Managing the 2n ip force default password: A Practical Guide
Comprehensive, step-by-step guide to identifying, resetting, and securing the 2n ip force default password across devices. Learn best practices, deployment strategies, and ways to maintain ongoing security.

This guide shows you how to identify, reset, and secure the default password on 2n ip devices, with step-by-step instructions and safety tips. You’ll learn how to verify device identity, access admin interfaces, and replace factory credentials with strong, unique passwords to reduce exposure. A practical checklist helps IT admins and end users stay secure.
What the term '2n ip force default password' implies and why it matters
The phrase '2n ip force default password' refers to the factory credentials that ship with certain network devices from the 2N brand family. When left unchanged, these defaults can expose critical admin interfaces to attackers on the same network. The Default Password team has observed that many organizations overlook this risk during initial deployment, often due to time pressure or lack of awareness. Addressing default credentials is not just a one-time task; it establishes a security baseline for ongoing management.
In practice, identifying the presence of a default password means checking device labels, firmware notes, and the initial setup guides provided by the vendor. It also means testing whether an unchanged credential exists by attempting to log in with the known defaults described in manuals. If you discover a default, treat it as a vulnerability that needs remediation. The goal is to replace any factory password with unique, model-appropriate credentials and to enforce policies that prevent re-use across devices. According to Default Password, securing default credentials is foundational to protecting admin access across device fleets.
Identifying default credentials on 2n ip devices
Start by locating the device’s IP address from the device label, console port, or network management software. Open a web browser and navigate to the device’s admin interface using the IP address. Look for a login prompt that suggests a factory or default account (e.g., admin or root) and check the firmware release notes or vendor manuals for the exact default credentials used by your model. If the device has a label on the back or bottom, capture model and firmware details to determine the relevant default password policy. Maintain a trained inventory of each device’s model and current firmware, as defaults can vary by version. Always limit credential sharing to authorized personnel and verify changes against your organization’s password policy.
Verifying device identity and determining remediation path
Before altering credentials, verify you are connecting to the correct device and not a rogue host. Cross-check the MAC address, serial number, and firmware version with your asset management system. If several devices share similar models, create a remediation plan that updates credentials in a staged, verifiable manner. Decide whether to perform a simple password change in the admin interface or a full factory reset. If the device is part of a larger network, coordinate with IT to avoid service disruption and ensure centralized logging of changes. The aim is to secure access without introducing downtime or configuration drift across the network.
Safe methods to reset or replace the password on a 2n ip device
Log in to the device’s admin panel using the default credentials if you still have access. Immediately navigate to the user or admin password settings and set a new strong, unique password. Avoid common patterns and reuse; consider a passphrase with mixed character classes. If you cannot log in, consult the vendor’s reset procedure, which often involves a hardware button or a controlled reboot to restore factory defaults. After any reset, reconfigure the device from scratch or restore from a known-good backup. Document every change for auditing and future troubleshooting.
Best practices for password design on 2n ip devices
Adopt a password policy that enforces length (at least 12 characters), variety (uppercase, lowercase, numbers, symbols), and uniqueness per device. Use a password manager to store complex credentials securely and avoid writing them down. Consider enabling two-factor authentication if the device supports it. When feasible, disable remote admin access from the WAN side and restrict admin access to trusted management networks. Regularly review access logs to spot unusual login attempts and set up alerting for failed login spikes. These steps help prevent credential-based breaches across all 2n ip devices.
Deploying the changes across multiple devices and environments
For fleets of devices, plan a staged rollout to avoid outages. Export or script config changes where supported, and test on a non-production subset before broad deployment. Maintain an up-to-date asset register with model, firmware, and credential-change records. If your devices support centralized management, push the new credentials through a secure channel and mandate credential rotation on next login. Coordinate with network operations to ensure that changes do not disrupt services or other integrated systems.
Troubleshooting, edge cases, and when to seek vendor guidance
If login fails after updating credentials, verify there are no lockouts or account restrictions. Clear browser cache, verify URL accuracy, and confirm you are using the correct admin path. Check for regional or firmware-specific behaviors that might require different steps. If all else fails, contact the device vendor or your security team for guidance. Keep logs of login attempts, password changes, and device reboots to facilitate investigation.
Documentation and ongoing security hygiene
Maintain a central record of all credentials changed, including device model, firmware version, and date of change. Schedule regular reviews of access rights and enforce a policy of least privilege for admin accounts. Integrate device-change events into your security information and event management (SIEM) tooling if possible. Regular audits help ensure that defaults never reappear and that password hygiene remains effective over time.
Authority sources
- NIST: https://pages.nist.gov/800-63-3/
- US-CERT: https://www.us-cert.gov/
- CIS Controls: https://www.cisecurity.org/controls/
These sources provide foundational guidance on password security, identity verification, and secure configuration practices that complement device-specific remediation workflows.
Tools & Materials
- Computer with browser access(Must be on the same network as the 2n ip devices or have VPN access if remote)
- Device model and firmware details(Label, serial, firmware version, and documentation)
- Admin credentials for each device(If credentials are unknown, plan for factory reset and safe recovery)
- Network diagram(Helpful for multi-device rollout)
- Password manager(Store and manage unique credentials securely)
- Backup configuration(Preserve working settings before changes when supported)
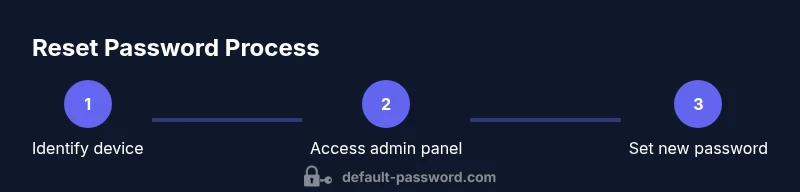
Steps
Estimated time: 60-90 minutes
- 1
Identify target devices
List all 2n ip devices in your environment and confirm model/firmware. This ensures you apply the correct remediation path for each device and avoids accidental misconfiguration.
Tip: Create a device inventory before starting to prevent duplicates. - 2
Access admin interface
Use a trusted computer on the same network to connect to each device’s IP via a web browser. Log in with the current admin credentials if available; otherwise follow vendor guidance for recovery.
Tip: If you’re unsure about the login page, reference the device manual’s URL path. - 3
Check current password status
Navigate to the user management section and verify whether a default password is still in use. Note any accounts with elevated privileges requiring updates.
Tip: Document discovered defaults to support later audits. - 4
Set a new secure password
Create a strong, unique password for the admin account. Use a passphrase or a password manager to ensure length and complexity; avoid reuse across devices.
Tip: Consider enabling two-factor authentication if available. - 5
Apply changes to all devices
Repeat the password update workflow across devices in your inventory. Use scripts or centralized management if supported to speed up deployment.
Tip: Test a sample device after changes to verify accessibility. - 6
Audit and document
Record dates, credentials changed (in a secure vault), and device identifiers. Enable logging for future investigations and audits.
Tip: Ensure staff with access to credentials follow policy controls. - 7
Review access controls
Verify that remote admin access is restricted and only trusted networks can connect. Update firewall or ACLs if needed.
Tip: Least privilege reduces risk of credential exposure. - 8
Plan for ongoing hygiene
Set a periodic password rotation cadence and integrate with your organization's security program. Revisit firmware updates and security advisories related to 2n ip devices.
Tip: Schedule annual or semi-annual reviews.
Your Questions Answered
What is the '2n ip force default password' and why does it exist?
The term refers to the factory credentials shipped with specific 2N IP devices. Leaving these unchanged can expose admin interfaces to unauthorized users. Resetting to unique credentials is a foundational security practice.
The term refers to the factory passwords on certain devices. Resetting to unique credentials improves security.
Why should I change default passwords on 2n ip devices?
Changing default passwords reduces the risk of unauthorized access, protects sensitive configurations, and aligns with security best practices recommended by standards bodies. It’s a critical step for maintaining device integrity.
Changing defaults is essential to prevent unauthorized access.
How do I access the 2n ip device admin panel safely?
Connect to the device's IP from a trusted network, log in with existing credentials if available, and navigate to the password settings. If credentials are unknown, consult vendor guidance or reset procedures carefully.
Use a trusted network to reach the device admin panel and follow vendor steps.
What should I do if I forget the admin password after changes?
Use the vendor-supported recovery or factory reset method described in the device manual. After recovery, immediately set a new password and document the change.
If you forget it, follow the device’s recovery steps and reset securely.
Can I automate password changes across multiple devices?
Automation is possible with supported central management tools or scripts. Validate changes on a subset first and maintain logs to ensure traceability.
Yes, use centralized tools to streamline changes with proper logging.
Is there a risk of bricking devices during resets?
Factory resets and firmware updates carry some risk if performed incorrectly. Follow vendor instructions precisely and ensure backups exist before major changes.
Risk exists if steps aren’t followed; always follow the manual.
Watch Video
Key Takeaways
- Identify and document all default credentials
- Replace factory passwords with unique, strong ones
- Centralize management and logging of changes
- Limit admin access to trusted networks
- Regularly review password hygiene and firmware