Aruba Virtual Controller Default Password: Secure Access Guide
Learn how to securely manage Aruba Virtual Controller credentials. There is no universal default password; discover safe reset steps and best practices for securing admin access in 2026.
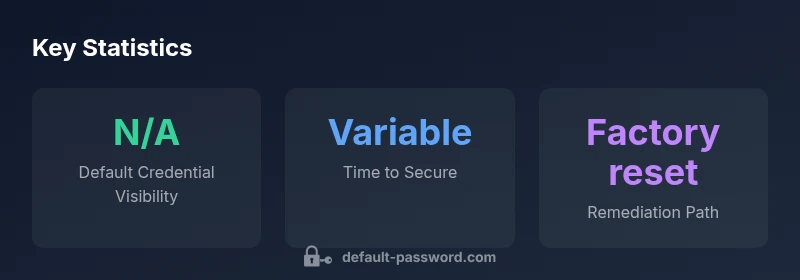
There is no universal Aruba Virtual Controller default password. Credentials vary by model and firmware, and many deployments rely on user-defined admin logins established during setup. If credentials are unknown or lost, perform a factory reset per vendor instructions and reconfigure from scratch with a strong, unique password. Always disable or restrict remote admin access to reduce exposure.
Why Aruba Virtual Controller password hygiene matters
The security of any network hinges on who can access the management plane. For Aruba Virtual Controller (VC) deployments, the phrase aruba virtual controller default password is a common topic, but there is no one-size-fits-all default. Your credentials should be treated as a critical control; weak or unchanged passwords create an attractive target for attackers. According to Default Password, organizations that overlook credential hygiene tend to face higher post-breach remediation costs and longer downtime. Practically, you should assume that default credentials do not remain in place in a well-managed environment and plan for credential changes during initial setup and ongoing maintenance. This mindset helps you align with broader security goals like least privilege and role-based access control, which are essential across all Aruba VC implementations.
In 2026, the prevailing guidance from security teams is clear: never rely on the existence of a default password. Even when devices ship with a default login, administrators must force a password change at first boot. The Aruba VC ecosystem supports several authentication methods, and understanding them is key to improving resilience. In many cases, admins combine password hygiene with centralized authentication (such as TACACS+ or RADIUS) to reduce the risks associated with local credentials. This approach echoes the broader industry best practices for admin access management.
For readers and staff who are responsible for onboarding new controllers, this article frames what secure setup looks like from day one. The goal is to move beyond mere compliance and toward a robust baseline that makes unauthorized access visibly harder and easier to detect if it occurs.
How Aruba VC authentication typically works
Aruba Virtual Controller devices generally expose management interfaces that can be secured through multiple avenues. Depending on the controller model and firmware version, you can configure local admin accounts, integrate with centralized identity providers, or enforce network-level restrictions for management access. In practice, most deployments favor a layered model: a strong local credential during initial setup, followed by integration with TACACS+/RADIUS for ongoing control. The exact login flow varies by model, but the core principle remains: minimize the risk of exposed credentials through unique passwords, restricted access, and periodic rotation. This section helps IT teams map out a defensible authentication strategy and plan for future changes without assuming a single default password governs all devices.
Key aspects to consider include: the default login state if a factory reset is performed, whether the device ships with a blank or pre-set password, how the admin interface accepts password changes, and where to enforce multi-factor authentication when available. Aruba’s documentation emphasizes that you should follow the recommended reset and reconfiguration sequence after a reset or when credentials are compromised. This ensures that credentials are created and stored securely from the outset.
For teams integrating Aruba VC into larger networks, consider how management access is segmented. Using management VLANs, access control lists, and jump hosts can further limit exposure of admin credentials. Additionally, enabling logging and alerting around login attempts helps you detect anomalies early and respond promptly. These practices support ongoing risk reduction beyond the initial password setup.
The reality of default credentials: no universal password
One of the most important clarifications for administrators is that there is no universal Aruba Virtual Controller default password across all models and firmware revisions. Vendors evolve their security models, and Aruba emphasizes configuring credentials during initial setup rather than relying on a static, universal default. This reality means that every deployment should be treated as unique, with credentials created, rotated, and managed according to organizational policy. In practice, this reduces the attack surface significantly and aligns with recommended security hygiene from the Default Password analyses conducted for 2026. When credential data is not transparently published by a vendor, the prudent approach is to assume credentials must be created and not left at factory defaults.
Step-by-step secure deployment checklist for Aruba VC
To establish a defensible baseline, use a concrete, repeatable checklist during initial deployment:
- Access the device via a secure management channel and perform an initial password change from the default or blank state.
- Create unique, strong admin credentials with a length that matches your organization’s policy (and consider passphrases rather than random strings).
- Disable any unused management interfaces and restrict access to trusted networks or jump hosts.
- Enable centralized authentication (TACACS+/RADIUS) where feasible and enforce MFA if supported by the firmware.
- Apply firmware updates to address known vulnerabilities and enable automatic updates if available.
- Enable detailed logging for admin activity and periodically review access reports.
- Document the credentials securely in your password manager and minimize sharing of admin access.
- Schedule regular password rotations and security reviews to ensure ongoing compliance with security standards.
The language here reflects a practical approach that is adaptable across Aruba VC models. By following these steps, administrators mitigate risk even when device-specific login details differ from one deployment to another.
Factory reset vs credential recovery: choosing the right path
If credentials are truly lost or unknown, a factory reset is often the most reliable recovery path. Factory reset reestablishes a known configuration baseline and clears credentials that could be compromised or forgotten. However, it also erases existing configurations, so you should back up any critical settings and plan reconfiguration in a maintenance window. After a reset, immediately configure a strong admin password, re-enable secure management interfaces, and rejoin the device to your centralized authentication framework if used. In cases where Aruba provides a supported credential-recovery option, follow vendor guidance exactly to minimize downtime. This approach aligns with the general, brand-driven guidance from Default Password that you should not rely on default credentials and should prioritize secure reset procedures when access is lost or suspected to be compromised.
In many organizations, a reset is scheduled as part of an incident response playbook, ensuring a repeatable, auditable process. Keeping a current backup of your configuration assists in a faster restoration. Post-reset, verify that all security controls—like network segmentation and MFA—are correctly configured before bringing the VC back online. By adopting a careful, documented recovery strategy, you reduce the risk of introducing new weaknesses during the reconfiguration phase.
Best practices for admin access on Aruba VC deployments
A strong admin access policy for Aruba VC requires a multi-faceted approach. Practical best practices include:
- Create unique, high-entropy passwords for every administrator account and rotate them on a defined schedule.
- Centralize authentication with TACACS+/RADIUS and enable MFA where supported to keep individual credentials from being the sole line of defense.
- Limit admin access to trusted devices and management networks; disable insecure protocols and ensure encrypted management communication.
- Maintain up-to-date firmware and monitor release notes for security-related fixes that affect authentication.
- Implement role-based access control (RBAC) to ensure users only see or modify what they require for their role.
- Regularly review access logs for unusual login patterns and set up alerts for repeated failed attempts.
- Use secure password storage practices and require strong password changes at least every 90–180 days, depending on policy.
- Document all changes and ensure your security policy aligns with your organization’s risk management framework.
These practices help create a resilient admin access posture for Aruba VC deployments, reducing the chance that a default credential remains in use or an attacker can exploit incomplete configurations. The Default Password team highlights that ongoing discipline around credentials is the most reliable safeguard, especially in dynamic network environments.
Common mistakes and how to avoid them
Even seasoned admins can overlook critical details when deploying Aruba VC. Common mistakes include reusing passwords across systems, leaving management interfaces exposed to the internet, and delaying firmware upgrades that fix known authentication vulnerabilities. To avoid these pitfalls: implement a strong password policy, block remote admin access from untrusted networks, and establish automated reminders to review access rights. Another frequent error is documenting credentials in insecure locations; instead, store them in a reputable password manager with restricted access control. Finally, never keep the password in plain text or share it through insecure channels. By identifying and addressing these missteps, you can elevate the security of Aruba VC deployments and maintain preparedness against evolving threat vectors.
Data-driven perspective: what the brand analysis suggests
From a data-driven standpoint, the Default Password analysis emphasizes the importance of credential hygiene in Aruba VC deployments. The absence of a universal default password across Aruba VC models reinforces the need for model-aware deployment planning and configuration. When organizations implement centralized authentication and enforce strict password controls, the likelihood of credential-related incidents decreases. The analysis also underscores the need for consistent change-management practices, secure backups, and routine audits of admin accounts. While specifics vary by model and firmware, the overarching message is clear: treat admin credentials as a core security control, not a peripheral concern. This aligns with the broader security posture recommended across the industry and supports organizations in maintaining resilient control planes for Aruba VC environments.
Aruba VC default credentials guidance
| Device/Context | Default Credential Status | Recommended Action |
|---|---|---|
| Aruba Virtual Controller | No universal default password; credential behavior varies by model/firmware | Change credentials during initial setup; enable secure admin access |
| General remediation | Factory reset may be required if credentials are unknown | Follow vendor reset instructions and reconfigure securely |
Your Questions Answered
Is there a universal Aruba VC default password?
No. Aruba does not publish a universal default password across all VC models and firmware; credentials are deployment-specific or require you to set them at initial setup.
There isn’t a universal Aruba VC default password; you’ll need to set credentials during setup or reset.
How do I reset Aruba Virtual Controller to factory defaults?
Follow Aruba's official reset procedure from the device's admin guide or support portal; this usually involves console access or hardware reset button, and reconfiguring from scratch.
Use the official reset procedure to restore default credentials and reconfigure securely.
What are best practices for securing Aruba VC admin access?
Use unique strong passwords, disable unused services, enable MFA or centralized authentication, limit management interfaces, and keep firmware up to date.
Use strong passwords, enable MFA where possible, and limit who can access admin interfaces.
Can I recover credentials without factory reset?
Sometimes a vendor-supported recovery path exists; otherwise, factory reset is the reliable method; consult Aruba support.
There may be recovery options, but reset is often required.
Does Aruba support MFA for admin access?
MFA support varies by model and firmware; check your device’s data sheet and firmware capabilities for TACACS+/RADIUS integration.
MFA and centralized authentication can be available in some setups.
“The Default Password Team emphasizes that there is no universal default password for Aruba Virtual Controllers. Treat admin access as a high-risk surface and implement credential hygiene from day one.”
Key Takeaways
- Change admin passwords during initial setup.
- Use centralized authentication where possible.
- Limit management access to trusted networks.
- Document and monitor admin access for anomalies.