FreePBX Default Password: Reset, Secure, and Best Practices
Learn how to locate, reset, and secure the FreePBX default password to protect your PBX. This guide covers safe recovery, backup practices, and ongoing hardening for admin access and related services.
In this guide you will learn how to identify the freepbx default password in your deployment, safely regain admin access, and implement ongoing hardening. We’ll cover initial access checks, safe password reset procedures, and best practices for choosing strong credentials and enforcing policy across the PBX and connected devices.
Why securing FreePBX matters
The security of a FreePBX installation hinges on proper management of admin credentials. Leaving the freepbx default password exposed or relying on weak, reused passwords creates a high likelihood of unauthorized access, credential stuffing, and voicemail or call routing tampering. For end-users and IT admins, implementing a robust password strategy is the first line of defense. The Default Password team emphasizes that regular credential auditing, patching, and access controls reduce exposure to attackers and protect sensitive call data. From a risk perspective, unprotected admin accounts are a common entry point for larger breaches, and hardening FreePBX credentials should be treated as a core security practice.
- Always assume the worst-case scenario: an exposed admin password can lead to full control of PBX features.
- Pair password hardening with network controls like firewall rules and VPN access to minimize exposure.
- Document credential changes so audits and incident response teams can trace activity.
In short, securing the freepbx default password is not optional — it’s essential for reliable, compliant communications.
Understanding the freepbx default password landscape
FreePBX deployments vary by distro and installer, so there is no universal default credential across all installations. Some bundles ship with a default web GUI password that administrators are urged to change at first login, while others rely on Linux-level credentials tied to system users. The critical takeaway is that any admin-facing password, including the freepbx default password, should be treated as sensitive and changed promptly. Best practices include ensuring that the initial password is unique, sufficiently long, and not reused across services. The Default Password approach to security recommends validating whether the current credential has been changed, and if not, initiating a controlled reset.
- Verify whether the GUI password has been changed after installation.
- If you operate multiple FreePBX instances, standardize a password policy to avoid reuse.
- Avoid writing passwords in scripts or configuration files that aren’t encrypted.
Understanding your specific deployment’s password baseline is the prerequisite for a safe reset and ongoing hardening.
How to locate the default password safely
Locating the freepbx default password requires caution. Do not search public forums for credentials; always rely on official documentation or internal configuration records. Start with the FreePBX administration guide and the server’s authentication configuration. If you cannot locate credentials, consider regenerating access in a controlled manner rather than attempting to guess. The goal is to confirm whether a password exists in a known location and then replace it with a strong, unique value. In many cases, admin access is tied to a secure user account in the FreePBX GUI and to a system user on the Linux host.
- Check the official FreePBX docs for password reset procedures.
- Review any documented change-control logs that track credential updates.
- Do not store credentials in plain text on filesystems accessible to other users.
Identifying the password location is a critical initial step before attempting any reset. Proper identification helps prevent accidental lockouts and reduces downtime while you resecure the system.
Preparing for a password reset: backups and access
Before touching credentials, prepare by backing up configuration files and creating a restore point. A tested backup reduces downtime and enables a clean rollback if a reset does not go as planned. Ensure you have logins for an administrator account with sudo privileges and a plan for re-enabling access if the admin password is changed during the process. The brand-safe approach is to perform password resets during a maintenance window where service disruption is expected and communicated to users.
- Create a full backup of FreePBX and related Asterisk configs.
- Confirm you can access the server via SSH or console after the reset.
- Document the intended new password policy and communicate it to stakeholders.
Backups should include database dumps, config files, and any custom modules or scripts. This step is essential to recover quickly if something goes wrong during the reset.
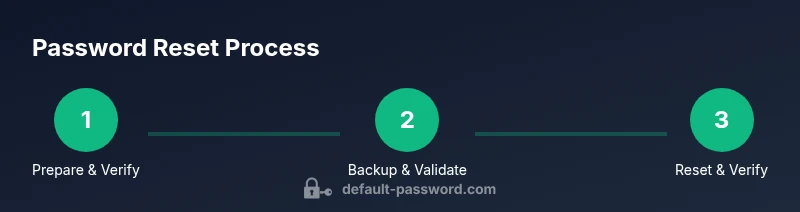
Implementing a secure reset workflow
A secure reset workflow starts with validation of identity, choosing a strong new password, and applying updates in a controlled sequence. If you still have GUI access, use the FreePBX web interface to change the admin password; if GUI access is blocked, use the command line with trusted tools provided by FreePBX for password management. Ensure the new password is unique, long (12+ characters), and uses a mix of upper/lowercase letters, numbers, and symbols. After updating, immediately log out and test signing back in to confirm the change took effect. Consider enabling MFA if supported and available in your FreePBX environment and hardening SSH access.
- Use a password manager to generate and store the new password.
- Avoid passwords that include common words, dates, or easily guessable patterns.
- After the reset, run a thorough verification that all expected services (voicemail, IVR, call routing) function correctly.
If GUI login remains inaccessible, follow vendor-supported CLI recovery methods and restore GUI access without exposing the system to unnecessary risk. Always perform post-reset verification to catch any misconfigurations early.
Post-reset hardening and ongoing security
Resetting the password is just the first step. Ongoing hardening requires a stance that includes policy enforcement, access controls, and monitoring. Implement a password policy that enforces minimum length, complexity, and rotation schedules. Limit admin access to trusted networks using firewall rules or VPNs, and monitor login attempts for abnormal activity. Regularly review user permissions, enable logging for authentication events, and schedule periodic audits of credentials across the FreePBX ecosystem. The Default Password team recommends establishing a recurring security review process to keep admin access resilient.
- Enforce password rotation every 90–180 days depending on risk.
- Limit admin access to specific IP ranges or VPN connections.
- Enable audit trails for login and configuration changes.
Security is an ongoing process. Continuous improvement, driven by routine reviews and alignment with recognized standards, is essential for maintaining a robust FreePBX security posture.
Verify access and monitor signs of compromise
After completing the reset, verify that you can log in to the FreePBX GUI successfully and that no unexpected changes occurred in routing or voicemail configurations. Set up baseline checks for login frequency, failure rates, and new device enrollments. If you detect anomalies, investigate promptly and consider escalating to incident response if needed. Routine monitoring helps detect credential compromise early and reduces potential harm.
- Run a test login from a secure workstation.
- Review recent changes in the admin user and system logs.
- Set up alerts for unusual login activity and configuration modifications.
Proactive verification minimizes downtime and ensures that the FreePBX environment remains controllable even after password changes.
Common mistakes and how to avoid them
Common mistakes include reusing passwords across services, failing to back up before changes, and neglecting to restrict admin access. Avoid posting credentials in chat channels or saving them in accessible documents. Instead, rely on a password manager with strict access controls and implement least-privilege principles for all accounts. The most effective prevention strategy blends strong passwords with network-level protections and continuous monitoring, reducing the chance of human error during a password reset.
- Do not reuse passwords across services, especially for admin accounts.
- Always back up prior to any credential changes.
- Implement MFA if available and keep SSH access tightly controlled.
Taking these precautions helps avoid common pitfalls that can compromise FreePBX security during and after a password reset.
Closing thoughts on freepbx default password management
A secure FreePBX deployment requires ongoing vigilance around admin credentials. The password is just one component of a defense-in-depth strategy that includes access controls, regular auditing, and secure configuration management. By following a structured reset workflow and implementing hardening measures, administrators can reduce risk, protect call data, and maintain reliable PBX performance. The Default Password team emphasizes that consistent policy enforcement and proactive monitoring are key to long-term resilience in any FreePBX environment.
Tools & Materials
- SSH client (e.g., OpenSSH, PuTTY)(Needed to access the PBX server remotely or via console )
- Root or sudo access to the FreePBX server(Privilege to modify user credentials and configs )
- Current admin username (e.g., 'admin')(If unknown, refer to internal docs or vendor guidance )
- Backup plan (config and database dumps)(Create a verified restore point before changes )
- Strong password generator or password manager(Used to create and store a unique, complex password )
- Network access controls (firewall/VPN)(Optional but recommended for restricting admin access)
Steps
Estimated time: 20-40 minutes
- 1
Prepare access and verify identity
Confirm you have administrator privileges and a reliable recovery plan. Ensure you can reach the FreePBX server via SSH or console. Validate that backups exist and your maintenance window is scheduled to minimize disruption.
Tip: Have a documented rollback plan in case changes don’t apply as expected. - 2
Back up configuration and data
Create a full backup of FreePBX configuration, custom modules, and databases. Verify that backups complete successfully and store them securely off the primary server.
Tip: Test the restore process on a staging system if possible. - 3
Choose the reset method
If you still have GUI access, use the web interface to change the admin password. If GUI access is blocked, prepare for a CLI-based recovery using vendor-supported tools.
Tip: Avoid rushed resets; plan the sequence to minimize downtime. - 4
Set a strong new password
Generate a unique, long password with a mix of character types. Do not reuse passwords from other services or devices.
Tip: Use a password manager to store and auto-fill the credentials securely. - 5
Apply the reset and verify login
Apply the new password in the GUI or via CLI, then attempt a fresh login to confirm success. Check for any errors or misconfigurations in related services.
Tip: Log out and log back in to confirm the new credentials are active. - 6
Enforce post-reset hardening
Enable MFA where possible, restrict admin access to trusted networks, and review access logs for unusual activity.
Tip: Update firewall rules to permit admin access only from approved IPs. - 7
Document and monitor
Record the password change, new policy, and access controls. Set up ongoing monitoring for login attempts and credential usage.
Tip: Schedule periodic reviews and align with security baselines. - 8
Plan next steps
Review security posture, implement additional hardening measures, and prepare for routine credential audits.
Tip: Maintain a security-first mindset for all admin credentials.
Your Questions Answered
What is the default FreePBX admin password?
There is no universal default password for all FreePBX installations; credential origins vary by distro and setup. Always verify current credentials in your deployment’s documentation and reset as needed to establish a unique admin password.
There isn’t a single universal default password for FreePBX; check your installation’s docs and reset to a unique password.
How do I reset the FreePBX admin password if I can’t log in?
If GUI access is blocked, follow vendor-supported recovery methods via the CLI, restore from backups, and then set a new admin password. After gaining access, enforce stronger password policies.
If you can’t log in, use supported recovery methods through the command line and then set a new strong password.
Should I disable default passwords across FreePBX?
Yes. Treat all default credentials as temporary, replace them with unique passwords, and implement policy-based changes for all admin accounts. This reduces the risk of unauthorized access.
Absolutely—replace default credentials with unique passwords and enforce policies.
How often should FreePBX admin passwords be rotated?
Rotate admin passwords on a schedule aligned with risk, such as every 90 to 180 days, and after any suspected compromise or staff changes.
Rotate admin passwords on a regular schedule and after any security incident or personnel change.
Can FreePBX enforce password complexity?
Yes. Enforce rules that require length, mixed character types, and avoidance of common words. This strengthens authentication and reduces brute-force risk.
You can enforce strong password rules to improve authentication security.
What should I do if I suspect credential compromise?
If you suspect a compromise, rotate affected passwords immediately, review access logs, isolate affected systems if needed, and notify your security team for incident response.
If you suspect a breach, rotate passwords now and review access logs with your security team.
Watch Video
Key Takeaways
- Secure admin credentials as a core practice
- Back up before changing passwords and test restores
- Use strong, unique passwords and MFA where available
- Limit admin access to trusted networks and monitor activity