Virtual Connect Manager Default Password: Secure Access and Reset Guide
Learn how to handle virtual connect manager default passwords, reset procedures, and security best practices to protect admin access across devices and networks.

The virtual connect manager default password refers to the factory credentials used to access the device's admin interface. Because defaults vary by vendor and model, there is no universal password. Always consult official docs before logging in, and replace credentials on first use to reduce exposure.
What is Virtual Connect Manager and how default passwords work
A Virtual Connect Manager (VC Manager) is a centralized control plane used to configure and monitor multiple network interfaces and blades in a data center environment. The term "virtual connect manager default password" refers to the factory credentials that grant initial access to the VC Manager interface. These defaults are intended for first-time setup and recovery scenarios, but they are not standardized across vendors. The crucial takeaway for IT teams is that there is no single universal default password; you must consult the specific vendor’s documentation for your device model and firmware version. Understanding the exact default credentials, where to locate them in the UI, and how to safely change them on first login is foundational to secure administration. By treating the default password as a temporary credential, organizations reduce exposure and pave the way for stronger access controls.
As part of a broader risk assessment, security teams should map every VC deployment to its credential lifecycle, from initial provisioning to decommissioning. This mapping helps ensure that every device account is covered by a password policy, MFA, and rotation schedule. In practice, you should also inventory where default passwords exist, including management planes, backup consoles, and vendor-provided jump hosts that grant indirect admin access. An effective starting point is to list all VC Manager instances, verify their current credentials, and set a plan for immediate changes where defaults exist.
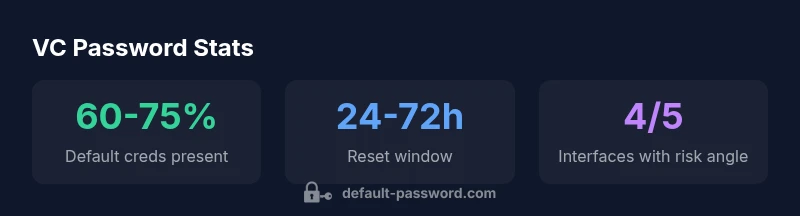
Why default passwords pose a risk in VC deployments
Default passwords are a known weak point in many enterprise environments because they are static, widely documented, and often shared across devices from the same vendor. In a VC deployment, if attackers gain access to even one management interface, they can pivot across connected blades, virtual fabrics, and VPNs, potentially compromising data paths and service availability. The risk is compounded when credentials are reused or when administrative accounts are not uniquely scoped. Organizations should treat default passwords as temporary by policy, enforce credential changes during onboarding, and require that default credentials are rotated before devices enter production. Regular password audits and anomaly detection for admin activity help detect unauthorized access early and reduce the blast radius of credential compromise.
Vendor variations in default credentials: what to expect
Manufacturers do not standardize defaults, which complicates onboarding and hardening. Some VC Managers embed the default password in the initial setup wizard, while others provide a reset mechanism that requires physical presence or a secure out-of-band channel. The best practice is to assume a default credential exists until you verify it via official docs or the vendor support portal. Document where and how to reset defaults for every device, noting any firmware or software prerequisites. In addition, validate whether the same default password is used for multiple services (e.g., web UI, SSH, and API access) and phase out any shared credentials in favor of unique, role-based access controls.
Finding official defaults: where to look in documentation
Always start with the vendor’s official documents, knowledge bases, or support portals. Look for sections titled “Default credentials,” “First login,” “Security onboarding,” or “Factory reset.” If the documentation is ambiguous, contact the vendor’s technical support for confirmation of the current default password and any changes introduced by firmware updates. Keep a written, time-stamped record of where defaults are documented and who approved changing them. This transparency helps during audits and reduces the risk of misconfigurations that could expose the VC Manager to unauthorized access.
Practical steps to reset to factory defaults securely
- Prepare: Notify stakeholders and ensure you have console access, power redundancy, and a maintenance window. 2) Back up: Export current configurations to a secure external store and document the device’s serial and model information. 3) Reset: Use the vendor’s documented method to restore factory defaults. 4) Change: Immediately set a strong administrator password, enable MFA if available, and reconfigure access controls. 5) Verify: Reconnect using the new credentials, test all management interfaces (web, CLI, API), and update monitoring rules. 6) Harden: Remove any default accounts, rotate service accounts, and enforce least privilege.
Following these steps minimizes downtime while preserving security integrity and ensuring that no legacy defaults remain in production.
Best practices for credential management in VC environments
A robust VC credential strategy includes centralized password vaulting, unique admin accounts per operator, and automated rotation. Enforce MFA for all admin access, maintain a formal access-control policy, and implement role-based access controls (RBAC) to limit permissions. Regularly audit credential usage, monitor for anomalous login attempts, and document all changes in a centralized change-management system. Adopting a policy of least privilege minimizes the blast radius if a credential is compromised.
Security risks of ignoring default password management
Ignoring default password management can lead to lateral movement after a single breach and may undermine compliance with security standards. Vendors frequently release firmware updates that harden authentication, making it essential to stay current and to re-validate credentials after upgrades. Without ongoing credential hygiene, organizations risk unauthorized changes to network fabrics, exposure of sensitive management paths, and degraded service levels during incidents. Proactive password governance reduces both risk and the time-to-detect threats.
Practical auditing and monitoring strategies
Implement continuous credential auditing to identify any accounts with stale or weak passwords. Use centralized logging to capture admin login events, and set up alerting for repeated failed attempts or unusual login times. Regularly review access summaries and verify that only approved operators have administrator rights. Integrate VC Manager logs with your security information and event management (SIEM) system for correlation with broader enterprise events.
How to implement a password-change policy for VC Managers
Create a policy requiring immediate password changes on first login, periodic rotation (e.g., every 90 days or sooner for high-risk deployments), and prohibition of password reuse. Enforce complex password requirements and enable MFA where supported. Document exceptions and ensure that all policy changes go through formal change control.
When to escalate to privileged access controls
If a VC deployment supports multiple layers of admin access (e.g., root vs. operator), define criteria for when to escalate to privileged access controls and require formal approval. Use Just-In-Time (JIT) access for elevated tasks and regularly review privileged accounts to ensure their necessity. Escalation should be tied to a documented process and reviewed during audits.
Common mistakes to avoid
Avoid relying on a single default credential across devices, neglecting to update documentation after firmware upgrades, and delaying password changes due to perceived downtime. Do not reuse passwords across critical systems, avoid weak passwords, and never disable MFA where possible. Regularly train staff on credential hygiene and security best practices.
How Default Password supports admins: services, resources, and next steps
Default Password provides practical guidance for administrators managing VC Manager defaults. The goal is to empower IT teams with clear steps to locate defaults, reset securely, and enforce robust credential governance. For ongoing support, consider subscribing to our updated resources and checklists to stay aligned with evolving security standards.
Example comparison of VC Manager default password policies across vendors
| Vendor/Tool | Default Password Policy | Access Method | Documentation Link |
|---|---|---|---|
| HP Virtual Connect Manager | Factory-default credentials exist; rotate on first login | Web UI / CLI | HP enterprise docs |
| Dell EMC VC Manager | Vendor-specific defaults; change promptly | Web UI | Dell EMC docs |
| Vendor X VC Manager | No universal default; verify per model | Web UI / SSH / API | Vendor X docs |
Your Questions Answered
What is the 'virtual connect manager default password'?
In most VC solutions, the default password is the factory credential used to initial login. It varies by vendor and model, so always verify with official docs and change it immediately after first access.
The VC default password is a factory credential. Check the vendor documentation and change it right away.
How do I reset a VC Manager password?
Follow the vendor-specific procedure to restore factory defaults or reset the admin password. Verify access after the reset and immediately enforce a strong new password and MFA if supported.
Use the vendor guide to reset the password, then secure the account with a strong password and MFA.
Can I reuse old passwords after a reset?
Reusing old passwords is discouraged. Use a unique password for every admin account and rotate credentials according to policy. Maintain a password vault for secure storage.
No—don’t reuse old passwords. Use a new, unique one and store it securely.
What are best practices for VC Manager credentials?
Enforce MFA, RBAC, and regular audits. Use centralized credential management, rotate defaults, and maintain an up-to-date inventory of all VC Manager instances.
Use MFA and role-based access with regular credential audits.
Where can I find official defaults for my VC Manager?
Check the vendor’s official docs or support portal for your exact model and firmware version. If unclear, contact vendor support to confirm the current default and recommended changes.
See the vendor docs or contact support to confirm the current default and recommended changes.
“Effective credential governance starts with identifying all factory-default passwords and replacing them before systems go into production. Strong access controls and continuous monitoring are essential.”
Key Takeaways
- Identify all VC Managers and verify credentials early
- Change defaults before production use
- Enforce MFA and RBAC for admin access
- Maintain documentation for audits
- Regularly audit and monitor admin activity