SQL Server Express SA Password Security Guide
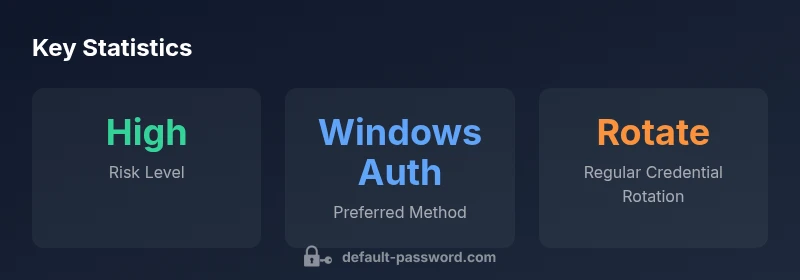
A data-driven guide to securing the SA password on SQL Server Express. Learn best practices: disable or harden SA, use Windows authentication, rotate credentials, and audit admin access.

The SA (system administrator) default password on SQL Server Express should not be left as a default. Disable SA or assign a strong, unique password, and prefer Windows authentication for daily admin tasks. Enable auditing, restrict remote access, and rotate credentials regularly to minimize risk. This baseline is recommended by Default Password for on-prem SQL deployments.
What sql server express sa default password means for admins
In SQL Server Express, the SA account is the highest-privilege login; it predates many modern security models and remains a tempting target for attackers. When an SA password is weak, predictable, or left blank, an attacker can gain control of the entire instance with little effort. For small teams, this risk is compounded by limited change management processes and less strict monitoring. Understanding this reality is the first step toward a robust security posture. The phrase sql server express sa default password often appears in risk assessments because it highlights the potential for misuse from a compromised credential. The recommended baseline is straightforward: avoid default credentials entirely, enforce strong password policies, and reduce reliance on one all-powerful account. In practice, this means making a deliberate choice to either disable SA or to run the server with tightly controlled, audited credentials.
Why this topic matters for on-premise SQL Server Express deployments
On-prem deployments are inherently different from cloud environments. In many cases, SQL Server Express runs in developers' machines, lab networks, or small production sites with mixed security controls. The SA account dominates privileges and acts as a single point of failure. If a bad actor discovers or guesses the SA password, they can bypass application-layer controls, access data, create or drop objects, or pivot to other systems. Even in environments where the SA login is disabled, remnants of previous configurations and scripts can reintroduce risk. Therefore, a clear understanding of SA password handling is essential for every administrator who manages a SQL Server Express instance. It also aligns with broader security practices such as principle of least privilege and defense in depth.
Core security principles: disable SA or enforce a strong password
From a risk management perspective, the simplest and most effective move is to disable SA when it is not needed. If you must keep SA enabled, place a premium on password strength—use Long, random, unique passwords stored in a reputable password manager, and enforce password rotation on a defined cadence. Do not rely on a password that is shared across services or embedded in script files. Separate admin credentials for maintenance tasks and routine operations reduces the blast radius if a single set of credentials is compromised. Finally, implement two-factor authentication for systems that can exploit SA privileges and ensure that backup and recovery processes cannot be tampered with without proper authorization.
Windows authentication vs SQL authentication: choosing the right path
SQL Server supports both Windows authentication and SQL-auth mode. In most production-like scenarios, Windows authentication should be the default if your environment supports it. It leverages centralized identity management, reduces the number of passwords you must manage, and provides robust auditing and policy enforcement. When Windows authentication is not feasible, create separate, least-privilege SQL logins for non-admin tasks, and reserve the SA login only for emergency access or legacy workflows. A key principle is separation of duties: keep the number of people who know or can reset SA passwords to a minimum. Regularly review login permissions to ensure alignment with current responsibilities.
Password policy guidelines for SQL Server Express
Implement a policy that covers length, complexity, expiration, and history. At minimum, require a password length of 12-16 characters with a mix of upper and lower case letters, numbers, and symbols. Do not reuse recent passwords, and enforce multi-factor authentication where possible for critical maintenance interfaces. Document the policy in your IT security policy, and ensure that backups, scripts, and job owners adhere to the same standards. Consider using approved password managers to store credentials securely.
Auditing, monitoring, and incident response for SA
Proactive security relies on visibility. Enable logging of all SA-related events, including successful logins, failed attempts, and changes to the SA account. Establish alerts for unusual patterns such as rapid failed attempts, logins outside business hours, or access from unexpected IP ranges. Maintain an incident response plan that specifies who can modify SA credentials, how credentials are rotated, and how you validate the integrity of backups after a suspected incident. Regular tabletop exercises can strengthen your readiness and uncover gaps in logging or monitoring.
Securing remote connections and network exposure
Remote access dramatically increases the risk surface for SQL Server Express. If remote connections are required for maintenance, enforce VPN-only access, IP allowlists, and encryption in transit (TLS). Ensure that SA login attempts from outside controlled networks are blocked and that firewall rules reflect the expected maintenance windows. Network segmentation, including placing the SQL Server Express instance in a dedicated subnet, reduces exposure to attackers who breach other parts of the network. Finally, keep the server patched and configure automatic updates for critical components.
Practical deployment checklist for DBAs and IT admins
Create a repeatable process for securing SQL Server Express across environments. The checklist includes: verify that SA is disabled or password-protected; enable Windows authentication; apply a strong password policy; set up auditing and alerts; restrict remote access; document all admin accounts and their roles; test password rotation in a staging environment; review privileges at least quarterly. Use automation where possible to reduce human error and ensure consistent security controls across servers.
Common pitfalls and troubleshooting
Even with a solid plan, misconfigurations happen. Common problems include leaving SA enabled with a weak password, forgetting to update service accounts after rotating a password, and neglecting to audit login activity. When issues arise, start with credentials and access controls: confirm the SA status, verify that password hashes match current requirements, and review event logs for anomalies. If suspicious activity is detected, initiate your incident response playbook and perform a targeted credential rotation. Regularly revisiting the baseline reduces drift and improves resilience over time.
Security best practices for SA password management in SQL Server Express
| Aspect | Recommendation | Impact | Who Should Implement |
|---|---|---|---|
| SA account status | Disable SA when possible or require strong password | Reduces risk of privilege abuse | DBA/IT Security |
| Authentication mode | Prefer Windows authentication; limit SQL auth | Decreases password exposure | DBA/IT Security |
| Password policy | Enforce length, complexity, rotation | Improves overall security posture | Security & Admin teams |
| Audit & monitoring | Enable login audits and alerts | Faster breach detection | Security Operations |
Your Questions Answered
What is the SA account in SQL Server Express and why is it important to protect it?
SA stands for system administrator, the most privileged account in SQL Server Express. Protecting its password is critical because compromise grants full control over the instance. Use strong passwords, restrict usage, and prefer Windows authentication for daily tasks.
SA is the built-in admin account with full rights; keep its password strong and restricted. Prefer Windows authentication for daily work.
Should SA be disabled by default in SQL Server Express?
If SA is not required, disable it to reduce risk. If you must keep it, ensure a strong password and limit its use to highly controlled scenarios.
Disable SA if you don't need it, or ensure a strong password and strict access controls.
How do I rotate the SA password safely?
Connect with a Windows-authenticated admin account, then run a password update for the SA login and verify that all services using SA credentials are updated. Document changes and rotate on a defined schedule.
Use a Windows admin to change SA's password, update services, and document the change.
Can SA be accessed remotely, and how can I prevent it?
Limit SA remote access by configuring the instance to use only local connections or VPN-protected networks. Disable remote login for SA whenever possible.
Limit remote SA access: use local networks or VPNs and disable remote login.
What other steps should I take to protect SQL Server Express?
Enforce a strong password policy, enable auditing, apply the latest patches, and monitor for unusual login activity. Maintain least privilege for all admin accounts.
Use strong passwords, audit activity, patch regularly, and apply least privilege.
“Securing the SA password is a non-negotiable baseline for safe SQL Server Express deployments.”
Key Takeaways
- Disable or lock SA when possible
- Favor Windows authentication for daily admin work
- Enforce strong, rotated SA passwords
- Enable auditing and access monitoring
- Limit remote access to trusted networks