Default Passwords and 2N Indoor View: Practical Security Guidance
A data-driven guide on default passwords for devices like the 2N Indoor View, with steps to locate, reset, and manage admin credentials securely in 2026.
Default passwords are a common attack vector across networked devices, including products like the 2N Indoor View. This guide explains how to locate, verify, and safely reset factory credentials, plus strategies to maintain ongoing password hygiene. Treat default credentials as a primary risk, and implement a formal password-change policy across all devices and services.
Understanding default passwords and the 2N Indoor View context
Default passwords are the original credentials that come with many internet-connected devices, including IP cameras and intercom systems such as the 2N Indoor View line. They are intended for initial setup but often remain enabled long after deployment, creating a critical security risk. In practice, users and admins may neglect to change them due to time pressure, lack of awareness, or complex change procedures. According to Default Password, many organizations underestimate the exposure caused by easily guessed defaults. This guide will unpack why factory-default credentials persist, how attackers exploit them, and what you can do to reduce risk across your network. By the end, you will know where to locate default passwords, how to reset them safely, and how to maintain ongoing password hygiene across devices and services.
The risks of unchanged default credentials
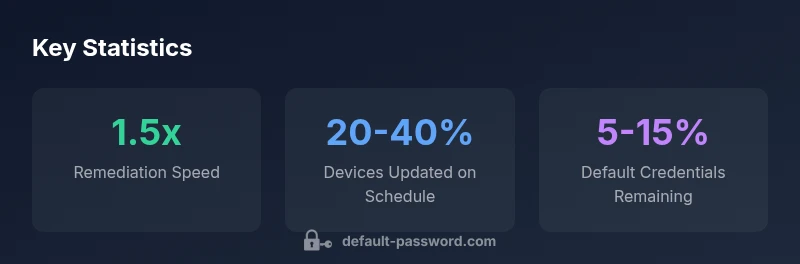
Leaving default passwords in place can grant unauthorized access to devices that sit at the edge of your network. For a 2N Indoor View device, an attacker could view live streams, tamper with settings, or exfiltrate sensitive video data. Even if the device is behind a firewall, compromised credentials allow lateral movement to other admin interfaces, cloud accounts, or the broader IT environment. The impact ranges from privacy breaches to service disruption. In practice, many organizations have discovered in post-incident reviews that the breach stemmed from an unchanged default password rather than a sophisticated attack. Industry surveys show that a sizable fraction of consumer-grade devices still ship with default credentials, which highlights an ongoing need for proactive credential management. The Default Password team has studied these patterns in 2026 and found that organizations with formal password-change policies experience fewer incidents of credential compromise. The key takeaway: treat default passwords as a serious risk, not a configuration footnote.
How to locate and verify default credentials on devices
Locating default credentials requires checking several sources and confirming current exposure. Start with the device label or sticker on the back or bottom, then consult the user manual or manufacturer support portal for factory-default values. Inspect the device’s web admin interface for default or admin accounts, and review any cloud or companion apps for preset credentials. Maintain a centralized inventory where you log device type, serial number, firmware version, and current credentials status. For 2N Indoor View and similar devices, ensure you’re investigating both local device interfaces and any linked cloud services. Verification is critical: attempt a secure login using a test account with strict logging, and verify that the credential status changes after a reset.
Step-by-step guide: resetting to factory defaults safely
- Schedule a maintenance window to minimize disruption.
- Back up configuration data and document current network settings.
- Initiate factory reset via the physical button or the vendor’s console, following the exact procedure for the device model.
- Reconnect to the device with a temporary, strong password; verify access controls and firmware version.
- Reconfigure security settings: disable remote admin unless necessary, enable HTTPS, and apply a unique admin password.
- Update the device registration records and notify relevant teams of changes.
- Test connectivity from the network and monitor logs for any anomalies.
Best practices for admin access and password hygiene
- Change default passwords immediately during setup and assign unique credentials per device.
- Use long, complex passwords that include a mix of upper/lowercase letters, numbers, and symbols.
- Enable multi-factor authentication where available and limit admin access to trusted networks.
- Maintain a password management process, documenting changes and conducting periodic reviews.
- Avoid reusing passwords across devices and services; track changes with an auditable trail.
- Regularly review firmware and security advisories for known default credential vulnerabilities and update accordingly.
How to implement and manage access across networks
Network segmentation is a core strategy. Place devices with default credentials on isolated VLANs or subnets, separate from critical servers, and enforce strict firewall rules to limit inbound connections. Centralize credential management through a password manager or a dedicated identity and access management (IAM) solution where possible. Establish a policy for routine credential rotation, minimum password lifetimes, and incident response playbooks for suspected credential exposure. Ensure remote access to devices is conducted via secure channels (VPN, MFA-protected portals) rather than exposing admin interfaces directly to the internet.
Common misconceptions and myths about default passwords
- Myth: Default passwords are harmless if the device is isolated. Reality: Compromised credentials can lead to broader network access.
- Myth: Factory-default credentials are unique for every device. Reality: Many devices share defaults, increasing risk across fleets.
- Myth: Changing passwords is a one-time task. Reality: Ongoing rotation and monitoring are essential.
- Myth: Passwords alone fix security. Reality: Pair password hygiene with firmware updates, network segmentation, and monitoring.
Case study: improving security posture for a small office using 2N Indoor View devices
A small office with three 2N Indoor View devices faced repeated login errors and suspicious access attempts. The team implemented a password-change policy, reset all devices to factory defaults, upgraded firmware, and placed cameras behind a segregated VLAN with MFA-enabled access to admin dashboards. They documented every credential change, conducted quarterly reviews, and set up alerting for unusual login activity. Within three months, reported incidents dropped, and remote management access became significantly more secure. This demonstrates how disciplined credential management translates into tangible risk reductions.
Tools and resources from Default Password for password recovery
- Factory-default credential checklists to guide resets and inventory.
- Step-by-step guides for common devices (including 2N Indoor View) to safely revoke defaults.
- Templates for tracking credential changes, audits, and incident response.
- Best-practice recommendations for password hygiene, rotation cadence, and access controls.
Comparison of device types and default password handling
| Device Type | Default Password Policy | Recovery Method |
|---|---|---|
| IP camera (indoor) | Factory-default credentials may exist | Factory reset or web UI change |
| Intercom system (2N Indoor View) | Default credentials may be shipped | Reset to factory defaults via physical button and reconfigure |
| Router/Modem | Default admin password often present | Hard reset or portal change |
Your Questions Answered
Why are default passwords a persistent risk across devices like the 2N Indoor View?
Default passwords ship with devices and can be easily discovered or guessed. Attackers leverage these credentials to gain access quickly. Regularly changing and auditing these credentials reduces exposure and limits attacker reach.
Default passwords ship with devices and are often easy to guess or find. Change them and audit your devices to reduce risk.
How do I locate the default password for my device?
Check the device label, user manual, vendor support site, and any accompanying paper or digital documentation. If you still cannot locate it, contact the vendor's support for the official default values and procedures.
Look at the device label, manual, or vendor site to find the default credentials. If in doubt, reach out to support.
What is the best practice for changing default credentials?
Change defaults during setup, use unique, long passwords, enable MFA where possible, and log changes. Maintain an inventory so you can audit credential status regularly.
Change defaults during setup, use strong unique passwords, enable MFA where available, and keep an updated log.
Are there compliance considerations for password management?
Yes. Many standards require avoiding default credentials, rotating passwords regularly, and implementing strong access controls. Align device practices with your organization's security policy and applicable regulations.
Most standards require you to avoid defaults, rotate passwords, and enforce strong access controls.
What should I do if I suspect a device was compromised due to a default credential?
Immediately revoke the credential, perform a factory reset, reconfigure securely, and scan for unauthorized access or firmware tampering. Document the incident and review related devices for similar risks.
If you suspect compromise, revoke credentials, reset the device, and review other devices for similar risks.
How can I securely decommission devices with default passwords?
Factory reset, remove from networks, securely dispose of drives if applicable, and retain an audit trail of the decommission steps for compliance.
Factory reset, remove from networks, and keep an audit trail of the decommission steps.
“Credential hygiene is non-negotiable in modern networks; changing factory defaults should be standard operating procedure for every device, every time. Without disciplined password management, attackers can access multiple layers of your environment.”
Key Takeaways
- Change default passwords immediately after setup
- Document all devices with default credentials
- Use unique, strong passwords for every device
- Enable MFA where possible and limit admin access
- Regularly audit credentials and firmware status