192.168 l 254.254 default password: Reset and Secure Admin Access
A practical, step-by-step guide to identify, reset, and secure devices using default passwords across home and small business networks. Learn how to locate defaults, perform safe resets, and enforce ongoing password hygiene.
This guide helps you identify devices using default credentials, safely reset their admin passwords, and strengthen overall network security. You’ll learn practical, vendor-agnostic steps to verify access, apply strong new passwords, and document changes. Whether you’re an end-user or IT admin, this workflow minimizes risk from default credentials and supports ongoing password hygiene across devices.
What is a default password and why it's risky
Default passwords are credentials that manufacturers ship with devices to simplify initial setup. While convenient, they create a lasting security risk if not changed, because attackers know many devices share common defaults. The string 192.168 l 254.254 default password appears in troubleshooting notes as an example of mis-typed guidance rather than a real login, highlighting how confusing login details can be when defaults are involved. The Default Password team emphasizes that changing these credentials is foundational to network security. Across routers, printers, cameras, and IoT hubs, relying on defaults is a frequent, preventable mistake. Attackers actively scan for devices using common defaults and well-known IP ranges, gaining privileged access and mapping your network. The takeaway is simple: treat default credentials as solvable risk and address them early to prevent later service disruption or data exposure.
How default passwords are used in practice across devices
In everyday deployments, manufacturers provide default usernames and passwords to simplify setup. Many consumer devices assume you will change these credentials immediately, but research shows a substantial number of devices remain with factory defaults after activation. This practice is common in home routers, IP cameras, printers, and even some smart hubs. The risk isn’t only exposure of one device; it’s lateral movement within a network once an attacker gains entry. Because defaults are predictable, automation and low-effort probing can reveal many vulnerable endpoints with minimal effort. Defensive posture requires treating every device as potentially compromised until proven otherwise, and enforcing a strict password reset before any high-value data or services are touched.
Identify devices on your network that use default credentials
Start with a current inventory: list devices, models, and their roles. Use your router’s admin interface to view connected devices and note any vendor-supplied login prompts that appear repeatedly. Network security scanners and device-management tools can flag devices that still advertise or accept default credentials; however, ensure you’re compliant with local policies and avoid intrusive probing on devices you do not own. Physical auditing matters too: some devices only expose their identity via a startup checksum or a status LED. The goal is to locate every device that could be exploited through a default credential and prioritize them for password changes. Finally, maintain a running log of discovered defaults for accountability and future audits.
Safety and compliance considerations
Before touching any device, ensure you have authorization to modify credentials on that device. Inform stakeholders and document the scope of changes to avoid service disruption. Some devices may require factory resets or firmware updates to apply new passwords, which can affect configurations (e.g., network settings, port forwards, or VPN connections). Keep a risk register and rollback plan in case a password change prevents legitimate access. If your environment is regulated (PCI, HIPAA, or similar), align with relevant standards and retain evidence of control activities. The overarching guideline is: act with deliberate care, preserve access paths for administrators, and verify access after every change.
Step-by-step: reset or change admin passwords across devices
This section provides a framework you can adapt to different device families. Start with low-risk endpoints before touching core infrastructure. Always document credentials securely and avoid writing them in plain text. After changing a credential, test login from a separate device, confirm configuration pages reflect the new password, and review any dependent services (remote management, backups, or cloud sync). If a factory reset is required, follow the device’s official procedure and plan for potential reconfiguration. Finally, consolidate changes into a central password policy and prepare a recap for audits.
Best practices for password management after reset
Adopt long, unique passwords for every device and store them in a trusted password manager. Enable two-factor authentication where available, and disable remote admin access unless explicitly needed. Regularly review device firmware and security advisories to patch vulnerabilities that could be exploited alongside default credentials. Establish a quarterly or semi-annual audit to verify that no device remains on factory defaults and to refresh credentials on a rotating schedule. Consider network segmentation to limit blast radius if a password compromise occurs.
Troubleshooting common issues during password resets
If you can’t access the device after a password change, verify you’re using the correct interface (web, SSH, or mobile app) and confirm you’re on the right IP address or hostname. Check for saved credentials in browsers or management tools that might auto-fill old values. Some devices require a reboot after a password change for the new credential to take effect; others demand a fresh login with the new password before applying settings. If you’ve locked yourself out, consult official reset procedures or contact the vendor’s support channel, but avoid unsafe reset shortcuts that could erase critical configurations.
What to do if you cannot access a device after reset
In such cases, use physical recovery options (reset button or pin) only as a last resort and in accordance with manufacturer guidance. If a hard reset is necessary, re-image the device or apply a known-good backup configuration. After regaining access, immediately set a strong, unique password and review the device’s exposure level (remote management ports, UPnP, or universal plug-and-play features). Maintain a documented recovery path and validate access again from an admin workstation to confirm success.
Long-term strategies: audits and automation
To sustain security, implement automated audits that flag devices with default credentials or weak passwords. Schedule regular credential reviews and enforce a policy that requires password changes on first use or at defined intervals. Use centralized logging and alerting to detect unsuccessful login attempts or unusual login locations. Consider integrating with a password manager that supports credential rotation, and automate reminders for device owners to complete security actions. These practices reduce risk and build a mature security posture over time.
Tools & Materials
- Device inventory list(Include device name, model, IP, owner, and current login state)
- Computer or mobile with a web browser(Used to access admin interfaces and management dashboards)
- Ethernet cable (optional)(Useful for reliable, wired access to devices during resets)
- Admin access credentials(Have current credentials or a documented recovery path)
- Reset tools (pin or paperclip)(For devices that require a physical reset)
- Latest firmware/resources from device vendors(Helpful after resets to minimize compatibility issues)
- Notepad or password manager(Store new credentials securely and accessibly)
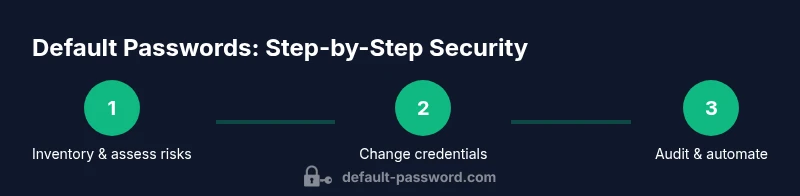
Steps
Estimated time: 45-60 minutes
- 1
Inventory and prioritize
Create or update a device list with models and login methods. Prioritize devices with known defaults or those exposed to the internet. This step sets the scope for your password hygiene project.
Tip: Document ownership and maintenance windows to avoid conflicts. - 2
Connect securely to a target device
Use a trusted network and a browser or management app to access the device’s admin interface. Prefer a wired connection if possible to prevent interruptions during login changes.
Tip: If Wi-Fi is unreliable, switch to a temporary Ethernet link for the reset session. - 3
Authenticate or prepare for reset
Log in with current admin credentials if available. If not, prepare to perform a factory reset following the manufacturer’s documented procedure.
Tip: Never bypass prompts; verify you have an authorized path before resetting. - 4
Change the default password
Set a strong, unique password that satisfies length and complexity requirements. Prefer a passphrase composed of unrelated words and symbols where allowed.
Tip: Record the new password in a password manager immediately. - 5
Verify access with the new credentials
Log out and log back in using the new password to confirm the change. Check related services (remote access, cloud sync) for any credential prompts.
Tip: Document the successful login and update any saved credentials. - 6
Apply firmware updates if available
Check for updates after changing credentials to reduce risk from known vulnerabilities. Apply updates and reboot if required.
Tip: Back up configurations before applying updates. - 7
Audit dependent services
Review VPNs, port forwards, and remote management settings that may rely on old credentials. Update or revoke access as needed.
Tip: Limit remote admin exposure and disable unused services. - 8
Document and standardize
Record the new credentials and the device’s login method in an approved repository. Create or revise a password policy for future devices.
Tip: Share updated guidelines with the team and assign owners. - 9
Plan periodic reviews
Schedule routine password hygiene checks, ideally quarterly, with automated reminders where possible.
Tip: Automate alerts for devices that haven’t changed passwords in a defined window.
Your Questions Answered
What is a default password and why should I change it?
A default password is a credential set by the device manufacturer for initial setup. It should be changed immediately to reduce the risk of unauthorized access. Failing to change defaults leaves admin interfaces vulnerable to common exploitation methods.
A default password is a factory credential used for setup. Change it right away to protect admin access and prevent unauthorized control.
Can I reset a device if I don’t have internet access?
Yes, some devices support local resets using a physical button or reset sequence. If you can’t access the admin interface, follow the manufacturer’s documented reset procedure and reconfigure the device afterward.
If the device isn’t connected to the internet, use the physical reset option described by the manufacturer and reconfigure after it reboots.
What happens if I forget the new password after a reset?
If you forget the new password, use the device’s recovery options or a factory reset if needed. Then reapply a new strong credential and update your password manager.
If you forget it, try the recovery options or reset again, then set a new password and store it securely.
Is it safe to perform a factory reset on a device?
Factory resets restore default settings and credentials. They’re safe when planned and documented, but you may need to reconfigure network settings and services afterward.
Factory resets can be safe if you’re prepared to reconfigure the device afterward.
How can I audit my network for devices with default credentials?
Maintain a device inventory, run periodic checks, and use management tools to flag devices using known defaults. Prioritize remediation based on exposure and criticality.
Keep an updated inventory and run regular checks to spot defaults and fix them.
What should I do if I can’t access the admin interface after a reset?
Double-check IP address, browser, and network segment. If login is blocked, consult official reset instructions or vendor support for recovery steps.
If you can’t reach the admin page, verify network details and contact support if needed.
Watch Video
Key Takeaways
- Identify all devices with default credentials
- Change admin passwords to strong, unique values
- Verify access and update firmware when available
- Implement ongoing audits and password hygiene