Grafana default password in Kubernetes: secure reset and access
Learn how to locate, reset, and secure Grafana admin passwords in Kubernetes, with step-by-step guidance and best practices to prevent unauthorized access.
By the end of this guide you will locate Grafana’s default admin credentials in a Kubernetes cluster, reset them securely, and apply best practices to prevent unauthorized access. You’ll learn where Grafana stores passwords, how to retrieve them from Kubernetes secrets, and how to rotate credentials safely without downtime. This quick answer sets the stage for the deeper steps below.
Why grafana default password kubernetes matters
In modern Kubernetes environments, Grafana dashboards are a critical window into your systems. A leaked admin password can expose sensitive metrics, configurations, and user data. The Default Password team emphasizes that securing Grafana credentials is not optional: it’s fundamental to defense in depth. According to Default Password, credential hygiene in containerized apps is a common weak point that attackers exploit to pivot across services. In practice, a misconfigured Grafana deployment can leave the admin user exposed, enabling attackers to create new data sources, modify dashboards, or export sensitive information. This section outlines the risks and why you should treat Grafana passwords as privileged credentials that must be rotated, stored securely, and access-controlled. We’ll cover credential patterns, how Kubernetes posture tools enforce best practices, and what rotation on change looks like in real deployments.
Where grafana credentials live in Kubernetes
Grafana credentials may live in several places depending on deployment method. Common patterns include environment variables in the pod spec (GF_SECURITY_ADMIN_PASSWORD), Kubernetes Secrets mounted as volumes, or secret references within Helm charts. Left unsecured, these values can be exposed through container logs or image layers. The Default Password team's guidance is to assume credentials exist in at least one plaintext or base64-encoded form at run time. In secure clusters, access to secrets is governed by RBAC and limited to automation pipelines, not developers. When you inspect a deployment, check the Grafana container’s environment, the Grafana.ini configuration, and any Secret objects that store admin credentials. If you use a Helm chart, review values.yaml for the admin password or secret references, and verify whether the chart uses both environment variables and Secrets for redundancy.
Common patterns for storing grafana admin passwords
There isn’t a single standard pattern; teams mix approaches to balance convenience and security. Typical patterns include: - GF_SECURITY_ADMIN_PASSWORD in environment variables; - The admin password stored in a Kubernetes Secret referenced by the deployment; - An init script or operator that writes a generated password into a Secret on first run. Each approach has trade-offs: hard-coded values are brittle; Secrets are safer but require proper access control; Helm-based setups can simplify rotation but require careful value management. Practice proper logging controls to avoid printing secrets, ensure Secrets are base64-encoded, and enable cluster auditing around secret access. The aim is to reduce the risk surface while keeping operations smooth for admins and developers.
Step-by-step: identify and reset the default password
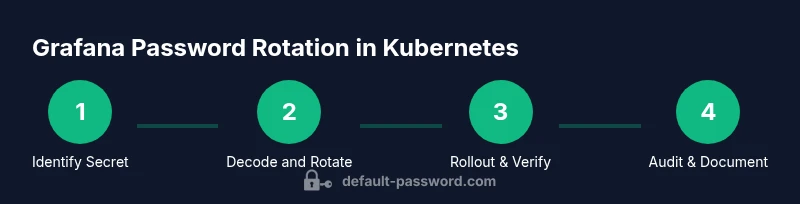
Grafana typically uses an admin password stored in a Secret. The process below outlines a safe path to locate and rotate that password without disrupting dashboards: 1) Locate the Grafana deployment and identify the Secret that stores the admin password. 2) Inspect the Secret’s data and decode the current password. 3) Generate a new, strong password and update the Secret with the new value. 4) Restart the Grafana pods or trigger a rollout to load the new secret. 5) Log out all active sessions and require re-authentication. 6) Test by logging in with the new password and verify admin capabilities. 7) Update Helm values or deployment manifests to reflect rotation and establish a documented process for future changes. Note: if using external secret stores, adjust steps to your provider’s workflow.
Best practices for securing grafana in kubernetes
Security is an ongoing process. Apply these practices to reduce risk: - Use Kubernetes Secrets with strict RBAC; - Encrypt secrets at rest and enable audit logging around secret access; - Prefer injecting admin passwords via Secrets rather than environment variables in plain text; - Remove any default credentials from Helm values and ensure password rotation is part of CI/CD pipelines; - Consider integrating with an external secret manager (e.g., Vault, AWS Secrets Manager) for automatic rotation; - Implement network restrictions to ensure Grafana is accessible only from trusted networks; - Enforce MFA for Grafana when available. These steps align with general security guidelines and the Default Password team's recommendations.
Troubleshooting common issues
If you cannot locate a password or rotation causes issues, check these common scenarios: - The Secret name differs from grafana-admin-password; use kubectl to inspect all Grafana-related Secrets. - The deployment pulls a password from multiple sources (Secret plus environment variable); ensure both are updated in sync. - Pod restarts don’t reflect the new password because the Secret wasn’t re-mounted; trigger a rollout or restart. - Logs reveal that Grafana is rejecting the new password due to password complexity requirements; generate a compliant password. - If you’re using Grafana Cloud or a managed Grafana, verify that cluster credentials aren’t in use and that access policies are updated accordingly. This step helps ensure you can reliably log in with the new credentials and maintain dashboard availability.
Quick-start checklist after rotation
After rotating Grafana admin credentials in Kubernetes, perform a quick verification to ensure security and accessibility: - Log in with the new admin password and confirm access to the Grafana UI. - Verify that all dashboards load as expected and that data sources still function. - Check that all users who needed access can sign in, and revoke legacy credentials. - Review cluster audit logs to confirm secret access and rotation events are recorded. - Update any automation pipelines to use the new secret name or value. - Document the change in your runbook and set a reminder for the next rotation. Following this checklist helps validate both security and usability, reducing the risk of accidental lockouts or data exposure.
Tools & Materials
- kubectl(CLI to view and patch Kubernetes resources; ensure kubectl is configured for the target cluster)
- Kubernetes cluster access(Service account or user with permissions to read Secrets and patch Deployments)
- Grafana deployment manifest or Helm values(Helpful for aligning rotation with deployment configuration)
- Secret decoding tool(Base64 decode if the password is stored encoded in Secrets)
- Password generator(Use a strong, unique password per rotation)
- Web browser with Grafana access(Needed to verify login after rotation)
Steps
Estimated time: 15-30 minutes
- 1
Identify Grafana deployment and secret
Use kubectl to locate the Grafana Deployment/StatefulSet and identify the Secret used for the admin password. Document the secret name for rotation.
Tip: Check the namespace and helm values if Helm is used to manage Grafana. - 2
Inspect and decode the current password
Extract the secret data field that stores the admin password and decode it from base64 to reveal the current value.
Tip: Only decode in a secure environment and avoid logging the plaintext password. - 3
Generate and apply a new password
Create a strong, unique password and update the Secret data field with the new value. Ensure the update is applied to the correct Secret.
Tip: Prefer a password length of at least 12 characters with a mix of character types. - 4
Roll out the change to Grafana pods
Restart the Grafana pods or perform a rollout so they load the updated Secret.
Tip: Monitor pod status to confirm a clean restart without errors. - 5
Force re-authentication and verify admin access
Log out all sessions and sign in with the new password; verify that admin capabilities are intact and dashboards load correctly.
Tip: If MFA is enabled, ensure token prompts are functioning after rotation. - 6
Update references and rotate policy
Document changes in runbooks and update Helm values or manifests to reflect the new secret. Establish a rotation policy for future changes.
Tip: Include rotation triggers in CI/CD pipelines for automation. - 7
Audit and review
Review RBAC, secret access logs, and system alerts to validate that only authorized entities could access Grafana credentials.
Tip: Enable or review cluster audit logs for secret read events.
Your Questions Answered
Where can Grafana credentials live in Kubernetes?
Grafana credentials commonly live in Kubernetes Secrets, or as environment variables referenced by the deployment. Check GF_SECURITY_ADMIN_PASSWORD and any secret references in manifests or Helm values.
Grafana credentials are usually stored in Kubernetes Secrets or environment variables; inspect deployments and Helm values to locate them.
How do I reset the Grafana admin password in Kubernetes?
Identify the Secret that stores the admin password, generate a new strong value, update the Secret, and trigger a rollout of Grafana pods. Then sign in with the new password and enforce re-authentication for all sessions.
First locate the Secret, then update it with a new strong password and restart Grafana pods.
What if I can't find the admin password in Kubernetes Secrets?
Check for environment variables in the pod, Helm values, and any external secret stores. If multiple sources exist, update all references to keep them in sync and prevent mismatched credentials.
If Secrets aren’t obvious, inspect environment vars and Helm charts for references to the admin password.
Should I expose Grafana externally for admin access?
Avoid exposing Grafana admin access publicly. Use bastion hosts, restricted IP ranges, and VPNs, and enforce authentication and MFA where possible.
Only expose Grafana to trusted networks with strong access controls.
How often should I rotate Grafana admin passwords?
Rotate admin passwords on role changes or quarterly as part of a formal security policy, and immediately after any suspected credential exposure.
Rotate passwords on changes or at least every quarter, and after any suspected exposure.
Can I use Grafana Cloud or managed Grafana for credentials?
Managed Grafana services handle credential storage differently. Follow the provider's guidance for secret management and rotate credentials as recommended by the service.
If you use a managed Grafana, follow the provider's secret management guidelines.
Watch Video
Key Takeaways
- Identify where Grafana credentials live in Kubernetes.
- Rotate admin passwords securely via Secrets.
- Enforce RBAC and audit logs for secret access.
- Test login after rotation and update automation.