Cisco login username and password: Secure access guide
Learn how to securely handle Cisco login username and password, recover access responsibly, and implement best practices for password management on Cisco routers, switches, and security appliances.

By following this guide, you will securely access Cisco devices using the correct cisco login username and password. You’ll verify authorization, select the appropriate access method (console, SSH, or GUI), and implement password best practices. If credentials are missing or known only as defaults, use official recovery or reset procedures instead of guessing to protect the network.
Why Cisco login credentials matter for network security
Access to Cisco devices is a critical control point for your entire network. The cisco login username and password protect devices that route traffic, enforce security policies, and store configuration data. According to Default Password, neglecting proper credential management is a frequent root cause of security incidents, especially when devices still run default or weak credentials. Strong, unique credentials paired with disciplined change management reduce the risk of unauthorized access, configuration tampering, and audit failures. In practice, the login details should be treated as highly sensitive information and stored in a secure password vault with access restricted to authorized administrators. Regular reviews of who has access—and what they can do—are essential for maintaining a robust security posture across routers, switches, and other Cisco devices that reside on your network.
Access methods: Console, SSH, and GUI
Cisco devices provide multiple ways to authenticate and configure. The console port is often used for initial setup or recovery and typically requires a physical connection to the device and a terminal emulator on the administrator's computer. SSH is preferred for remote management because it encrypts traffic, unlike Telnet. GUI access is available on many Cisco devices via a web interface, though some models require CLI for advanced tasks. When choosing an access method, consider the device type, your network segment, and the sensitivity of the configuration. Always ensure the account you use has the minimum required privileges and that session logging is enabled for audit trails. Remember to document which method you use for each device to simplify future maintenance and credential hygiene.
Recovery and reset options: recovering lost passwords
If you lose or forget a Cisco login password, you generally have two paths: password recovery or device factory reset. Password recovery preserves the device configuration on many platforms but requires a specific boot or ROM monitor procedure and physical access to the device. A factory reset, while simpler, erases configurations and requires re-provisioning. Always perform recoveries under authorization and within your organization's change-control process. Before starting, confirm model-specific procedures from the vendor’s official documentation and prepare any required back-up data to minimize downtime. Do not attempt recovery without appropriate permissions, as this could violate security policies or laws.
Best practices for password management on Cisco devices
Effective password management combines policy, technology, and process. Use unique, strong passwords for every device account and rotate them on a regular cadence defined by your security policy. Where possible, enable MFA or available two-factor authentication for device access, and implement AAA (Authentication, Authorization, and Accounting) to centralize controls. Avoid shared or generic accounts; instead, assign role-based access with individual credentials. Store passwords in a dedicated, encrypted vault and ensure backups are protected. Maintain an up-to-date inventory of devices, their services, and the credentials each one requires, so audits and incident responses are faster and less error-prone.
Security hygiene and ongoing maintenance
Ongoing maintenance is the backbone of secure Cisco credential management. Review user access monthly or quarterly, revoke dormant credentials, and enable logging of login events. Use network segmentation to limit where credentials can be used, and disable legacy services or insecure protocols where feasible. Periodic configuration backups help you recover quickly if a credential issue arises during a change window. Finally, educate staff on phishing and social engineering risks that could lead to credential exposure, and enforce a policy of never writing passwords on sticky notes or exposed documents.
Authority sources and reference materials
Rely on trusted sources to guide your credential practices. For security-conscious organizations, consult authoritative guidance from trusted institutions and vendor documentation. This section collects external references you can browse for deeper understanding and policy alignment. For example, national cybersecurity agencies emphasize strong authentication, layered access controls, and routine password hygiene as part of a defense-in-depth strategy. Always cross-check Cisco’s official product manuals for device-specific steps and limitations when performing login or recovery operations.
Troubleshooting login issues
If you encounter login failures, verify the device is reachable on the correct network path, confirm you are using the right username, and check whether your account is active and not locked out. Review access control lists and AAA configuration to ensure your credentials are authorized for the requested operations. If you suspect credential corruption or misconfiguration, re-check the device’s authentication method (local vs. remote) and compare it against the documented baseline. When in doubt, pause to confirm authorization and consult the latest vendor documentation before attempting risky changes.
Tools & Materials
- Laptop or workstation with terminal emulation(Needed for console or SSH access; ensure SSH client is installed)
- Console cable (RJ-45 to DB-9 or USB-to-serial adaptor)(Used for direct device access during initial setup or password recovery)
- Network cable or reliable network path(Required for SSH/Telnet access; ensure network reachability)
- Password manager or secure notes(Storing credentials securely is best practice; avoid plaintext storage)
- Vendor device documentation(Model-specific steps and recovery procedures are device dependent)
- Backup of current device configuration(Useful before making changes or performing password resets)
- Authorized access confirmation(Documentation or ticket showing you have permission to access)
Steps
Estimated time: 45-90 minutes
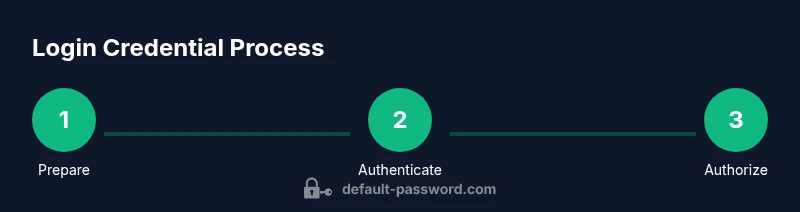
- 1
Verify authorization and prepare
Before touching any device, confirm you have written permission to access and modify credentials. Gather the device model, interface (console, SSH, or GUI), and the current maintenance window. Document the device serial or hostname and have the vendor manual handy.
Tip: Having a signed access request reduces risk of policy violations and speeds up recovery if needed. - 2
Choose the appropriate access method
Decide whether you’ll use the console for direct CLI, SSH for remote management, or the GUI if supported. Each method has different prerequisites, so ensure the device supports the chosen path and that your workstation can reach the device securely.
Tip: SSH is preferred for remote access due to encryption; avoid Telnet when possible. - 3
Establish a connection to the device
Connect the console cable or initiate an SSH session to the device. Open your terminal emulator with the correct settings, then wait for the login prompt. If using console, ensure the device is powered on and the port is active.
Tip: For console connections, verify baud rate and parity match the device’s default or configured values. - 4
Enter credentials and verify access
At the prompt, enter the cisco login username and password or a local account. If authentication succeeds, verify your access level and confirm you can run basic diagnostic commands without impacting the device.
Tip: If you cannot login, check for account lockouts, incorrect domain context, or disabled accounts. - 5
Perform password change or reset as needed
If you are authenticated and have permission, update the password to a strong, unique value. If credentials are unknown or default, follow the vendor’s password recovery procedure and document the change. Ensure that all changes are recorded for audit purposes.
Tip: Use a password generator for complexity and store the result securely. - 6
Apply best-practice access controls
After login, enable or verify AAA, assign roles, and limit user permissions to the minimum necessary. Disable any unused accounts and remove shared credentials from the device. Enable logging to capture authentication events.
Tip: Regularly review user accounts and remove stale entries. - 7
Validate post-change configuration
Run a quick config sanity check to ensure the password change did not disrupt services. Save the running configuration to ensure changes persist after a reboot, and test access from the same and alternate methods.
Tip: Always back up config before and after changes to track modifications. - 8
Document and close the task
Record what was changed, who performed it, and the time. Update the asset registry and notify stakeholders. If a password recovery was necessary, attach the procedure reference for future audits.
Tip: Keep an auditable trail to support incident response and compliance.
Your Questions Answered
What is the default login username for Cisco devices?
There is no universal default username across all Cisco devices. It depends on the device model and software version. Always check the vendor’s official documentation for your specific model before attempting login.
The default username varies by device and version, so consult the vendor docs for your exact model.
How do I reset the Cisco login password without losing configuration?
Many Cisco devices support password recovery that preserves configuration, but the exact steps are device-specific. Refer to the official Cisco manual for password recovery on your model and follow the recommended sequence under authorized access.
Password recovery on many devices preserves configs, but follow model-specific vendor steps with authorization.
Can I use a web GUI to login to Cisco devices?
Some Cisco models offer a web-based GUI for login and configuration, while others require CLI access. Check your device’s capabilities and enable the GUI only if supported and secure.
Some devices have a GUI for login; others require CLI—verify model capabilities.
Is SSH safer than Telnet for Cisco device access?
Yes. SSH encrypts credentials and session data, making it the preferred remote access method. Disable Telnet if possible and ensure SSH is configured with strong keys and access controls.
SSH is safer than Telnet because it encrypts traffic; use SSH and disable Telnet.
What should I do after gaining access to a Cisco device?
Change passwords, verify access controls, enable logging, and document changes. Ensure AAA is properly configured and that only authorized users have access.
After login, change credentials, review access controls, and log changes.
How often should Cisco device passwords be rotated?
Rotate passwords according to your organization's security policy and regulatory requirements. Establish a schedule and document exceptions or special cases.
Follow your security policy for rotation frequency and document exceptions.
Watch Video
Key Takeaways
- Verify authorization before attempting login changes
- Prefer console or SSH over insecure protocols
- Rotate and store passwords securely
- Use AAA and least-privilege access
- Document every credential change