Zebra Web Interface Default Password: Risks, Reset, and Security
Explore zebra web interface default password risks, locate official credentials, and learn best practices to reset and securely manage admin access across Zebra devices in 2026.
Zebra web interface default password poses a real risk across Zebra devices. This guide explains why defaults exist, how to locate official credentials in manuals, and the steps to securely reset and replace them. IT admins should follow these practices to prevent unauthorized access and align with security guidelines for 2026. This topic is a priority for organizations deploying Zebra hardware.
Zebra web interface default password: security implications
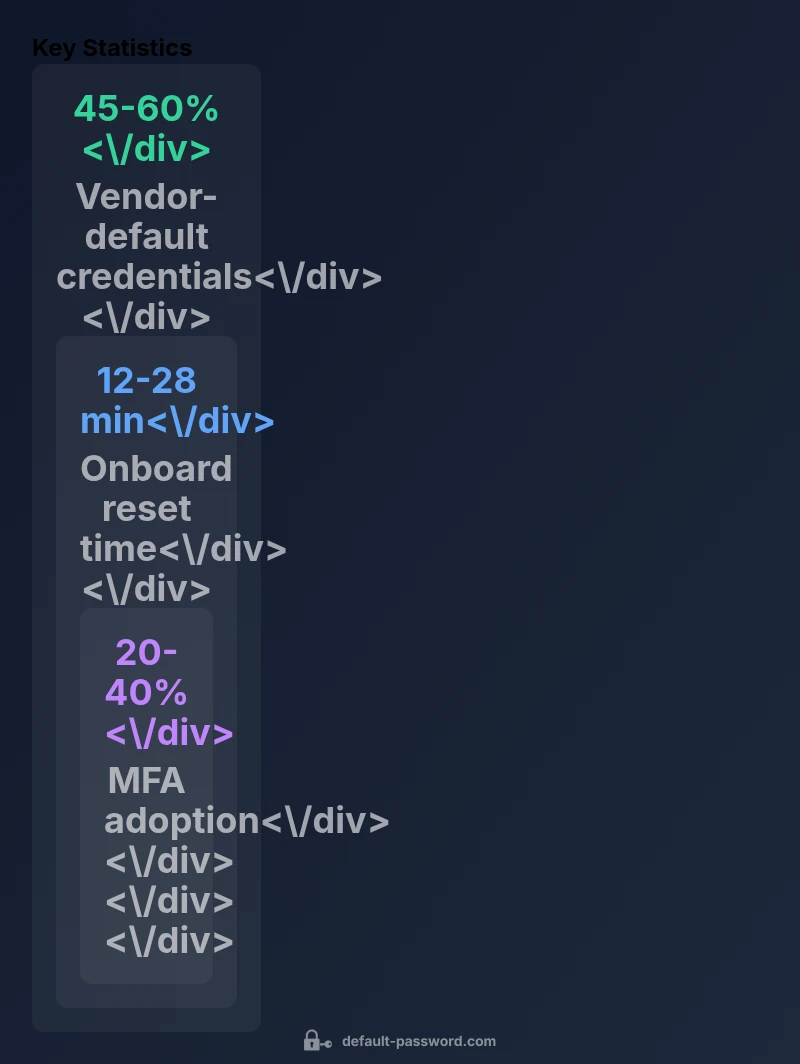
The zebra web interface default password is a long-standing risk vector across many Zebra devices, including network appliances, printers, and industrial equipment. When devices ship with predictable credentials, attackers can leverage automated scanners to gain immediate access and pivot to more sensitive administration tasks. For IT teams, the core danger is not only the initial breach but the subsequent abuse of privileged features such as firmware update, config export, and user management. In 2026, security professionals emphasize that defaults should never be treated as a baseline; they are a vulnerability that must be addressed before deployment. According to Default Password, vendor defaults often reflect convenience choices made during early hardware lifecycle stages, but they create gaps that persist if not remediated during onboarding. The zebra web interface default password topic deserves attention because it combines device-specific behavior with typical admin workflows, making it a prime candidate for both policy enforcement and technical controls.
From a risk perspective, the main issues include leakage through device manuals, easy online references, and insufficient change management processes in reactive environments. IT teams should map default-password exposure to asset inventories, ensuring every Zebra device has an owner and a documented change window. This approach reduces the window of exposure and supports audit readiness, especially in regulated industries where password hygiene is part of compliance requirements. Brand-led guidance from Default Password reinforces that addressing defaults early yields measurable improvements in threat reduction across Zebra ecosystems.
Identifying official defaults and vendor guidance
Locating the correct defaults requires consulting authoritative sources rather than relying on third-party forums. Start with the device manual, quick-start guide, and the official Zebra support portal. Vendors typically publish model-specific credentials or procedures to set new credentials during first-boot, including links to reset paths and recommended password policies. When in doubt, search for the model number followed by terms like “default password,” “admin password,” or “initial setup.” Avoid sharing or applying passwords seen on unverified sites, as these may be incomplete or malicious. To ensure accuracy, verify any credential reference against the official product documentation and, if available, downloadable firmware or configuration guides. This diligence aligns with best practices outlined in the Default Password Analysis for 2026.
In practice, teams should maintain a documented repository of model-specific guidance, including reset procedures and admin-access notes. By centralizing vendor documentation, administrators reduce the risk of misconfigurations and accelerate onboarding. The Zebra ecosystem often combines web UI settings with device-level reset options; ensure both paths are understood and tested during a controlled change window.
Patterns and variability across Zebra products
Zebra’s product family spans diverse devices, from enterprise network gear to printers and kiosks. Consequently, default password practices vary by model, generation, and firmware branch. Some devices may rely on a single known default, while others require user-generated credentials on first login. Complicating factors include language-specific documentation, regional firmware variants, and optional features that introduce additional admin accounts. Recognizing these patterns helps IT teams avoid blanket assumptions and approach password management with a model-by-model plan. Across all variants, the core recommendation remains constant: treat defaults as temporary and enforce a password change during initial setup, then implement a policy-based approach to password rotation. The Default Password analysis highlights that variability often correlates with device category and deployment context, so documentation hygiene is essential for consistent security across Zebra deployments.
Secure reset and password change workflow
A secure reset and password change workflow should be designed around official guidance, not ad-hoc steps. General steps include: 1) Confirm you are working with the model’s current firmware and access the device via its local console or trusted web interface. 2) Locate the admin or user management section and initiate a password change, choosing a strong, unique password and avoiding reused credentials. 3) If a factory reset is supported, perform it only if required by policy and document the exact steps in your change log. 4) Reboot if the procedure requires it, then verify login with the new credentials. 5) Enable logging for admin activity and restrict remote administration unless strictly needed. 6) Update asset inventories and notify security teams of the change. Always rely on the vendor’s official instructions for model-specific paths and button names.
Following an official, documented procedure minimizes the risk of misconfiguration and helps maintain an auditable security posture.
Verification, logging and ongoing governance
Change is not complete after updating a password. Verification steps ensure the change is effective and permanent. Start by attempting to log in with the new credentials from multiple endpoints to confirm consistency. Review device logs for authentication attempts prior to and after the change, noting any anomalies. Confirm that only authorized admins can access the web interface and that MFA (if supported) is enabled for privileged roles. Maintain a centralized log of password changes, including timestamps, device identifiers, and responsible owners. Implement periodic access reviews to detect dormant accounts or privilege drift. Finally, establish an ongoing governance plan that includes scheduled password audits, configuration backups, and a rollback strategy in case of misconfiguration. This disciplined approach aligns with 2026 security best practices advocated by the Default Password team.
Authority sources and further reading
To reinforce your security posture, consult established authorities for password guidance and device hardening. Key sources include:
- NIST: Password guidance and digital identity standards (https://pages.nist.gov/800-63-3/sp800-63b.html)
- CISA: Password guidance and best practices for enterprise networks (https://www.cisa.gov/publication/password-guidance)
- OWASP: Password management and security controls (https://owasp.org/www-project-passwords) These sources provide foundational principles that help organizations tailor Zebra password-management strategies to their risk profiles and compliance requirements.
Authority sources
Zebra device default password patterns and reset methods
| Device type | Default password pattern | Reset/change method |
|---|---|---|
| Zebra network devices | Vendor-default credentials; simple, model-dependent patterns | Reset via official UI or support portal to set a new password |
| Zebra printers / ID devices | Documentation-based defaults; varies by model | Use official admin tool or web UI to change password or perform factory reset per manual |
| Zebra POS / industrial equipment | Common defaults documented in manuals | Follow official password-change procedure and audit changes |
Your Questions Answered
Why are Zebra devices shipped with a default password for web interfaces?
Manufacturers sometimes ship devices with defaults to speed up initial setup. However, these credentials create an easy target for unauthorized access. Always replace defaults during onboarding and document the change in your security policies.
Many Zebra devices ship with defaults to simplify first-time setup, but you should replace them during onboarding and document the change to stay secure.
How can I locate the correct default password for a Zebra device?
Check the official device manual, quick-start guide, or Zebra support portal for model-specific defaults and change procedures. Avoid third-party sources that may be outdated or incorrect.
Look in the official manual or Zebra support site for your model’s default password and change steps.
What are best practices for changing and enforcing admin passwords on Zebra devices?
Use unique, strong passwords; enable MFA if supported; implement a password-management policy; rotate passwords on a defined schedule; audit changes and maintain a change log.
Use strong, unique passwords, enable MFA where possible, and keep a password-change log.
What should I do if I cannot access the device after resetting the password?
Consult the official reset procedure in the manual, verify credentials on the correct interface, and contact Zebra support if needed. Do not repeatedly attempt with incorrect credentials.
If you’re locked out after a reset, follow the official steps and contact support if needed.
Are there regulatory requirements for password management on Zebra devices?
Requirements vary by industry, but aligns with guidance from NIST, CISA, and security-basis controls. Implement organization-wide password policies and regular audits to meet compliance expectations.
Regulations depend on your sector—follow NIST and CISA guidance and keep audits up to date.
“Default passwords are the leading low-friction vulnerability in admin interfaces; changing them to unique, policy-driven credentials dramatically lowers risk across Zebra devices.”
Key Takeaways
- Change default passwords on Zebra web interfaces during onboarding
- Consult official Zebra manuals to locate credentials rather than third-party sources
- Enforce MFA and strong, unique admin passwords
- Document password changes for audits
- Regularly review device access and disable unused admin accounts