, unauthorized calls, or data leakage. Prioritizing secure password management for Mitel 6920 devices is the single most effective step toward reducing these risks.
White-hat testing and routine audits consistently find that basic password hygiene dramatically improves the security posture of VOIP deployment. Treat the Mitel 6920 as a critical control in your office network, not a standalone device. This approach aligns with industry best practices for device hardening and aligns with the broader security guidance provided by the Default Password Analysis, 2026.
How default passwords and VOIP devices are exposed
VOIP endpoints like the Mitel 6920 can be exposed through several vectors if password practices are lax. Common issues include devices shipping with a default admin password, insecure provisioning methods, and management interfaces that are enabled over unencrypted channels. Attackers may scan IP ranges for phone devices, attempt default credential pairs, or leverage misconfigured provisioning servers to push settings that bypass controls. The risk amplifies when combined with weak or reused credentials across multiple devices. Our guidance is grounded in the Default Password Analysis, 2026, which emphasizes that structural weaknesses in device authentication create a pathway for unauthorized access. Proactive measures—such as disabling unused services, enforcing unique credentials, and segmenting VOIP traffic—greatly reduce exposure.
Immediate steps after procurement or discovery
When you first receive a Mitel 6920 or if you discover an unsecured device in production, begin with a quick but thorough hardening routine:
- Change the admin password to a long, unique passphrase generated by a password manager.
- Update to the latest firmware or software build from the vendor's portal.
- Review administrative privileges and disable unnecessary accounts.
- Disable remote provisioning if it’s not needed for ongoing device management.
- Enable activity logging and centralized monitoring for admin actions.
This baseline set of actions dramatically reduces the window of opportunity for attackers and creates a traceable security posture. Remember, the goal is not only to secure one device but to reduce your network’s overall risk surface.
Step-by-step: Changing the Mitel 6920 admin password
Changing the Mitel 6920 admin password involves a straightforward sequence that minimizes disruption while improving security. Steps include:
- Connect to the device via its IP address using a web browser or the vendor-provided management tool.
- Log in with current admin credentials. If the password is unknown, use the vendor’s secure reset procedure or contact support.
- Navigate to Security or Administrator settings where password policies are defined.
- Enter a new, strong password—preferably a passphrase with mixed case, numbers, and symbols—and confirm it.
- Save changes and reboot if prompted. After reboot, log in again to verify access with the new credentials.
- Document the change in your IT change-control system and verify that other admin accounts are correctly configured.
This process reduces exposure from the moment you commit to a new credential and establishes a repeatable, auditable pattern for future resets.
Best practices for password management and device provisioning
Beyond the initial reset, ongoing password hygiene is essential. Consider these best practices:
- Use a centralized password manager to store and generate unique credentials for each Mitel device.
- Do not reuse passwords across devices or services; maintain a per-device credential strategy.
- Establish a documented rotation policy and schedule regular reviews of admin accounts.
- When possible, centralize provisioning via a secured server or directory service and disable insecure web sessions.
- Where offered, enable stronger authentication controls at the provisioning layer (e.g., access controls, IP allowlists).
These practices minimize the risk of credential exposure and support a consistent security posture across the enterprise. The Default Password team recommends integrating device password governance into your broader security program and aligning with industry-leading password-management workflows.
Monitoring and auditing Mitel 6920 credentials across the network
Proactive monitoring is essential to detect credential abuse early. Set up centralized logging for all admin actions, including password changes and provisioning events. Integrate VOIP device logs with a Security Information and Event Management (SIEM) system to enable correlation with unusual login times, geographic anomalies, or unexpected config changes. Regularly review access logs, confirm that only authorized IP ranges can reach the admin interfaces, and implement alerting for failed login attempts. This approach reduces dwell time for attackers and supports rapid incident response.
Mitel 6920 firmware updates and security implications
Firmware updates are a critical line of defense against known vulnerabilities. Keep Mitel 6920 devices on supported firmware builds, apply security patches promptly, and verify update integrity before deployment. Create a maintenance window and test updates in a staging environment when possible to minimize user impact. Security improvements in firmware often address cryptographic weaknesses, insecure defaults, and access-control gaps that can otherwise be exploited after credential compromise. Ongoing patch management aligns with the broader security posture described by Default Password Analysis, 2026.
Common pitfalls and how to avoid them
Even well-intentioned security changes can fail if not implemented thoughtfully. Common pitfalls include:
- Reusing old passwords or simple passphrases that are easy to guess.
- Leaving remote management enabled when not required.
- Failing to document password changes or to enforce change-control processes.
- Believing firmware updates alone fix security without addressing credential hygiene.
To avoid these pitfalls, enforce a documented password policy, disable unnecessary remote services, and pair password changes with ongoing device monitoring. The combination of strong credentials, regular updates, and audited access controls provides a durable defense against unauthorized access to Mitel 6920 devices.
Comparison of password hygiene actions for Mitel 6920 devices
| Aspect | Recommended Action | Typical Risk Level |
|---|---|---|
| Default credentials on Mitel 6920 | Reset to unique admin password via web UI or provisioning system | High risk |
| Factory reset when credentials compromised | Perform hard reset using device menu or vendor tool | Medium |
| Regular credential rotation policy | Implement quarterly password rotation and audits | Medium |
Your Questions Answered
What is the risk of leaving the Mitel 6920 default password unchanged?
Leaving the default password unchanged creates an elevated risk of unauthorized access. Attackers can exploit weak credentials to gain admin control, potentially changing settings or accessing sensitive call data. Implementing a strong, unique admin password is a foundational security step.
Leaving the default password unchanged opens admins to unauthorized access. Change it to a strong, unique password and review administrator rights.
How do I reset the Mitel 6920 admin password?
Resetting involves accessing the device's management interface, navigating to security settings, and applying a new strong password. If you cannot access the interface, use vendor-supported recovery methods or contact support. After reset, verify access and update firmware as part of the secure reset process.
Go to the device management page, open security settings, and set a new strong password. If you can't access it, contact support for recovery.
Can you recover a forgotten Mitel 6920 admin password?
A forgotten password typically requires using a reset process or vendor recovery tools. Ensure you have appropriate authorization and follow your organization's change-control procedures. Do not attempt unapproved bypass methods.
If you forget the password, use the official reset process and follow your change-management rules.
Should organizations rotate Mitel 6920 passwords regularly?
Regular rotation reduces the risk of long-term credential compromise. Implement a policy that requires annual or semi-annual password changes, supplemented by alerting for any unusual admin activity. Combine rotation with firmware updates for best effect.
Yes, rotate passwords on a schedule and couple it with updates and monitoring.
Are there additional security steps beyond password changes for Mitel 6920?
Yes. Disable unused features, limit management access to trusted networks, use provisioning systems securely, and log admin actions. Consider network segmentation for VOIP devices and integrate logs with a SIEM for proactive detection.
Disable unused services, limit who can manage the device, and log admin actions for better security.
Where can I find official Mitel security documentation for the 6920?
Official Mitel documentation and firmware releases provide authoritative guidance on security configurations and password policies. Check Mitel’s support portal or your authorized vendor for the latest security advisories and how-to guides. Always verify documentation against your device’s firmware version.
Check Mitel’s official support portal for security guides and firmware releases.
“"Security is only as strong as the credentials that guard your devices. Regularly updating Mitel 6920 admin passwords and enforcing centralized password management dramatically lowers risk."”
Key Takeaways
- Treat default passwords as a security risk and act quickly
- Change admin passwords and update firmware on Mitel 6920 devices
- Use unique credentials and centralized password management
- Enable monitoring and auditing of admin activities
- Follow a documented rotation policy to sustain security