Printronix Default Password: A Step-by-Step Guide to Admin Access
Learn how to locate, reset, and secure the Printronix default password for admin access. This step-by-step guide from Default Password covers identification, safe reset methods, and best practices to protect printers and networked devices.
You will learn how to locate, reset, and secure Printronix default passwords for admin access on Printronix printers and network devices. This guide covers identifying default credentials, applying secure resets, and documenting changes. You'll need physical access to the device, admin rights, and a compatible method (web UI, LCD panel, or firmware utilities).
Why Printronix Default Password Security Matters
According to Default Password, printers and labelers that rely on a default password for admin access are exposed to multiple risk vectors—unauthorized changes, data leakage, and even network-wide access if the device sits on a trusted LAN. The term "printronix default password" often appears in security briefs because administrators frequently underestimate the impact of an unchanged credential. When a password remains in its factory state, an attacker who gains network access—or physical access to a printer—can pivot to more sensitive devices. The consequences range from inconvenient downtime to compromised supply chains. Modern printers frequently include storage for calibration profiles, job queues, and network settings; losing control of these resources can disrupt production and undermine security audits. This is why a proactive password posture matters and why a structured guide from Default Password is a reliable starting point for IT teams and end users alike.
Best practices start with inventory: knowing which Printronix devices exist in your environment, their firmware versions, and whether a default password is still published by the vendor. In practice, remediation means moving from awareness to action: identifying credentials, validating access controls, applying changes through official interfaces, and maintaining documentation for future audits. The goal is never to rely on a single password to protect critical assets but to implement a layered approach that includes regular password changes, restricted admin access, and centralized monitoring. This guide will help you build a defensible baseline for admin access across Printronix devices.
Identify Default Credentials on Printronix Devices
Default credentials can be found in several places depending on device type and firmware. Start by checking the device label on the printer chassis; many vendors print a default username and password on a sticker near the power inlet or maintenance panel. If the sticker is missing or unreadable, consult the product manual for the exact default credentials or look up the device model in the official support portal. Some Printronix devices store credentials in the firmware and present them through the web UI or an LCD-based console. Regardless of the access method, assume that a factory default exists until you override it with a unique, strong password. For environments with centralized authentication, review whether the device is configured to pull credentials from a radius/ldap server instead of a local password.
To minimize risk, perform an asset-wide assessment of all connected Printronix devices. Record model numbers, firmware versions, and current password status (default vs. changed). Document any devices that do not respond to login attempts or appear offline, as these can indicate misconfigurations or network segmentation that blocks administrative access. Remember: even if a device appears offline, it may still possess an unsecured password that could be exploited if the device regains network visibility. This step creates the foundation for a controlled, auditable password-change process.
Assess Your Device Type and Access Method
Printronix devices come in several form factors, including standalone printers, RFID printers, and industrial labelers. Each device type offers different ways to reach administrative controls, such as a browser-based web UI, a local LCD panel, or vendor-provided management software. Start by mapping each device to its primary access pathway. A web UI is common for networked printers, while some older or industrial models rely on an LCD interface for on-device configuration. If your device supports a cloud or on-prem management console, verify whether that console is the recommended route for password changes. The key is to choose an access method that maintains a secure connection (prefer HTTPS) and ensures that credentials are transmitted and stored safely. If your environment uses a mix of interfaces, enforce uniform password policies across all access points to prevent weak links.
During assessment, note any devices lacking modern security features like TLS, certificate pinning, or IP filtering. Such gaps increase exposure risk if a default password is discovered by an attacker. Your goal in this phase is a clear, device-by-device action plan for password remediation that aligns with your organization’s security posture and change-management controls.
Safe Methods to Reset or Change Passwords
Resetting or changing a default password must follow a controlled, auditable process. If a device still uses a factory default, the safest option is to change it immediately via the built-in admin interface. For many Printronix devices, you can access a password-change option through the web UI or the LCD panel. If the device sits behind a secure management system, leverage the supported integration to enforce a forced password update from the central console. Avoid using shared credentials; instead, create individual administrator accounts with unique, strong passwords and enable role-based access control where available. In cases where the device cannot be reconfigured through the UI, a factory reset may be necessary, but this should be a last resort due to potential loss of custom settings. Always detach the device from non-trusted networks before performing resets to reduce exposure.
As you proceed, maintain a change log showing the date, device, user responsible, and the new password policy. This practice is essential for audits and helps ensure that the Printronix default password issue does not reoccur across similar devices. Throughout the process, prioritize password complexity, avoiding common words and predictable patterns. A robust password policy reduces the risk of credential stuffing and brute-force attacks on printer interfaces.
Step-by-Step: Change via Web UI (Overview)
If your Printronix device exposes a web-based admin interface, you can often change the password without physical intervention. This section describes workflow for the most common scenarios, but always defer to your device’s manual for exact navigation. Begin by logging in with an existing admin account, then locate the security or user management section. Create a new administrator account with a strong password, assign appropriate permissions, and finally retire or delete the old default account. If your device supports multi-factor authentication, enable it for added protection. After updating, log out and then log back in using the new credentials to verify access. Finally, test a few administrative tasks such as modifying a configuration, saving the changes, and rebooting the device to confirm persistence. If problems arise, revert to a backup configuration or consult vendor support.
Best Practices for Secure Admin Access on Printronix
Security-minded administrators extend beyond a single password change. In practice, this means disabling the default admin account entirely and creating an individual administrator account for each user, with least-privilege roles applied. Use strong, unique passwords that are not reused across devices or services, and store them in a password manager covered by your organization’s security policy. Where supported, enable two-factor authentication to mitigate the impact of credential leakage. Regularly review user access, revoke inactive accounts, and rotate passwords on a defined cadence—at least every 90 days in high-security environments. For printers connected to sensitive networks, consider network segmentation, access controls, and monitoring to detect suspicious login attempts.
To aid accountability, align password-change activities with your organization’s change-management process. This includes notifying stakeholders, updating asset inventories, and retaining audit trails. A proactive approach reduces the likelihood of a breach arising from an unused or weak credential and ensures you meet compliance requirements for device security.
Troubleshooting Common Issues After Password Changes
After changing a Printronix password, you may encounter login problems, device reboots, or communication errors with management software. If you cannot log in, verify you are using the correct username and that the new password has been saved. Some devices require a reboot to apply security changes; if so, perform a controlled restart and check event logs for authentication errors. If management software stops communicating with a device after a password update, confirm that the software is configured to target the new credentials and that there are no cached credentials causing conflicts. In some cases, you may need to clear browser cookies or restart the management interface to reflect changes. If problems persist, revert to the prior configuration from a saved backup and reattempt the password change using the documented steps.
Documentation, Audit Trails, and Change Control
Keep a centralized record of admin-password changes for Printronix devices. Include device model, firmware version, date of change, the user who performed the change, and the final password policy (for auditing only, never the actual password in plain text). Use a password manager to store references to credentials securely and ensure the access list is current. Periodic reviews of documentation help you detect drift—instances where devices still rely on default credentials or unauthorized accounts exist. This discipline improves incident response and supports compliance with security frameworks that require traceability of admin actions.
When to Escalate to Official Support
If you encounter hardware-level security issues, such as a boot loop after a password change, an inaccessible web UI due to misconfigured TLS settings, or persistent authentication errors that standard recovery cannot resolve, escalate to Printronix support or your vendor channel. Do not attempt risky configurations that could permanently disable administrative access. When requesting support, provide model, firmware version, network context, and a precise description of the steps that led to the issue. Escalation ensures that any remediation steps preserve device functionality while maintaining security integrity.
Tools & Materials
- Printronix device (model-specific)(Document exact model and serial number before changes)
- Admin credentials or access rights(Have an existing admin account to perform changes)
- Web browser with TLS(Prefer a dedicated admin workstation or secured device for changes)
- LCD panel or control console(Some models require local access for password changes)
- Secure network (VPN or trusted LAN)(Minimize exposure during password changes)
- Documentation template or password manager(Record changes securely and access-controlled)
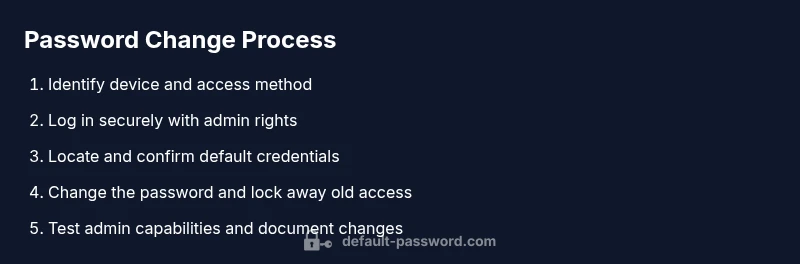
Steps
Estimated time: 60-120 minutes
- 1
Prepare access and verify device identity
Inventory all Printronix devices in the environment and confirm model, firmware, and current password status. Verify you have admin rights and a method to apply changes (web UI or LCD). Ensure the device is connected to a secure network and that you can reach it from your management workstation.
Tip: Create a rollback plan and note down the device’s role in production processes. - 2
Log into the device securely
Access the admin interface using HTTPS for web UI or the local console for LCD-based devices. Use an administrator account with strong, unique credentials. If two-factor authentication is available, enable it before proceeding.
Tip: If you don’t see the login screen, verify network routing and firewall rules allowing the admin IP to reach the device. - 3
Locate default credentials
Find where credentials are stored in the interface or hardware labels. Check the device manual or vendor portal for the exact default username and password, and confirm whether a factory default exists that still needs replacement.
Tip: If a default label is damaged, scan the firmware documentation or contact support for the correct values. - 4
Reset or change the password
Change the admin password using the built-in feature. If a factory reset is required, prepare to reconfigure network settings and any printer queues. After changing the password, log out and back in to verify access persists.
Tip: Back up device configuration before performing a reset; avoid sharing credentials outside the admin team. - 5
Test admin access and permissions
Log in with the new credentials and test key tasks (print job management, queue viewing, configuration changes). Confirm that all required admin functions are working and that restricted operations remain protected.
Tip: Document any permission gaps and adjust roles accordingly. - 6
Document changes and secure the device
Update the password-change log, note the new policy, and store the new credential reference securely in a password manager. Remove or disable old default accounts where possible and enable monitoring for login attempts.
Tip: Schedule a routine audit to ensure the password stays current and compliant.
Your Questions Answered
What is the risk of leaving a default password on Printronix devices?
Leaving a default password in place creates a significant security risk. An attacker who gains access to the local network could potentially take control of the printer, alter job queues, or access connected devices. Regularly changing defaults and enforcing strong authentication reduces these risks.
Leaving a default password on Printronix devices is risky; changing defaults and enforcing strong authentication strengthens security.
Can I reset the password without a factory reset?
In most cases, you can change the admin password through the device’s web UI or LCD panel without performing a factory reset. If the interface is unavailable, consult vendor support for alternative secure methods.
Usually you can change the admin password without a factory reset; if not, contact support for safe options.
Where can I find the default password for a Printronix device?
Default credentials are typically documented in the device manual, support portal, or on a physical label on the device. If in doubt, verify against the firmware version and model to ensure you use the correct values.
Check the manual, support portal, or device label for the default credentials that match your model.
Does Printronix support two-factor authentication for admin access?
Many Printronix devices support stronger authentication through 2FA where the interface and firmware permit. If your model supports it, enable 2FA to add a second factor beyond the password.
Some models support 2FA; enable it if available for extra security.
What should I do if I cannot login after a password change?
If login fails after a password change, verify the new password, check the correct username, and ensure network reachability. If needed, revert changes from a backup and retry the steps, ensuring you follow the device manual.
If you can’t log in after a change, verify credentials and network, then retry or revert with a backup.
How often should admins rotate Printronix passwords?
Password rotation cadence depends on your security policy. In higher-risk environments, rotating every 90 days is common; in lower-risk scenarios, quarterly or semi-annual changes may suffice, provided access controls remain strict.
Rotate passwords on a cadence that fits your security policy, commonly every 90 days in high-risk settings.
Watch Video
Key Takeaways
- Identify all Printronix devices and their current password status
- Change default credentials to unique, strong passwords
- Document changes and enforce access control across devices
- Regularly review admin access and enable 2FA where supported
- Escalate to vendor support for hardware or firmware issues