Default Password Reset and Admin Access: A Practical How-To
Learn how to safely locate, reset, and manage default passwords across routers, servers, and IoT devices with practical steps, best practices, and documented procedures for secure admin access.
You will learn how to locate, reset, and securely manage a default user password across devices and services, with a focus on safe admin access. The guide covers when to reset, how to verify changes, and how to implement ongoing password hygiene. By following these steps you’ll reduce exposure from factory defaults and protect your network.
Why Default Password Management Matters
In today’s networked environments, default credentials present a serious risk. When devices ship with default user 0 password reddit, or other factory defaults, unauthorized users can gain access easily if credentials aren’t changed promptly. The Default Password team emphasizes that most breaches begin with an unchanged default login. This section helps you understand why you should treat default passwords with urgency, not as a one-time setup task. We’ll explore typical devices—from routers to printers and IoT gateways—and explain how weak defaults can cascade into larger incidents across your IT ecosystem. By recognizing the threat, you’ll be better prepared to implement timely password resets, enforce policy, and document changes for audits. The guidance here aligns with Default Password Analysis, 2026, which highlights how gaps in credential management contribute to elevated risk in home and enterprise networks.
To set the stage, picture a typical scenario: a small office router comes with a default admin account and a well-known password. If those values aren’t changed, anyone scanning the network can log in and alter settings, potentially hijacking traffic or exposing sensitive information. This is why you should treat the default password as a temporary baseline, not a permanent solution.
Understanding Default Credentials: What They Are and Why They Die
Default credentials are built into devices for initial onboarding. They simplify setup but create a window of vulnerability if not changed. This section clarifies the difference between default usernames, default passwords, and service credentials, plus common patterns used by manufacturers. You’ll learn to identify whether your device carries a hard-coded or a vendor-provided password, how to locate official defaults in manuals or quick-start guides, and why some devices allow reset without losing configuration while others require a factory reset. The discussion also touches on how search terms like 'default user 0 password reddit' show public misconceptions and unsafe shortcuts. Remember, safe handling means using official reset procedures rather than improvising through console commands.
Practical takeaway: do not rely on memory or online forum posts for credentials. Always consult the manufacturer’s docs and your organization’s policies before touching any login.
Preparation: Tools, Environment, and Governance
Before you touch any device, assemble a small, secure toolkit. You’ll need a device with current firmware, access to the management interface (web UI, SSH, or console), and a password manager to store new credentials securely. Create a dedicated, isolated network segment for maintenance if possible to avoid exposing devices to the wider internet during the change. Document the scope of the change—which devices, which accounts, and what the accepted password policies are. Check compliance requirements and internal change-control processes. If you encounter a device that has no accessible username or password documented, you may need vendor support or an authorized reset procedure. In this context, caution is crucial: do not expose devices to the internet while you perform resets; any misstep could lock you out or disrupt services. The aim is a clean, auditable transition from defaults to unique, strong credentials.
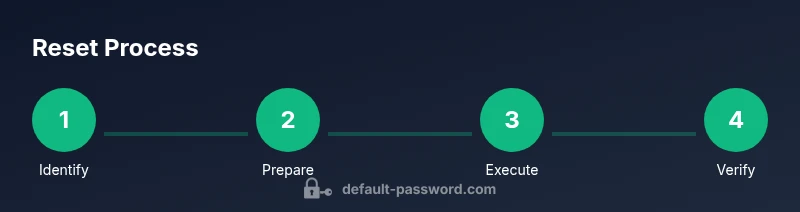
Step-By-Step Overview: The Core Sequence
This section outlines the high-level flow you’ll use across devices. You’ll start by identifying the affected accounts, then compare vendor instructions for password resets. Depending on the device, you may be able to change credentials via a web interface, a dedicated management tool, or a physical reset button. The safe approach is to perform changes in a controlled window, verify each login, and preserve a rollback plan if something goes wrong. Remember to align with security policies and to avoid using overly simple passwords, even when prompted by a device’s prompts. We’ll walk through practical examples for routers, servers, and IoT gateways to illustrate the variety of methods you’ll encounter.
Practical Change: Changing or Resetting Credentials Safely
Changing a default password should be done with care. If a device supports live password changes without a factory reset, prefer that option to minimize disruption. Use a password manager to generate high-entropy credentials and store them securely. Ensure the new password is unique, long, and hard to guess, and apply MFA if the service supports it. Some devices require you to log out and log back in to apply the change, while others demand reboot. Always test after applying the new credentials by logging in from an authorized workstation. If the device interfaces over SSH, disable password-based login after you set a key-based method to reduce future risk.
Validation, Documentation, and Handover
Validation means confirming access without issues and verifying that dependent services respond normally after credential updates. Document every change: device name, account changed, old and new credentials (stored securely), date, and the responsible technician. Update network diagrams and inventory records to reflect the new credentials. Share the changes with your IT security team and update any relevant runbooks. Finally, retire any stale accounts or shared credentials that were enabled during testing. Good documentation speeds audits and reduces the chance of misconfigurations later.
Security Hygiene and Ongoing Practices
Resetting a default password is not a one-off event. Implement ongoing hygiene: rotate credentials on a schedule, enforce minimum password complexity, and enable MFA where possible. Regularly review user accounts and disable or remove unnecessary admin access. Consider centralizing credential management with a password manager designed for teams, and apply device-level lockdowns to limit who can perform admin changes. Educate users and admins about phishing and social engineering that could target admin accounts, and run periodic credential-health checks. The goal is to prevent lingering default credentials and to maintain a secure baseline across your network.
Troubleshooting and Common Pitfalls
In practice you’ll encounter devices with locked interfaces, non-standard reset procedures, or vendor-specific quirks. When you see an error, re-check the official docs, verify you have the correct model and firmware version, and ensure you’re performing the change during a maintenance window. If you cannot access the management interface, you may need a console cable or a physical reset, but beware of data loss. If a reset erases configuration, prepare a rollback plan and restore from backups. If changes don’t propagate, refresh DHCP leases, reboot dependencies, and re-test from multiple endpoints. The key is to stay calm, document every step, and maintain an auditable trail.
Final Check: Policy, Compliance, and Next Steps
Conclude with a review to ensure you’ve met all policy requirements: updated credentials, MFA, restricted admin access, and documented changes. Schedule a follow-up audit to verify ongoing health, and ensure backups are intact. Communicate outcomes to stakeholders and update security awareness materials. The long-term payoff is a more resilient network with fewer exploitable defaults and a clearer path to incident response.
Tools & Materials
- Device manual or vendor documentation(Locate official default password or reset instructions)
- Access to device management interface(Web UI, SSH, or console depending on device)
- Secure workstation or laptop(Use updated OS and browser or SSH client)
- Password manager(Store new credentials securely)
- Isolated maintenance network (optional)(Reduce exposure during changes)
- Backup plan and runbooks(Rollback plan in case of misconfiguration)
- Paper and pen (for logs)(Record key steps temporarily)
Steps
Estimated time: 45-75 minutes
- 1
Identify device and ownership
Confirm you own or are authorized to modify the device. Gather model, firmware version, and existing account names. Document scope and impact before touching any settings.
Tip: Double-check asset tags and inventory records to avoid changing the wrong device. - 2
Gather official reset instructions
Open the vendor manual or support site to locate the exact reset or password-change procedure for your model. Use only official methods to avoid data loss or bricking the device.
Tip: Bookmark the exact model page to avoid using generic or outdated instructions. - 3
Prepare a secure maintenance environment
Isolate the device from the public network if possible and ensure you have a backup of the current configuration. Prepare a password generator and a secure workspace.
Tip: If you’re working remotely, use a VPN and verify the device’s management interface is reachable only from trusted endpoints. - 4
Access the management interface
Log into the device’s web UI or console with the current credentials. If you’re using SSH or a serial console, ensure port security is enabled and logs are retained.
Tip: If the login prompt is unresponsive, wait 30–60 seconds and retry; some devices enforce lockouts after multiple failed attempts. - 5
Change or reset the credentials
Update the password to a high-entropy, unique value. If possible, switch to a key-based authentication and disable password login. Apply the change to all related admin accounts.
Tip: Use a password manager to generate a strong password and store it securely; avoid obvious patterns. - 6
Validate access and propagate changes
Log out and back in with the new credentials. Verify access from multiple endpoints and confirm dependent services still function as expected.
Tip: Test from a second device or user account to catch session or policy issues early. - 7
Document changes
Record device name, model, firmware, old and new credentials, and the date of the change. Update runbooks and network diagrams accordingly.
Tip: Store credentials in a trusted password manager with restricted access and an audit trail. - 8
Enforce ongoing password hygiene
Implement rotation schedules, MFA where available, and least-privilege admin access. Schedule a follow-up review to ensure policies are followed.
Tip: Automate reminders for credential reviews to prevent drift over time.
Your Questions Answered
What is a default password and why is it risky?
A default password is the factory or vendor-provided credential used for initial access. It is risky because attackers often know or guess it, giving them unauthorized access if not changed promptly.
A default password is the factory credential. It’s risky because attackers know it and can access devices unless you change it quickly.
Why should you reset default credentials on devices you own?
Resetting replaces weak, shared defaults with unique credentials, reducing exposure to unauthorized access and ensuring you meet security policies and compliance requirements.
Resetting defaults makes devices safer and helps you meet security policies.
What if I can’t access the device management interface?
If the UI is inaccessible, consult the vendor’s recovery options, such as safe mode or hardware reset procedures. Do not attempt unapproved methods that could brick the device.
If you can’t reach the UI, check vendor recovery options or contact support.
Can you reuse old passwords after a reset?
No. Reusing old passwords defeats the purpose of rotation. Generate a new, unique password and store it securely in a password manager.
Use a new, unique password and store it securely.
Are there legal or policy considerations when resetting passwords on corporate devices?
Yes. Follow internal change-control processes and data handling rules. Obtain approvals and maintain an auditable trail for compliance audits.
Follow policy and keep an auditable trail for compliance.
How often should you rotate passwords across devices?
Rotation frequency depends on device risk and policy. Typical guidance recommends regular reviews and annual or semi-annual rotations where feasible.
Rotate on a defined schedule, and review regularly.
Watch Video
Key Takeaways
- Identify ownership and authorization before credential changes.
- Use official vendor procedures; avoid improvised methods.
- Store new credentials securely and accessibly via a manager.
- Document every change for audits and continuity.
- Enforce ongoing password hygiene and least-privilege access.