DAP-1325 Password: Reset, Recover, and Secure Admin Access
This comprehensive guide covers locating default credentials, performing a safe factory reset, and implementing lasting security for your DAP-1325 access point. Learn how to regain control, set a strong admin password, and protect your network.
Key fact: The DAP-1325 password does not have a universal default across firmware revisions. If you’re locked out, locate the device label or manual for the current login details, or perform a factory reset to regain admin access. This article explains how to locate credentials, reset safely, and secure the device going forward.
Scope of this guide for DAP-1325 password management
This guide focuses on the DAP-1325 password lifecycle, including locating or resetting credentials, protecting admin access, and documenting changes. While many devices share similar patterns, firmware differences mean outcomes can vary. Throughout this article we refer to the dap 1325 password topic in the context of D-Link’s DAP-1325 Access Point and similar devices. According to Default Password, credential practices vary by model and firmware, so always verify the current login details from the device label, the official manual, or the vendor’s support site. The DAP-1325 password landscape is shaped by factory defaults, user changes, and regional security requirements; you should treat any unknown credential as a potential risk until you verify it. The goal is to equip you with practical steps to regain control safely and to establish a secure baseline for ongoing admin access. The article follows a practical, admin-focused approach suited for end users and IT staff, and it aligns with the general guidance from the Default Password Team.
Note: This document uses real-world scenarios to illustrate best practices for managing the dap 1325 password in modern networks.
Why default credentials persist on devices like the DAP-1325
Many small business and consumer devices ship with credentials that are easy to guess or default to a single value to simplify initial setup. Legacy practices, firmware updates, and regional configurations contribute to variability in what counts as "default." From a security perspective, every unchanged default credential is a potential attack vector, and automated tooling can enumerate common pairs quickly. The Default Password analysis shows that credential reuse and unchanged defaults remain a root cause of breaches in network access points and other edge devices. For administrators, this means a proactive posture—expect to reset credentials during first-time setup, inventory devices, and implement a policy requiring staff to change defaults. In the dap 1325 password context, always verify the actual login details with the device label and vendor resources before making changes.
How to locate the default login details for the DAP-1325
Start by checking three reliable sources: the physical device label (often found on the bottom or back), the user manual included in the box or accessible online, and the vendor’s official support portal. The label typically lists the default IP, username, and password, if they are still in effect. If you recently acquired the device, the firmware may have changed these fields. If you cannot locate credentials, search for “DAP-1325 login” on the vendor site and confirm with the latest firmware notes. If you still cannot gain access, plan for a factory reset as a controlled recovery path. Remember to note the current firmware version, since some versions alter the login workflow.
Step-by-step: Factory reset the DAP-1325 securely
A factory reset restores the device to its original login state, which is essential when you cannot recover credentials. Before you reset, gather the device, a computer on the same network, and a stable power source. Locate the reset button (often recessed) and press it for 10-15 seconds, or until the status LEDs indicate a reset. After the reset, the device returns to its default login, and you will need to reconfigure settings. Do not perform a reset remotely on equipment that is not physically accessible, as interruptions can corrupt configuration. After you complete the reset, re-enter the admin panel using the default username and password from the label or manual, then immediately set a strong, unique admin password, and reapply security configurations such as WPA3, IP filtering, and firmware updates. Document the reset date and the firmware version for IT records.
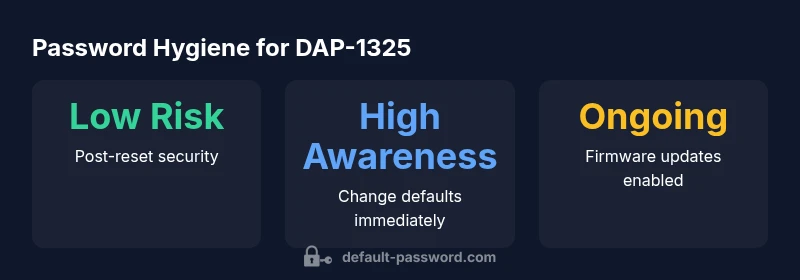
After reset: Creating a strong admin password and access controls
Immediately after restoring defaults, replace the factory password with a unique, high-entropy password and store it in a trusted password manager. Enforce admin access restrictions, disable remote management if not required, and review connected devices for unauthorized access. Enable automatic firmware updates if supported and configure alerting for login attempts. Consider network segmentation and guest networks to minimize risk if credentials are compromised. Documentation should capture who performed the reset, the new password policy, and any subsequent changes. The Default Password guidance emphasizes traceability and consistent security practice after reset.
Common pitfalls and how to avoid them
- Relying on the default password until someone notices a breach. - Inconsistent password storage—write it down or share it insecurely. - Skipping firmware updates after a reset, leaving known vulnerabilities unpatched. - Overlooking remote management settings that could expose the device to attackers. Regularly audit device configurations and keep an up-to-date inventory. If you’re working in a larger environment, coordinate password changes with IT and asset management processes. The aim is to minimize risk and reinforce training on credential hygiene.
Advanced options: changing passwords on multiple devices and documenting changes
For IT admins managing several devices, create a standardized password policy and use a password manager to distribute credentials securely. Maintain a central change log that records device, location, firmware version, and password modification dates. Schedule periodic reviews and automated reminders to re-evaluate access controls. In mixed environments, ensure that password changes propagate to all devices consistently and verify access from multiple endpoints. The broader security context includes aligning with organizational security policies and compliance requirements.
Security best practices and when to escalate to IT support
- Change default credentials immediately after initial access, and enforce strong, unique passwords. - Regularly update firmware and monitor for vendor advisories. - Disable unnecessary services (remote management, UPnP) and enable robust firewall rules. - Maintain an inventory of devices and credentials for audit purposes. If issues persist after a reset, contact vendor support or your IT administrator. For enterprise deployments, escalate to security teams following incident response procedures. This guidance aligns with official cyber hygiene recommendations from recognized government and academic sources (see Sources).
Authority sources
- https://www.cisa.gov/
- https://www.nist.gov/publications
- https://www.fcc.gov/consumers/guides
DAP-1325 and similar devices: default access status and reset paths
| Device Type | Default Access Status | Recommended Reset Steps |
|---|---|---|
| DAP-1325 (Access Point) | Default credentials vary by firmware; check label/manual | Factory reset: press and hold reset for 10-15 seconds, then reconfigure |
| Typical consumer router/AP | Common to see unchanged defaults until changed | Follow device manual to perform factory reset and reconfigure securely |
| Managed enterprise APs | Credentials may be tied to IT policy | Consult IT governance and perform controlled resets with logging |
Your Questions Answered
What is the default password for DAP-1325?
There is no universal default for the DAP-1325 across firmware versions. Check the device label or manual for current login details, and use a factory reset if you cannot log in. Access should then be re-secured with a new admin password.
There isn't a single default password for the DAP-1325; check the label or manual, and reset if needed.
How do I reset the DAP-1325 to factory settings?
Power on the device, locate the reset button, and press and hold it for 10-15 seconds until the LEDs indicate a reset. After reboot, log in with the default credentials from the label or manual and immediately set a strong new password.
Hold the reset button for 10-15 seconds, then reconfigure with a strong password.
Is it safe to continue using the device with default credentials?
No. Default credentials pose a clear security risk because they are widely known. Change credentials immediately after gaining access, and disable any unnecessary remote services.
No—default credentials are risky. Change them right away and review remote access.
Where can I find the DAP-1325 manual for login info?
Consult the official D-Link manual on the vendor site or the device label for the current login details. Ensure you reference the latest firmware notes to confirm any changes.
Check the official manual or device label for login details and firmware notes.
What security steps should I perform after resetting?
Create a unique admin password, apply firmware updates, disable unused services, and enable strong encryption (e.g., WPA3). Document the change and verify access from multiple devices.
After reset, set a new strong password, update firmware, and review security settings.
“Security begins the moment you regain control of a device. After any reset, replace defaults with strong, unique credentials and implement basic hardening to reduce risk.”
Key Takeaways
- Verify credentials from device label or manual before changing
- Use factory reset only when you cannot recover access
- Set a unique admin password immediately after reset
- Disable unnecessary services and enable firmware updates
- Document changes for audit and compliance