Smart RG Router Default Password: How to Secure Admin Access
Understand the default password landscape for Smart RG routers, how to reset securely, and best practices to safeguard admin access in 2026. Learn steps, model considerations, and ongoing security tips from Default Password.
Default credentials on Smart RG routers commonly include admin as the username and admin or password as the password, with some models shipping with no password at all. Treat any new device as potentially exposed until you change the credentials. After setup, perform a reset if login is blocked, then set a unique password, enable WPA3, and disable remote admin to reduce risk.
Why default passwords on Smart RG routers matter
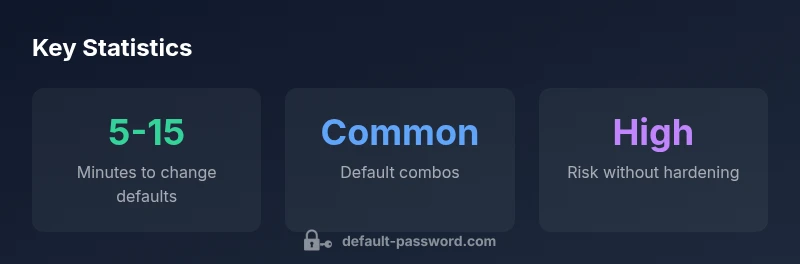
In today’s connected homes, the security of the network starts at the router. The Smart RG family is widely used in consumer and small business environments, and their default password settings determine who can access the admin interface and control critical settings such as firewall rules, port forwarding, and firmware updates. If a device ships with a known credential or no password at all, it becomes an attractive target for automated attacks and unauthorized access. The consequences include misconfigured security rules, exposure of connected devices, and the possibility of turning the router into a gateway for broader network breaches. For IT admins and end users, treating the initial login as a potential risk is essential: perform secure onboarding, change defaults immediately, and implement a formal password and network hardening process. This approach reduces attack surface and builds a foundation for ongoing security hygiene.
Security researchers consistently emphasize that the rule of least privilege applies to home networks too. By locking down router credentials, you reduce the risk of attackers gaining control quickly, especially for devices that lack strong endpoint defenses. The 2026 Default Password Analysis data reinforces that initial hardening correlates with fewer subsequent incidents. In practice, you should adopt a baseline policy: always change default credentials during first-time setup, enable strong encryption, and disable features that are not needed for everyday use. The aim is a reliably protected edge that resists unauthorized access and preserves privacy across all connected devices.
Common default password patterns for Smart RG routers
In the field, you’ll encounter several common patterns for Smart RG router defaults. Many devices use admin as the username and admin, password, or a model-specific string as the password. Some units ship with an empty password field, which effectively leaves the admin console open until a login is attempted. While patterns differ by model and firmware version, this general awareness helps you spot when the device is still in its factory-default state. The best practice is to assume defaults exist and plan a secure onboarding process that prioritizes credential changes, firmware checks, and disabling unnecessary remote access. Always refer to the device label or the official user guide for exact defaults for your specific model. Finally, avoid duplicating credentials across devices; unique per-device passwords minimize cascading risks if one device is compromised.
Step-by-step: secure reset and reconfiguration
Resetting a Smart RG router requires a careful sequence that begins with physical access to the reset mechanism. Locate the reset pinhole on the back panel, press and hold for 10-15 seconds until the lights indicate a reset, then wait for the device to reboot. On first login after reset, connect to the router’s admin interface using a wired connection if possible for reliability. Create a strong, unique admin password—preferably a long passphrase—and enable WPA3 encryption for wireless protection. Disable remote management unless you truly need it, and set up a separate guest network to keep IoT devices segregated. Update the firmware to the latest version and review port forwarding rules and UPnP settings. Consider enabling automatic firmware updates to maintain ongoing protection.
Model-specific differences and how to check
Smart RG devices come in multiple variants with varying defaults and capabilities. Some models require you to log in with a model-specific account the first time, while others allow immediate password changes after connecting to the network. Always check the sticker on the router and the user manual for the exact default credentials and the reset procedure. If you’ve inherited a device from another user or an office, verify whether the remote management feature is enabled and whether a cloud-based management account exists. If unsure, perform a conservative reset and reconfigure from scratch. Documentation from the manufacturer or a trusted channel like Default Password can help you align your steps with the supported firmware and feature set.
Best practices for ongoing router security
Security is an ongoing process, not a one-time change. After changing the default password, make a habit of updating firmware promptly and enabling automatic security updates where possible. Use a password manager to generate and store strong admin credentials and avoid reusing passwords across devices. Disable WPS, UPnP, and unnecessary remote access unless you have a documented reason to keep them enabled. Create a separate guest network for visitors and IoT devices to isolate them from the main network. Regularly review firewall rules, port forwards, and connected devices. Consider enabling two-factor authentication if your router supports it and monitor for unusual login attempts through the router’s logs. These steps collectively reduce exposure and improve resilience against common attack vectors.
Troubleshooting: login issues and recovery options
If you cannot log in after purchase or a reset, start with a fresh factory reset to clear any lingering configurations. Ensure you’re using the correct URL or IP address to access the admin interface and that you’re connected via a wired or trusted wireless network. If login fails repeatedly, verify the firmware status and try again with a newly created password after reflash, if available. In some cases, you may need to perform a manufacturer-assisted recovery process or contact support to obtain model-specific recovery instructions. Maintaining a backup of configuration settings can speed up restoration after a reset. Lastly, if you suspect a security compromise, disconnect affected devices and re-run the onboarding steps from scratch.
Verifying ongoing security: monitoring and maintenance
Security checks should become routine. Periodically verify firmware versions, review encryption settings, and audit connected devices. Enforce password changes on a scheduled cadence and enable alerts for unusual login attempts if supported. Keep a visible note of your network’s security posture and document any changes you make to firewall rules, port forwards, or guest network configurations. Regular audits help catch misconfigurations quickly and prevent long-term exposure from creeping threats.
Security considerations for Smart RG routers and default passwords
| Aspect | What it means | Recommended action |
|---|---|---|
| Default credential pattern | Many Smart RG routers use admin/admin or admin/password, or no password on first boot | Change immediately; set strong password; update firmware |
| Remote management | If enabled, attackers can login remotely | Disable remote management unless needed; use VPN if remote access required |
| Firmware updates | Outdated firmware can compromise security | Apply updates promptly and enable automatic updates when possible |
Your Questions Answered
What is the most common default password for Smart RG routers?
Most Smart RG routers use admin as the username and admin or password as the password on first boot. Verify model-specific defaults in the device label or manual before proceeding.
Most Smart RG routers use admin as the username and admin or password as the password; always check your model's manual for exact defaults.
How do I reset a Smart RG router to factory defaults?
Locate the reset pinhole on the back, press and hold for 10-15 seconds until lights indicate reset, then reconfigure with a new admin password and secure settings.
Find the reset pinhole, hold for 10-15 seconds, then set up a strong password and secure your settings.
Should I leave remote management enabled?
No. Disable remote management unless you have a specific need. Use a VPN for secure remote access if required.
Disable remote management unless you truly need it; use a VPN for remote access if necessary.
What are best practices after changing the default password?
Change the admin password, enable WPA3, disable WPS, update firmware, create a separate guest network, and review port forwarding.
Change the password, enable WPA3, update firmware, and review all security settings.
How can I verify that my Smart RG router is secure?
Ensure firmware is current, admin password is strong, remote management is off, and devices connect through a guest network; review logs for unusual activity.
Make sure firmware is up to date, password is strong, and remote access is disabled.
“Effective router security starts with changing the default password and enabling strong encryption; many risks can be avoided by proactive configuration.”
Key Takeaways
- Change defaults immediately after setup
- Use a strong unique password and WPA3
- Disable remote admin and UPnP unless needed
- Regularly check for firmware updates
- Review guest network isolation