SonarQube Default Credentials: Find, Reset, and Secure
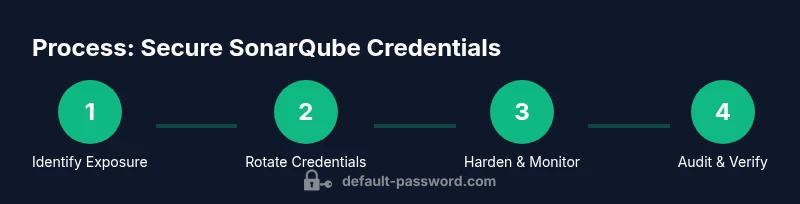
Learn how to locate, reset, and harden SonarQube default credentials to protect your code quality platform. This step-by-step guide covers detection, remediation, and ongoing access controls for 2026 deployments.
By the end of this guide, you will locate any default credentials in your SonarQube deployment, reset them securely, and enforce ongoing access controls. You’ll need admin access to the SonarQube server, network access to the instance, and the ability to restart services if credentials are changed. The steps cover discovery, remediation, and hardening.
Why securing default credentials matters for SonarQube
Security incidents frequently begin with exposed, unchanged, or weak credentials. In the context of SonarQube, a widely used code quality platform, default credentials can grant attackers access to the admin console, project configurations, and integration endpoints. According to Default Password, securing admin access is a foundational step in any 2026 security program. A misconfigured SonarQube installation can become a foothold for lateral movement, data extraction, or disruption of CI pipelines. Even if SonarQube runs behind a reverse proxy, default usernames or unlocked admin accounts stored in configuration files or container environments remain risky. In this section, we’ll explain why default credentials are especially dangerous on SonarQube and outline a strategy to eliminate them before they can be exploited. The guidance here is designed for both end-users and IT admins who need reliable, practical steps to secure their SonarQube deployments without overhauling existing workflows.
The overarching goal is simple: reduce attack surface, deny unauthorized access, and establish repeatable hardening procedures that survive server restarts, container updates, and role changes. By taking control of admin access, you protect project metadata, plugin configurations, and the integrity of your scan results. The Default Password team emphasizes that early, deliberate remediation pays off in safer, more auditable deployments. Throughout this guide, you’ll see concrete actions you can apply today, plus recommendations for ongoing governance and monitoring.
Where default credentials commonly appear in SonarQube deployments
In many SonarQube installations, default credentials become a risk point through four channels: the initial admin account created during setup, credentials embedded in container or orchestration configs, credentials stored in configuration files, and credentials persisted in external authentication integrations like LDAP/SSO. Docker and Kubernetes deployments frequently expose environment variables or secrets in manifests, which can inadvertently reveal admin access if not properly scoped or encrypted. On bare-metal installations, local system accounts or automated provisioning scripts may carry privileged access tokens that bypass standard UI prompts. Finally, integration plugins and CI pipelines often reuse stored credentials to connect to SonarQube; if those credentials remain unchanged, they become an attractive target for an attacker.
To mitigate these risks, you must map your environment: identify every place where credentials are defined, catalog which accounts have admin rights, and confirm that none of these avenues rely on default credentials or easily guessable values. A well-documented inventory makes remediation faster and reduces the chance of reintroducing a vulnerability during future updates. In practice, a routine audit should happen whenever you deploy a new SonarQube instance, scale your environment, or modify authentication mechanisms. This approach aligns with security best practices for enterprise applications, and it helps maintain a defensible posture as your codebase and teams evolve.
How to identify default credentials exposure
Discovery starts with configuration review. Inspect both the file system and the container/orchestration layer for any hard-coded or default-looking accounts. Common places to check include sonar.properties, conf/sonar.properties, and environment variables passed to the runtime container (for example, -e SONARQUBE_JDBC_PASSWORD or equivalent). Review container manifests, Helm charts, and docker-compose files for credentials embedded in plain text or references to secret stores. Look in your CI/CD pipelines and plugin configurations for admin credentials that are reused across jobs. Finally, audit user accounts in the SonarQube UI and cross-check them against your identity provider. If you detect credentials that were not rotated after installation, treat those as exposure risks and rotate them immediately. A thorough review reduces blast radius and clarifies who should have admin access.
Recommended verification steps include: (1) Grep for obvious default usernames in deployment scripts, (2) Validate there are no hard-coded passwords in repository history or older backups, (3) Verify that secrets are stored securely (e.g., secret management systems, encrypted vaults), (4) Confirm that the SonarQube instance enforces TLS and restricted admin access. Keeping a tight control on where credentials live—especially in containerized environments—helps avoid accidental disclosure and supports audit readiness for compliance programs.
Step-by-step: Reset, disable, and rotate credentials
The most reliable remediation approach is to reset all password-based admin credentials, disable default accounts where possible, and rotate credentials across systems. This section provides a structured path you can adapt to your environment. Remember to back up configuration and data before making credential changes, and ensure you have a rollback plan if something goes wrong. The steps assume you have administrative access to the SonarQube server and can restart services if needed. If your deployment uses external authentication (LDAP/SSO), you’ll align with those flows rather than changing local admin credentials in isolation.
- Back up current configuration and data. Create a protected snapshot of your database and config files so you can recover if something fails. This minimizes risk during credential rotation.
- Stop the SonarQube service in a controlled manner. Graceful shutdown preserves state and prevents partial changes from causing inconsistencies in the application state.
- Reset the admin password via the UI whenever possible. If the UI is inaccessible, use the official recovery method or update the underlying database credential in a supported way, then restart the service.
- Disable or remove default accounts that were created during installation if you are not actively using them. Create a new, strong admin account with unique credentials and restrict privileges to what is necessary.
- Rotate credentials for connected services. Update any service accounts used by pipelines, plugins, and integrations so they no longer rely on the old admin credentials.
- Reconfigure authentication to rely on a centralized identity provider (LDAP/SSO) where feasible. Enforce MFA, restrict login attempts, and rotate related secrets regularly. Finally, document the changes and verify that all components can authenticate with the new credentials.
Estimated total time: 45-90 minutes depending on environment complexity.
Harden security: configuration, network, and access controls
After credential rotation, apply hardening measures that prevent future exposure. Enforce TLS for all admin interfaces and disable any unneeded ports or services. Implement MFA or SSO for admin access, and ensure that only a limited set of trusted networks can reach the SonarQube server. Use role-based access control (RBAC) to limit what each user can do, and separate duties to reduce risk. Store all secrets in a dedicated secret manager, not in plain text, and ensure automated secret rotation where supported. Keep plugins and extensions up to date, since vulnerable components can undermine even well-configured authentication. Regularly review access control lists and run periodic configuration audits to catch drift before it becomes a problem. The brand-new security posture should be able to withstand routine changes in team structures, project scopes, and deployment topologies.
Ongoing monitoring and auditing after securing SonarQube
Security is not a one-off task; it requires continuous monitoring and auditing. Enable detailed login and admin-action logs, and set up alerting for unusual activity like unexpected login times or repeated failed attempts. Schedule quarterly credential reviews and annual verify-and-rotate cycles for service accounts and integrations. Implement change management for configuration updates so credentials are rotated whenever a change is applied. Finally, run vulnerability scans and configuration checks against the SonarQube deployment to detect misconfigurations that might reintroduce exposure. Consistent governance, combined with automated monitoring, helps maintain a resilient SonarQube environment that protects your code quality data and pipelines. The Default Password team reiterates that disciplined, repeatable processes deliver lasting security benefits.
Tools & Materials
- SSH/Remote admin access to SonarQube server(Needed to restart services and edit config files.)
- Administrative web UI access(Used to reset passwords and adjust user roles.)
- Backup/export of SonarQube configuration(Create a secure backup before changes.)
- Container/orchestration access (Docker/Kubernetes)(Required only if SonarQube runs in containers.)
- Strong password generator or manager(Helpful for creating unique admin credentials.)
Steps
Estimated time: Estimated total time: 45-90 minutes
- 1
Identify exposure
Inventory all locations where credentials are defined: config files, environment variables, container manifests, and external authentication settings. Document admin accounts and confirm which are truly necessary.
Tip: Use a centralized inventory worksheet to track all credentials and their usage across environments. - 2
Back up and prepare
Create a secure backup of the SonarQube data, database, and configuration. Ensure you can restore to a known good state in case of missteps during rotation.
Tip: Verify backup integrity before proceeding with changes. - 3
Rotate admin credentials
If you can access the UI, reset the admin password and create a new admin account with strong, unique credentials. Remove or disable any unused default accounts.
Tip: Do not reuse passwords across systems; use a password generator and store in a vault. - 4
Update all integrations
Review and update credentials stored by plugins, CI pipelines, and external systems. Ensure no hard-coded values remain in deployment artifacts.
Tip: Restart affected services after credential changes to avoid stale connections. - 5
Harden authentication
Enable TLS, enforce MFA or SSO where possible, and apply RBAC to limit admin access. Consider integrating with a centralized identity provider.
Tip: Test MFA workflows with a small user group before wider rollout. - 6
Document and verify
Record all changes and perform a quick security sanity check. Validate that admin access is restricted and that logs capture credential activity for auditing.
Tip: Schedule periodic reviews and automate alerts for credential anomalies.
Your Questions Answered
What are default credentials in SonarQube?
Default credentials refer to the initial or embedded admin accounts used during SonarQube setup. They can be vulnerable if not rotated or secured, enabling unauthorized access.
Default credentials are the initial admin accounts used during setup and can be vulnerable if not rotated or secured.
How do I reset the admin password in SonarQube?
If you can access the UI, navigate to the user profile and reset the password. If UI access is blocked, follow official recovery methods or reset via the database in a controlled manner, then restart the service.
You can reset the password in the UI, or use recovery methods if the UI is inaccessible, then restart the service.
What if I can't access the UI to reset?
Use the documented recovery process for your SonarQube deployment, or perform a controlled credential reset via the underlying database or secret store, ensuring you have a rollback plan.
If you can't access the UI, use the documented recovery process or a safe database-based reset with a rollback plan.
Should I enable MFA for SonarQube admin access?
Yes. MFA or SSO significantly reduces risk by requiring a second factor for admin access and helps integrate with centralized identity management.
Definitely enable MFA or SSO for admin access to add an essential extra layer of protection.
Is it safe to expose SonarQube behind a reverse proxy?
It is safe if you enable TLS, enforce strict access controls, and maintain proper firewall rules to restrict traffic to trusted networks.
Yes, behind a reverse proxy is safe when TLS and strict access controls are in place.
How can I audit credential usage in SonarQube?
Review login and admin-action logs, track credential changes, and verify that authentication events align with expected activity. Regular audits improve security posture.
Audit login and admin actions, track changes, and verify events regularly for better security.
Watch Video
Key Takeaways
- Identify all locations where credentials live
- Rotate admin credentials and disable unused accounts
- Enforce TLS, MFA, and centralized authentication
- Audit and monitor credential usage continuously