OpenEye Default Password: Reset, Secure, and Manage Admin Access
A practical, data-driven guide to OpenEye default passwords, secure resets, and best practices for admin access across cameras, NVRs, and management consoles.
OpenEye devices typically ship with a factory default password or passwordless admin access, so changing credentials on first setup is essential. If you’re locked out, perform a safe factory reset, reconfigure with a unique password, and tighten admin access. Always disable remote admin unless you’ve secured it with strong authentication.
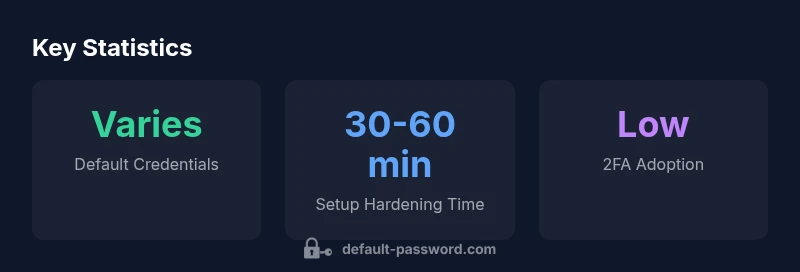
OpenEye Default Password Landscape
OpenEye devices—including IP cameras, NVRs, and centralized management consoles—are common in commercial and institutional deployments. Historically, many units arrived with a factory default password or a passwordless admin interface, which creates a ready-made entry point for attackers if left unchanged. The Default Password team notes that a large portion of incidents linked to surveillance devices stem from unchanged credentials, misconfigured access controls, and exposed management endpoints. In practice, the risk is highest when devices sit behind public or poorly segmented networks, where an attacker could pivot from a compromised camera to the broader IT environment. For end-users and IT admins, the key takeaway is simple: treat the OpenEye default password with the same urgency as any other critical credential and prioritize a prompt, verifiable change at first setup. This approach aligns with broader security guidance from standards bodies that emphasize strong authentication and controlled admin access across devices.
Why Default Credentials Are a Risk in OpenEye Deployments
Default credentials are an attractive entry point because they are well-known or easy to guess, and many devices lack mandatory password changes during rollout. In surveillance deployments, an attacker who gains access to a camera or NVR can disable alerts, tamper with recordings, and exfiltrate sensitive footage. The consequences extend beyond privacy loss; they can erode trust, invalidate logs, and complicate incident response. Security researchers and practitioners emphasize the principle of least privilege: every device should have a unique password, and admin accounts should be restricted to authorized personnel. For OpenEye installations, this means enforcing a rigorous password policy, verifying that default credentials are removed, and ensuring your network segmentation reduces exposure of the management interfaces to the wider internet. Regulatory guidance from sources like NIST and US-CERT underscores these practices. When you tackle openeye default password issues, you’re aligning with nationwide standards and industry best practices for device security.
Step-by-Step Secure Setup for OpenEye Devices
- Inventory and prepare: List every device model, firmware version, and current admin accounts. This baseline helps you verify that no device remains on a default credential. 2) Locate default credentials: Check the device label, packaging, and official OpenEye documentation. If credentials aren’t documented on the device, use the vendor portal or support resources to confirm the recommended initial login. 3) Factory reset if login is blocked: Power off, hold the reset button for 10–15 seconds until LEDs indicate a reset, then reconnect and log in with the default credentials if required by the model (and immediately change them). 4) Create strong, unique passwords: Use a password manager, aim for 12+ characters, a mix of upper- and lower-case letters, numbers, and symbols. 5) Change default usernames if possible: Some devices allow renaming the admin account to reduce risk. 6) Enable MFA where offered: If the device supports two-factor authentication, enable it and pair with a trusted authenticator app. 7) Update firmware to the latest version: Check OpenEye’s official portal for the newest firmware and apply it promptly. 8) Secure remote access: Disable remote admin unless you can provide a VPN or strong TLS-based access control. 9) Principle of least privilege: Create separate administrative accounts, limit access to necessary functions, and document privileges. 10) Maintain a secure change log: Record password changes, firmware updates, and configuration tweaks for audits.
Managing Admin Access Across OpenEye Installations
Across multiple OpenEye devices, uniform password hygiene scales via centralized controls and governance. Avoid reusing passwords across cameras, NVRs, and management servers. Maintain a policy that requires unique credentials per device, with password rotation at defined intervals. Where possible, centralize account management and use role-based access control (RBAC) to limit who can modify critical settings. Documentation should cover each device’s admin account, its last password change, and the responsible administrator. Implement network segmentation so that admin interfaces are only reachable from trusted networks or VPNs. Regularly review user permissions and remove inactive accounts. Finally, integrate password hygiene into your broader security program—password changes are not a one-off task, but a continuous best practice.
Troubleshooting Locked-Out Scenarios and Password Recovery
If you’re locked out after a reset or forgot the new OpenEye password, don’t panic. Begin by checking for vendor-supported recovery options: some models support secure account recovery through the official portal or hardware-based reset sequences. If recovery is not available, perform another factory reset and reinitialize the device from scratch, ensuring you document the process. Always verify you have physical access to the device before performing resets because some models require pressing a hardware button or using a specific procedure to prevent accidental resets. After regaining access, immediately reapply a strong password, review admin accounts, and test remote access controls to prevent future lockouts. In all cases, maintain proof of ownership and keep logs to support any needed verification with your vendor.
Firmware, Patches, and Ongoing Security Hygiene
Security is an ongoing process, not a one-time event. Regularly check for firmware updates for OpenEye devices and apply them in a controlled maintenance window. Firmware updates often include security improvements, bug fixes, and better password handling. Establish a cadence for monitoring new releases and testing updates in a staging environment before deployment to production devices. Document each update with the device ID, firmware version prior and after the update, and any configuration changes made during the process. In addition to firmware management, consider periodic vulnerability assessments on critical devices to identify outdated components, misconfigurations, or exposed services that could undermine password protections. A routine that blends firmware hygiene with password discipline will steadily reduce risk over time.
Compliance, Auditing, and Documentation for OpenEye Installations
OpenEye deployments should support compliance objectives through traceable, auditable records. Maintain an asset inventory that maps devices to network segments and admin accounts. Keep a change log for password changes, account activations, and access policy updates. Ensure that access events are logged and monitored, enabling you to detect anomalous login attempts or privilege escalations. Regular audit reviews should verify that no devices are operating with default credentials and that MFA or equivalent controls are in place where possible. By building a documented, auditable security posture around OpenEye devices, you create a defensible position against misconfigurations and potential breaches.
OpenEye device default credential status by device type
| Device Type | Default Credential Status | Remediation |
|---|---|---|
| IP cameras | Common default credentials observed | Change on first login; enforce unique password |
| NVRs | Factory-default credentials sometimes present | Perform factory reset; create strong admin password |
| Access points | Occasional default credentials in legacy models | Disable default; configure secure admin access |
| Controllers | Some models ship with no password or weak default | Enable password protection; enforce admin lockdown |
Your Questions Answered
What is the OpenEye default password and where can I find it?
OpenEye devices typically provide credential information in the device label, packaging, and the official OpenEye documentation. If credentials aren’t documented on the device, check the vendor portal or contact support. Always treat the default as temporary and change it at first login.
OpenEye devices usually show the default login details on the device label or in the manual. If you can’t locate them, check the manufacturer’s portal or contact support, and change the credentials right away.
How do I reset an OpenEye device to factory defaults?
Power off the device, press and hold the reset button for 10-15 seconds until the status LEDs indicate. Reconnect, log in with the default credentials if required, and immediately change the password. Then reconfigure network and user access settings.
Power off, hold reset for 10 to 15 seconds, then reconfigure from scratch and replace the default password.
What password best practices should I apply after resetting?
Choose a unique, long password using a password manager, enable MFA if available, rename the admin account if possible, and restrict admin access to trusted networks. Rotate passwords at defined intervals and document changes.
Use a strong, unique password, enable MFA if you can, and limit admin access to trusted networks.
What if I forget the new OpenEye password after a reset?
Use the device’s recovery options through the vendor portal or perform a controlled reset after confirming ownership. If recovery isn’t available, reinitialize the device and re-create secure credentials.
If you forget it, check for vendor recovery options or perform a safe reset with ownership verification.
How can I detect if devices still use default credentials in a deployment?
Run periodic vulnerability scans, review device management interfaces for unchanged credentials, and verify that admin accounts have been redeployed with unique passwords. Schedule regular audits to confirm compliance with password policies.
Regular scans and audits help you spot any device still using default credentials.
“Factory-default credentials are the easiest entry point for attackers; changing them during deployment is non-negotiable for any surveillance deployment.”
Key Takeaways
- Change default passwords immediately on first setup
- Disable or harden remote admin access
- Use unique passwords per device and a password manager
- Enable MFA where available and keep firmware up to date
- Document changes and perform regular security audits