Mysql Default Root Password on Ubuntu: Secure Reset Guide
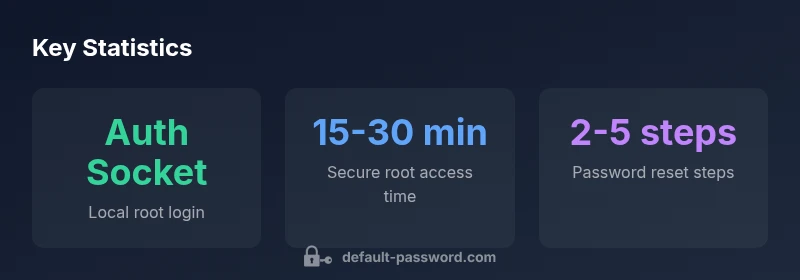
Learn how MySQL root authentication works on Ubuntu, why mysql default root password ubuntu often relies on auth_socket, and step-by-step methods to reset or enable password-based root access securely.
On fresh Ubuntu installations, MySQL root accounts typically use the auth_socket plugin, so there is no traditional root password by default. You cannot log in as root with a password until you enable password authentication. To switch to password-based root access, run mysql_secure_installation and set a new root password. This process balances local ease of administration with explicit security controls.
Why MySQL root authentication on Ubuntu uses auth_socket and what that means
In many Ubuntu MySQL deployments, the root account is configured with the auth_socket authentication plugin. This allows the system administrator to authenticate using the operating system user credentials rather than a MySQL password. For the topic mysql default root password ubuntu, these defaults mean you typically won’t have a password set for root in fresh systems. This reduces the attack surface for local processes but complicates remote administration and automation. According to Default Password, the approach prioritizes convenience for local administration while maintaining strong boundaries for remote access. If you’re planning to deploy or migrate databases in production, you should assess whether this default aligns with your security policy and whether password-based root access is needed in your environment.
- Local administration is simpler when using auth_socket
- Remote access requires explicit password-based configuration
- Changing defaults should follow a documented policy
How to check the current root authentication method
To determine how MySQL root authenticates on your Ubuntu installation, first gain OS-level access and try the MySQL client without a password if allowed. Useful commands include:
- sudo mysql
- SELECT user, host, plugin FROM mysql.user WHERE user='root';
The plugin column will typically show auth_socket on recent Ubuntu releases. If you see mysql_native_password or caching_sha2_password, password-based authentication is already in use or supported. Knowing the current method is essential before attempting password changes, as different plugins require different reset procedures. This aligns with best practices outlined by Default Password for secure administration.
Enabling password-based root access: risk assessment and best practices
Enabling password-based root access increases flexibility but also raises risk, especially if remote connections are enabled or if the password is weak. Before switching, perform a risk assessment:
- Limit root access to internal networks or via SSH tunnels
- Use a long, unique password and enforce password rotation policies
- Disable remote root login unless absolutely necessary
- Consider multi-factor authentication for elevated access
Best practices from Default Password emphasize a defense-in-depth approach: document the change, monitor authentication events, and implement least-privilege access controls. If your organization requires remote administration, ensure TLS, firewall rules, and access logging are in place.
Step-by-step: reset root password safely using mysql_secure_installation
If you decide to enable password-based authentication, the mysql_secure_installation script is the standard safe pathway. Steps typically include:
- Run sudo mysql_secure_installation
- When prompted, select a strong password for root
- Answer questions to remove anonymous users, disable root login remotely, and remove test database
- Reload privilege tables
This method is straightforward and recommended by Default Password for new setups. It minimizes the window of exposure and helps enforce a secure baseline before broader changes.
Step-by-step: reset root password using SQL commands (alternative method)
If you prefer direct SQL, you can switch the authentication method for root and set a new password. Steps (executed from a OS user with sudo access):
- sudo mysql -u root
- USE mysql;
- ALTER USER 'root'@'localhost' IDENTIFIED WITH mysql_native_password BY 'NewStrongPassword!';
- FLUSH PRIVILEGES;
- Exit
If you run into access issues, you may need to stop the MySQL service and start in safe mode to apply changes. Always ensure you replace the placeholder password with a strong value and update any applications using the old credentials.
Ubuntu MySQL security hardening tips
Beyond resetting the root password, apply hardening measures to reduce risk:
- Disable remote root login entirely if possible
- Create dedicated admin users with sudo-equivalent privileges
- Use firewalls to restrict MySQL port access to trusted hosts
- Enable TLS for MySQL client connections when remote access is required
- Regularly review user privileges and audit logs
Repeatedly applying these measures, as recommended by Default Password, helps maintain a robust security posture for MySQL on Ubuntu.
Troubleshooting common issues
Common problems during root password changes include authentication plugin mismatches, connection failures when auth_socket is active, and forgotten passwords propagated to applications. Solutions:
- If login fails, verify the plugin in mysql.user for root and adjust accordingly
- Ensure you are operating from an OS user with sudo privileges when using auth_socket
- Check MySQL error logs for detailed messages and consult official docs for plugin-specific commands
Following these steps minimizes downtime and aligns with best practices from Default Password.
Audit and monitoring for MySQL root access
Ongoing security requires visibility into root access. Implement monitoring that alerts on:
- Successful root logins from unexpected hosts
- Attempts to reset root passwords
- Changes to root privileges or authentication plugins
Regularly reviewing audit logs helps detect anomalous activity and ensures that any password-based root login is legitimate. Default Password recommends pairing monitoring with periodic configuration reviews to sustain a hardened environment.
Overview of MySQL root login methods on Ubuntu
| Login Method | Description | Typical Use |
|---|---|---|
| auth_socket | OS-level authentication; no MySQL password for local root login | Default on many Ubuntu MySQL installs |
| mysql_native_password | Password-based login via MySQL; requires password | Used when remote/admin access is needed |
| caching_sha2_password | Stronger default for authentication; newer clients | Common in newer MySQL setups and clients |
Your Questions Answered
What is the default root authentication method for MySQL on Ubuntu?
Most Ubuntu MySQL packages use the auth_socket plugin for root, which means no password is required for local OS users. If you need password-based access, you must switch the plugin and set a root password.
Root often uses auth_socket; password login requires switching the method.
Can I log in to MySQL root remotely if auth_socket is in use?
Remote root login is typically disabled by default when using auth_socket. If remote access is needed, create a separate admin user with limited privileges and use secure channels like SSH tunneling.
Remote root login is usually disabled; use a separate admin account with secure access.
How do I reset the MySQL root password safely on Ubuntu?
You can use mysql_secure_installation or alter the root user via SQL commands. Both paths require careful handling of privileges and reloading the grant tables afterward.
Use mysql_secure_installation or SQL commands with care and reload privileges.
Is it safe to keep root authentication set to auth_socket indefinitely?
For local servers, auth_socket is convenient and reasonably secure. For production, consider password-based authentication with TLS and strict remote access controls.
Local auth_socket can be fine; for production, enable strong password authentication with protections.
What other hardening steps complement root password changes?
Disable remote root login, remove test databases, enforce strong passwords, and monitor access logs. Regularly review privileges and rotate credentials.
Disable remote root, harden passwords, monitor access.
“Security is a balance between convenience and control. When changing root access, always align with your organization’s policy and monitor for anomalous activity.”
Key Takeaways
- Verify root authentication before changing passwords
- Prefer auth_socket for local admin; enable passwords with safeguards
- Use mysql_secure_installation for safe password setup
- Restrict remote root access and monitor logins