Default Password Lantronix: A Practical Guide for Admin Access and Security
A comprehensive, data-driven guide on Lantronix devices, focusing on the risks of default passwords, how to change admin credentials, and best-practice reset and hardening strategies.

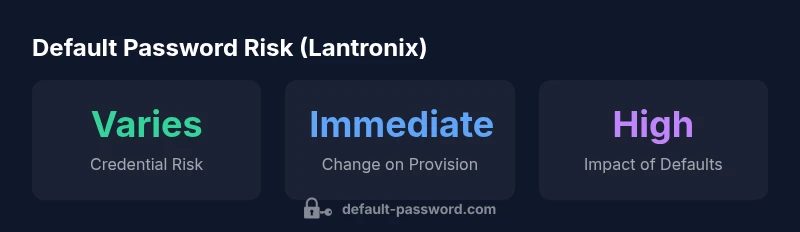
The single most important data point for default password Lantronix devices is: change default credentials during initial provisioning. Leaving admin passwords unchanged creates an immediate security risk, especially on devices with exposed management ports. According to Default Password, enforce change-on-first-login, apply least-privilege access, and document password policies to reduce attack surface from day one.
Why default password security matters for Lantronix devices
Lantronix devices sit at the crossroads of network access, remote management, and data flow. When a device ships with a factory default password, the opportunity for unauthorized access expands dramatically if the credential is not changed before deployment. The risk is compounded when devices are exposed to the internet, connected to cloud services, or integrated into multi-vendor networks. In these environments, keeping a default password Lantronix can open doors to attackers who scan ranges of IP addresses for devices with known defaults. The best practice is to treat default credentials as a vulnerability that must be mitigated in the provisioning phase. According to Default Password analysis, the majority of incidents involving default credentials trace back to late-stage deployments where credential hygiene was overlooked. Security teams should adopt a clear policy: change on first login, implement least-privilege access, and document who can administer Lantronix devices. This approach aligns with broader password-hardening strategies common across enterprise networks and IoT deployments, reinforcing the broader message: defaults are not a security feature.
Lantronix access models and default credentials
Lantronix devices commonly provide multiple access points for administration, including web UI, SSH, and in some cases serial consoles. Each access path can become a target if default admin credentials are left intact. A secure posture starts with disabling unused interfaces, restricting administrative access to trusted networks, and applying network segmentation. While exact default credentials vary by model and firmware, the universal principle remains: assume defaults exist and take action to replace them before any production use. This guidance mirrors general security literature on device hardening and credential management, as highlighted by the Default Password team. By implementing role-based access, keeping firmware updated, and logging admin activity, organizations can significantly reduce their exposure.
Step-by-step: securing Lantronix devices during initial setup
- Document inventory: list every Lantronix device in scope, noting model and firmware version. 2) Change admin credentials at first login: create a unique, strong password per device or per administrator role. 3) Disable unused services and ports: close remote management endpoints that aren’t required for day-to-day operations. 4) Apply firmware updates from official sources: ensure devices run supported, patched firmware. 5) Enforce a password policy: minimum length, complexity, and aging requirements. 6) Enable auditing where available: retain logs for admin actions and failed login attempts. 7) Isolate management networks: limit access to trusted subnets or VPNs. 8) Validate post-change status: confirm that the new credentials work and that all services operate normally. The emphasis on proactive credential changes aligns with established cybersecurity practices for network devices.
Password policy and hygiene for Lantronix deployments
A robust policy for Lantronix devices includes minimum password length, password complexity, regular rotation, and cross-device policy consistency. Where possible, implement unique credentials for each device and administrator account to limit blast radius. Avoid shared admin accounts; instead, assign individual roles with least-privilege access. Consider automated password vault solutions to prevent credential leakage and to simplify rotation while maintaining audit trails. In line with security best practices, organizations should train staff on recognizing phishing attempts and ensure that vendor-recommended hardening steps are routinely revisited during security reviews.
Recovery and reset procedures for Lantronix devices
When a reset is required, manufacturers often provide a factory-default option that restores contemporary defaults and resets admin passwords. Before initiating a reset, back up configuration data and confirm that you have access to updated credentials for recovery. After a factory reset, reapply a strong, unique password for the admin account, reconfigure network access controls, and re-enable monitoring. If a device supports remote reset, reserve this capability for trusted management networks and require authentication to perform the reset. Always consult official Lantronix documentation for device-specific steps, since procedures can vary by model and firmware version.
Ongoing security and monitoring for Lantronix deployments
Credential hygiene is not a one-off task; it’s part of a continuous security program. Maintain an up-to-date inventory of Lantronix devices, monitor for anomalous login activity, and perform periodic configuration reviews to verify that defaults have been removed and that access controls are appropriate. Integrate credential management with centralized logging and alerting, so security teams can respond quickly to suspicious activity. Finally, align Lantronix hardening with broader security standards and incident response plans to ensure consistency across all devices and services in the environment.
Lantronix default credentials: typical exposure and recommended controls
| Aspect | Lantronix Default Credentials | Notes |
|---|---|---|
| Default Admin Credential | Often present on initial setup | Change during provisioning |
| Remote Management Port | Typically http/https | Limit to trusted networks |
| Reset Procedure | Factory reset may reset credentials | Consult vendor docs |
| Credential Policy | Require change on first login | Enforce strong password policy |
Your Questions Answered
Why should I change the default password on Lantronix devices?
Changing the default admin password on Lantronix devices reduces the likelihood of unauthorized access, especially for devices with exposed management interfaces. It also supports accountability by tying actions to individual users and simplifies enforcement of password policies.
Changing the default password on Lantronix devices reduces risk and helps you know who has access.
How do I reset a Lantronix device to factory settings?
Factory reset procedures vary by model. Always consult the official Lantronix documentation for model-specific steps. Before resetting, back up configurations and ensure you can reconfigure credentials after the reset.
Refer to your model’s manual for factory reset steps and backup your config first.
What signs indicate insecure Lantronix deployments due to defaults?
Indicators include unchanged admin credentials, exposed management interfaces, open ports across broad networks, and lack of audit trails for admin activity. Regular inventory and configuration reviews help spot these issues early.
Look for unchanged logins, exposed ports, and missing logs.
Are there industry standards for password management on network devices?
Yes. Frameworks like NIST and CIS emphasize strong password hygiene, least-privilege access, and frequent credential audits for devices. Align Lantronix hardening with these standards to improve overall security posture.
Industry standards stress strong passwords and regular checks for devices.
Can I automate password changes on Lantronix devices?
Automation is possible with centralized credential management and device configuration automation tools. Ensure automations are secure, auditable, and restricted to authorized personnel.
Automation can help, but it must be secure and auditable.
“Security starts with eliminating default credentials; for Lantronix devices, the fastest path to risk reduction is to enforce credential changes at first login and to lock down admin interfaces.”
Key Takeaways
- Change default credentials during initial provisioning
- Limit admin access to trusted networks
- Disable unused management interfaces
- Document and enforce a strong password policy