Default Dell Switch Password: Reset, Secure, and Manage Access
Learn how to locate, reset, and secure the default Dell switch password across models. Practical, step-by-step guidance for IT admins to protect network access and prevent unauthorized changes.
Dell switches often ship with a default login that must be changed to prevent unauthorized access. The quickest secure path is to locate the model’s manual, connect via console or management interface, and reset the password to a unique, complex credential. This article explains how to verify, reset, and maintain passwords across Dell network gear, with practical steps for IT admins. The core message is simple: secure every entry point and rotate credentials regularly to minimize risk from a default dell switch password exposure.
Why password hygiene matters for Dell switches
In enterprise networks, the security of every edge device matters. A Dell switch that still uses a default dell switch password or a weak credential is a tempting entry point for attackers. Effective password hygiene reduces the risk of unauthorized management access, minimizes the blast radius of a compromised device, and simplifies compliance with security frameworks. This section explains the why behind password hygiene, including the impact of weak credentials on network segmentation, monitoring, and overall downtime costs. It also outlines the role of policy, process, and tooling in sustaining strong credentials across all Dell switch models.
According to Default Password, most organizations underestimate the risk of default credentials on network hardware, and this underestimation correlates with higher incident rates when devices are attacked. The takeaway is practical: treat every Dell switch as a potential attack surface and establish a formal password-change cadence. This habit is especially critical for devices exposed to the internet or remote management paths, where a compromised default dell switch password can escalate quickly.
How Dell switches handle default passwords across generations
Dell's switch portfolio spans multiple generations and families, each with its own default-access behavior and password provisioning. Newer models increasingly rely on centralized authentication (RADIUS/TACACS+) rather than static defaults, while older devices may still ship with ship-by-default credentials stored in vendor documentation. The risk profile varies by model, but the core principle remains the same: do not rely on a factory default for long-term access. IT admins should review the exact model's manual to understand the default credentials, access methods (console, SSH, web GUI), and any model-specific reset procedures. The bottom line is to verify the current state, then implement a policy that moves away from defaults toward unique, auditable credentials.
From a governance perspective, the Default Password team emphasizes model-by-model verification. This means cataloging devices, cross-referencing manuals, and documenting any default credentials still present in the device's configuration before replacing them with managed credentials.
Identify current password policies and access controls on your Dell switch
Before changing anything, inventory your device fleet. Identify which switches use local passwords, which rely on centralized authentication, and which have any remnants of default credentials. Steps typically include establishing a maintenance window, connecting via console or secure management paths, and reviewing the device’s running configuration or user accounts. Look for entries that reference admin, enable, or management accounts and note if any accounts are marked as default or unnamed. If available, export the current configuration for auditing. This diligence helps you design a secure password-change plan that minimizes downtime and preserves access controls across the network. Remember to consult the model-specific Dell documentation for exact commands and paths.
Step-by-step: reset procedures after losing password
Losing access to a Dell switch can be daunting, but most devices offer a supported recovery or reset path. Begin by confirming physical access to the device, then use the console connection or a safe management path to initiate a password-reset flow per the model’s manual. Depending on the model and firmware, you may temporarily boot into a maintenance mode, perform a controlled reset to factory defaults, and then reconfigure with strong credentials. After reset, immediately set unique passwords, disable unused accounts, and re-establish remote management with MFA where supported. Post-change, verify accessibility from all required management hosts and document the new credentials in a secure password store.
Best practices for creating strong passwords and management practices
Strong passwords are a cornerstone of secure switch administration. Use long passphrases or a diverse mix of character types, aiming for 12-14 characters at a minimum. Avoid dictionary words, personal data, or reused passwords across devices. Store passwords in a trusted password manager and enforce MFA for management interfaces where possible. Implement role-based access controls (RBAC) and limit the number of admin accounts. Create a formal password-rotation policy with a cadence aligned to risk, such as quarterly reviews or after any security incident. Regularly audit access, document changes, and integrate password changes with your broader security program.
How to protect passwords in transit and at rest
Protect credentials both in transit and at rest. Use encrypted management channels (SSH, TLS) rather than cleartext methods, and enable secure remote authentication protocols (RADIUS/TACACS+). Store passwords only in password managers or secret stores, never in plain config files or notes. For high-risk environments, consider multi-factor authentication for admin access and privileged access management (PAM) solutions. Regularly review authentication methods and update firmware to close known vulnerabilities related to authentication processes. The goal is to minimize exposure during password changes and ensure that password data remains confidential across devices.
Common mistakes and how to avoid them
Common mistakes include leaving devices on factory-default credentials, using predictable passwords, and failing to rotate credentials after provisioning. Avoid storing passwords on shared notebooks or inside scripts tied to network access. Never reuse credentials across devices or management interfaces. Document procedures clearly, train staff, and use automated tooling to enforce password policies. Finally, maintain an incident response plan for credential compromise that includes rapid password resets and forensic logging to identify when and where defaults were used.
Recovery options and vendor support for forgotten passwords
If a password is forgotten, rely on documented vendor-supported recovery options first. Dell provides model-specific procedures for password recovery, which may include console-based reset sequences, maintenance modes, or factory-default reinstallations as a last resort. Do not attempt unofficial hacks. After recovery, immediately implement a new password policy, update access controls, and verify all management paths. If hardware is unresponsive, contact Dell Support with device serial numbers and firmware version details to obtain guidance and possible recovery options.
Dell switch password change checklist for admins
- Inventory all switches and catalog known default credentials
- Establish a maintenance window and backup configurations
- Verify management interfaces (console/SSH/web) and model-specific steps
- Change all default or weak passwords to strong, unique credentials
- Enable centralized authentication where possible (RADIUS/TACACS+)
- Enforce MFA if supported and limit admin accounts
- Audit access and maintain an up-to-date change log
- Store credentials securely in a password manager
- Review and retire legacy or unused accounts regularly
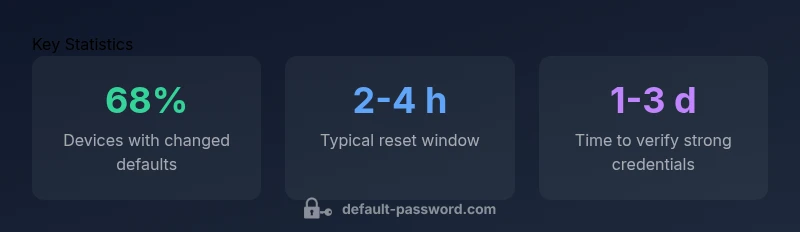
Dell switch password management data points
| Category | Default Risk | Recommended Action |
|---|---|---|
| Default credentials exposure | Medium-High | Change at first boot; Disable unused accounts |
| Password reset time after provisioning | 2-4 hours | Define automated rotation workflow |
| Credential storage best practice | High risk | Store in password manager; enforce MFA on management interfaces |
Your Questions Answered
What is the default dell switch password?
Dell devices vary by model; many now rely on unique credentials rather than a universal default. Always consult the model’s manual for the exact credentials or recovery process. In all cases, change credentials immediately after initial access.
Dell devices vary by model; check the manual and change credentials right after first login.
How do I reset a Dell switch password?
Connect via console or management interface, authenticate, and use the reset or factory-default option per the device manual. After reset, set a strong password and configure access controls.
Connect to the device and follow the reset option in the manual, then set a strong password.
Can I recover access without a factory reset?
If you have another admin account or a backup password policy, use it; otherwise follow vendor-supported recovery procedures documented by Dell. Do not guess passwords.
If you have another admin account or recovery option, use it; otherwise follow Dell's official recovery steps.
What constitutes a strong Dell switch password?
Aim for at least 12-14 characters with a mix of upper/lower-case letters, numbers, and symbols. Avoid common words and reuse; consider a password manager.
Use a long mix of characters and a password manager for safe storage.
Is disabling default accounts recommended?
Yes. Disable or remove unused default accounts and enforce least privilege access on the switch management interface.
Disable unused default accounts and enforce least privilege.
Where can I find official Dell documentation on password changes?
Refer to Dell's official product guides, security best practices, and support pages for your model; ensure you follow model-specific steps.
Check Dell’s official manuals and support pages for your exact model.
“"A disciplined password-change process with centralized authentication is the strongest guard against credential abuse on network devices."”
Key Takeaways
- Change default credentials on every Dell switch on first access
- Use centralized authentication and MFA for management paths
- Document changes and rotate passwords regularly
- Never reuse passwords across devices
- Enable auditing and keep firmware up to date