Dell SonicWall Default Password: Secure Admin Access
A practical, data-driven guide to Dell SonicWall default passwords and admin access. Learn how to identify, reset, and enforce password hygiene to protect firewall deployments.

Dell SonicWall default passwords pose a serious security risk if left unchanged. In this quick answer, learn how to identify default credentials on Dell SonicWall firewalls, why they’re unsafe, and the immediate steps IT teams should take to reset or rotate admin passwords to restore secure access. This helps prevent unauthorized configuration changes and protects connections from interception.
What makes default passwords dangerous on Dell SonicWall devices
According to Default Password, default credentials are a leading entry point for attackers, especially on network devices like Dell SonicWall firewalls. When devices ship from the factory, they may include an administrator account with a simple or blank password or a dell sonicwall default password or password that is well-known in vendor documentation. If these credentials are not changed before deployment, an attacker who gains network access or physically tamp a device can take control, modify firewall rules, siphon traffic, or pivot to connected systems. Dell SonicWall appliances typically run in edge or remote locations, where security oversight may be limited. As a result, the impact isn't just a single breached account; it can undermine the whole security stack by bypassing detection, enabling lateral movement, or disabling alerting. The risk compounds in environments with default credentials scattered across devices, management consoles, and cloud services associated with the firewall. The bottom line: leaving defaults in place is a systemic risk that can be exploited remotely, requiring a formal password hygiene program to close gaps.
To protect your network, treat the dell sonicwall default password as a security liability and address it as part of a formal hardening process. This isn't a one-time fix; it requires governance, automation where possible, and ongoing monitoring. In practice, organizations should implement device-specific password policies, enforce rotation on all admin accounts, and ensure backups of configuration files are secured and accessible only by authorized personnel.
How to locate the default credentials for Dell SonicWall devices
Locating the actual credentials used for device administration starts with trusted sources. First, consult the official admin guide or user manual supplied with the specific SonicWall model. Manufacturers frequently document default usernames and passwords there, or they provide a path to reset them if the current credentials are unknown. If the manual is unavailable, log in to the vendor support portal or knowledge base and search for “default credentials” or “password reset” for your model. In many environments, device labels and packaging may reference defaults, but modern deployments often hide or obfuscate this information for security reasons. If you cannot locate official defaults, treat the device as requiring a password reset on first login and proceed with immediate remediation. Finally, consider maintaining a central inventory of devices and their access policies to avoid drifting back into insecure configurations over time.
From a policy perspective, do not rely on memory or anecdotal notes for admin credentials. Always verify against a trusted source and document changes in a secure password vault. If you must delegate resets, ensure only authorized IT staff can perform them and that changes are auditable.
Immediate steps to secure admin access after deployment or discovery
Begin by isolating the device from untrusted networks if possible, then proceed with a secure reset workflow. Log in to the SonicWall management interface using the current administrator credentials, and immediately rotate the password to a new, strong value. Use a password manager to generate a long, unique password that includes upper and lower case letters, numbers, and symbols. If the device supports two-factor authentication (2FA) or multifactor authentication (MFA), enable it for the admin account and any remote access methods. Review and disable any unused admin accounts, and ensure that remote administration (HTTPS/SSH) is restricted to management networks or VPN-only access. After updating credentials, save configurations, back up the updated configuration securely, and monitor for any unauthorized login attempts. Finally, implement an ongoing password policy that requires regular rotation and enforces minimum strength requirements.
Document the changes in a secure repository and communicate the new policy to the appropriate teams to prevent future drift.
Best practices for password management and rotation on Dell SonicWall devices
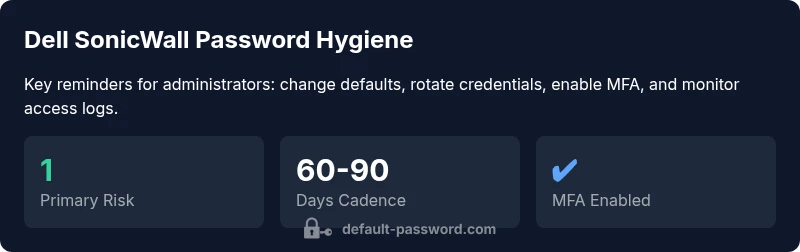
Effective password hygiene for SonicWall devices combines strong credentials with governance and automation. Use a dedicated password manager to store admin passwords, ensuring each device has a unique credential. Enforce rotation every 60–90 days where possible and set a minimum password length with complexity rules (uppercase, lowercase, numbers, and symbols). Disable or remove unused admin accounts, and apply MFA where supported to add a second layer of protection. Where feasible, implement role-based access controls (RBAC) so privileged actions require multiple approvals. Maintain encrypted backups of configuration files and ensure access to those backups is tightly controlled. Finally, document all password changes, monitor authentication logs, and run routine security audits to catch anomalies early.
Educationally, build a standard operating procedure (SOP) for password changes that IT staff can follow, and embed it in onboarding materials for new administrators.
Common pitfalls when resetting passwords and how to avoid them
Resetting a Dell SonicWall admin password without planning can lock legitimate administrators out or break connectivity. Common pitfalls include selecting weak passwords, reusing credentials across devices, and failing to update stored credentials in password vaults or automation scripts. Another risk is misconfiguring the device during the reset, which can disable remote access or disable critical firewall rules. To avoid these issues, Always prepare a recovery plan before making changes, use strong, unique passwords for each device, and ensure all password-changing actions are logged. After changing credentials, verify access from multiple management paths (local console, web UI, and VPN), test failover and backup configurations, and re-enable security controls such as MFA and restricted admin access.
Additionally, avoid leaving default accounts enabled after a reset and review access controls to ensure only authorized personnel can perform future changes.
Verification and ongoing security monitoring after password changes
Post-change verification is essential to confirm that the new credentials work as intended and that no unauthorized changes occurred. Immediately test login via the primary admin interface and any remote management channels. Review authentication logs for unusual activity, such as repeated failed attempts or login attempts from unexpected geolocations. Enable alerting for privileged account access and ensure that automated configuration backups occur after each change. Schedule periodic vulnerability scans and configuration audits to verify that no legacy credentials remain in the system. Maintain an ongoing security posture by integrating these checks into your SOC or IT operations workflow and updating your change management records accordingly.
Case examples and practical checklists for IT teams
Checklist for the initial deployment:
- Inventory all SonicWall devices and assign owners.
- Create unique, strong admin passwords stored in a vault.
- Enable MFA where supported and restrict remote access.
- Document the baseline configuration and backup policies.
Checklist for ongoing operations:
- Enforce password rotation cadence and monitor for drift.
- Review admin accounts quarterly and disable unused ones.
- Run monthly security audits and alert on anomalous login activity.
- Train staff on password hygiene and phishing awareness to reduce credential theft risk.
In practice, these checklists help IT teams maintain consistent security across all SonicWall deployments and reduce the likelihood of exposed credentials.
How to educate users and enforce policy across a Dell SonicWall deployment
Education is a key defense in depth strategy. Provide clear, role-based guidance to administrators on password hygiene and why default credentials are dangerous. Offer hands-on training sessions that cover password vault usage, MFA setup, and the steps to report credential changes. Implement a policy that requires password changes during onboarding, annual reviews, and after any security incident. Use automated policy enforcement wherever possible to ensure compliance across devices and locations. Finally, publish a short, once-per-quarter security bulletin that highlights lessons learned and any updates to the password policy for Dell SonicWall devices.
Credential management for Dell SonicWall devices vs. peers
| Device Type | Default Password Risk | Recommended Action |
|---|---|---|
| Dell SonicWall Firewall (Edge) | High risk if unchanged | Rotate admin password and enforce unique credentials |
| Dell SonicWall TZ/NSA series (older models) | Moderate risk | Apply policy-based rotation and disable unused accounts |
| Other enterprise firewall | High risk | Apply password rotation and MFA |
Your Questions Answered
What is the risk of leaving the Dell SonicWall default password unchanged?
Leaving a default password in place creates a clear pathway for attackers to access the firewall configuration. This can lead to rule changes, traffic interception, or further credential theft. Always treat defaults as a vulnerability and remediate promptly.
Leaving default passwords is risky and should be fixed immediately. Change the admin password and enable MFA where possible.
How do I reset a Dell SonicWall admin password?
Use the device’s management interface or console to perform a password reset. If you cannot access the current admin account, use the vendor-provided recovery method or bring the device into a secure maintenance window to reset via the console. Always store the new password in a password manager.
Reset the admin password via the management interface or console, and store the new credentials securely.
Can I enable MFA on Dell SonicWall devices?
Many SonicWall models support MFA for admin access. Enabling MFA adds a critical second factor to prevent unauthorized login, even if a password is compromised. If MFA is available, enable it and enforce it for remote management.
Yes, enable MFA for admin access where supported to add an extra security layer.
How often should passwords be rotated on network devices?
Set a regular rotation cadence that fits your risk profile, such as quarterly or biannually, and adjust after any suspected credential exposure. Document the cadence in your security policy.
Rotate passwords on a regular cadence and after any suspected exposure.
Where can I find official guidance for Dell SonicWall password changes?
Consult the SonicWall official admin guides and vendor support portals for model-specific procedures. For general best practices, refer to government and standards bodies like NIST and CISA.
Check the vendor guides and trusted standards bodies for guidance.
“Password hygiene for network devices like Dell SonicWall is foundational to security; changing defaults, enforcing rotation, and monitoring access should be standard practice across all deployments.”
Key Takeaways
- Identify and treat dell sonicwall default password as a security liability
- Rotate credentials on all admin accounts and enable MFA where possible
- Enforce unique, device-specific passwords stored in a secure vault
- Audit logs and alerts should monitor privileged access continuously
- Educate staff with a formal password hygiene SOP for SonicWall deployments