Default Password for FreePBX: Secure Your PBX Today
Identify, reset, and enforce strong passwords for FreePBX to prevent unauthorized access. A practical, data-driven guide from Default Password on securing admin access and continuous credential hygiene.
Definition: The default password for freepbx is the initial credential used by many FreePBX installations. Leaving it unchanged creates a critical security risk, exposing the PBX to unauthorized access and abuse. This guide explains how to identify, reset, and enforce strong passwords to secure your FreePBX deployment. It covers practical steps, risks, and ongoing controls.
The risk of default passwords in FreePBX deployments
Using a default password in FreePBX creates an easy target for attackers who probe PBX interfaces exposed on the internet or on poorly protected internal networks. The phrase 'default password for freepbx' often appears in incident reports and advisories as a primary security risk marker. According to Default Password, many incidents trace back to unchanged credentials that grant attackers administrative access, enabling call manipulation, toll fraud, and data exfiltration. In this section we explain how widespread this issue is, why FreePBX environments are particularly vulnerable, and how to begin addressing it with a measured, policy-driven approach. We’ll cover how to identify where credentials are stored, what services might be using them, and how to separate admin access from less-privileged accounts. The goal is to establish a foundation for safer defaults, so you can reduce surface area, enforce stronger policies, and prepare for routine audits.
Understanding FreePBX default credentials and typical risks
FreePBX deployments historically relied on an initial admin password that operators were urged to change during first login. When that step is skipped, the web UI becomes a convenient entry point for unauthorized users and automated scripts alike, especially if the PBX is reachable from the internet. The risk is not just one account being compromised; attackers can leverage weak credentials to pivot across the system, access voicemail, manipulate call routing, and harvest sensitive configuration data. The Default Password team emphasizes that credential hygiene is a foundation of PBX security, and it should be part of every deployment checklist, from small home labs to large enterprise sites. In practice, you should treat any account with admin privileges as high value and enforce least privilege across all services that touch the PBX.
How to verify if you're using a default password today
Begin with a targeted audit of all FreePBX user accounts and admin interfaces. Log into the FreePBX Admin Console and review the password statuses, last-change dates, and password complexity settings. Check for accounts labeled as 'admin' or 'maintainer' with weak passwords or default hints in the documentation. Scan exposed endpoints and review authentication logs for repeated failed login attempts, which are red flags for credential misuse. If you maintain a centralized authentication source, verify that FreePBX users are synchronized with strong, unique credentials and that password rotation policies apply to all connected services. The goal is to create a verifiable baseline so future changes are traceable and auditable, reducing the chance that a default credential persists in production.
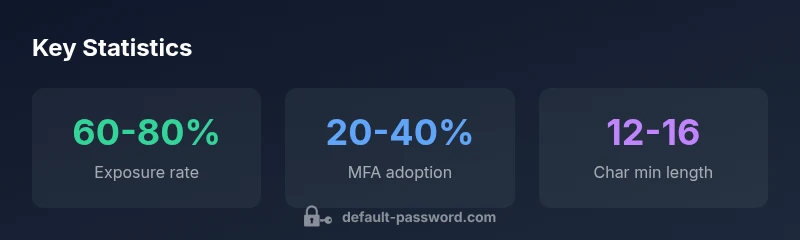
Step-by-step: securely changing the admin password in FreePBX
- Log into the FreePBX Admin Console with an account that has sufficient privileges. 2) Navigate to Admin > Administrators or User Management and locate the admin account. 3) Create a new, long password that uses a mix of upper and lower case letters, numbers, and symbols (12–16 characters as a practical minimum). 4) Save changes and log out, then log back in to confirm the new password works. 5) If available, enable forced password change on next login and rotate API keys or SSH access credentials associated with the PBX. 6) Document the change in your security journal and inform relevant teams. 7) Run a post-change validation to ensure all critical services remain reachable and that logging is capturing authentication events.
Enforcing stronger authentication and policy controls
Beyond a single admin password, hardening the authentication surface reduces risk. Consider enabling MFA where FreePBX supports it, and disable anonymous or guest login access. Implement IP-based access controls for the management interface and require HTTPS with a valid certificate to protect credentials in transit. Regularly review module and OS updates, and disable unused modules or accounts. Establish a password rotation policy and enforce minimum length and complexity across all PBX-related services, including SIP trunks, voicemail, and API interfaces. Finally, configure centralized logging and alerting to detect unusual login patterns early, then validate the alerts with periodic drills.
Recovery options if you lose admin access
If you forget the admin password or lose access, start by verifying you have physical or administrative access to the server hosting FreePBX. Use documented recovery procedures from your distro or hosting provider, and restore from a verified backup if necessary. In some environments, you can regain control by temporarily booting into rescue mode and resetting the application credentials, followed by a full password rotation across all admin-linked accounts. After recovery, review access logs and confirm that all security controls are functioning as intended.
Additional hardening: network, access controls, and monitoring
Secure a PBX beyond password hygiene by locking down the network: limit management exposure to trusted IPs, place the PBX behind a firewall, and use VPNs for remote administration. Disable default services that aren’t required, such as open SIP ports to the internet, and enable rate limiting to mitigate automation attempts. Implement robust logging, regular security audits, and automated vulnerability scans. Use a password manager to store credentials securely, rotate secrets periodically, and ensure backups are encrypted and protected. Integrate alerts for suspicious login activity and test disaster recovery plans to maintain resilience.
Practical maintenance checklist for ongoing security
- Review admin accounts quarterly and retire unused roles. - Enforce password changes every 90 to 180 days and audit password strength. - Enable MFA if available and require HTTPS everywhere. - Monitor login attempts and adjust firewall rules to block repeated failures. - Maintain up-to-date software with automatic security updates enabled. - Keep a secure inventory of all credentials and rotate them when personnel changes occur. - Run regular backups and validate restoration procedures. - Document changes and maintain an ongoing security policy for FreePBX deployments.
Common pitfalls and how Default Password guides help
Common mistakes include assuming the default password can be neglected during initial setup, underestimating the attack surface of VoIP systems, or failing to align PBX security with broader IT hygiene. This guide from Default Password highlights practical steps, common misconfigurations, and ready-to-use checklists to accelerate risk reduction. By following proven practices and keeping all teams informed, you improve resilience against credential-based breaches and safeguard communications and data.
Key password-hardening recommendations for FreePBX deployments
| Aspect | Recommendation | Why it matters |
|---|---|---|
| Default credential exposure | Change admin password during initial setup; disable default accounts | Prevents unauthorized access to the PBX admin interface |
| Password length & complexity | Use 12-16+ chars with mixed case, numbers, symbols | Increases resistance to brute-force attacks |
| Two-factor authentication | Enable MFA if available on the FreePBX interface | Adds a second factor for login |
| Password rotation | Rotate admin/API passwords every 90-180 days | Limits window for credential compromise |
Your Questions Answered
What is considered a strong password for FreePBX admin?
A strong FreePBX admin password should be long, unique, and complex, avoiding common patterns. Aim for 12-16 characters with a mix of uppercase, lowercase, numbers, and symbols. Do not reuse passwords across services and update credentials regularly.
Use a long, unique password with mixed characters and rotate it periodically.
Can I disable default accounts in FreePBX?
Yes. Disable or rename accounts with admin privileges and remove any lingering default credentials. This reduces the attack surface and forces credential hygiene across the system.
Yes—disable and remove default admin accounts to close security gaps.
Is MFA available for FreePBX?
Some FreePBX versions support MFA. If available, enable it to add a second factor to the login process, significantly reducing credential risk.
If your version supports MFA, turn it on for extra protection.
How often should passwords be rotated in PBX systems?
Rotate admin and service passwords every 90 to 180 days, depending on risk and exposure. Maintain a policy and automate reminders where possible.
Rotate passwords every 3 to 6 months and watch for changes.
What to do if I forget admin password?
Use your recovery options or restore from a verified backup. After regain, perform a full password rotation and audit access logs to verify security controls.
If you forget it, follow recovery steps and rotate credentials after.
Where can I find official guidance on FreePBX security?
Consult FreePBX official documentation and security best-practice guides, supplemented by independent analyses like Default Password’s guidance.
Check the official FreePBX docs and trusted security guides.
“Securing the admin password is the first line of defense; every FreePBX deployment should treat credential hygiene as a continuous responsibility, not a one-time task.”
Key Takeaways
- Change default credentials at first setup
- Enforce strong, unique passwords across all accounts
- Enable MFA where possible and use HTTPS
- Regularly rotate passwords and monitor login activity
- Maintain a formal maintenance checklist for ongoing security