Network Video Client Default Passwords: Reset & Secure
Learn to identify, reset, and secure default passwords on network video clients. This step-by-step guide covers risks, best practices, audit methods, and ongoing password hygiene for IP cameras, NVRs, and video servers.

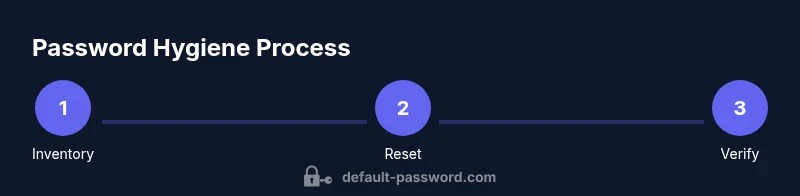
Goal: Audit and secure network video clients by removing default passwords. You will identify every device, verify current credentials, and reset them to unique, strong passwords. Then implement access controls, firmware updates, and a documented password policy. The quick path also covers testing connectivity after resets, documenting changes, and establishing ongoing rotation and monitoring to prevent future exposures.
Why Network Video Clients Need Password Hygiene
Network video clients include IP cameras, network video recorders (NVRs), video servers, and encoder gateways that sit at the heart of surveillance and monitoring systems. They often manage sensitive streams, storage, and alerting workflows. A hidden but critical truth is that a network video client default password is a frequent attack vector. The Default Password team has observed that many deployments rely on the credentials that ships with devices, or use easy-to-guess combinations such as admin/admin or admin/password. When these defaults persist, every compromised device expands the attack surface, enabling unauthorized access to live feeds, stored video, and configuration settings. Password hygiene—changing defaults, enforcing strong passwords, and applying consistent rotation policies—reduces exposure and speeds up future hardening. In practice, you should treat every device as potentially vulnerable until you verify credentials, apply unique passwords, and document changes. This section sets the stage for a practical, risk-based approach that respects operational needs while strengthening security across your video network.
Common Default Password Scenarios in Video Devices
Video devices vary by vendor, but several default password patterns recur. Many IP cameras and NVRs ship with admin credentials that are well known, or with predictable strings tied to the device model. Common examples include admin/admin, admin/password, or blank passwords left in place after initial setup. Some devices require a password reset at first login, while others allow unchanged defaults to persist for years. The risk scenario is amplified when multiple devices share a single credential or when default passwords are used to enable remote administration. In addition to the obvious admin accounts, some devices embed default service accounts with limited visibility but broad access. The goal in this section is to help you quickly identify where defaults are likely to exist by inventorying devices, checking firmware notes, and validating whether a device still uses its factory credentials. A structured discovery, using a device list with model numbers, IP addresses, and current credentials, is essential for an accurate security baseline.
Risks of Leaving Default Passwords Active
Leaving default passwords in place introduces several concrete threats. Attackers can perform credential stuffing against exposed interfaces, gain administrator access to cameras or NVRs, and tamper with feeds or alerts. If a device is reachable from the internet, the risk multiplies because automated probes routinely probe for common defaults. Other risks include stale firmware that lacks security updates, misconfigured permissions that elevate access, and poor logging that hides unauthorized changes. A single compromised device can be a foothold for lateral movement, potentially exposing an entire network segment. By prioritizing remediation, you reduce risk, support compliance requirements, and improve the reliability of monitoring and incident response.
How to Audit Your Video Network for Default Passwords
Auditing starts with a complete inventory. Gather device model, firmware version, IP address, and current user accounts. For each device, verify whether the default password is still active and check if there are any accounts with elevated privileges that lack MFA or advanced controls. Use vendor manuals, security advisories, and your own device baseline to map a secure state. Perform a controlled password reset where feasible, keeping a log of changes. Where possible, isolate devices during reset to avoid confusing outages, and verify that services resume normally after credentials are updated. The audit should culminate in a documented baseline that identifies gaps, assigns owners, and sets a realistic remediation timeline.
Step-by-Step: Reset to a Secure State (Narrative)
Begin with a device-by-device assessment: confirm device type, model, and current login status. For each device, perform a secure, device-appropriate reset—prefer a factory reset only when the configuration is not recoverable or when inventory indicates a mass update is required. After the reset, immediately apply a strong, unique password, and reconfigure essential services with least-privilege access. Update firmware if available, disable unused features, and restrict administrative access to trusted networks or management hosts. Finally, document the new credentials in a secured vault and verify connectivity and proper video streams. This approach minimizes downtime while restoring secure access.
Choosing and Implementing Strong Passwords
Strong passwords for video devices should be unique, lengthy, and unpredictable. A practical rule is a minimum of 12–16 characters combining upper and lower case letters, numbers, and symbols. Prefer passphrases that are easy to remember for the human operator but difficult for machines to guess. Do not reuse passwords across devices. Use a password manager to generate and store credentials securely; this reduces the chance of reuse and simplifies rotation. For devices that support MFA or hardware tokens, enable them where feasible to add an additional security layer. Finally, adopt a standard naming convention for accounts and document the purpose of each credential. A consistent approach reduces errors during audits and simplifies incident response.
Access Control, Roles, and Network Segmentation
Security grows as you reduce exposure. Implement role-based access control so only authorized personnel can reach device configuration pages. Restrict management interfaces to trusted networks or VPNs, and place video devices behind network segmentation such as VLANs. Disable unused services (like UPnP, Telnet, or SSH when not needed) and enforce firewall rules at the device or network perimeter. Regularly review users, roles, and permissions, and enforce policy-driven password changes aligned with your organization’s security calendar. These measures limit attacker reach and improve visibility for security teams.
Documentation, Monitoring, and Follow-Up
Remediation is not a one-off task; it requires ongoing discipline. Maintain an updated asset inventory, including device owner, location, firmware level, and password status. Establish a quarterly review to detect drift, verify password rotations, and reconcile any exceptions. Enable logging and alerting for admin logins, failed attempts, and configuration changes. Store credentials in a secure password vault with restricted access and auditing. Finally, train staff and operators on recognizing phishing attempts and safe password practices, so the entire team contributes to a stronger security posture.
Troubleshooting Common Issues After Reset
After a reset, some devices may not boot with the new credentials, or services may fail to start due to misconfigurations. If you cannot log in, consult the vendor recovery procedures or perform a controlled factory reset only if you have current backups of configurations. Verify network connectivity, time synchronization, and DNS settings since these can block management access. If streams do not appear after credentials are updated, check RTSP/HTTP endpoints, firewall rules, and user permissions. Finally, re-check firmware compatibility and reapply settings as needed. The goal is to restore service quickly while preserving security.
Get Ready for the Next Cycle
Plan to revisit password hygiene on a regular cadence. Schedule quarterly audits, annual policy reviews, and periodic training for admins. Integrate password hygiene into change management workflows and incident response playbooks. By treating default password remediation as an ongoing process, you reduce the probability of a future breach and keep surveillance operations reliable.
Tools & Materials
- Device admin credentials(Have admin access to all devices in scope)
- Inventory sheet or asset database(Record device model, IP, firmware, and current credentials)
- Network access to devices(Access via LAN/Wi‑Fi, VPN if remote)
- Secure password storage(Use a password manager or vault (with admin access controls))
- Firmware update utility or vendor portal(Optional but recommended for secure devices)
- Documentation template(Record new credentials and rotation schedule)
Steps
Estimated time: 60-120 minutes
- 1
Inventory all devices
Create a comprehensive list of cameras, NVRs, and encoders with model numbers, IP addresses, and current credentials. This establishes the scope for remediation and avoids missing devices during resets.
Tip: Cross-check against vendor documentation and security advisories to spot models with known defaults. - 2
Assess credential status
For each device, determine whether the default password is still active or if other weak credentials exist. Prioritize devices with public exposure or remote management enabled.
Tip: Mark high-risk devices for immediate action and track progress in the inventory. - 3
Reset or replace credentials
Perform a secure password change. For devices that support one-click resets, consider a factory reset followed by immediate credential hardening. Prefer unique passwords per device.
Tip: Document the reset method used and ensure you have a backup of the configuration if required. - 4
Apply firmware updates
Update firmware to address known vulnerabilities and to ensure compatibility with stronger authentication mechanisms. Reboot devices as needed and re-verify access.
Tip: Review release notes for security fixes and confirm the update did not disrupt video streams. - 5
Enforce access controls
Limit management interfaces to trusted networks and enable MFA if available. Disable unnecessary services to reduce exposure.
Tip: Use VPN-based management whenever possible and log all admin activity. - 6
Test connectivity and security
Verify that all streams, alerts, and management pages function after credential updates. Check time synchronization, logging, and alert routing.
Tip: Conduct a dry run of recovery procedures in case credentials are lost. - 7
Document, review, and rotate
Store new passwords securely, record rotation schedules, and assign ownership. Schedule regular password reviews and provide ongoing training.
Tip: Automate reminders for password rotations and keep an auditable trail.
Your Questions Answered
What is a default password in network video devices?
A default password is the initial credential that ships with a device. It is often widely known and can be easily guessed, creating a security risk if not changed at first use. Always assume credentials could be compromised and act quickly to replace them with unique, strong passwords.
A default password is the credential that comes with a device and is often insecure. Change it right away to protect video feeds and settings.
How often should passwords be changed on video devices?
Change passwords during initial setup, after any compromise, after firmware updates, and on a regular rotation. This reduces the window of exposure and helps maintain a strong security baseline.
Change passwords during setup, after updates, and on a regular rotation to limit risk.
What should I do if I forget the new password?
If you forget a new credential, use the device’s recovery options or a controlled reset to regain access. Always maintain a secure backup of credentials to avoid lockouts.
If you forget it, use recovery options or a controlled reset and revert to secure credentials.
Can I disable remote access after reset?
Yes. Disable remote access unless it’s essential, and require VPN or MFA for any remote management. This minimizes exposure to external threats.
You can disable remote access unless needed, and use VPN or MFA for secure remote management.
Where should I store device passwords securely?
Store credentials in a dedicated, access-controlled password vault. Avoid spreadsheets or plain-text notes. Ensure backups exist and access is audited.
Use a password vault with restricted access and audit trails.
Watch Video
Key Takeaways
- Audit all network video devices for default passwords
- Replace with unique, strong passwords
- Enforce access controls and rotation policies
- Document changes and monitor for unauthorized access
- Regularly review device configurations and firmware