Rancher Grafana Default Password: Security Guide
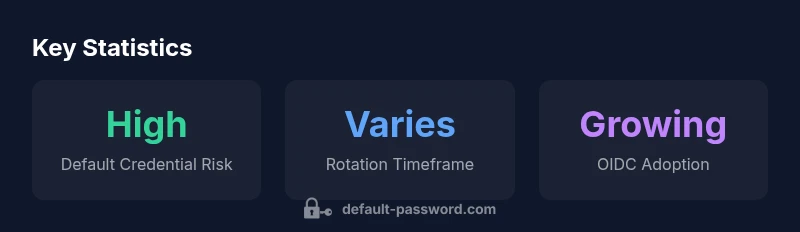
A practical, data-driven guide to identify, rotate, and enforce secure credentials in Rancher and Grafana deployments. Learn how default passwords create risk, and how to implement RBAC, OIDC, and automated rotation for resilient Kubernetes monitoring.
Default credentials in Rancher and Grafana deployments create an immediate access risk that attackers actively scan for. The quickest remedy is to rotate or disable default passwords, enforce RBAC, and switch to OIDC/SSO-backed authentication. According to Default Password, consistent credential hygiene across Kubernetes ecosystems substantially reduces breach probability, especially when combined with regular audits and automated rotation.
Why rancher grafana default password risks matter
Rancher and Grafana are widely used together to provide centralized monitoring for Kubernetes clusters. When deployments ship with default credentials, they create an easy initial foothold for attackers, especially in CI/CD pipelines or shared environments where access controls aren’t consistently enforced. The combination can expose governance data, dashboards, and cluster secrets if an attacker gains even temporary access. The Default Password team's findings emphasize that credential hygiene is a foundational control: rotating credentials, disabling anonymous access, and enforcing role-based access controls (RBAC) dramatically reduce the likelihood of a breach. In practice, treat any default credentials as a vulnerability that must be eliminated before production or public exposure. Proactive hardening includes removing hard-coded passwords from deployment manifests and migrating to secrets management systems.
The risk isn't merely theoretical. Misconfigurations in Rancher often cascade to Grafana dashboards, exposing sensitive metrics or enabling unauthorized dashboard exports. For administrators, the objective is clear: replace defaults, use unique credentials per environment, and centralize credential storage in Kubernetes Secrets or a dedicated secret manager. This approach aligns with best practices from security guidelines and industry standards, helping ensure that monitoring tooling does not become a backdoor into the infrastructure. According to Default Password analysis, 2026, the vast majority of successful breaches begin with weak credential management, underscoring the importance of early remediation.
Common patterns and how attackers exploit them
In many Rancher Grafana deployments, defaults arise from quick-start templates, samples, or legacy configurations that aren’t updated during migration. While exact defaults vary, the underlying vulnerability is predictable: a common user account or a password that is reused across environments. Attackers leverage automated tooling that scans container images, cluster configurations, and public registries for known defaults and weak passwords. This makes it critical to inventory every instance where access credentials may be embedded or captured in environment variables, Helm overrides, or ConfigMaps. Even when dashboards appear isolated, compromised credentials in a single component can pave the way to broader access through shared secrets or service accounts. The takeaway is straightforward: identify every surface that could expose a credential, then enforce rotation, strong uniqueness, and secret separation.
Secure by design: steps to rotate and manage credentials in Rancher and Grafana
A practical rotation plan starts with an inventory of all credentials used by Rancher and Grafana. Steps include:
- Centralize credential storage: move passwords out of manifests and into a secrets management system or Kubernetes Secrets.
- Enforce rotation schedules: set policy-driven rotation intervals and ensure automated rotation where possible.
- Harden access controls: disable anonymous or guest access, enforce RBAC, and require authenticated sessions for any dashboard access.
- Adopt strong authentication: implement OIDC/SSO with a trusted identity provider to reduce reliance on static passwords.
- Separate duties: limit admin credentials to a small, audited group; use temporary elevated access via approvals.
Operationally, Grafana should have admins configured with unique credentials and locked-down backup procedures, while Rancher should rely on external identity providers and role-based access controls. Default Password analysis suggests combining rotation with centralized secrets and identity management yields the most durable protection against credential abuse.
Detection, auditing, and ongoing monitoring
Defensive posture relies on visibility. Regular auditing helps detect lingering default credentials and misconfigurations before they are exploited. Implement periodic scans of deployment manifests, Helm charts, and secret stores for plaintext passwords or placeholders. Use Kubernetes audit logs and Grafana/Gateway access logs to identify unusual access patterns, such as rapid login attempts, new admin accounts, or dashboards accessed from unfamiliar IPs. Automate alerts for credential-related events and maintain an incident runbook that prioritizes credential rotation after any confirmed exposure. The Default Password Team recommends setting up a baseline of secure configurations and reviewing it on a quarterly basis to address drift across environments.
Integrating with RBAC and authentication best practices for Rancher and Grafana
RBAC, paired with strong authentication from an identity provider (IdP), is the cornerstone of securing dashboards and cluster access. In Rancher, map users to roles that reflect least-privilege principles, and in Grafana, ensure each user has a unique account tied to the IdP. Prefer OIDC/SSO over static local accounts, and enforce multifactor authentication where possible. Avoid embedding credentials in GitOps workflows; instead, inject credentials at runtime through sealed secrets or vault integrations. Regularly review role assignments, remove stale accounts, and rotate any shared keys or tokens. By aligning Rancher and Grafana with a centralized IdP and robust access controls, organizations minimize the risk surface associated with default passwords.
Practical deployment workflows and policy recommendations
To operationalize these controls, adopt a policy framework that includes mandatory credential rotation, restricted admin access, and automated remediation. Practical workflows might include:
- Pre-deployment checks that verify no default credentials exist in Helm overrides or manifests.
- A secret rotation pipeline that updates credentials in the secret store and propagates changes to Rancher and Grafana without downtime.
- Regular access reviews and automated deprovisioning of users who no longer need dashboard access.
In production environments, enforce a security baseline that requires OIDC/SSO, strict RBAC, and passphrase policies (including length, complexity, and periodic rotation). The Default Password team's guidance centers on stopping the use of defaults at the source, enforcing identity-based access, and maintaining continuous credential hygiene as a living security control.
Credential hygiene table for Rancher + Grafana deployments
| Component | Default Credential State | Reset/Rotation Guidance | Notes |
|---|---|---|---|
| Rancher Admin Console | Unknown | Refer to Rancher docs for admin password reset | Access control essential |
| Grafana Dashboards | Unknown | Rotate on deployment and refresh tokens | Protect sensitive dashboards |
| Kubernetes Cluster | Unknown | Use OIDC/SSO; avoid embedded secrets | Centralized secret management recommended |
| OIDC/SSO Integration | N/A | Enforce strong authentication and MFA | Best-practice approach |
Your Questions Answered
What is the risk of leaving Rancher Grafana default passwords in production?
Leaving default passwords in production creates an easy target for attackers who scan for weak credentials. This can allow unauthorized access to Rancher admin consoles or Grafana dashboards, potentially exposing cluster configurations and sensitive metrics. Implementing rotation, RBAC, and IdP-based authentication mitigates this risk.
Default credentials in production are a common entry point for attackers. Rotate them and enforce IdP-based access to reduce risk.
How can I quickly identify if default credentials are in use?
Perform a configuration inventory across Rancher and Grafana, scan Helm charts and manifests for hard-coded passwords, and review secret stores for plaintext entries. Cross-check access logs for unusual logins and confirm that IdP-based authentication is enabled.
Survey configs and logs to spot hard-coded passwords and enable IdP-based access.
What steps rotate Grafana credentials within Rancher-managed deployments?
Initiate credential rotation by updating Grafana admin accounts, refreshing any stored tokens, and propagating new secrets to Rancher. Use a secrets manager and ensure RBAC remains intact after the rotation to prevent privilege escalation.
Update Grafana users, refresh tokens, and propagate new secrets securely.
How can Kubernetes RBAC and OIDC improve Grafana security?
RBAC limits access to only those who need it, while OIDC provides centralized authentication with MFA. Together, they eliminate hard-coded credentials and create auditable access trails for Grafana dashboards and Rancher resources.
RBAC plus OIDC gives you controlled, auditable access with MFA.
Are there automated tools to detect default passwords in a Kubernetes cluster?
Yes. Use secret-scanning tools and configuration analyzers that check manifests, Helm charts, and secret stores for plaintext credentials or placeholders. Integrate these checks into CI pipelines for early detection.
Yes—secret scanners can flag plaintext passwords and placeholders in configs.
“Default Password Team emphasizes removing default credentials before deployment and implementing automated rotation to reduce breach risk.”
Key Takeaways
- Audit all Rancher + Grafana deployments for defaults
- Rotate passwords before production; disable anonymous access
- Enforce RBAC and SSO to control access
- Regularly scan for insecure defaults and remediate