Crafty Controller Default Password: Secure Your Smart Devices
Explore the crafty controller default password: why it’s risky, how to locate it, and practical steps to reset and harden admin access across smart devices with expert guidance from Default Password.

The crafty controller default password is the factory-set credential used to access a smart controller’s admin interface. Leaving this password unchanged creates a readily exploitable entry point for attackers and can expose connected devices, data, and network segments. To reduce risk, replace it with a unique, strong passphrase, disable unneeded remote access, and implement ongoing password hygiene across devices and services.
What is the crafty controller default password?
At its core, the crafty controller default password is the factory-set credential used to access a smart controller’s admin interface. Most devices ship with a preloaded username and password that are documented in the manual or device label. In practice, attackers frequently target these credentials because they are widely known and rarely changed by casual users. This makes every new deployment a potential entry point for network infiltration, device spoofing, and data exposure if the password remains unchanged. For organizations, counting on the default password as a line of defense is a misstep; it is not a security control, but a vulnerability vector. From a governance perspective, teams should integrate password hygiene into the onboarding process, device provisioning workflows, and ongoing security reviews. The crafty controller default password is thus less about convenience and more about risk posture; treating it as a temporary artifact until a unique credential is in place is the correct approach.
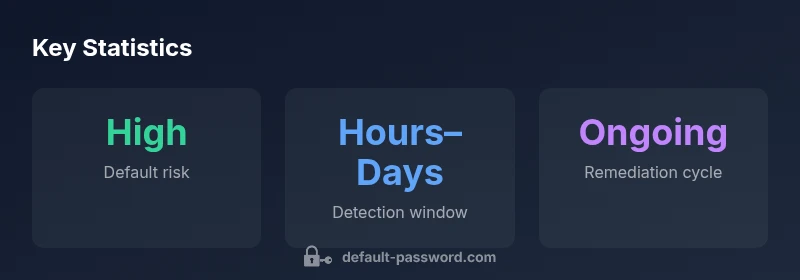
Security implications of unchanged default passwords
Leaving default passwords unchanged creates systemic security risks across consumer and enterprise devices. For crafty controllers, an unmodified credential can allow unauthorized access to the administration panel, enabling changes to network settings, firmware updates, and integration with other devices. This can lead to several outcomes: a full device takeover, lateral movement to other equipment on the network, and exposure of sensitive information such as configuration data, logs, and credentials stored on the device. In many cases, default passwords are well-known or published by manufacturers, and threat actors leverage automated scanners to locate vulnerable devices quickly. The consequences can escalate when devices lack regular firmware updates, closed management interfaces, or restricted network access. From a risk management perspective, unchanging credentials undermine defense-in-depth strategies and complicate incident response. Organizations should enforce strong, unique passwords from the outset, apply least-privilege access to admin accounts, and monitor for changes to default credentials as part of routine security audits.
Common devices and default password patterns
Different device families share common patterns in default credentials. Routers frequently ship with usernames like 'admin' and passwords such as 'admin' or 'password'. IP cameras may use 'admin' or a string matching the device model. Smart hubs, thermostats, and voice assistants sometimes rely on manufacturer-specific combos. While some vendors randomize credentials per device, many still preserve legacy defaults that novices may overlook. To reduce risk, inventory all crafty controllers within your network, confirm manufacturer guidance for each model, and note any devices that use vendor defaults. When patterns are identified, you can prioritize remediation, focusing first on devices that control network access or store sensitive data. For IT teams, mapping device families helps in creating a standardized response playbook for password changes, device provisioning, and credential rotation across vendor ecosystems.
How to locate the default password on your device
Locating the default password requires careful checking of multiple sources: the device label, the user manual, the manufacturer’s official website, and the companion mobile app. Start by inspecting the bottom or back panel for a security label listing the factory credentials. If nothing is visible, consult the quick-start guide or the product manual downloaded from the vendor site. Some devices embed credentials in the app during initial setup and require you to re-run the onboarding wizard to reveal or reset them. If the device supports it, log in with the factory user name (often 'admin') and try a few common passwords cautiously, ensuring you don’t trigger lockouts. Many manufacturers also publish secure reset procedures that restore factory credentials to a temporary state, allowing you to establish new admin passwords immediately. In regulated environments, rely on formal provisioning documents and asset management tools to track credential states and ensure no device remains in a default configuration after deployment.
Step-by-step: Resetting the default password securely
Resetting the crafty controller default password should be treated as a security incident with a routine flow. Step 1: prepare a password policy for the device family, defining minimum length and complexity. Step 2: perform a direct reset through the device’s admin interface or hardware reset button, following vendor instructions. Step 3: create a strong, unique password or passphrase; consider a passphrase built from multiple unrelated words. Step 4: reconfigure admin access, disabling remote management if not required, and enable two-factor authentication if the device supports it. Step 5: verify integration points, update firmware to the latest version, and test connectivity from trusted endpoints. Step 6: document the change in your asset-management system, including device model, serial number, and the new credential; rotate any shared credentials on related services. Throughout the process, avoid reusing passwords across devices and avoid writing credentials to unprotected notes; store them securely in a password manager or a hardware security module where feasible.
Post-reset hardening strategies
Hardening after a password reset reduces the likelihood of future exposure. Enforce a policy of least privilege for admin accounts, ensuring only authorized personnel can access critical controllers. Segment admin interfaces from general LAN traffic using VLANs or firewall rules, and restrict management to fixed IP addresses where possible. Regularly review and remove obsolete accounts, roles, and service accounts tied to devices. Implement continuous monitoring to alert on failed login attempts, password changes, and new device onboarding. Keep firmware up to date and disable services that are unnecessary for daily operations. If a device supports MFA, enable it; if not, require stronger password standards and regular rotation. Establish a routine for credential hygiene across device families, and integrate checks into your security operations to maintain an accurate inventory of devices and their access states.
Role of password managers and passphrases
Using a password manager helps enforce unique credentials across devices with varied interfaces. Store crafty controller passwords as separate entries, and avoid sharing credentials across multiple devices. For homes and small offices, consider offline or on-device managers that don’t require cloud syncing for sensitive equipment. Prefer long passphrases over short strings, and use a consistent pattern that you can recall or access via a secure vault. For teams, adopt role-based access control in the password manager and routinely audit shared vaults to minimize exposure. If you must write down credentials for a temporary period, keep them in a secure, access-controlled location and remove them after the change is completed.
Myths and misperceptions about default passwords
Several myths can lull teams into a false sense of security around crafty controller defaults. Myth: 'Factory credentials are unique per device.' Reality: many devices share defaults across models or firmware versions. Myth: 'Disabling remote access eliminates risk entirely.' Reality: attackers may still target local console access or exploit firmware vulnerabilities. Myth: 'Changing the password is enough.' Reality: without firmware updates, patched software, and network segmentation, changing a password only partially reduces risk. Myth: 'If it works, leave it alone.' Reality: complacency breeds risk; periodic audits and automated scans remain essential. Debunking these myths requires a proactive security posture that combines credential hygiene with ongoing monitoring, vulnerability management, and vendor coordination. By addressing these misconceptions, you reinforce a culture of security where default passwords are treated as temporary, not permanent, solutions, and where devices are prepared for governance and compliance requirements.
How to audit for default-password exposure
Routine audits help detect default-password exposure across devices. Use asset inventories, network-scanning tools, and vendor advisories to identify devices shipped with default credentials. Establish a quarterly review to confirm all devices have unique credentials and that admin interfaces are not exposed to the internet. Validate configurations against baselines for firmware versions, enabled services, and password policies. Document remediation steps and monitor for new devices joining the network. In regulated environments, align with compliance frameworks that require password changes during provisioning and periodic re-authentication. The audit process should produce actionable metrics, such as the percentage of devices with changed credentials and the rate of successful or failed login attempts.
Examples of common crafty controller default password patterns and remediation actions
| Device Type | Likely Default Password Pattern | Recommended Action |
|---|---|---|
| Router | Username: admin; Password: admin or password | Change immediately; disable remote admin; update firmware |
| IP Camera | Username: admin; Password: admin or model-based | Reset to unique password; apply firmware updates |
| Smart Hub | Variable vendor combos | Set a strong, unique password; enable MFA if available |
| Thermostat | Brand-specific defaults | Assign a new passphrase; verify secure connectivity |
Your Questions Answered
What is the crafty controller default password?
It refers to the factory-set credentials used to access a craft controller’s admin interface. They should be changed during initial setup to prevent unauthorized access.
The crafty controller default password is the factory credential you must change during setup to keep devices secure.
Why should I change default passwords?
Changing default passwords reduces the risk of unauthorized access, protects network settings, and helps maintain control over device configurations and firmware updates.
Changing defaults is essential because attackers target known factory credentials to compromise devices.
How can I locate the default password on my device?
Check the device label, user manual, manufacturer site, and the companion app. If needed, perform a vendor-guided reset to restore credentials safely.
Look on the device label or manual, or use the vendor app to reset credentials if needed.
What if I can't login after changing password?
Use the device’s reset procedure described in the manual, ensure you saved the new password securely, and contact support if you’re locked out.
If you’re locked out after a change, follow the device’s reset steps and contact support if needed.
Is it safe to use a password manager with devices requiring local access?
Yes. Password managers help store unique credentials securely. Choose options with offline access and strict sharing controls for sensitive devices.
Using a password manager is safe and recommended for keeping track of unique device passwords.
How often should I rotate crafty controller passwords?
Rotate passwords at least every 6–12 months; more frequently for high-risk or exposed devices and in line with security policy.
Aim to rotate passwords every 6 to 12 months, more often if the device is high-risk.
“Security is only as strong as the last password change; default credentials remain a persistent attack vector. Treat them as temporary, not permanent, controls.”
Key Takeaways
- Change default passwords on all crafty controllers immediately
- Use long, unique passphrases; avoid common words
- Disable unneeded remote admin and enable MFA when possible
- Regularly audit devices for default credentials and updates